10 Key Elements for Effective Cybersecurity Plans for Contractors
Explore essential elements to strengthen your cybersecurity plans for defense contractors.

Introduction
In an era where cyber threats are more pronounced than ever, defense contractors grapple with the formidable task of safeguarding sensitive information while adhering to rigorous regulations. This article explores ten essential elements that underpin effective cybersecurity plans specifically designed for contractors, providing insights that can significantly bolster their security posture.
With threats evolving and compliance requirements becoming increasingly complex, how can organizations ensure they are not merely meeting standards but also proactively preventing potential breaches? By examining these critical strategies, contractors can not only protect their assets but also gain a competitive advantage in the defense sector.
CMMC Info Hub: Comprehensive Guidance for CMMC Compliance
CMMC Info Hub stands as a centralized knowledge base, offering detailed roadmaps, articles, and practical strategies specifically tailored to the Cybersecurity Maturity Model Certification (CMMC). This platform provides organized direction, enabling defense contractors to understand and implement the essential measures required for compliance. By doing so, it significantly enhances their qualifications for defense contracts.
Moreover, the platform emphasizes peer insights, allowing users to learn from the experiences of others who have successfully navigated the compliance landscape. Have you ever wondered how others achieved their compliance goals? Learning from their journeys can provide invaluable lessons.
Additionally, CMMC Info Hub may contain links to external websites. However, we have no control over the content of these external sites and accept no responsibility for their content or availability. Importantly, the inclusion of any link does not imply endorsement by us.
In conclusion, leveraging the resources available on CMMC Info Hub can significantly enhance the cybersecurity plans of defense contractors aiming for compliance. Take action today and explore the wealth of information at your fingertips.

NIST Cybersecurity Framework: Essential Standards for Defense Contractors
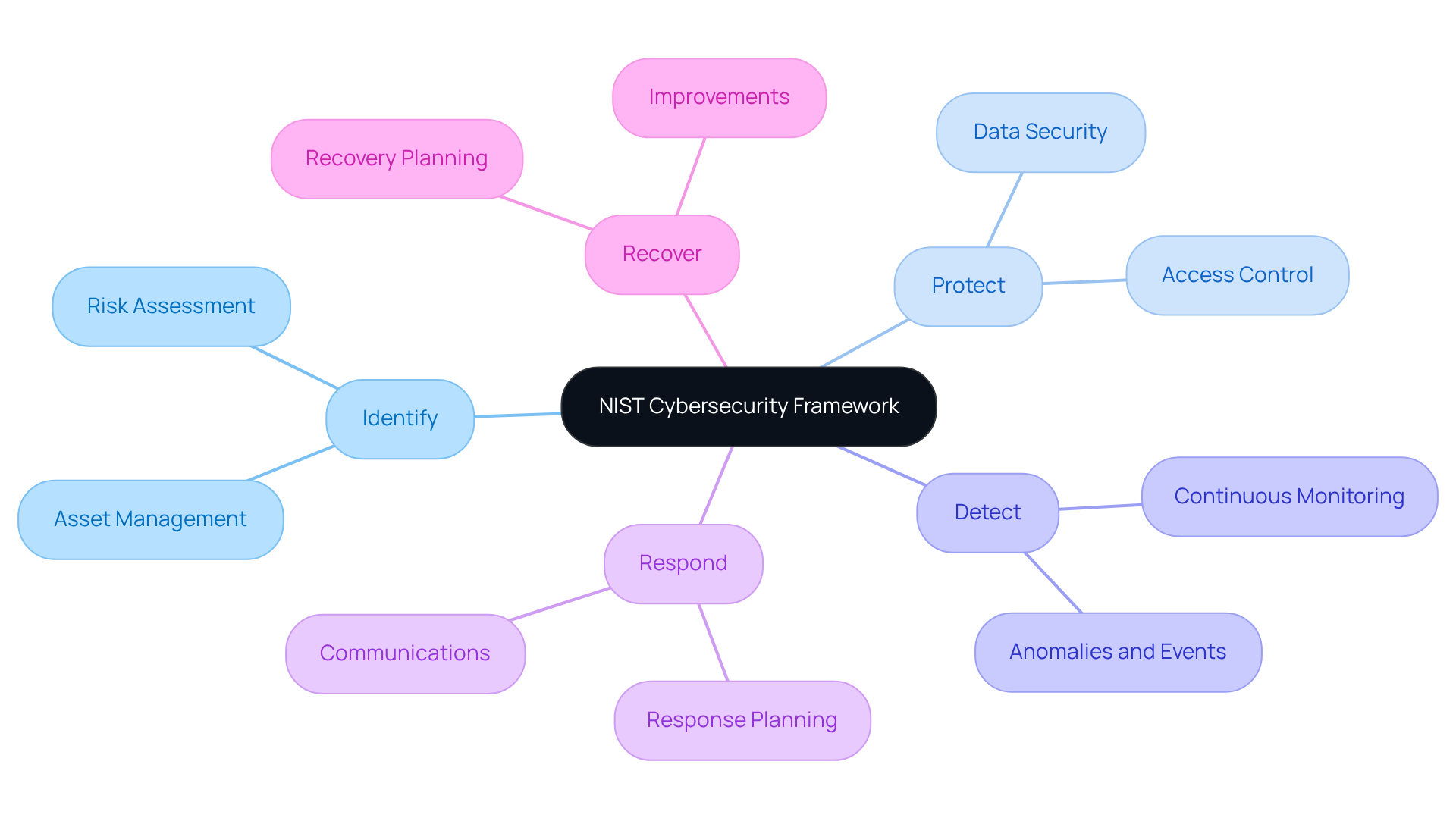
