10 Key Components of a Cybersecurity Risk Assessment Framework
Discover essential elements of a cybersecurity risk assessment framework for effective protection.

Introduction
In an era where cyber threats are more prevalent than ever, organizations are confronted with the formidable task of protecting their digital assets. With nearly half of all cyberattacks aimed at small-to-medium enterprises, the need for a comprehensive cybersecurity risk assessment framework is more pressing than ever. This article explores ten essential components that not only bolster security measures but also ensure compliance with the evolving standards established by the Cybersecurity Maturity Model Certification (CMMC). As companies navigate the intricate landscape of risk management, one critical question emerges: how can they effectively pinpoint vulnerabilities and implement robust strategies to mitigate potential threats?
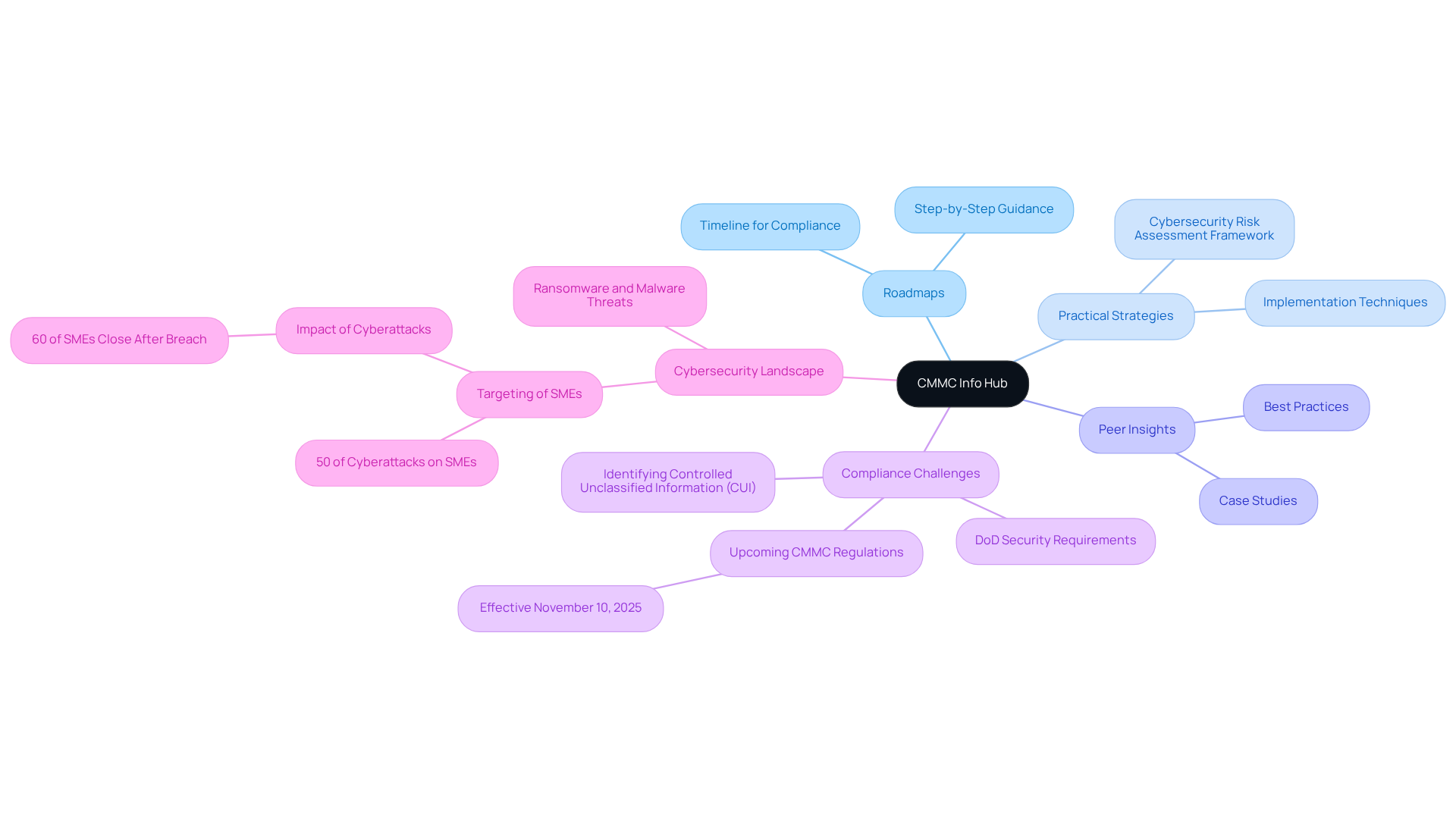
CMMC Info Hub: Comprehensive Guidance for Cybersecurity Maturity Model Certification
CMMC Info Hub stands as an essential resource for organizations aiming to achieve compliance with the Cybersecurity Maturity Model Certification (CMMC). This platform offers organized support, featuring comprehensive roadmaps, practical strategies, and peer insights that guide users through the complexities of DoD security requirements. Did you know that nearly 50% of all cyberattacks target small-to-medium enterprises (SMEs)? This statistic underscores the urgent need for robust protective measures.
By transforming confusion into clarity, the cybersecurity risk assessment framework provided by CMMC Info Hub empowers entities with the confidence necessary to tackle compliance challenges head-on. Leveraging the information provided by CMMC Info Hub allows organizations to streamline their compliance processes and strengthen their cybersecurity risk assessment framework. This is crucial for meeting the stringent criteria required for securing defense contracts, especially with new CMMC regulations mandating verified security compliance set to take effect on November 10, 2025.
In summary, CMMC Info Hub not only simplifies the compliance journey but also fortifies your organization against potential cyber threats. Don't wait - take action now to ensure your readiness for the evolving landscape of cybersecurity compliance.
