10 Essential Steps for the NYDFS Cybersecurity Checklist
Navigate the NYDFS cybersecurity checklist with these 10 essential compliance steps.

Introduction
Navigating the complex landscape of cybersecurity compliance presents a significant challenge, particularly for defense contractors who must adapt to the evolving requirements established by the New York Department of Financial Services (NYDFS). With cyber threats escalating and the stakes higher than ever, grasping the essential steps outlined in the NYDFS cybersecurity checklist is not merely advantageous - it is vital for protecting sensitive information and securing valuable contracts.
How can organizations effectively align their security practices with these stringent regulations while preparing for potential vulnerabilities? This article explores the ten essential steps that defense contractors must undertake to bolster their cybersecurity posture and achieve compliance. By transforming regulatory challenges into opportunities for resilience and growth, organizations can not only meet compliance standards but also enhance their overall security framework.
CMMC Info Hub: Your Guide to NYDFS Cybersecurity Compliance for Defense Contractors
CMMC Info Hub stands as an essential resource for defense contractors aiming to meet the New York Department of Financial Services (NYDFS) security regulations. This Hub not only provides organized support but also practical tactics that empower organizations to navigate the complexities of regulatory requirements effectively. For defense contractors, aligning security practices with both CMMC standards and the NYDFS cybersecurity checklist is crucial.
Why is this alignment so vital? It not only paves the way for securing defense contracts but also safeguards sensitive information amid rising cyber threats.
As digital security regulations continue to evolve, leveraging the insights and tools offered by CMMC Info Hub can significantly enhance a contractor's preparedness and resilience against compliance challenges. By utilizing these resources, contractors can stay ahead of the curve, ensuring they meet the necessary standards while protecting their operations and data.
Understand the Amended Cybersecurity Regulation: Key Requirements for Compliance
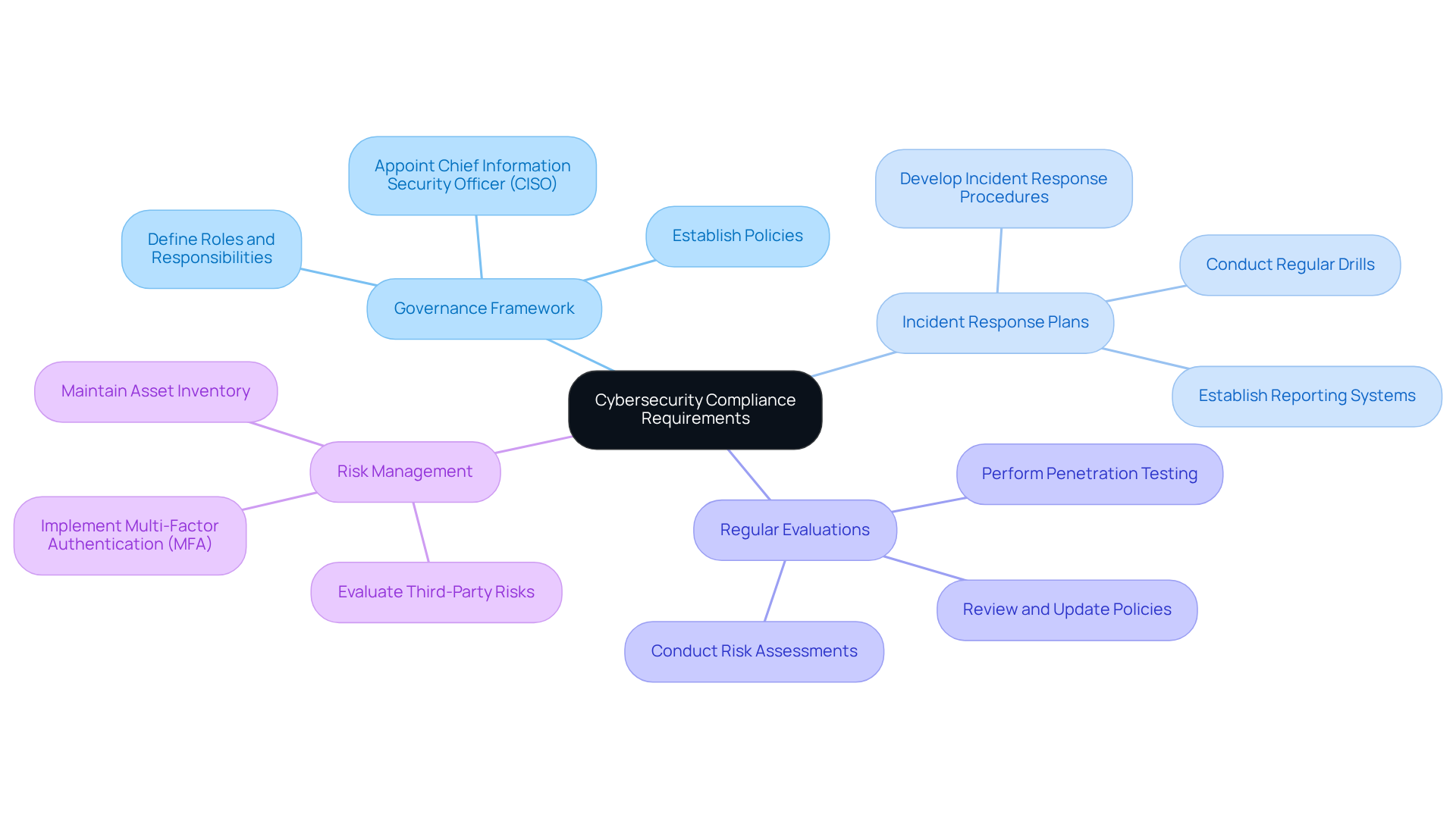
The revised NYDFS cybersecurity checklist on information security outlines several critical requirements for organizations, underscoring the necessity of a comprehensive security program. Are you aware of the vulnerabilities that could jeopardize your organization? Regular evaluations are essential to identify these vulnerabilities and ensure that security measures remain effective.
