10 Essential Skills for Developing Cybersecurity Talent in Defense
Discover essential skills for cultivating cybersecurity talent in defense and enhancing security measures.

Introduction
In an era where cyber threats are more pronounced than ever, the defense sector urgently requires skilled cybersecurity professionals. The complexities surrounding compliance, especially with the upcoming Cybersecurity Maturity Model Certification (CMMC) requirements, underscore the need for a comprehensive skill set among defense contractors.
What essential skills should these professionals develop to not only meet compliance standards but also effectively protect sensitive information? This article explores ten critical competencies that will enable organizations to cultivate top-tier cybersecurity talent, adept at navigating the ever-evolving landscape of digital security.
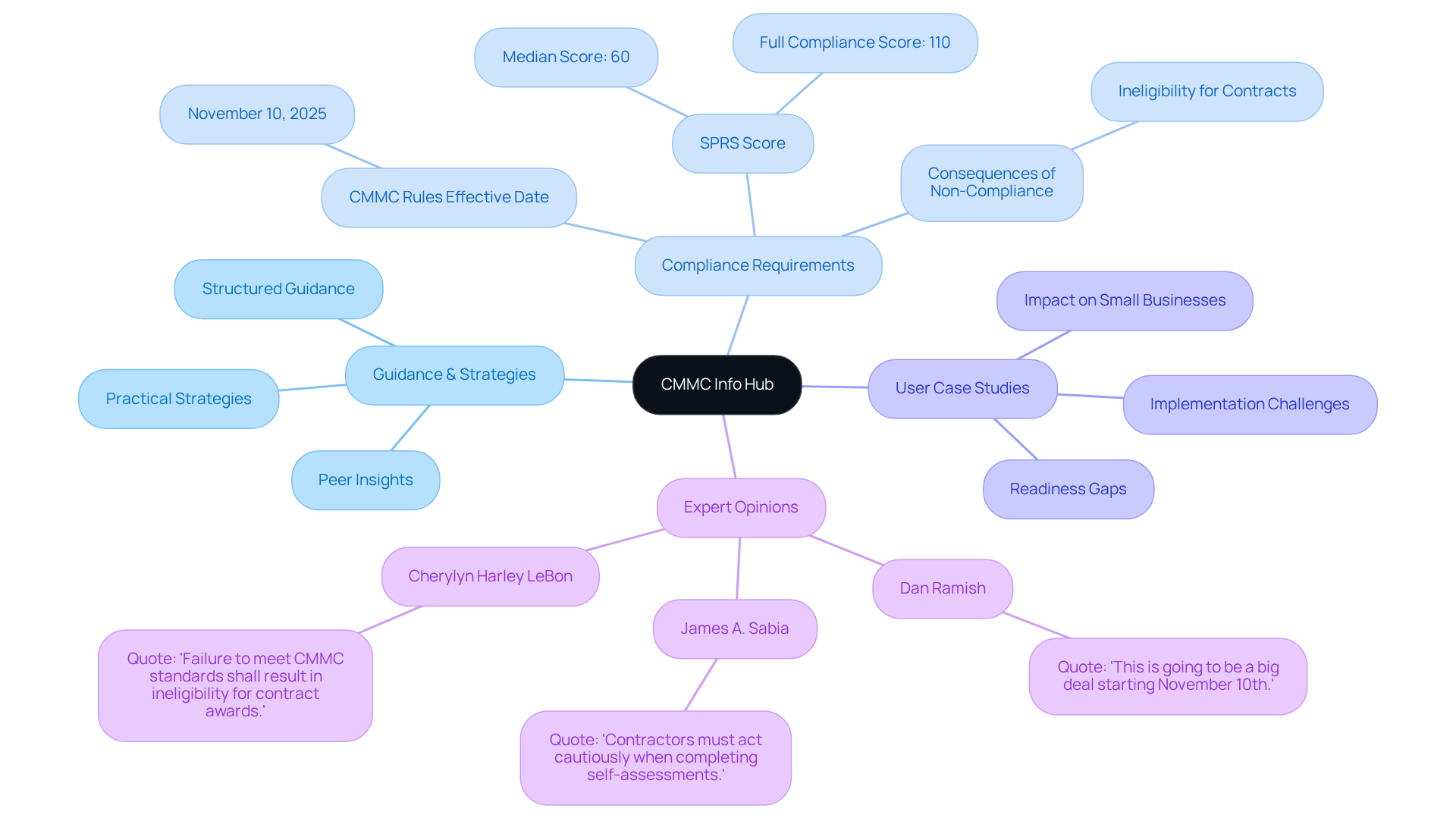
CMMC Info Hub: Essential Resource for Cybersecurity Compliance
CMMC Info Hub stands as an essential resource for organizations aiming to achieve compliance with the Cybersecurity Maturity Model Certification (CMMC). It offers structured guidance, comprehensive plans, and practical strategies tailored to the complexities of DoD security requirements. By tapping into insights from peers who have successfully navigated the compliance landscape, users can turn confusion into clarity, ensuring they meet rigorous standards and secure defense contracts effectively.