Cybersecurity Risk Assessments: Identifying Vulnerabilities and Threats
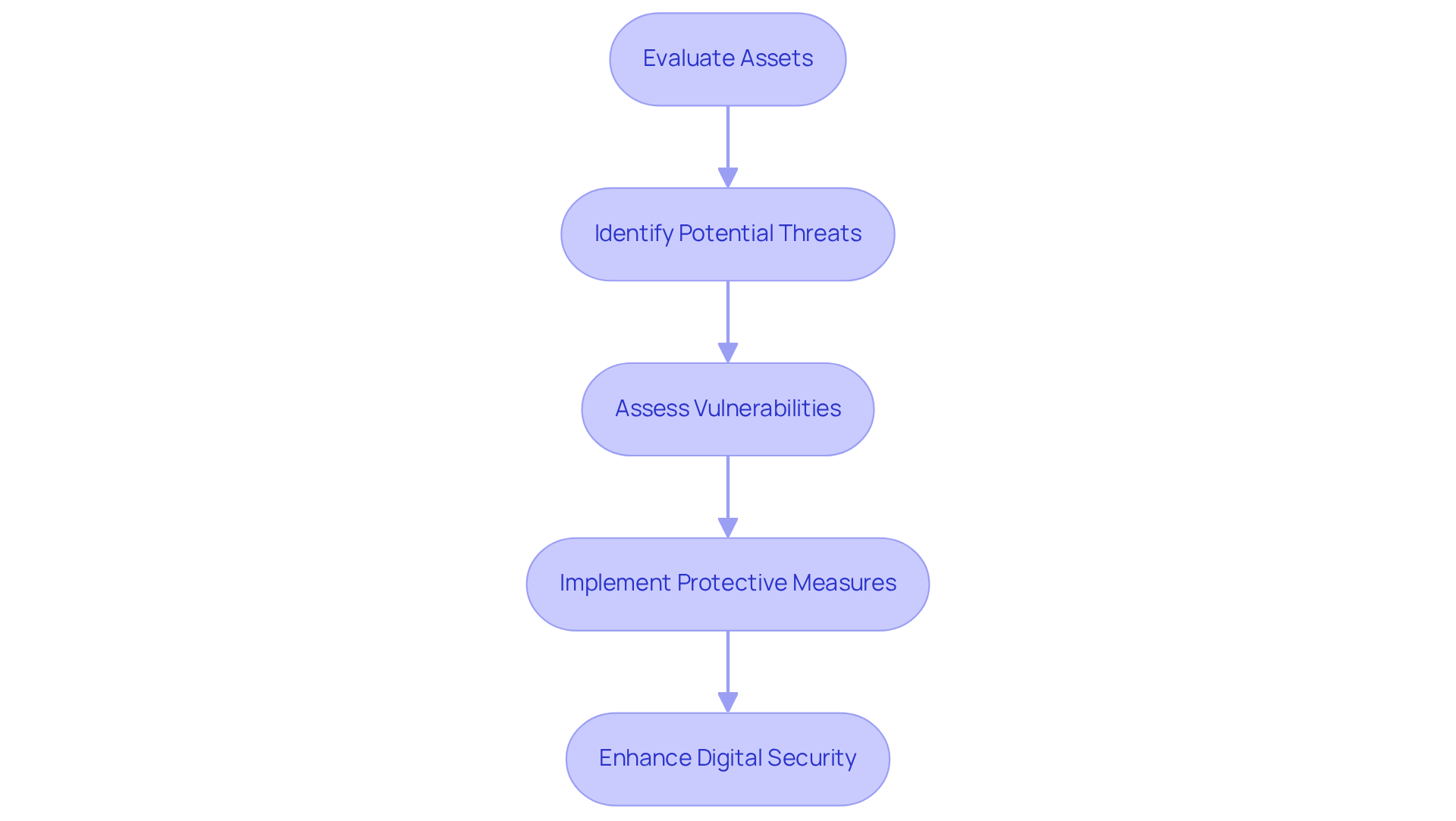
The cybersecurity risk assessment framework is crucial for identifying weaknesses and threats within a company's infrastructure. This systematic process involves evaluating assets, pinpointing potential threats, and assessing vulnerabilities within a cybersecurity risk assessment framework that could be exploited. Have you considered how often your organization conducts these evaluations? Regular threat assessments within a cybersecurity risk assessment framework not only help prioritize protective measures but also enable companies to allocate resources efficiently to mitigate identified vulnerabilities. By doing so, organizations can significantly enhance their overall digital resilience.
In today's digital landscape, the stakes are high. Companies that neglect cybersecurity evaluations risk exposing themselves to severe threats. Therefore, it’s imperative to integrate these evaluations into your regular cybersecurity risk assessment framework. By prioritizing cybersecurity, you not only protect your assets but also build trust with your clients and stakeholders.