Organizations must establish a robust governance framework for information security, clearly defining roles and responsibilities for managing security threats. This framework is not just a formality; it’s a vital component of your security strategy. Additionally, having well-defined incident response plans and reporting systems is crucial for prompt action in the event of a security incident. These criteria not only help in adhering to regulations but also significantly reduce the risks associated with online security threats when following the NYDFS cybersecurity checklist.
Recent statistics reveal that entities implementing these comprehensive programs have experienced a marked improvement in their ability to manage and mitigate cyber risks. This underscores the importance of compliance with these regulations. By taking these steps, organizations can not only protect themselves but also enhance their overall security posture. Are you ready to take action and ensure your organization meets these essential requirements?
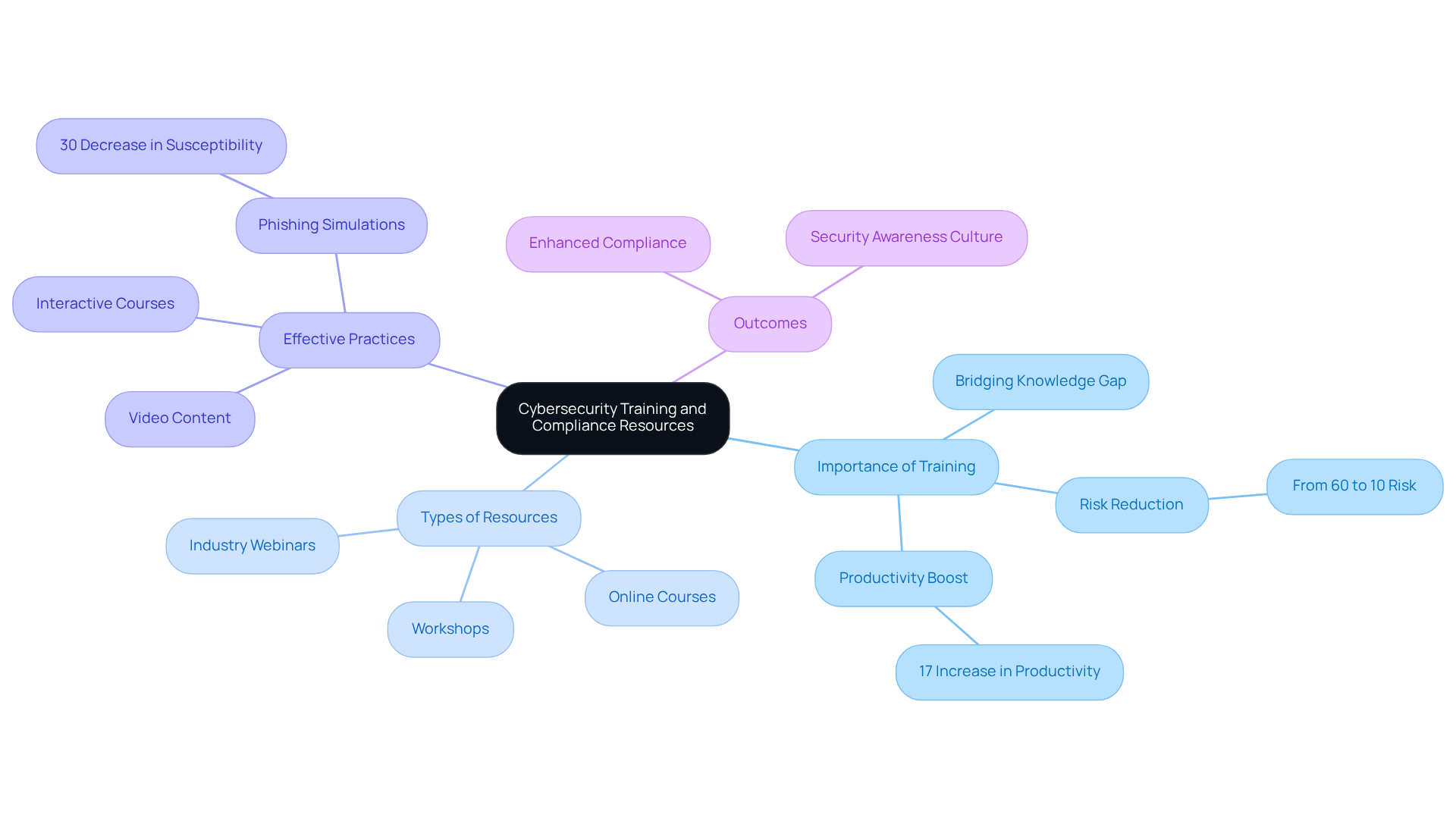
Utilize Training and Compliance Resources: Equip Your Team for Cybersecurity Success
Allocating funds for training and regulatory resources is essential for organizations aiming for success in digital security. Why is this so crucial? Regular training sessions that cover best practices, updates on regulatory changes, and simulations of potential cyber incidents are vital. Currently, 70% of companies report that their employees lack essential cybersecurity knowledge, revealing a significant gap in preparedness. To bridge this gap, organizations should leverage a variety of resources, including:
- Online courses
- Workshops
- Industry webinars
These tools can significantly enhance understanding of compliance requirements and individual roles in maintaining a secure environment.
Effective training practices include engaging formats such as:
- Interactive courses
- Video content
These have been proven to improve retention and application of knowledge. Moreover, regular training can reduce risk from 60% to 10% within the first 12 months, showcasing the effectiveness of comprehensive training programs. Incorporating phishing simulations can further help employees recognize and respond to real threats, decreasing susceptibility to attacks by up to 30%. Additionally, organizations that provide essential training experience a 17% boost in productivity, as employees become better equipped to tackle challenges.