In the realm of online security, recognizing the importance of reliable resources is crucial. This platform may include links to external websites that can provide additional information; however, users should always verify the credibility of these sources. The presence of any link does not imply endorsement by us, and we bear no responsibility for the content or availability of these external sites.
Recent updates underscore the growing necessity of compliance with the cybersecurity framework, with new regulations set to take effect on November 10, 2025. These rules will require verified cybersecurity adherence for specific defense contracts. This shift emphasizes the role of the Info Hub in helping contractors prepare for these changes, as non-compliance could result in lost contract opportunities.
Successful case studies demonstrate the effectiveness of the Info Hub in guiding entities through the compliance process. For example, contractors who have utilized the platform report improved readiness and a clearer understanding of the requirements. This clarity is vital in a landscape where the median SPRS score among contractors is only 60, significantly below the full compliance score of 110.
Expert opinions further validate the value of the Info Hub, showcasing its tailored insights and practical strategies that empower defense contractors to confidently navigate the evolving compliance landscape. As the DoD continues to enforce CMMC requirements, leveraging the resources available through CMMC Info Hub will be crucial for organizations striving to attract cybersecurity talent and maintain their competitive edge in securing defense contracts.
AI Proficiency: Leveraging Artificial Intelligence in Cybersecurity
Proficiency in artificial intelligence (AI) is not just beneficial; it’s becoming a cornerstone of contemporary digital security strategies. Why is this important? AI technologies can automate risk detection, analyze vast amounts of data for anomalies, and significantly enhance incident response times. By incorporating AI into their security systems, organizations can proactively recognize potential dangers and mitigate risks before they escalate. This capability is particularly crucial in the defense sector, where the stakes are high and the threat landscape is constantly evolving.
Organizations must take action now. Embracing AI isn’t merely an option; it’s a necessity for staying ahead of threats. The integration of AI into security frameworks not only fortifies defenses but also empowers teams to respond swiftly and effectively. As the digital landscape continues to shift, those who adapt will lead the charge in safeguarding their assets and ensuring compliance with evolving standards.