The NIST Cybersecurity Framework (CSF) serves as a vital tool for organizations aiming to manage and mitigate digital security risks effectively. With its five essential functions - Identify, Protect, Detect, Respond, and Recover - the CSF is fundamental for defense firms looking to bolster their security posture. But why is adherence to these standards so crucial? It’s not just a best practice; it’s a critical requirement for compliance with the Cybersecurity Maturity Model Certification (CMMC).
By integrating the CSF into their cybersecurity plans, firms can significantly enhance their resilience against ever-evolving cyber threats. This alignment with the stringent requirements set by the Department of Defense is not merely beneficial; it’s essential for maintaining a competitive edge in the defense sector. Security experts widely commend the execution of the CSF, recognizing it as an industry best practice that fosters a proactive approach to risk management.
This structured methodology not only aids in achieving compliance but also cultivates a culture of continuous improvement in security practices. Ultimately, this proactive stance benefits suppliers in their pursuit of defense contracts. Are you ready to elevate your organization’s cybersecurity strategy? Embrace the CSF and create effective cybersecurity plans to position your firm for success in a challenging digital landscape.
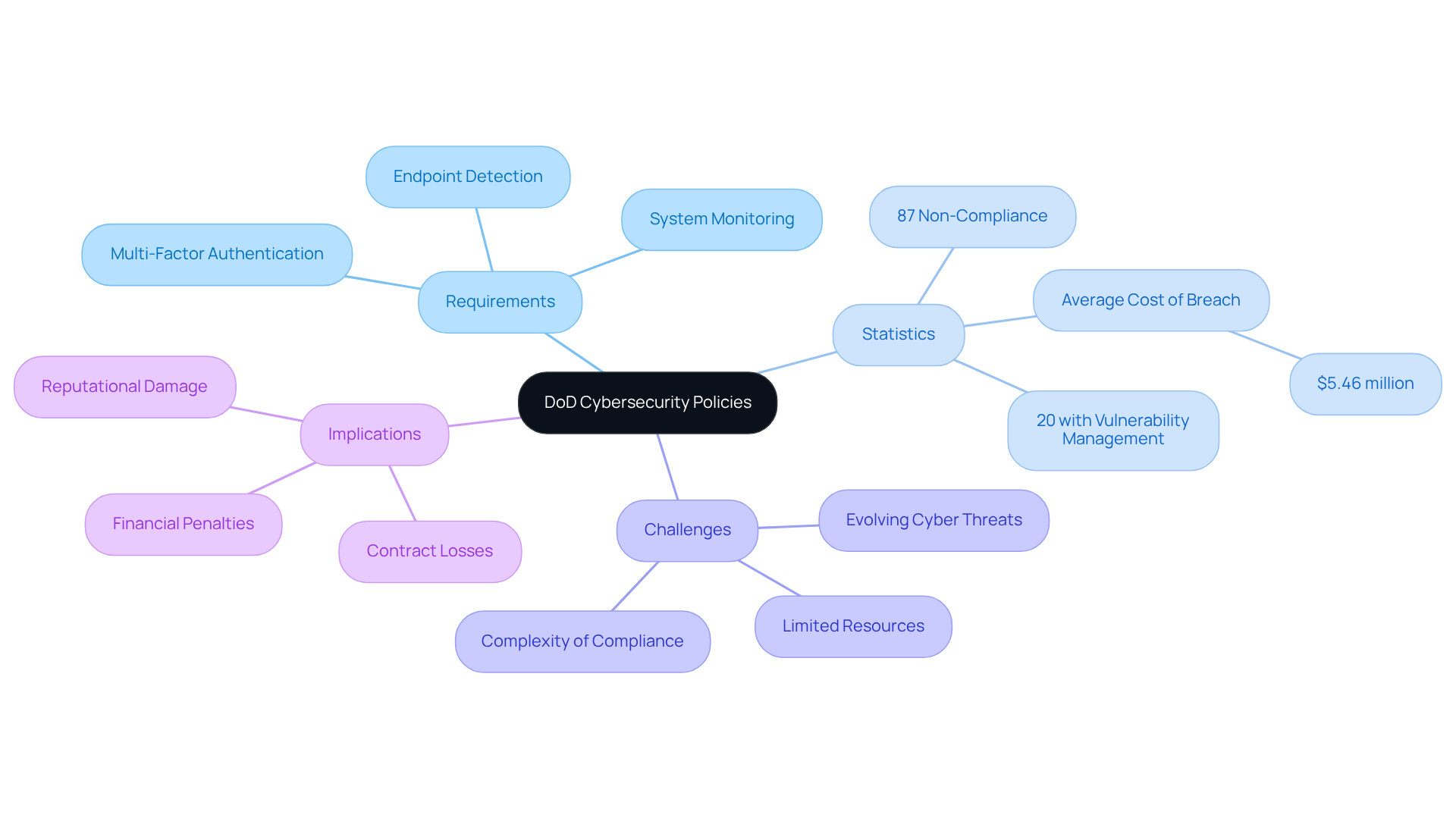
DoD Cybersecurity Policies: Mandatory Compliance for Contractors
Defense suppliers face stringent requirements from the Department of Defense (DoD) regarding information security, particularly through the Defense Federal Acquisition Regulation Supplement (DFARS) and the Cybersecurity Maturity Model Certification (CMMC). These regulations mandate that builders implement specific security controls to protect sensitive information. Alarmingly, 87% of Pentagon supply chain contractors have not met the minimum cybersecurity standards, highlighting the urgent need for compliance. Non-compliance can result in severe consequences, including contract losses and hefty financial penalties. In fact, the average cost of a data breach in the defense sector is around $5.46 million, underscoring the financial stakes involved.
Key requirements under DFARS and CMMC include:
- Maintaining a comprehensive multi-factor authentication system
- Continuous system monitoring