By prioritizing thorough training initiatives, companies not only enhance their compliance efforts but also foster a culture of security awareness that is crucial for lasting success. To further improve clarity in adherence efforts, organizations should routinely assess training effectiveness and adapt programs to meet evolving regulatory requirements.
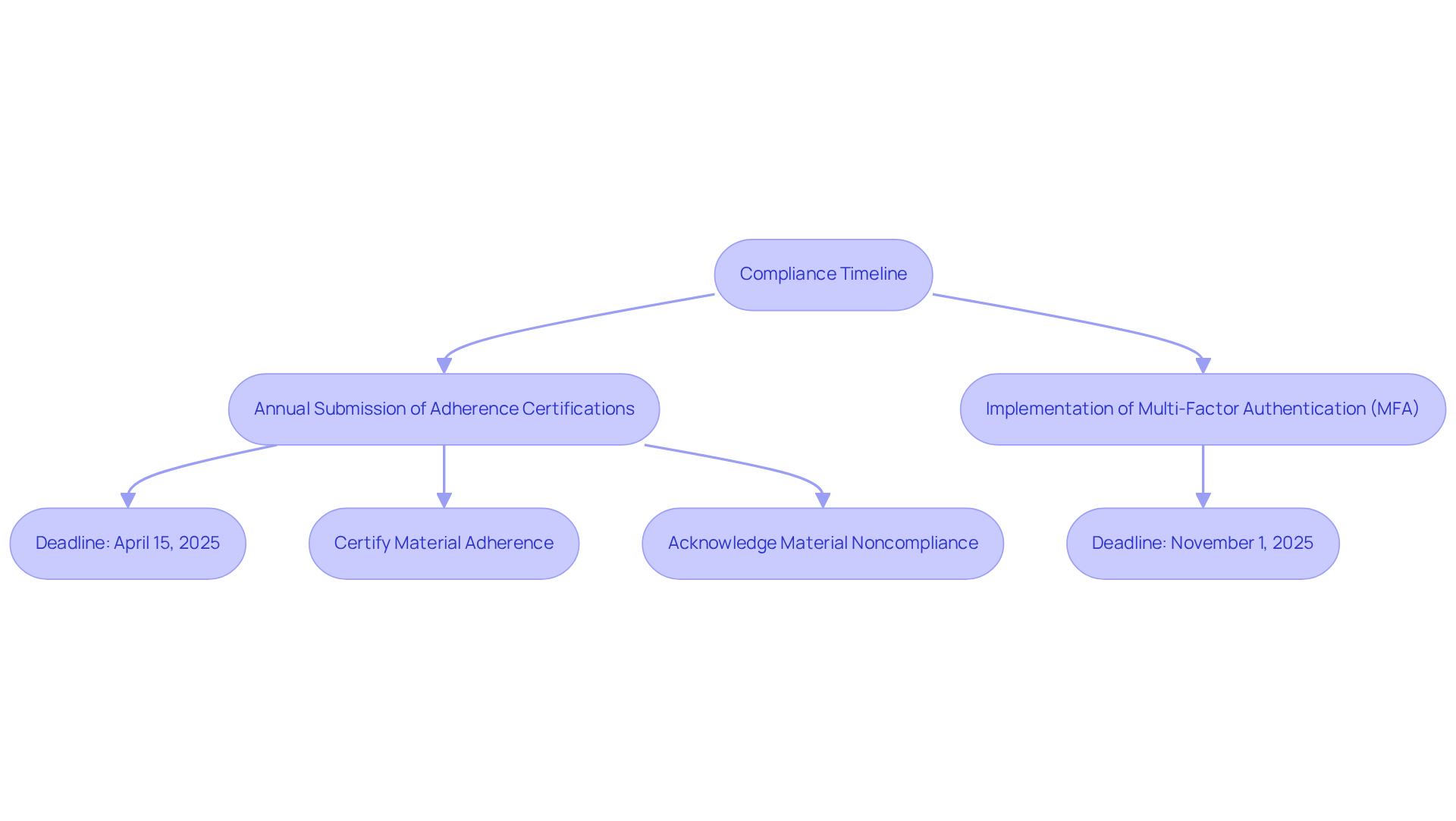
Track Key Compliance Dates: Stay Ahead of Cybersecurity Deadlines
Organizations must remain vigilant regarding critical deadlines associated with the NYDFS cybersecurity checklist. Key deadlines include the annual submission of adherence certifications by April 15, 2025. Covered entities must either certify material adherence or acknowledge material noncompliance. Additionally, the implementation of multi-factor authentication (MFA) is required by November 1, 2025.
To effectively manage these timelines, utilizing regulatory calendars and project management tools is essential. These resources not only help monitor important dates but also ensure that all necessary actions are executed promptly, minimizing the risk of non-compliance and potential penalties. Furthermore, it is crucial to retain all supporting records for the annual certification for five years, underscoring the importance of comprehensive documentation.
For defense contractors, maintaining a detailed compliance calendar can significantly streamline the process of adhering to the NYDFS cybersecurity checklist. This proactive approach not only enhances compliance but also strengthens their security posture, safeguarding sensitive information. Are you prepared to take the necessary steps to ensure compliance and protect your organization?