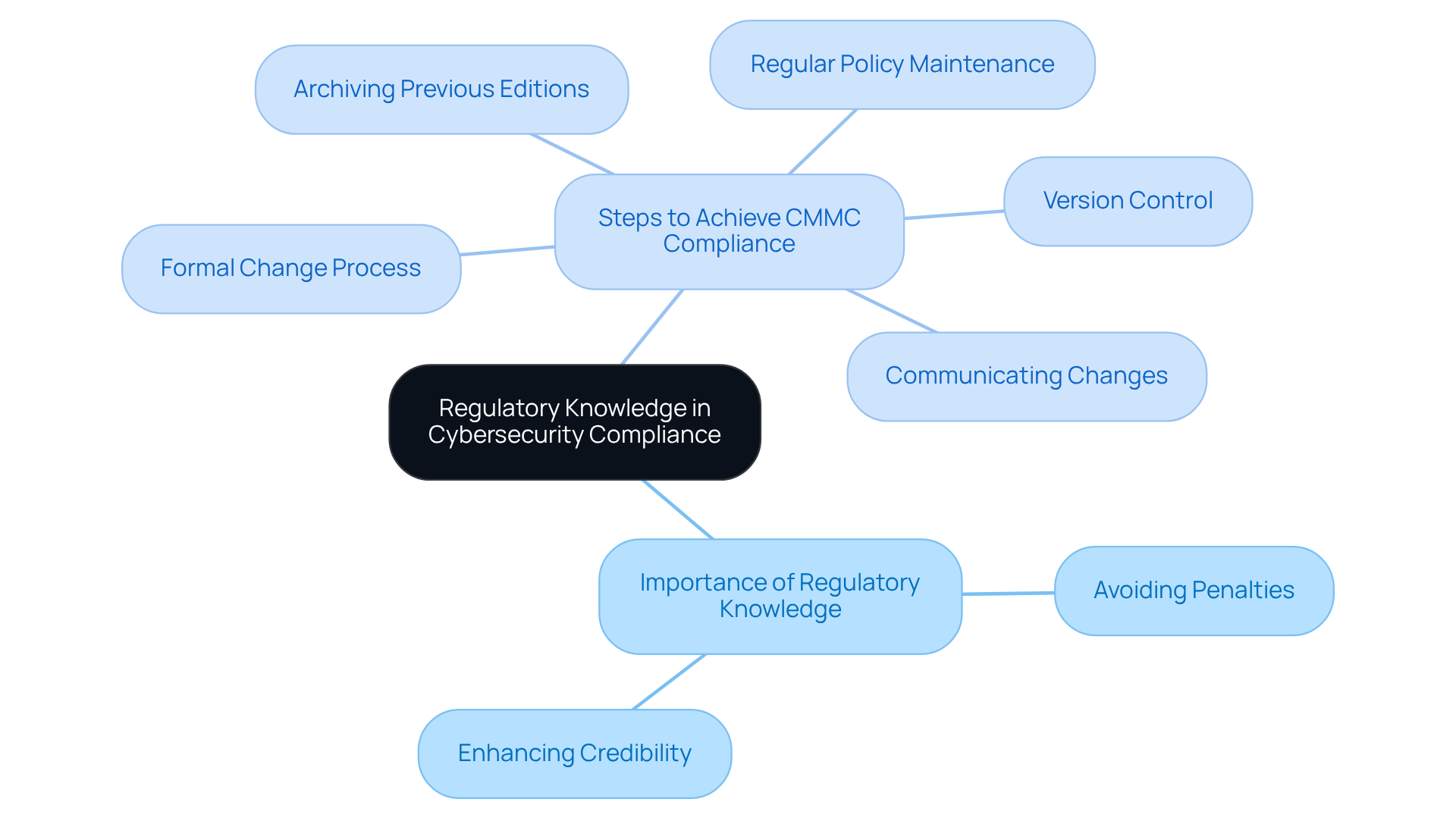
Regulatory Knowledge: Navigating Cybersecurity Compliance Standards
A deep understanding of regulatory knowledge is essential for cybersecurity talent, especially in the defense sector. Familiarity with standards like NIST and ISO 27001 enables organizations to establish crucial controls and demonstrate compliance during evaluations. This expertise not only helps avoid penalties but also enhances the organization's credibility and trustworthiness in the eyes of clients and regulatory bodies.
To effectively achieve CMMC compliance, organizations should adopt a comprehensive approach. This includes:
- Regular policy maintenance, reviewing policies at least annually.
- Establishing a formal change process.
- Maintaining version control.
- Archiving previous editions.
- Communicating changes to all impacted personnel.
This structured method ensures that organizations remain compliant and prepared for evaluations, ultimately supporting their success in securing defense contracts. Are you ready to take the necessary steps towards compliance?
Network Security Expertise: Protecting Systems from Threats
Network security knowledge is essential for safeguarding an organization's network infrastructure against cyber risks. This includes configuring firewalls, intrusion detection systems, and secure access protocols. Professionals in this field must stay vigilant, continuously updating their knowledge on emerging vulnerabilities and threat vectors to effectively counteract attacks.
In the realm of defense contracting, where sensitive data is at stake, robust network security is not merely a best practice; it is a necessity for compliance with Cybersecurity Maturity Model Certification (CMMC) requirements. Did you know that the cybersecurity industry is facing a shortage of approximately 4 million cybersecurity talent professionals? This statistic underscores the critical demand for skilled experts, particularly cybersecurity talent, in this area. Organizations must prioritize hiring and training to cultivate cybersecurity talent capable of implementing effective security measures.
Effective network security measures demonstrate that proactive strategies - such as regular security evaluations and the adoption of advanced technologies - can significantly enhance an organization's resilience against cyber risks. As the landscape of cyber threats evolves, defense contractors must adapt their security protocols to protect their systems and maintain compliance. This adaptability is crucial for securing vital defense contracts.