Security Controls: Essential Measures for Risk Mitigation
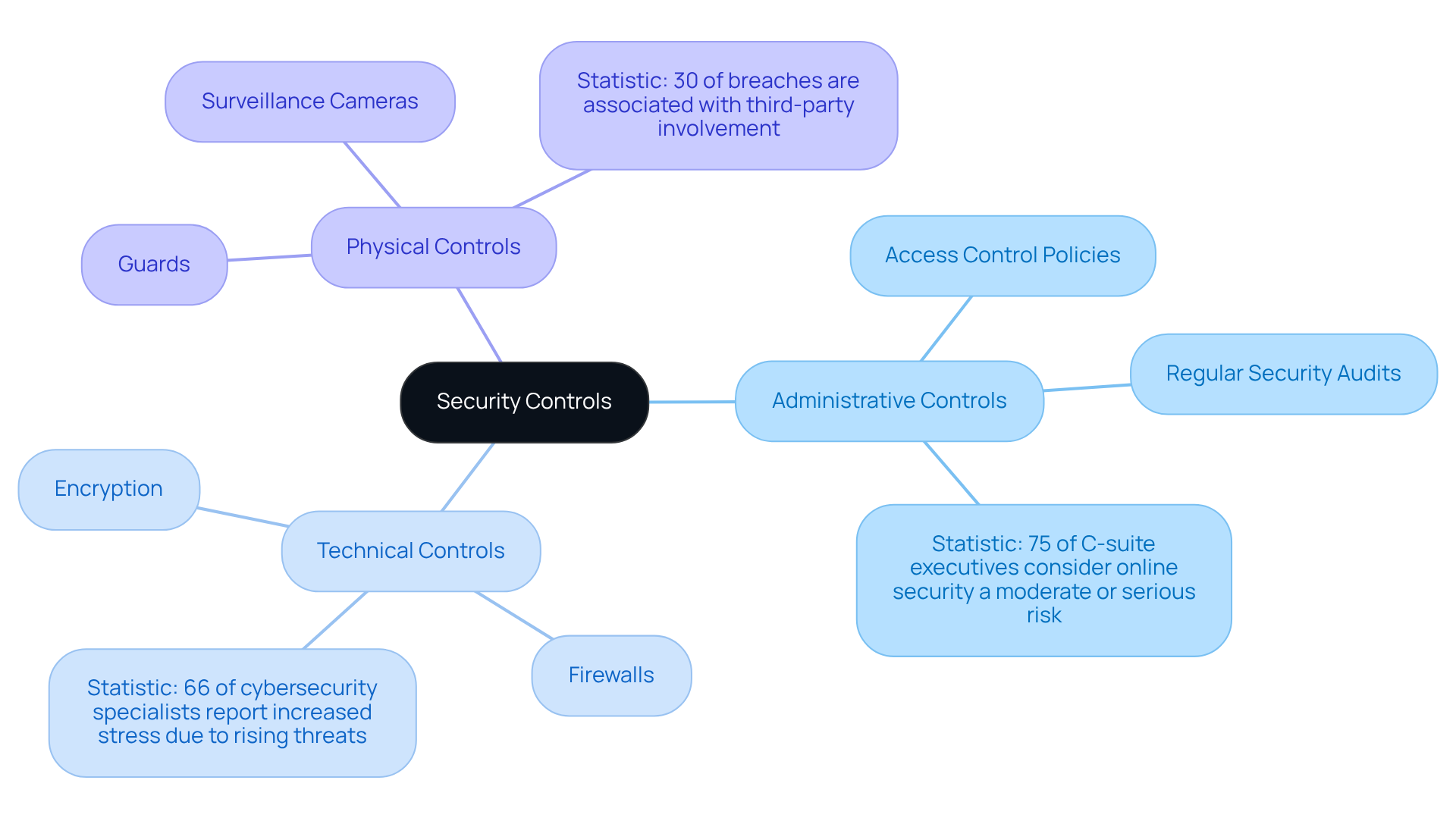
Security controls are essential actions that entities must adopt within the cybersecurity risk assessment framework to effectively reduce risks identified during the cybersecurity evaluation phase. These controls fall into three primary categories: administrative, technical, and physical.
-
Administrative Controls: These consist of policies and procedures that regulate safety practices within a company. For instance, access control policies ensure that only authorized personnel can access sensitive information. Regular security audits are also vital, as they assist entities in identifying vulnerabilities and enhancing their cybersecurity risk assessment framework. Did you know that 75% of C-suite executives consider online security a moderate or serious risk? This statistic underscores the need for robust administrative measures.
-
Technical Controls: This category encompasses technological solutions designed to protect systems and data. Examples include encryption, which secures data in transit and at rest, and firewalls that monitor and control incoming and outgoing network traffic. As we look ahead to 2025, entities are increasingly adopting advanced technical controls. In fact, 66% of cybersecurity specialists report that their roles have become more stressful due to rising threats.
-
Physical Controls: These measures protect the physical infrastructure of an organization. Instances include guards, surveillance cameras, and secure entry points to facilities. The implementation of physical controls is essential, especially in defense contracting, where sensitive information is often at risk. A significant statistic indicates that 30% of breaches are associated with third-party involvement, highlighting the necessity of thorough protective measures.
By creating a strong structure of protective measures, entities can greatly lower their susceptibility to cyber threats and ensure adherence to the cybersecurity risk assessment framework and CMMC requirements. As Jacob Fox, a specialist in online protection, observes, "The changing environment of digital dangers requires a proactive strategy for safeguarding, incorporating administrative, technical, and physical measures to protect sensitive information.
Continuous Monitoring: Ensuring Ongoing Security Effectiveness
Ongoing surveillance stands as a pivotal strategy in cybersecurity, empowering organizations to assess their protective measures proactively and respond to threats in real-time. This approach involves the continuous monitoring of network traffic, system logs, and user activities to identify anomalies that may signal a security breach.
Key activities for achieving CMMC compliance include:
- Conducting regular vulnerability scans to pinpoint weaknesses.
- Implementing timely patch management for systems and applications.
- Reviewing audit logs consistently for signs of incidents.
Moreover, organizations should monitor systems for any deviations from established configuration baselines, perform routine assessments of user access to ensure appropriateness, and maintain vigilant observation for potential incidents. By adopting ongoing surveillance, companies can ensure their protective measures remain effective and adapt to evolving threats.