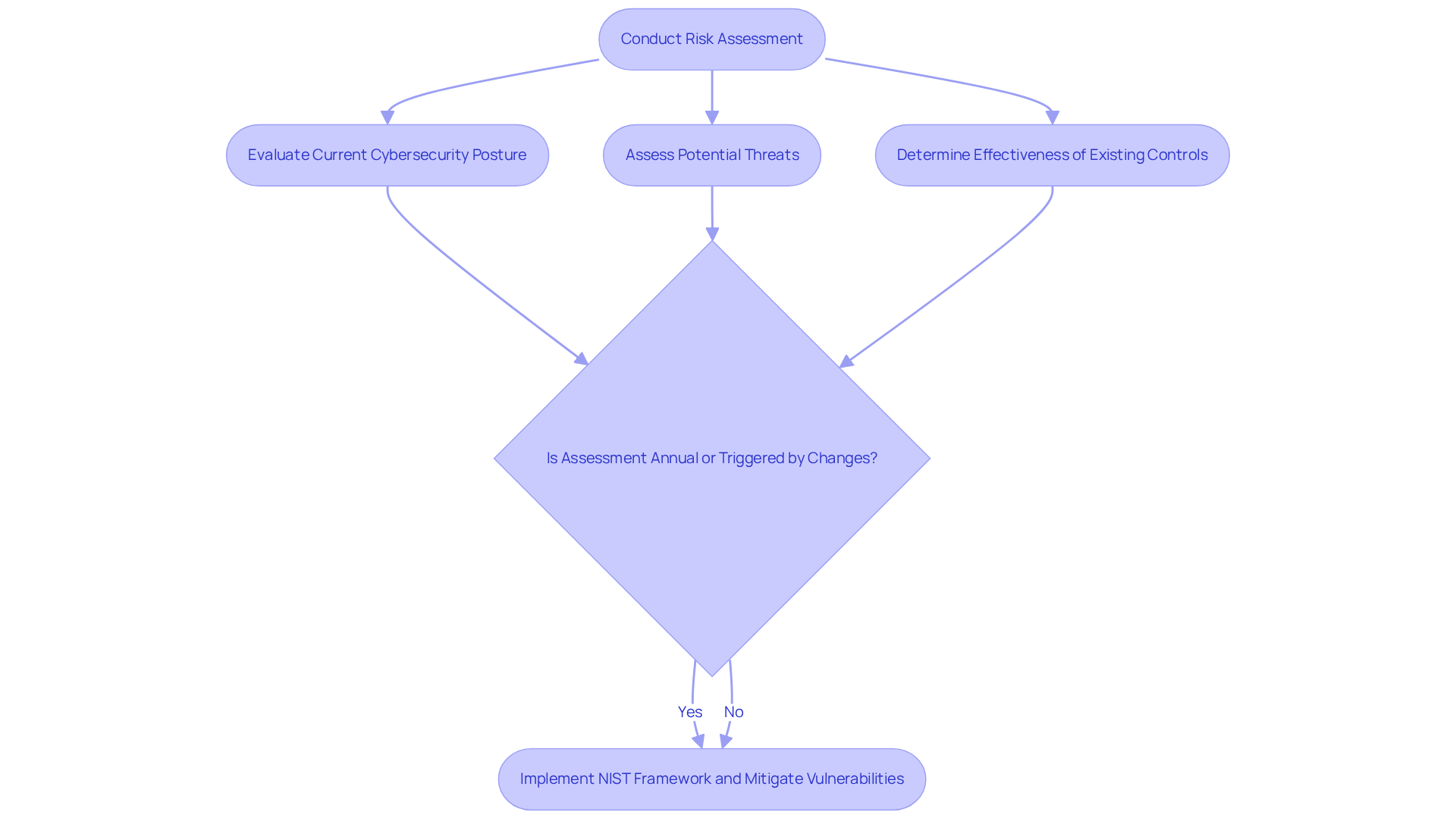
Perform a Risk Assessment: Identify and Mitigate Cybersecurity Vulnerabilities
Conducting a thorough risk evaluation is vital for identifying and mitigating security vulnerabilities. Organizations must evaluate their current [cybersecurity posture](https://thehackernews.com/search/label/Risk Assessment), assess potential threats, and determine the effectiveness of existing controls. This process should occur at least once a year or whenever substantial changes arise within the entity. Notably, around 39% of organizations employ the NIST framework for their evaluations, showcasing its broad recognition as a best practice in the sector. Furthermore, 24% of entities conducted assessments more than four times annually, indicating a rising trend towards more frequent evaluations.
Cybersecurity experts emphasize the significance of these evaluations. One expert stated, "Annual evaluations are essential for comprehending the changing threat environment and ensuring that controls remain effective." This perspective is echoed by numerous organizations that have successfully integrated the NIST framework into their management strategies, allowing them to systematically address vulnerabilities and enhance their overall security posture. Moreover, with research indicating that approximately 90% of cyber incidents are linked to human errors, prioritizing vulnerability assessments becomes even more crucial. By doing so, companies can not only meet regulatory standards but also foster a culture of proactive information security management.
Establish Cybersecurity Governance: Create a Framework for Effective Management
Creating a strong governance framework for digital security is not just important; it’s essential for effectively managing risks, particularly in the defense sector. This framework must clearly outline roles and responsibilities, establish thorough policies and procedures, and ensure that security initiatives align with the organization’s strategic objectives. How can organizations ensure oversight and accountability in their security initiatives? Consistent reporting to upper management and the board of directors is key.
Organizations that prioritize governance frameworks often see a significant decrease in security incidents. For instance, while 75% of organizations reported experiencing at least one ransomware attack last year, those with robust governance frameworks are better equipped to mitigate such threats. Moreover, as Rob Sobers points out, "90% of cybersecurity breaches are attributed to human error," highlighting the critical role of training and awareness programs within the governance structure.
Effective governance not only mitigates risks but also enhances overall organizational resilience. By mastering CMMC requirements and implementing necessary controls, entities can turn confusion into clarity, ensuring they are well-prepared for compliance. Industry leaders increasingly recognize digital security as a vital business facilitator, with over 39% of them agreeing on its significance. By fostering a culture of security and integrating cybersecurity considerations into every business decision, organizations can navigate the complex threat landscape more effectively and safeguard their assets.