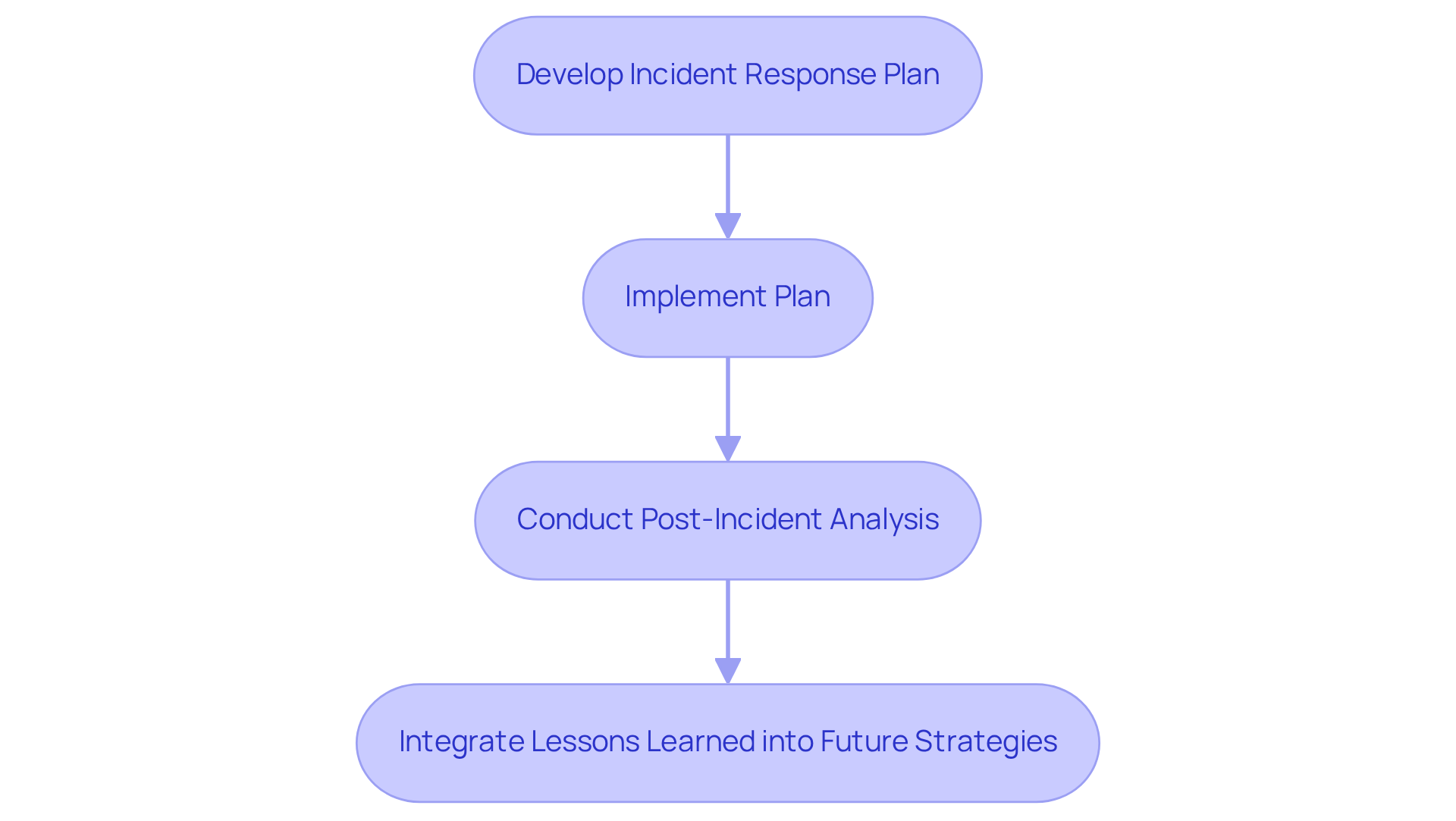
Incident Response Skills: Managing Cybersecurity Breaches
Incident response abilities are essential for security experts tasked with managing breaches and mitigating their impacts. Have you considered how a well-structured incident response plan can transform your organization's security posture? This involves not only developing and implementing comprehensive incident response plans but also conducting thorough post-incident analyses. By ensuring that lessons learned are integrated into future strategies, organizations can significantly enhance their resilience against future threats.
Effective incident response does more than just aid recovery from breaches; it actively strengthens a company's overall security posture. By identifying and addressing vulnerabilities, organizations can create a proactive defense against potential attacks. In today’s rapidly evolving threat landscape, investing in robust incident response capabilities is not just advisable - it's imperative.
To summarize, prioritizing incident response not only prepares your organization for immediate challenges but also fosters a culture of continuous improvement in security practices. Don't wait for a breach to highlight the need for a solid incident response strategy; take action now to safeguard your assets and reputation.