- Robust endpoint detection and response solutions
Yet, only 20% of builders have a vulnerability management solution in place, revealing a significant gap in preparedness.
Concerns about the complexities of meeting these requirements are prevalent among defense providers. One builder noted, "The changing cyber threat environment poses continuous difficulties in upholding DFARS and CMMC standards." This sentiment resonates with many in the sector, as 31% of security providers report challenges in developing effective protocols to prevent data breaches.
The impact of DFARS on adherence efforts is substantial. With the final rule effective from November 10, 2025, vendors must post CMMC Level 1 or Level 2 self-assessment results to the Supplier Performance Risk System (SPRS) before contract awards or extensions. This new mandate underscores the necessity of proactive cybersecurity plans, as organizations that fail to adhere risk not only financial penalties but also reputational damage and lost business opportunities. As the landscape evolves, staying informed and prepared is crucial for those looking to secure their positions within the defense supply chain. Builders are encouraged to leverage external resources available through platforms like CMMC Info Hub, which can provide valuable insights and guidance on effectively navigating regulatory requirements.
Risk Management Framework (RMF): Proactive Risk Mitigation Strategies
The Risk Management Framework (RMF) serves as a vital procedure that integrates security, privacy, and cyber supply chain risk management tasks, playing a crucial role in the journey toward CMMC compliance. Why is RMF essential? It categorizes information systems, selects and implements security controls, and continuously monitors their effectiveness. For defense providers, adopting RMF is not just beneficial; it’s imperative for identifying potential vulnerabilities and ensuring compliance with DoD requirements.
By proactively managing risks and implementing practical cybersecurity plans, builders can significantly enhance their overall security posture. This approach allows them to navigate Level 1 and Level 2 requirements effectively, ultimately reducing the likelihood of security incidents. Imagine transforming confusion into clarity - this is what RMF offers. It empowers contractors to pursue CMMC adherence with confidence.