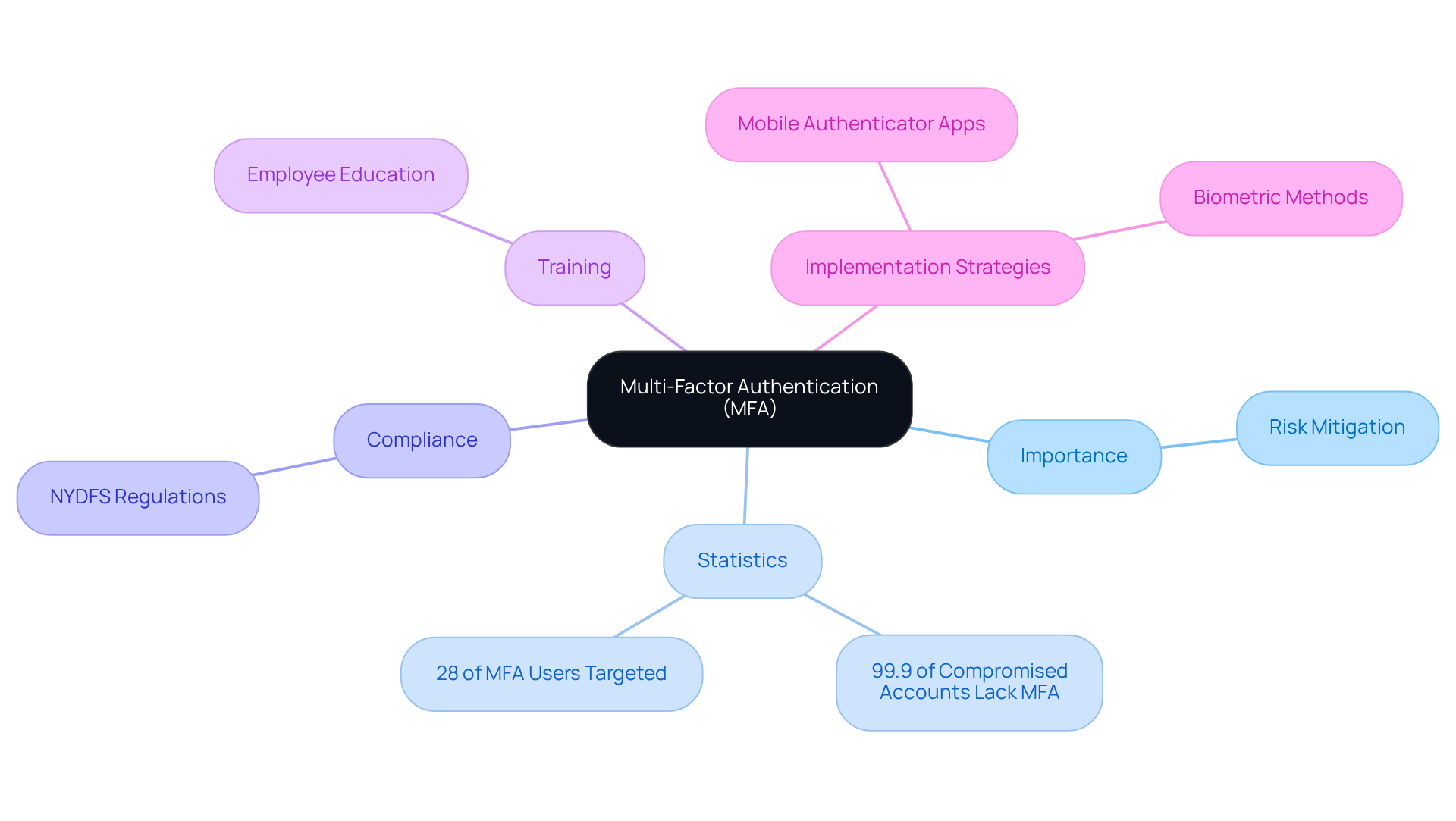
Implement Multi-Factor Authentication: Strengthen Access Security
Implementing multi-factor authentication (MFA) is essential for enhancing access security within enterprises. Why is MFA so crucial? By requiring users to provide two or more verification factors - such as passwords, mobile device codes, or biometric data - MFA significantly mitigates the risk of unauthorized access. In fact, statistics reveal that over 99.9% of compromised accounts lack MFA protection, underscoring its importance in preventing security breaches.
However, it’s noteworthy that 28% of users who have enabled MFA are still targeted by attackers. This highlights that while MFA is crucial, it is not infallible. To comply with NYDFS regulations, organizations must enforce MFA for all remote access and sensitive systems as outlined in the NYDFS cybersecurity checklist. Additionally, training employees on the significance of MFA and providing clear instructions on its use are crucial steps in fostering a security-conscious culture.
Given that 62% of small to mid-sized organizations do not implement MFA, comprehensive training and implementation strategies are vital. Effective MFA strategies, such as using mobile authenticator applications and introducing backup authentication alternatives, can further improve adherence efforts and safeguard sensitive information from advancing cyber threats. Organizations should also consider assessing their current MFA practices and integrating biometric methods to strengthen their security posture.