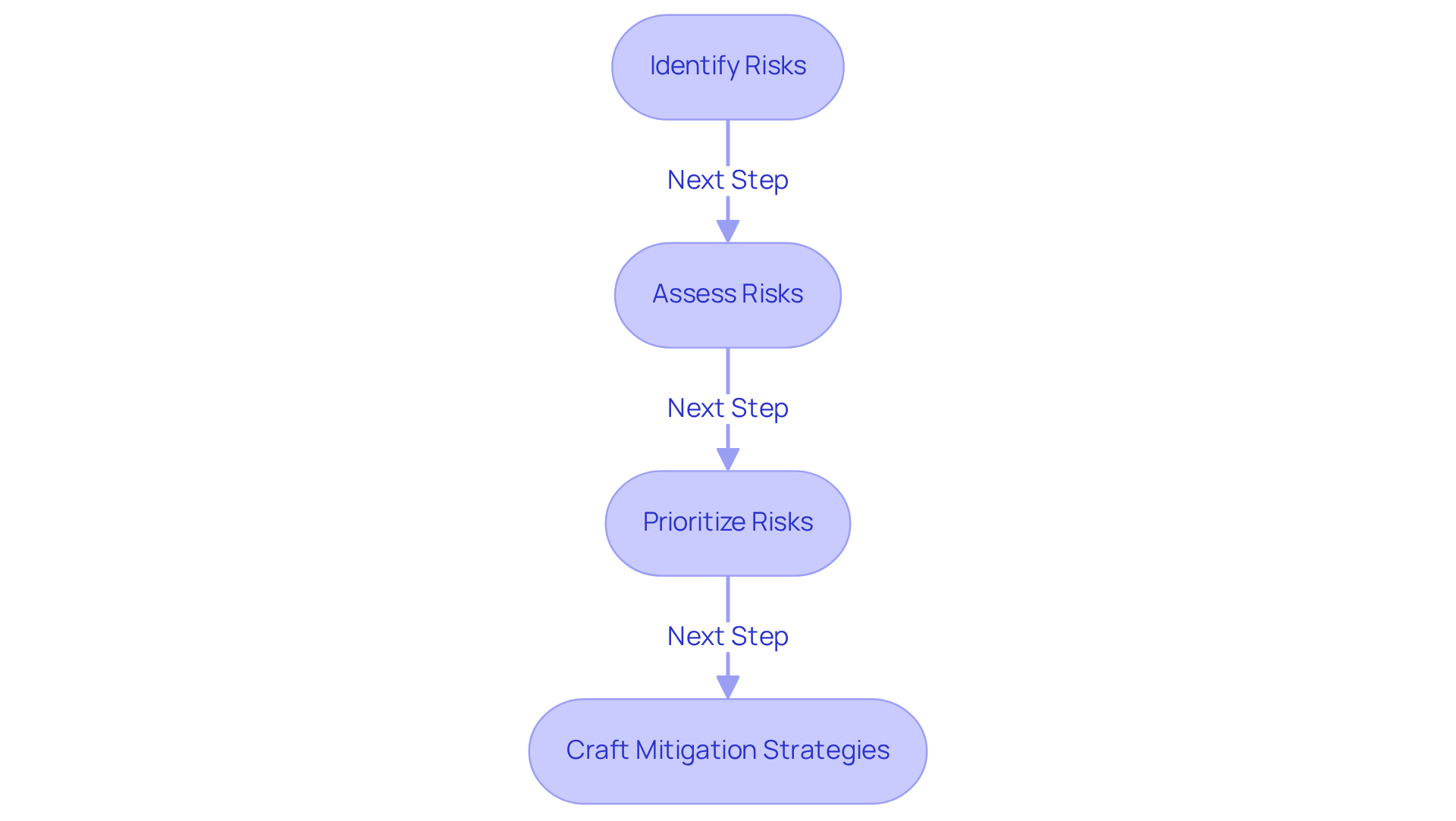
Risk Management Acumen: Identifying and Mitigating Threats
Risk management acumen is essential for identifying, assessing, and prioritizing risks linked to cybersecurity talent. To cultivate cybersecurity talent, professionals in this field must excel at conducting thorough risk assessments, analyzing potential impacts, and crafting effective mitigation strategies. This proactive approach is particularly vital for entities in the defense sector, where the repercussions of a breach can be catastrophic. By managing risks effectively, organizations can allocate resources more efficiently and enhance their cybersecurity talent to bolster their overall security posture.
But how can defense contractors navigate the complexities of compliance? Leveraging practical strategies and insights from the CMMC Info Hub can transform confusion into clarity. This empowers defense contractors to pursue CMMC compliance with confidence, ensuring they are well-prepared to meet the challenges ahead. In a landscape where security is paramount, taking these steps is not just advisable - it's imperative.