In summary, embracing the RMF is a strategic move that not only safeguards your organization but also aligns with regulatory expectations. Are you ready to take the next step in fortifying your security framework?

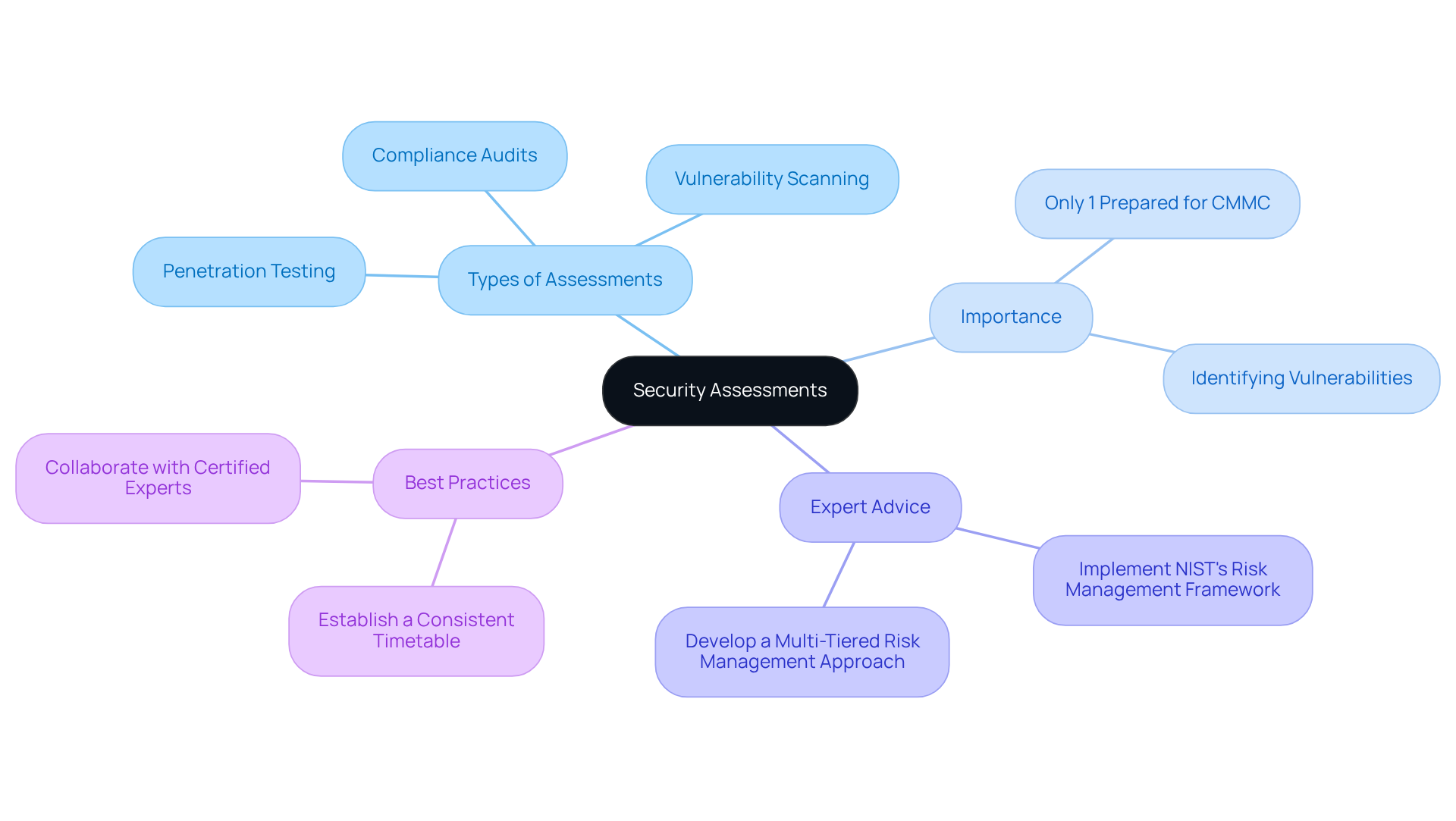
Security Assessments: Continuous Evaluation of Cybersecurity Measures
Regular security assessments are crucial for identifying vulnerabilities within an organization's cybersecurity plans. These assessments can take various forms, including penetration testing, vulnerability scanning, and compliance audits. For military suppliers, performing comprehensive security evaluations as part of their cybersecurity plans is essential - not just for fulfilling CMMC standards, but also for strengthening safeguards against potential cyber risks.