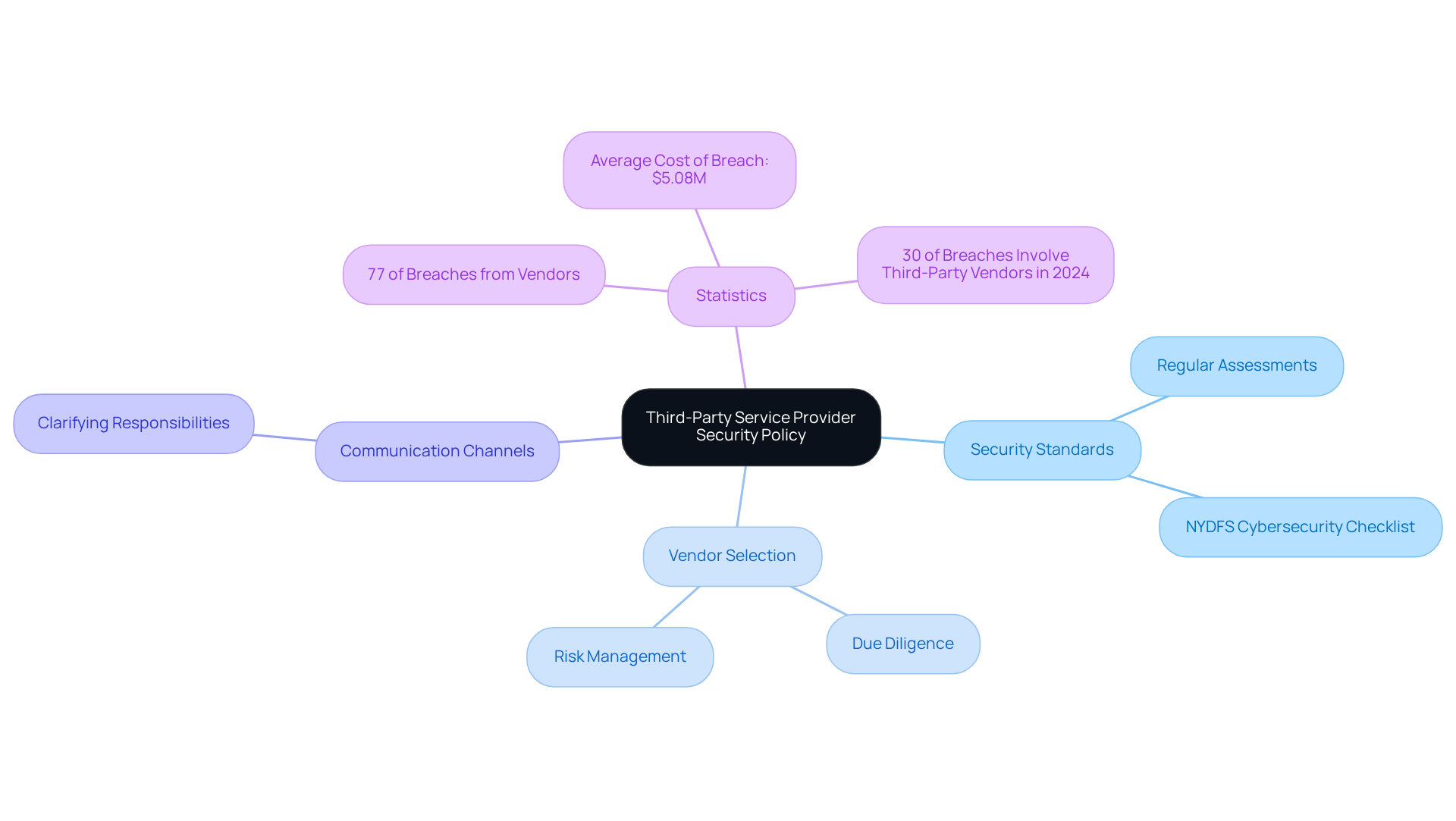
Create a Third-Party Service Provider Security Policy: Safeguard Your Supply Chain
Establishing a robust third-party service provider security policy is not just important; it’s essential for safeguarding your supply chain. This policy must clearly define the security standards that vendors are required to meet, including the necessity for regular security assessments and adherence to the NYDFS cybersecurity checklist. Organizations should conduct thorough due diligence when selecting vendors, ensuring they meet these critical security requirements.
Moreover, creating efficient communication channels is vital to clarify security responsibilities among all parties involved. Did you know that 77% of security breaches originate from third-party vendors? Recent findings highlight that in 2024, 30% of breaches will involve a third-party vendor-twice as much as the previous year. This statistic underscores the importance of implementing stringent security policies. Additionally, consider the financial implications: the average cost of a third-party breach exceeds $5.08 million.
By conducting thorough vendor security evaluations and maintaining appropriate internal risk management measures, organizations can significantly reduce risks and enhance their overall security posture. It’s time to take action-ensure your vendor security policies are robust and effective.
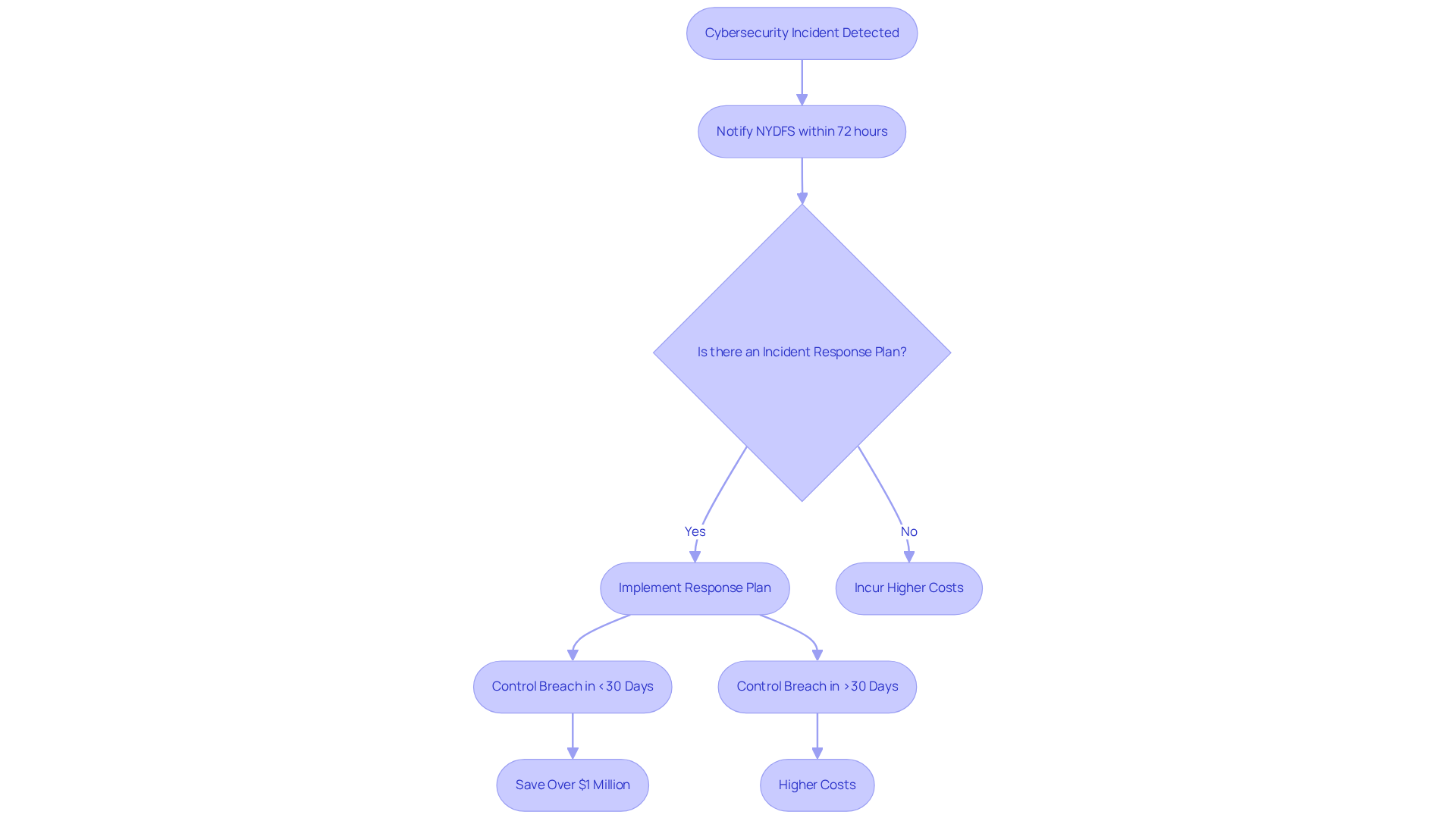
Report Cybersecurity Incidents: Ensure Timely Response and Compliance
Organizations must establish clear procedures for reporting security incidents as outlined in the NYDFS cybersecurity checklist to ensure a prompt response and compliance with NYDFS regulations. Why is this crucial? Under the amended guidelines, covered entities are mandated to notify the NYDFS within 72 hours of confirming a cybersecurity incident. Alarmingly, the average time to detect a breach is approximately 197 days, and the average breach lifecycle can extend to 258 days for those lacking a formal strategy. This underscores the urgency of swift reporting.
Developing a comprehensive incident response plan is essential. Such a plan should outline communication protocols and delineate responsibilities, which are crucial for effective incident management. Not only do these plans aid in compliance, but they also significantly lower expenses. In fact, entities without an incident response plan face breach costs that are $2.66 million greater than those with a defined response structure.
Prompt incident reporting is vital. Entities that can control a breach in under 30 days save over $1 million compared to those that take longer. By prioritizing these elements, companies can enhance their security posture and ensure compliance with the NYDFS cybersecurity checklist. Are you ready to take action and strengthen your incident response strategy?
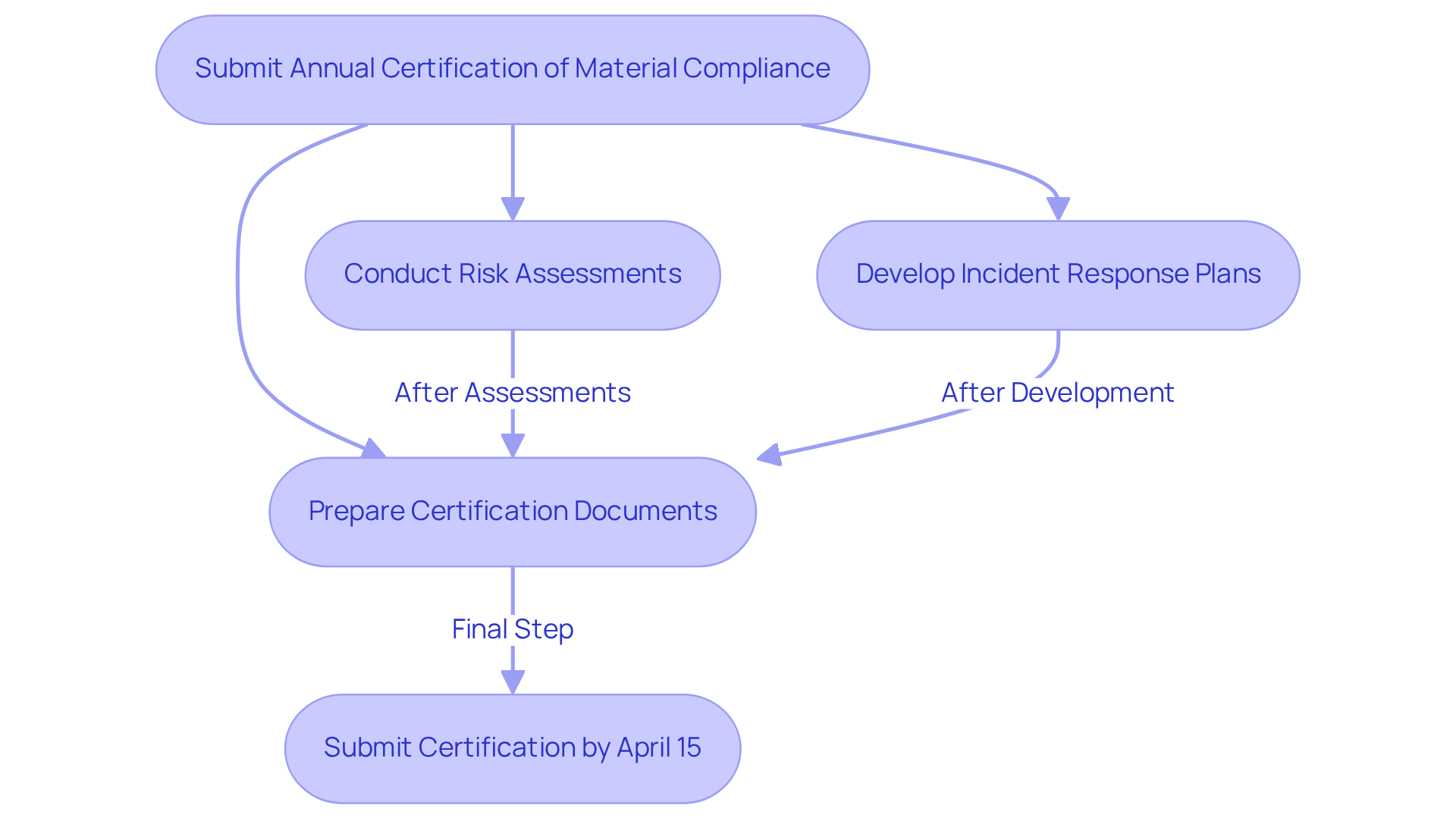
Submit Annual Certification of Material Compliance: Confirm Your Cybersecurity Commitment