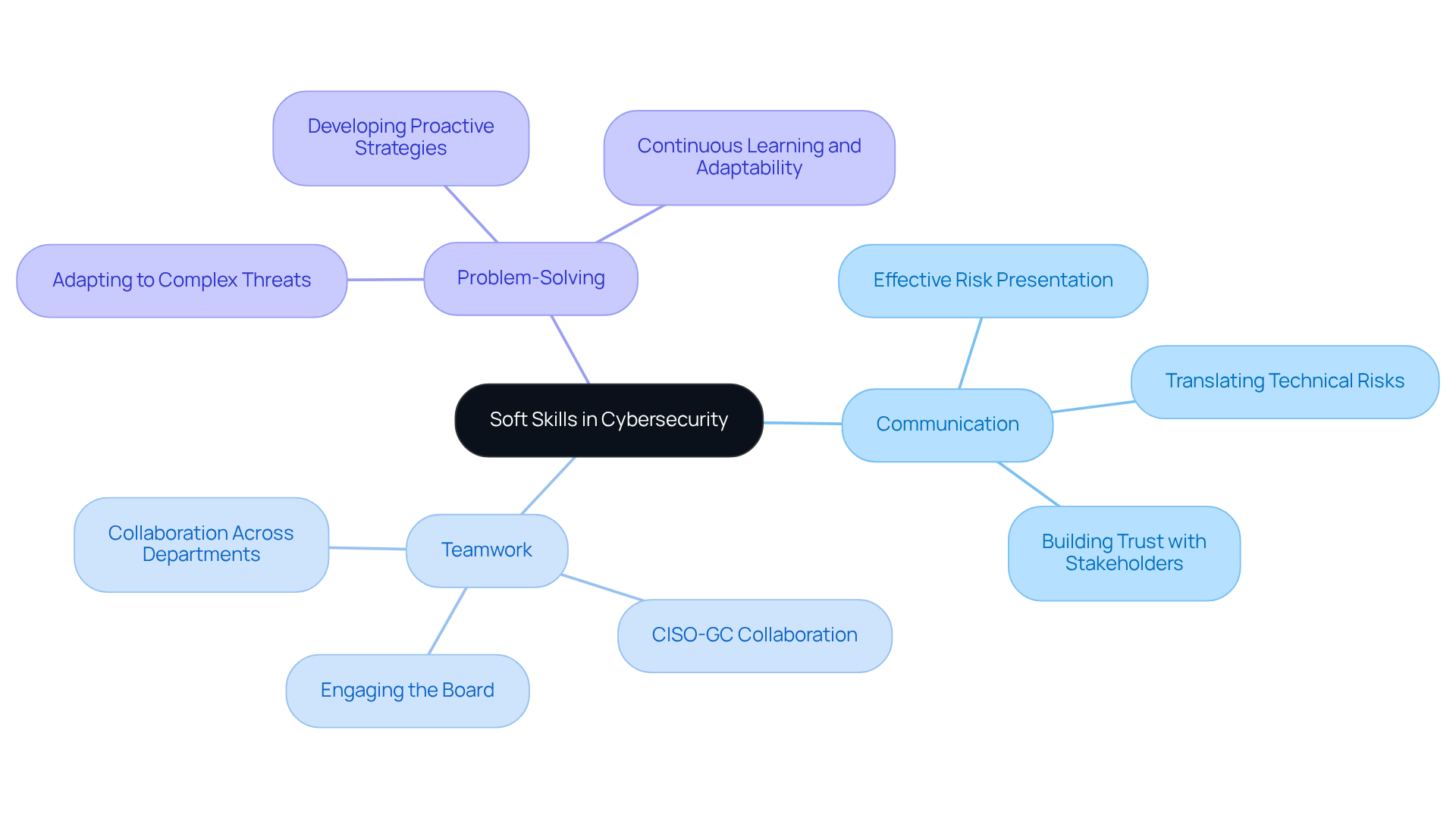
Soft Skills: Enhancing Communication and Teamwork in Cybersecurity
In the realm of online security, soft skills like communication, teamwork, and problem-solving are increasingly recognized as essential for success. Why is this the case? Experts must convey complex technical concepts to non-technical stakeholders effectively, ensuring that everyone understands the implications of security measures. This clear communication fosters collaboration across departments, which is crucial for addressing security challenges comprehensively.
Consider this: when Chief Information Security Officers (CISOs) and General Counsels (GCs) present cyber risks together, it not only validates their message but also builds trust with the board, driving decisive action. Andrew Stephens highlights that the collaboration between CISOs and GCs is vital in managing cyber risks effectively. By cultivating an environment of transparent communication and collaboration, companies can significantly enhance their security posture, leading to a more unified and efficient response to emerging challenges.
The impact of robust communication on team efficiency cannot be overstated. It enables security teams to operate more effectively and adaptively in an increasingly complex threat landscape. With 67 percent of organizations reporting at least one cyber-attack in the past year, the need for effective communication in attracting cybersecurity talent has never been more critical.
In summary, prioritizing soft skills in online security is not just beneficial; it is imperative for fostering a proactive security culture that enhances the development of cybersecurity talent. Companies that invest in these skills will find themselves better equipped to navigate the complexities of cyber threats.
Cloud Security Knowledge: Protecting Data in the Cloud
Cloud security knowledge is essential for safeguarding data in cloud environments, encompassing principles and practices that ensure robust security measures. Understanding shared responsibility models is a key component, as they delineate the security obligations of both cloud service providers and users. This understanding is crucial, especially as companies increasingly transition to the cloud; in fact, 80% of entities reported at least one cloud breach in the last 12 months. Professionals must be skilled in implementing encryption and configuring access controls to effectively protect sensitive information.