As highlighted in the Ultimate Guide to Achieving CMMC Compliance, these evaluations are part of the broader cybersecurity plans for DoD security success. They ensure that vendors can master CMMC requirements and implement necessary controls effectively. A recent CyberSheath survey revealed a startling statistic: only 1% of U.S. defense providers feel fully prepared for the CMMC program. This underscores the critical need for proactive evaluations.
Statistics show that a significant number of vulnerabilities are discovered during these assessments, emphasizing their importance. By continuously assessing their cybersecurity plans, professionals can adapt to evolving threats and maintain a robust security posture. As Ron Ross, a senior computer scientist, advises, "Implement NIST's risk management framework, from defining risks to selecting, implementing, and monitoring information security controls." This approach is essential for aligning with CMMC standards.
To enhance their preparedness, security providers should establish a consistent timetable for security evaluations. Collaborating with certified experts is vital to ensure adherence and security efficiency, aligning with crucial continuous monitoring and maintenance practices for CMMC compliance.
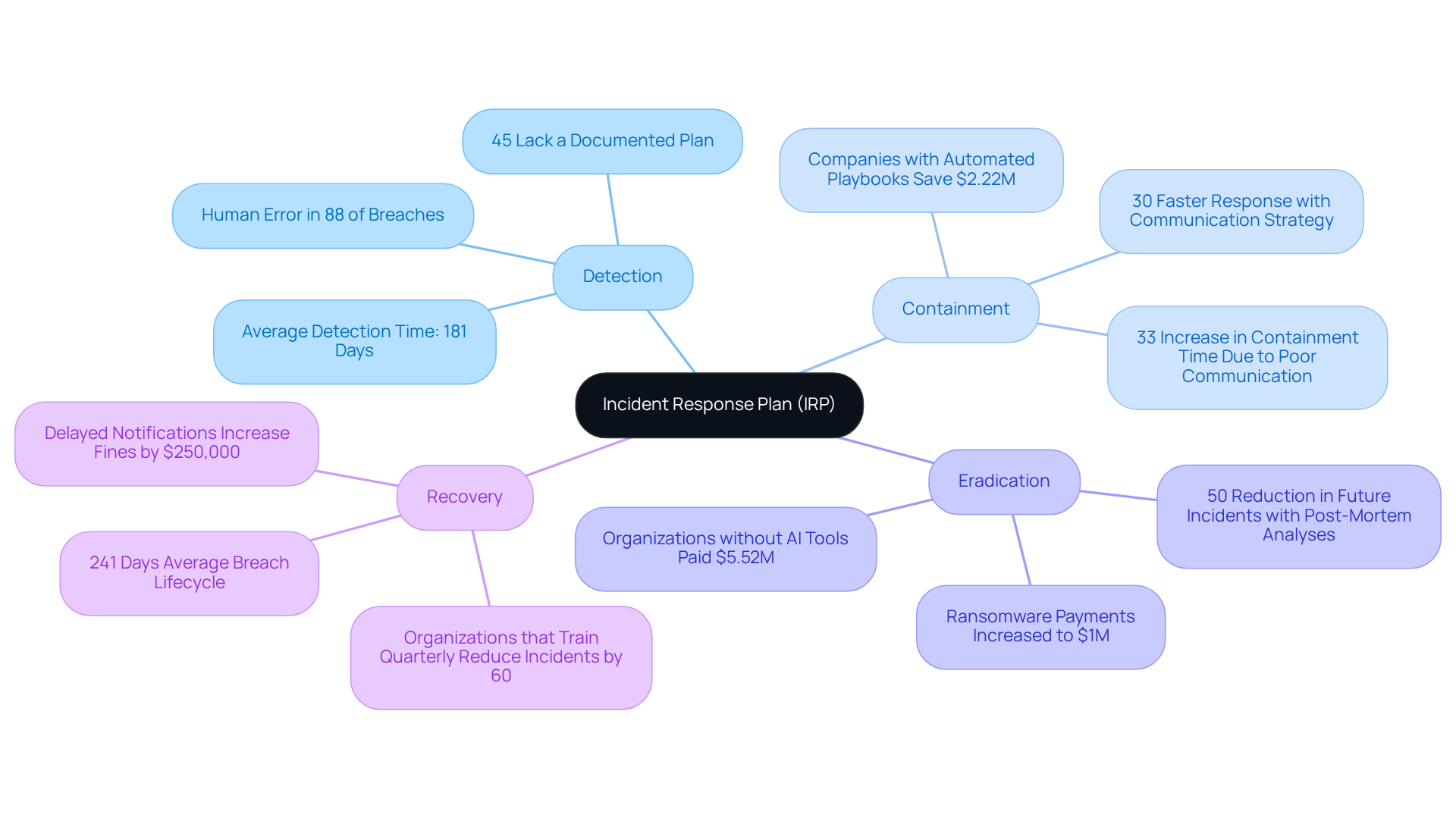
Incident Response Plans: Swift Action Against Cyber Threats
An incident response plan (IRP) is an essential documented strategy that outlines how an organization will address cybersecurity incidents through its cybersecurity plans. It encompasses procedures for detection, containment, eradication, and recovery, specifically tailored for contractors. The importance of a robust Incident Response Plan (IRP) cannot be overstated; it minimizes the impact of cyber threats and ensures compliance with Department of Defense (DoD) regulations, highlighting the necessity of comprehensive cybersecurity plans. Did you know that organizations with a predefined incident communication strategy can reduce response time by 30%? Furthermore, those that conduct incident response drills at least quarterly respond 35% faster to incidents.