Incident Response Plans: Preparing for Security Breaches
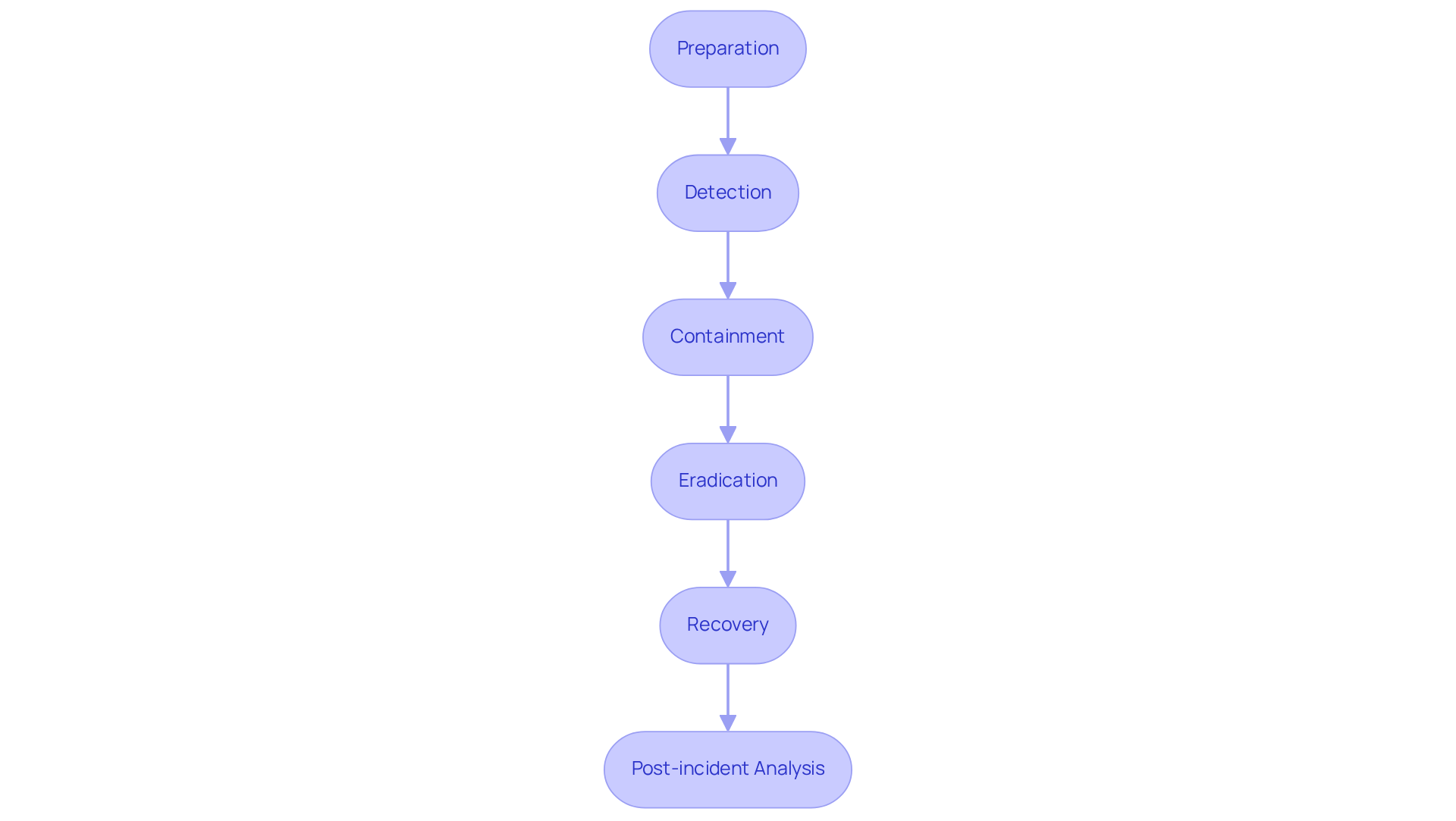
An incident response plan (IRP) is a crucial element of any company's security strategy. It outlines the specific actions to take in the event of a security breach, ensuring that organizations are prepared to respond effectively. A well-structured IRP encompasses several key phases:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- Post-incident analysis
Why is having a clear plan so important? By implementing an IRP, entities can respond swiftly to incidents, minimizing damage and facilitating a quicker recovery. Consider this: organizations with a robust IRP are often able to reduce the impact of breaches significantly, safeguarding their assets and reputation.
In summary, an effective IRP not only protects your organization but also instills confidence among stakeholders. It’s time to prioritize your incident response strategy and ensure your team is equipped with the necessary resources to handle potential security threats.
Cybersecurity Training and Awareness: Empowering Personnel Against Threats
Cybersecurity training and awareness programs are crucial for equipping personnel to identify and respond effectively to potential threats. These programs should cover essential topics such as:
- Phishing prevention
- Password management
- Safe browsing practices
Did you know that nearly 70% of companies believe their staff lack basic online security awareness? This figure has risen from 56% in 2023, underscoring the urgent need for comprehensive training. By fostering a culture of awareness, organizations can significantly reduce the risk of human errors, which account for approximately 68% of cyberattacks, according to industry research.
Effective training programs go beyond the basics; they incorporate interactive formats like games and high-quality video productions to engage employees. This approach has been proven to enhance knowledge retention and application. For instance, organizations that prioritize cybersecurity training report a notable decrease in incidents related to human error, reinforcing the necessity of a well-informed workforce.
Industry leaders emphasize that empowering employees through awareness training is vital. A remarkable 89% of leaders observed improvements in their company's security posture after implementing such programs. John Maddison stated, "These findings highlight the importance of our award-winning Awareness and Training service for enterprises." Furthermore, 96% of surveyed organizations indicated leadership support for these initiatives, reflecting a strong commitment to cultivating a cyber-aware culture. By investing in robust training, companies can establish a 'human firewall' of employees trained to thwart phishing scams, ultimately protecting sensitive information and enhancing their overall security posture.