Recent trends reveal that 71% of organizations face a shortage of cybersecurity talent, especially skilled cloud security professionals, underscoring the urgent need for targeted training and development in this area. Effective cloud security implementations, particularly those adhering to the Cybersecurity Maturity Model Certification (CMMC), demonstrate the success of organized methods in protecting cloud infrastructures. The Ultimate Guide to Achieving CMMC Compliance offers practical strategies and peer insights that can assist defense contractors in navigating the complexities of CMMC requirements. By prioritizing cloud security training and incorporating best practices, businesses can enhance their operational integrity and protect sensitive information from emerging risks. Breaches are no longer rare events; they’ve become a regular occurrence in business. The question isn’t if a breach will happen, but how often.

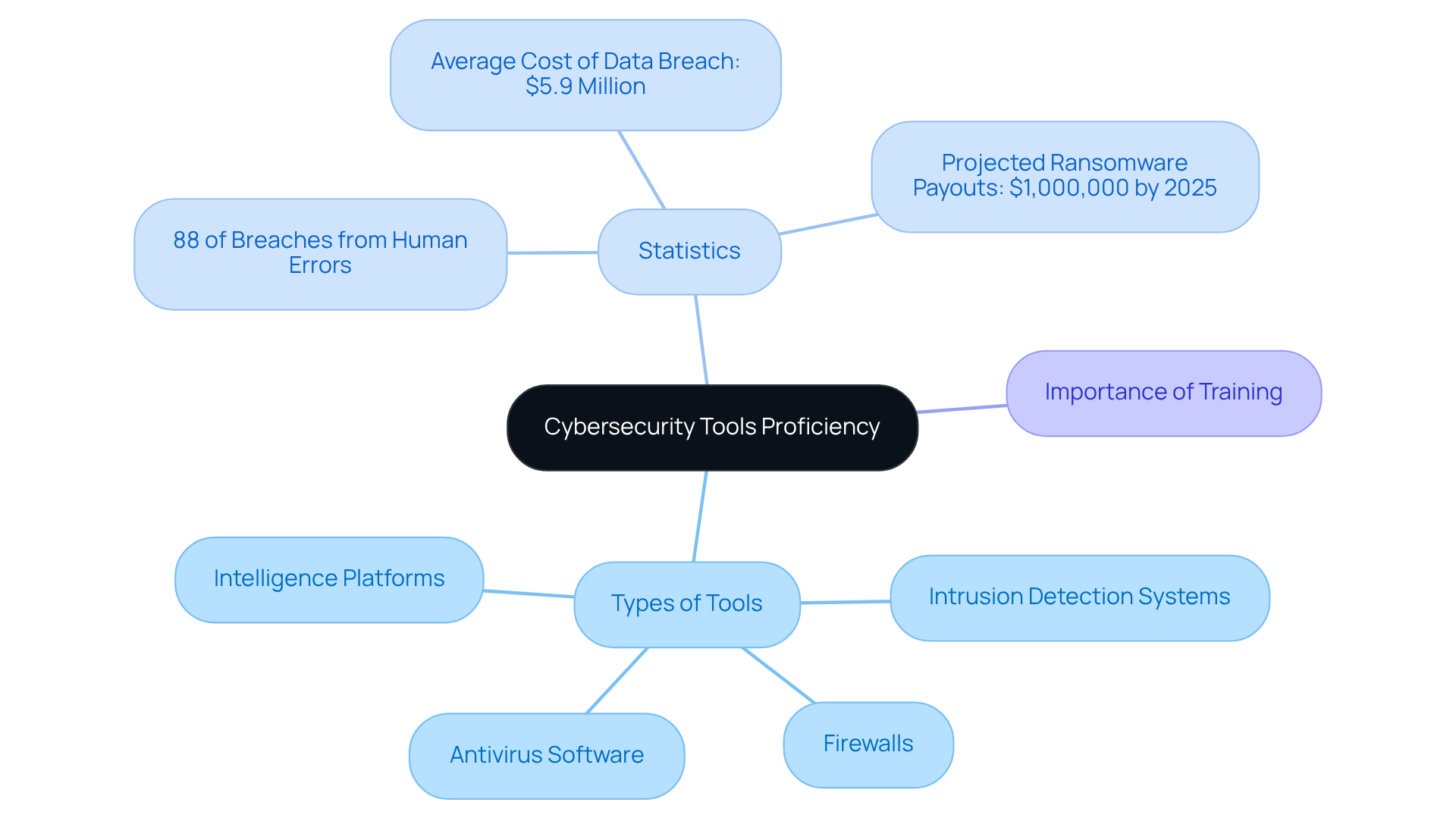
Cybersecurity Tools Proficiency: Utilizing Technologies for Defense
Skill in security tools is essential for anyone with cybersecurity talent who is responsible for safeguarding against online threats. Understanding intrusion detection systems, firewalls, antivirus software, and intelligence platforms significantly enhances an organization’s detection capabilities. By utilizing these technologies effectively, incident response procedures become more streamlined, ensuring compliance with security regulations.