Statistics reveal that:
- 45% of organizations lack a documented incident response plan, resulting in prolonged recovery times and increased costs.
- In the security sector, the average lifecycle of a breach in 2025 was 241 days, highlighting the urgent need for effective preparedness.
- High-performing security teams that conduct detailed post-mortem analyses after incidents can reduce future incident rates by 50%.
This proactive approach not only enhances response capabilities but also protects sensitive information and minimizes downtime.
Recent incidents, such as the WannaCry ransomware attack, which cost the U.K.'s National Health Service over $100 million, serve as stark reminders of the potential financial and operational repercussions of inadequate incident response strategies. By learning from these events, contractors can implement effective cybersecurity plans that prioritize swift action and thorough preparation. Ultimately, this safeguards their operations against evolving cyber threats. This aligns with the comprehensive guide to attaining CMMC compliance, providing a roadmap for DoD security success.
Employee Training Programs: Building a Cybersecurity-Conscious Workforce
Employee training programs are crucial for cultivating a cybersecurity-aware workforce, especially in the contracting sector. These initiatives must cover vital topics like:
- Phishing awareness
- Password management
- Safe internet practices
Regular training sessions empower employees to identify and respond effectively to potential threats, significantly lowering the risk of human errors, which account for a substantial portion of security breaches.
Did you know that organizations with strong security awareness training programs can reduce their breach likelihood by up to 65%? This statistic, from KnowBe4, underscores the importance of these initiatives. Moreover, tailored training approaches, including role-specific content, have been shown to boost phishing threat detection by as much as 90% within just six months. However, a study involving 19,500 employees at UC San Diego Health revealed that current anti-phishing training programs do not significantly mitigate the risk of employees falling for phishing scams. This finding highlights the necessity for organizations to consider technical countermeasures alongside training.
Additionally, engagement with embedded training materials has been disappointingly low, with many users interacting for only a minute or less. By prioritizing employee training, military suppliers can strengthen their cybersecurity plans and transform their workforce into a formidable barrier against cyber threats. It's time to take action and invest in comprehensive training programs that incorporate cybersecurity plans to educate and empower employees to safeguard their organizations.