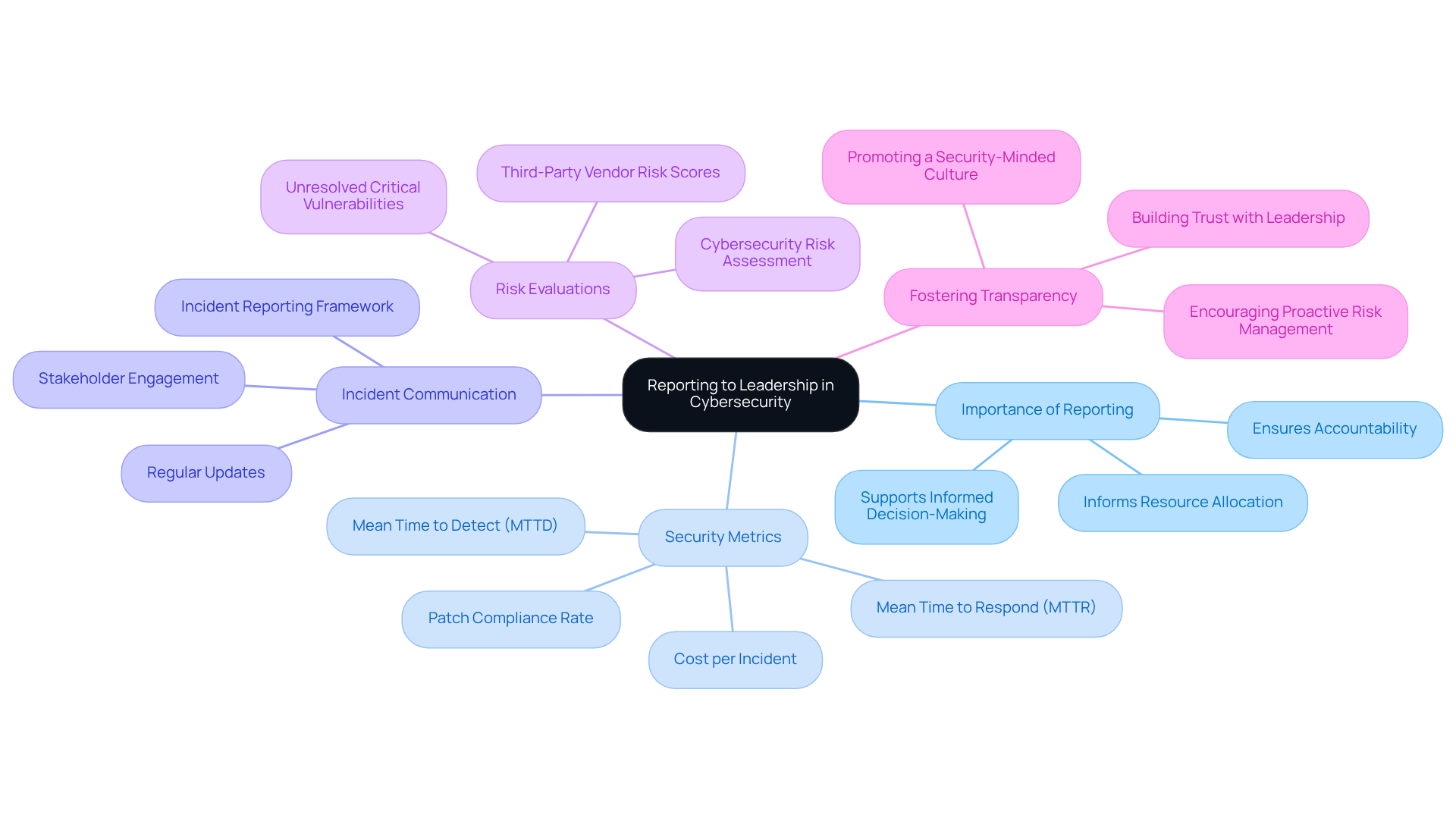
Reporting to Leadership: Maintaining Accountability in Cybersecurity
Effective reporting to leadership is essential for ensuring accountability in digital security. Organizations must establish a robust cybersecurity risk assessment framework to regularly communicate security metrics, incidents, and risk evaluations to senior management. This clarity empowers leadership to grasp the organization's security posture, allocate resources effectively, and make informed decisions regarding security strategies.
Why is this important? Without a clear understanding of security metrics, leadership may struggle to prioritize initiatives or respond to incidents effectively. By routinely sharing this information, organizations can foster a culture of transparency and proactive risk management.
In conclusion, implementing a structured reporting framework not only enhances accountability but also contributes to the organization's cybersecurity risk assessment framework, thereby strengthening its overall security posture. Take action now to ensure your leadership is equipped with the insights they need to protect your organization.