Did you know that 88 percent of security breaches stem from human errors? This statistic underscores the necessity for ongoing training on the latest tools and technologies to cultivate cybersecurity talent and stay ahead of emerging threats. The financial implications are staggering; the average cost of a data breach in the financial sector is $5.9 million. This figure highlights the urgent need for robust security training.
Moreover, with ransomware payouts projected to reach around $1,000,000 by 2025, investing in skill development is not just advisable - it's crucial for strengthening defenses and protecting sensitive information. As Rob Sobers aptly states, "the time to change the culture toward enhanced digital security is now."
In summary, prioritizing the development of cybersecurity talent through security training and tool proficiency is vital for any organization aiming to mitigate risks and safeguard its assets.
Continuous Learning: Adapting to Evolving Cybersecurity Challenges
Ongoing education is essential for security experts navigating the rapidly changing threat landscape. How can professionals stay ahead? By keeping informed about the latest trends, technologies, and regulatory updates, they can enhance their incident response and compliance capabilities. Organizations must foster a learning culture by providing diverse training resources, workshops, and certifications.
Investing in ongoing education not only sharpens the skills of security teams but also significantly boosts their incident response effectiveness. In fact, entities that prioritize training report a remarkable 21% increase in profitability and a 20% increase in sales compared to those that do not. Furthermore, consider this: 94% of employees are more likely to stay with a company that invests in their career development. This statistic underscores the critical importance of nurturing a skilled workforce.
By implementing robust training programs, organizations can ensure their cybersecurity talent is well-equipped to tackle sophisticated threats and maintain compliance with industry standards. The time to act is now-prioritize ongoing education and watch your organization thrive.

Conclusion
The development of cybersecurity talent in defense is critical to ensuring robust protection against evolving threats. Organizations must focus on essential skills such as:
- AI proficiency
- Regulatory knowledge
- Network security expertise
- Incident response capabilities
These competencies are not just beneficial; they are necessary for compliance with frameworks like the Cybersecurity Maturity Model Certification (CMMC) and for maintaining a competitive edge in securing defense contracts.
Key insights reveal the importance of continuous learning and the integration of soft skills in fostering a proactive cybersecurity culture. As the landscape of cyber threats continues to evolve, organizations must prioritize training and development to cultivate a skilled workforce capable of implementing effective security measures. Did you know that significant talent shortages exist, with financial implications of security breaches underscoring the urgency of this need?
In conclusion, investing in cybersecurity talent development is not merely a strategic advantage; it is essential for safeguarding sensitive information and ensuring compliance with regulatory standards. Organizations must take decisive action to build and enhance their cybersecurity capabilities. Embracing ongoing education and collaboration will effectively address the challenges ahead. As the stakes grow higher, the commitment to developing skilled professionals will determine success in the defense sector’s fight against cyber threats.
Frequently Asked Questions
What is the CMMC Info Hub?
The CMMC Info Hub is a resource designed to help organizations achieve compliance with the Cybersecurity Maturity Model Certification (CMMC) by offering structured guidance, comprehensive plans, and practical strategies tailored to DoD security requirements.
Why is compliance with CMMC important?
Compliance with CMMC is essential for securing defense contracts, as new regulations will require verified cybersecurity adherence for specific contracts starting November 10, 2025. Non-compliance could lead to lost contract opportunities.
How can the CMMC Info Hub assist organizations?
The Info Hub provides insights from peers who have successfully navigated compliance, helping users gain clarity on requirements and improve their readiness for evaluations.
What are the recent updates regarding cybersecurity compliance?
Recent updates highlight the necessity for compliance with new cybersecurity regulations set to take effect on November 10, 2025, which will enforce verified adherence for certain defense contracts.
What evidence supports the effectiveness of the CMMC Info Hub?
Successful case studies indicate that contractors using the Info Hub report improved readiness and a clearer understanding of compliance requirements, which is crucial given the median SPRS score among contractors is significantly below the full compliance score.
How does artificial intelligence (AI) play a role in cybersecurity?
AI is becoming essential in digital security strategies as it can automate risk detection, analyze data for anomalies, and enhance incident response times, allowing organizations to proactively recognize and mitigate risks.
Why is regulatory knowledge important in cybersecurity?
A deep understanding of regulatory knowledge, such as NIST and ISO 27001 standards, is crucial for establishing controls and demonstrating compliance, which enhances an organization's credibility and helps avoid penalties.
What steps should organizations take to achieve CMMC compliance?
Organizations should adopt a comprehensive approach that includes regular policy maintenance, establishing a formal change process, maintaining version control, archiving previous editions, and communicating changes to all affected personnel.