Data Encryption: Safeguarding Sensitive Information
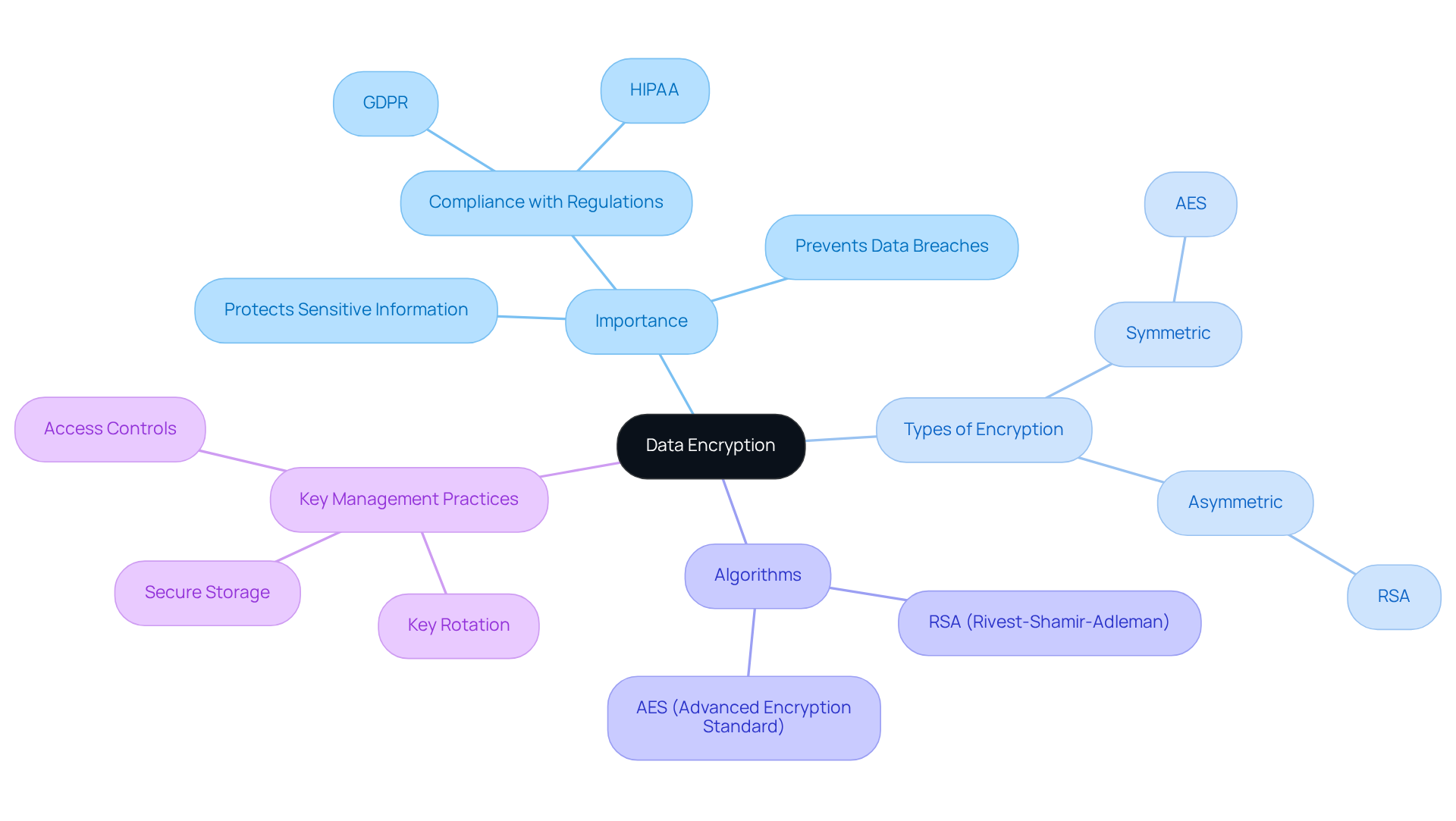
Data encryption stands as a cornerstone of any robust cybersecurity plans, particularly for organizations that manage sensitive information. By converting data into an unreadable format, encryption serves as a formidable barrier against unauthorized access. This means that even if a breach occurs, the data remains safeguarded. Have you considered the implications of not implementing encryption? Contractors are required to enforce encryption for both data at rest and in transit, not only to comply with Department of Defense regulations but also to protect sensitive information from the ever-evolving landscape of cyber threats.
Employing strong encryption algorithms is essential. For symmetric encryption, AES is a widely recognized standard, while RSA is the go-to for asymmetric encryption. These methods are crucial for maintaining data integrity and confidentiality. Furthermore, effective key management practices - such as key rotation, secure storage, and stringent access controls - are vital for protecting encryption keys and enhancing overall data security.
As cyber threats continue to evolve, prioritizing encryption in cybersecurity plans not only fortifies security but also aligns with regulatory requirements, including GDPR and HIPAA. This alignment is essential for protecting both the organization and its clients. Are you ready to take action and ensure your data is secure?