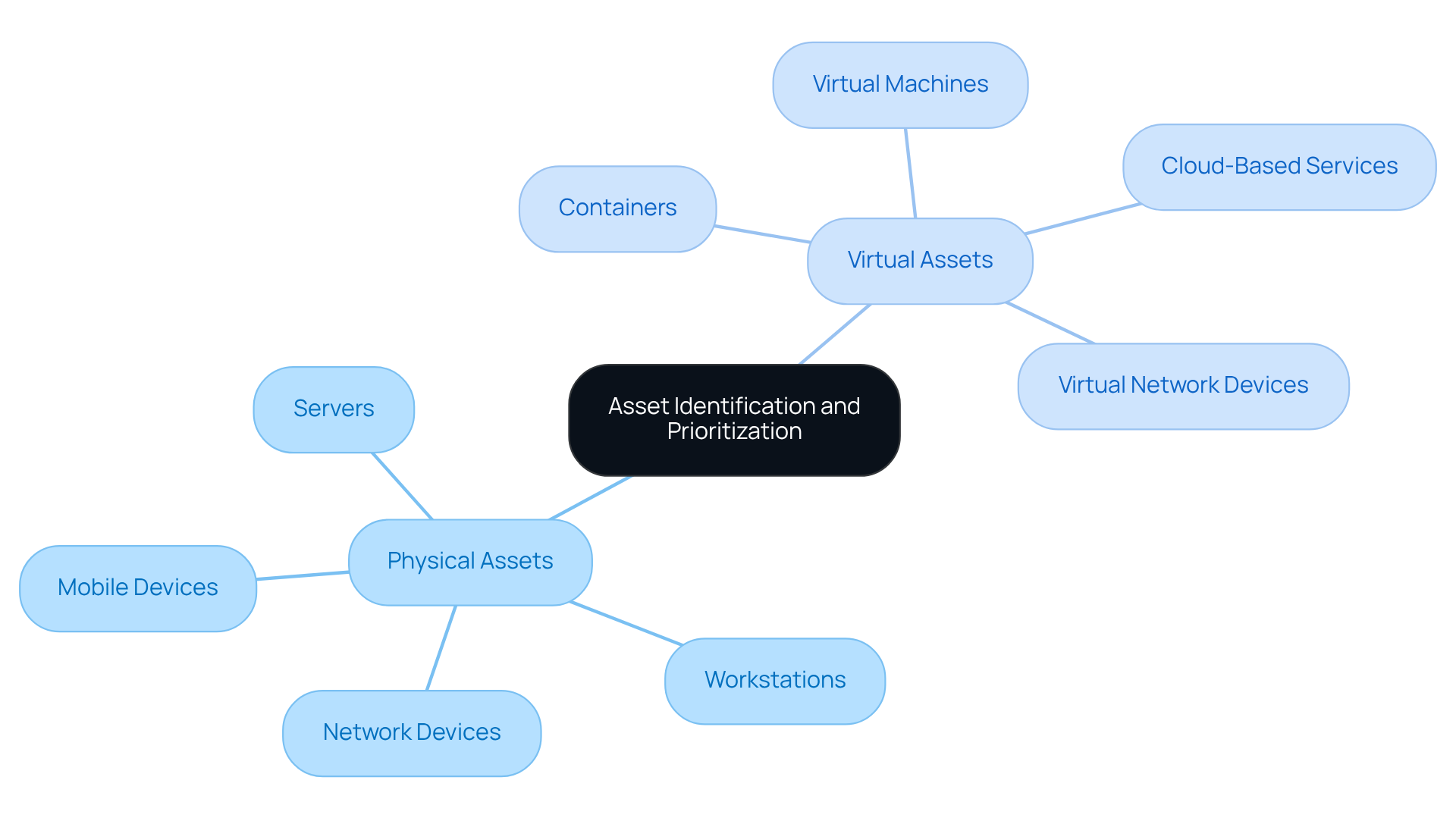
Asset Identification and Prioritization: Understanding What Needs Protection
Asset identification and prioritization are essential components of a robust cybersecurity strategy. Organizations must develop a comprehensive inventory of all assets, encompassing both physical assets - such as servers, workstations, network devices, and mobile devices - and virtual assets, including virtual machines, containers, cloud-based services, and virtual network devices.
Why is this assessment crucial? Understanding the value and sensitivity of these assets allows organizations to prioritize their most critical components. By focusing on these key assets, entities can allocate resources effectively and implement targeted security measures to protect their most valuable information. This approach not only enhances security but also ensures compliance with CMMC requirements, which is vital in today’s regulatory landscape.
In summary, a well-structured asset inventory and prioritization process is not just a best practice; it is a necessity for organizations aiming to safeguard their information through a cybersecurity risk assessment framework and meet compliance standards.
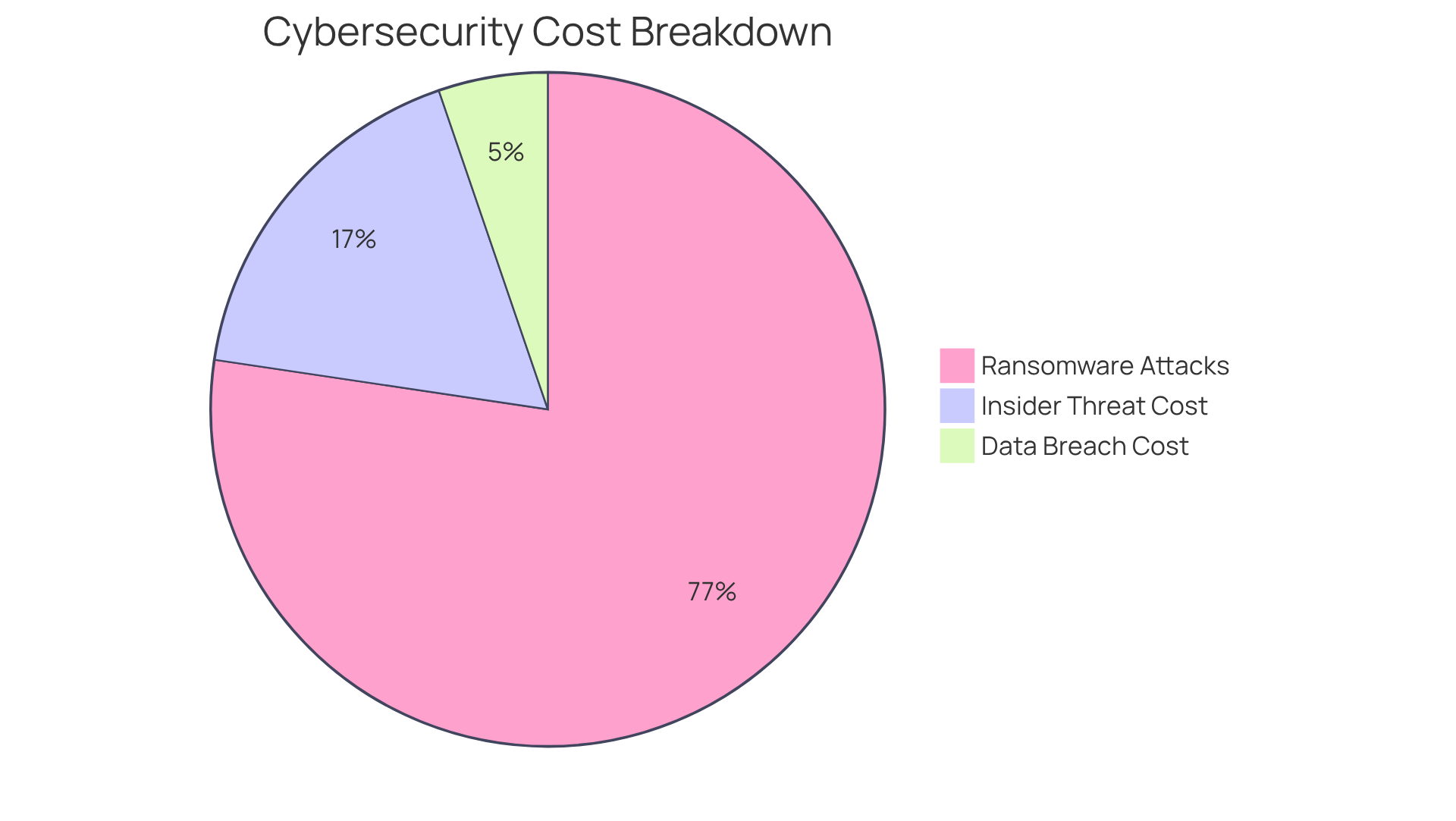
Risk Assessment and Analysis: Understanding Potential Threat Impacts
Organizations aiming to evaluate the potential impacts of identified threats on their assets and operations should implement a cybersecurity risk assessment framework, as risk assessment and analysis are crucial. This process involves determining the likelihood of various cybersecurity threats and their potential consequences. Did you know that 72% of companies faced ransomware attacks in 2023? Moreover, global cybercrime losses are projected to reach USD 10.5 trillion by 2025. These alarming statistics underscore the necessity of evaluating such threats. By understanding these elements, organizations can prioritize threats effectively.