Submitting an annual Certification of Material Compliance is not just a regulatory requirement; it’s a critical commitment for entities governed by NYDFS regulations. Due by April 15 each year, this certification acts as a formal declaration that the entity has met the stringent security standards mandated by the NYDFS. Have you considered how your organization presents its certification documents? A significant number of enterprises effectively showcase their compliance with the NYDFS cybersecurity checklist, reflecting a strong dedication to robust cybersecurity practices.
Comprehensive documentation plays a pivotal role in this process. It not only demonstrates adherence to regulations but also includes essential components such as:
- Risk assessments
- Incident response plans
Regulatory specialists emphasize that thorough documentation is a cornerstone of effective governance management. It ensures that entities can validate their compliance with legal requirements.
Successful organizations that have adeptly navigated this certification process emphasize the importance of a structured approach to compliance through the NYDFS cybersecurity checklist. This reinforces the necessity for all entities to prioritize their annual certification efforts. Are you ready to take the necessary steps to ensure your organization meets these critical standards?
Conclusion
Navigating the NYDFS cybersecurity checklist is not just a regulatory obligation; it’s a vital commitment to protecting sensitive information and bolstering organizational resilience against cyber threats. For defense contractors, aligning security practices with both the NYDFS and CMMC standards is crucial. This alignment not only ensures compliance but also secures essential defense contracts.
To achieve compliance, organizations must take several essential steps:
- Establish a robust governance framework
- Conduct regular risk assessments
- Implement multi-factor authentication
- Provide thorough training for all employees
Each of these components is integral to crafting a comprehensive cybersecurity strategy that meets regulatory requirements and mitigates risks associated with cyber incidents. Moreover, timely reporting and maintaining an organized compliance calendar are critical practices that significantly enhance an organization’s ability to respond effectively to incidents.
In today’s increasingly complex digital landscape, prioritizing cybersecurity transcends mere compliance; it’s about cultivating a culture of security awareness and proactive risk management. Organizations must act decisively to implement these essential steps, ensuring they are prepared for upcoming deadlines and equipped to handle potential threats. By doing so, they not only safeguard their operations and sensitive data but also contribute to a more secure environment for all stakeholders involved.
Frequently Asked Questions
What is the purpose of the CMMC Info Hub?