To assess the likelihood and impacts of cybersecurity threats, companies often employ quantitative techniques, such as Monte Carlo simulations. These methods help in comprehending and quantifying the probability of various outcome scenarios. Additionally, advanced analytics enable real-time oversight of compliance activities, allowing organizations to quickly identify anomalies and highlight potential threats.
Consider the entities that actively assess potential threat effects; nearly 75% have established robust incident response strategies, with 63% consistently evaluating them. This showcases a proactive approach to managing uncertainties. Cybersecurity experts emphasize the importance of ongoing education and adaptation in this dynamic environment. Solomon Fadun, a recognized authority in threat management, notes that organizations must remain vigilant against emerging dangers.
The impact of digital security threats on businesses can be substantial. For instance, the average cost of a data breach is projected to reach $4.88 million in 2024, reflecting a 10% increase from the previous year. Furthermore, the average annual cost of insider threats stands at $16.2 million. These figures highlight the urgent need for organizations to invest in a cybersecurity risk assessment framework that identifies potential dangers and assists in developing effective mitigation strategies to protect vital assets.
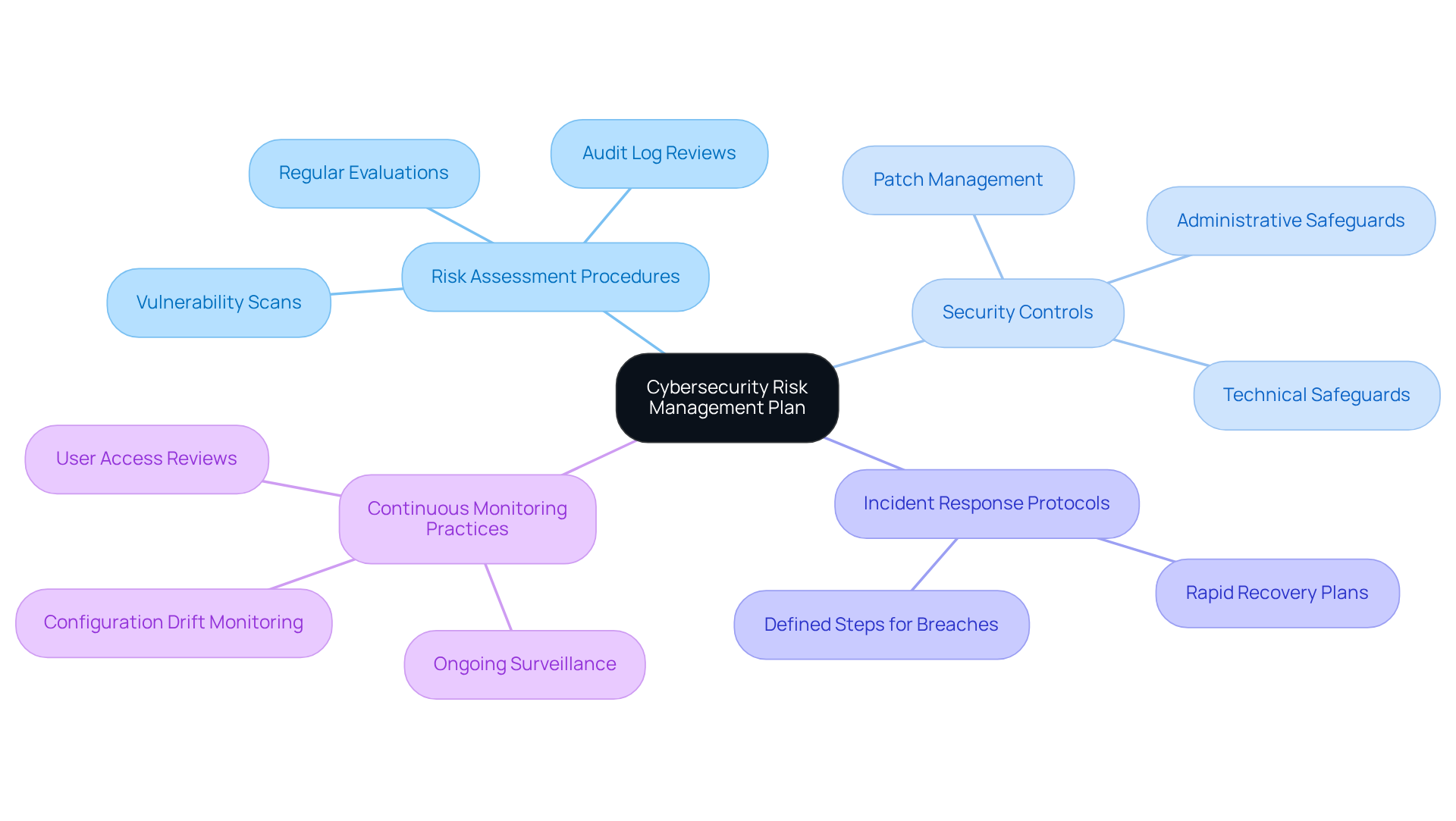
Cybersecurity Risk Management Plan: Outlining Strategies for Risk Mitigation
A robust cybersecurity risk assessment framework is essential for organizations seeking to effectively mitigate identified risks. This plan should encompass several key components:
- Risk Assessment Procedures: Regular evaluations to identify vulnerabilities and threats.
- Security Controls: Implementation of technical and administrative safeguards to protect sensitive data.
- Incident Response Protocols: Clearly defined steps for addressing breaches, ensuring rapid recovery and minimal impact.
- Continuous Monitoring Practices: Ongoing surveillance of systems to detect and respond to threats in real-time.
To maintain CMMC compliance, organizations must engage in essential ongoing activities, such as:
- Conducting regular vulnerability scans to identify security weaknesses.
- Implementing timely patch management for systems and applications.
- Regularly reviewing audit logs for signs of breaches.
- Monitoring systems for configuration drift from baselines.
- Conducting regular reviews of user access to ensure appropriateness.
- Continuously monitoring for security incidents.
Efficient threat reduction strategies in defense contracting also require collaboration among different departments. This is exemplified by the creation of Operations Centers (ROCs), which gather vulnerability data, enabling agencies to prioritize weaknesses and allocate resources effectively. As industry leaders emphasize, a proactive approach to threat management not only enhances security but also fosters resilience against evolving cyber dangers. With ransomware attacks costing businesses an average of $1.85 million per incident, the necessity for comprehensive risk management strategies has never been more critical.
Conclusion
In today's increasingly complex cybersecurity landscape, a robust risk assessment framework is essential for organizations that aim to protect their assets and ensure compliance. Identifying vulnerabilities, implementing security controls, and maintaining continuous monitoring are crucial steps that can significantly enhance an organization's cybersecurity posture.
Key components of an effective strategy include:
- The necessity of incident response plans
- The empowering role of cybersecurity training for personnel
- The critical nature of effective reporting to leadership
Each of these elements contributes to a comprehensive approach that not only mitigates risks but also fosters a culture of proactive security awareness and accountability.
As the threat landscape evolves, organizations must prioritize their cybersecurity risk assessment frameworks to safeguard against potential breaches and comply with emerging regulations like the CMMC. Taking decisive action now to implement best practices and invest in training will not only protect sensitive information but also build resilience against future cyber threats. Embracing these strategies is not merely a compliance requirement; it is a vital step toward securing the digital future of any organization.
Frequently Asked Questions
What is the purpose of the CMMC Info Hub?
The CMMC Info Hub serves as a resource for organizations seeking to achieve compliance with the Cybersecurity Maturity Model Certification (CMMC), offering roadmaps, strategies, and insights to navigate DoD security requirements.
Why is cybersecurity important for small-to-medium enterprises (SMEs)?
Nearly 50% of all cyberattacks target SMEs, highlighting the urgent need for these organizations to implement robust protective measures.
How does the CMMC Info Hub assist organizations with compliance?
The CMMC Info Hub provides a cybersecurity risk assessment framework that helps organizations clarify compliance challenges, streamline processes, and strengthen their cybersecurity measures.
When do new CMMC regulations regarding verified security compliance take effect?
The new CMMC regulations mandating verified security compliance will take effect on November 10, 2025.
What is the significance of cybersecurity risk assessments?
Cybersecurity risk assessments are crucial for identifying vulnerabilities and threats within a company's infrastructure, allowing organizations to prioritize protective measures and allocate resources effectively.
How often should organizations conduct cybersecurity evaluations?
Organizations should conduct regular cybersecurity evaluations to identify weaknesses, assess vulnerabilities, and enhance their overall digital resilience.
What are security controls and why are they important?
Security controls are essential actions taken to reduce risks identified during cybersecurity evaluations. They help protect an organization’s assets and ensure compliance with cybersecurity frameworks.
What are the three primary categories of security controls?
The three primary categories of security controls are administrative, technical, and physical controls.
Can you provide examples of administrative controls?
Administrative controls include policies such as access control to ensure only authorized personnel can access sensitive information and regular security audits to identify vulnerabilities.
What types of measures fall under technical controls?
Technical controls include technological solutions like encryption for data security and firewalls to monitor network traffic.
What are physical controls and why are they critical?
Physical controls protect an organization's physical infrastructure, such as guards and surveillance systems, and are particularly important in defense contracting to safeguard sensitive information.
What is the impact of third-party involvement on cybersecurity breaches?
Approximately 30% of breaches are associated with third-party involvement, emphasizing the need for comprehensive protective measures.