The CMMC Info Hub serves as a resource for defense contractors to help them comply with New York Department of Financial Services (NYDFS) security regulations, providing organized support and practical tactics for navigating regulatory complexities.
Why is alignment with CMMC standards and NYDFS cybersecurity checklist important for defense contractors?
This alignment is crucial for securing defense contracts and protecting sensitive information from rising cyber threats.
How can the CMMC Info Hub enhance a contractor's preparedness?
By leveraging the insights and tools offered by the CMMC Info Hub, contractors can improve their readiness and resilience against compliance challenges, ensuring they meet necessary standards while safeguarding their operations and data.
What are the key requirements outlined in the amended NYDFS cybersecurity regulation?
Key requirements include establishing a comprehensive security program, a robust governance framework for information security, clearly defined roles and responsibilities, and well-defined incident response plans and reporting systems.
Why are regular evaluations of vulnerabilities important for organizations?
Regular evaluations are essential to identify vulnerabilities and ensure that security measures remain effective, thereby protecting the organization from online security threats.
What benefits do organizations experience by implementing comprehensive cybersecurity programs?
Organizations that implement comprehensive programs have shown marked improvements in their ability to manage and mitigate cyber risks, enhancing their overall security posture.
Why is training and regulatory resource allocation important for organizations?
Allocating funds for training and regulatory resources is crucial for success in digital security, as it helps employees stay informed about best practices, regulatory changes, and potential cyber incidents.
What types of training resources can organizations utilize to improve cybersecurity knowledge?
Organizations can utilize online courses, workshops, and industry webinars to enhance understanding of compliance requirements and individual roles in maintaining a secure environment.
How effective are interactive training formats in improving cybersecurity knowledge retention?
Engaging formats like interactive courses and video content have been proven to improve retention and application of knowledge among employees.
What impact does regular training have on organizational risk and productivity?
Regular training can reduce cybersecurity risk from 60% to 10% within the first 12 months and can lead to a 17% boost in productivity as employees become better equipped to tackle challenges.
How can organizations assess the effectiveness of their training initiatives?
Organizations should routinely assess training effectiveness and adapt programs to meet evolving regulatory requirements to ensure ongoing compliance and security awareness.