Software Updates and Patch Management: Keeping Systems Secure
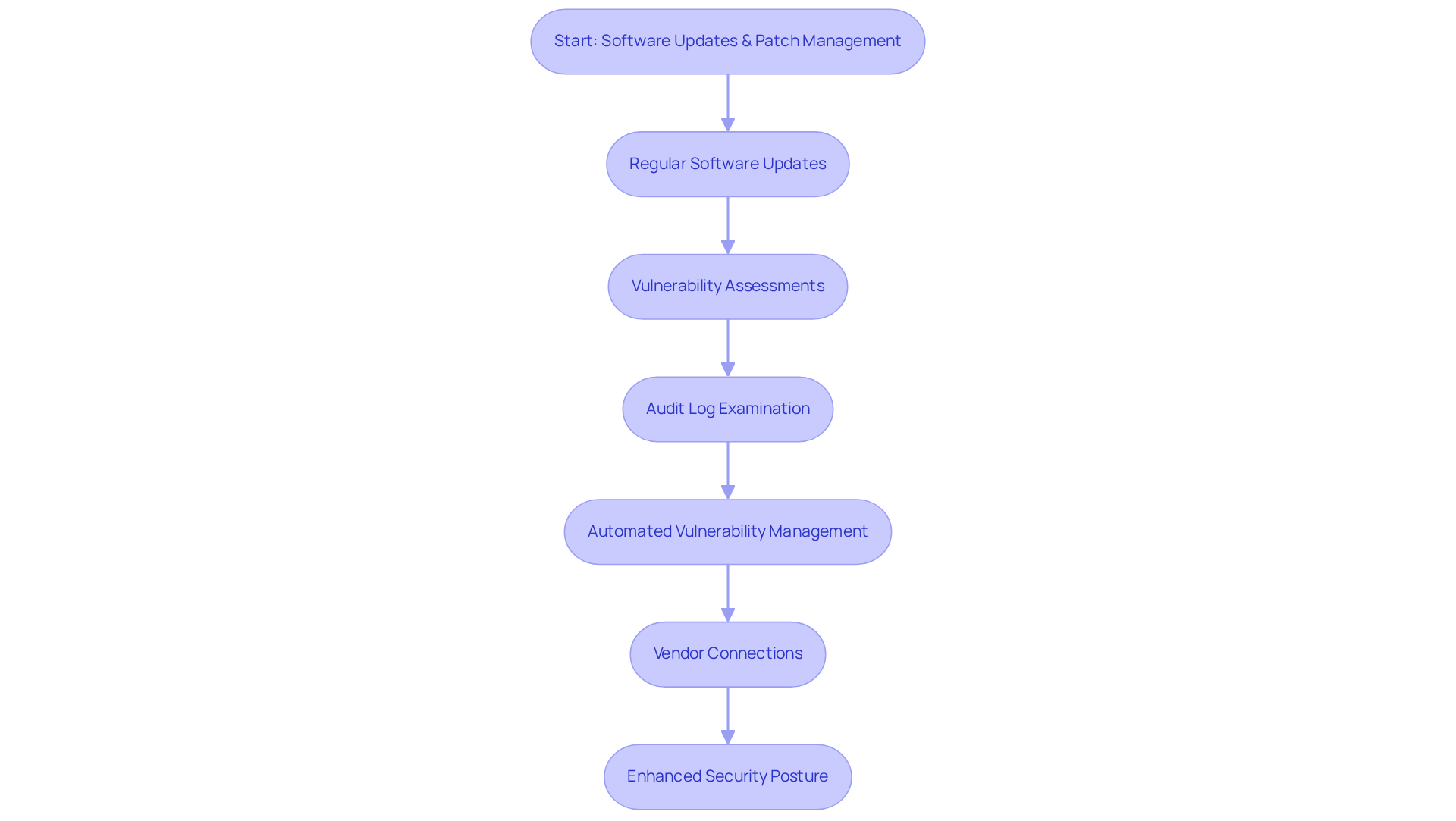
Regular software updates and effective patch management are crucial for safeguarding IT systems against cyber threats. Did you know that outdated software often harbors vulnerabilities that cybercriminals can exploit to gain unauthorized access? For security suppliers, establishing a robust patch management program is not just beneficial; it’s essential. This program should prioritize critical updates and ensure their timely installation. Research indicates that nearly 90% of defense contractors have faced financial, reputational, or operational losses due to cyber incidents.
To strengthen your security posture, continual monitoring methods are vital. Performing routine vulnerability assessments to detect security flaws and examining audit logs for indications of security events are essential elements of comprehensive cybersecurity plans. By maintaining a precise inventory of software assets and keeping software up to date, organizations can significantly reduce their attack surface, which enhances their cybersecurity plans.
Moreover, integrating continuous, automated, and risk-based vulnerability management programs can streamline the process, minimize human error, and accelerate the deployment of necessary updates. This proactive approach not only mitigates risks associated with outdated software but also fosters a culture of security awareness through user education about the risks of outdated systems.
Finally, fostering robust vendor connections is crucial for proactive planning related to patch releases and security notices. This ultimately results in a more resilient barrier against evolving cyber threats. Are you ready to take action and enhance your organization's security measures?
Cybersecurity Expert Collaboration: Leveraging Professional Insights
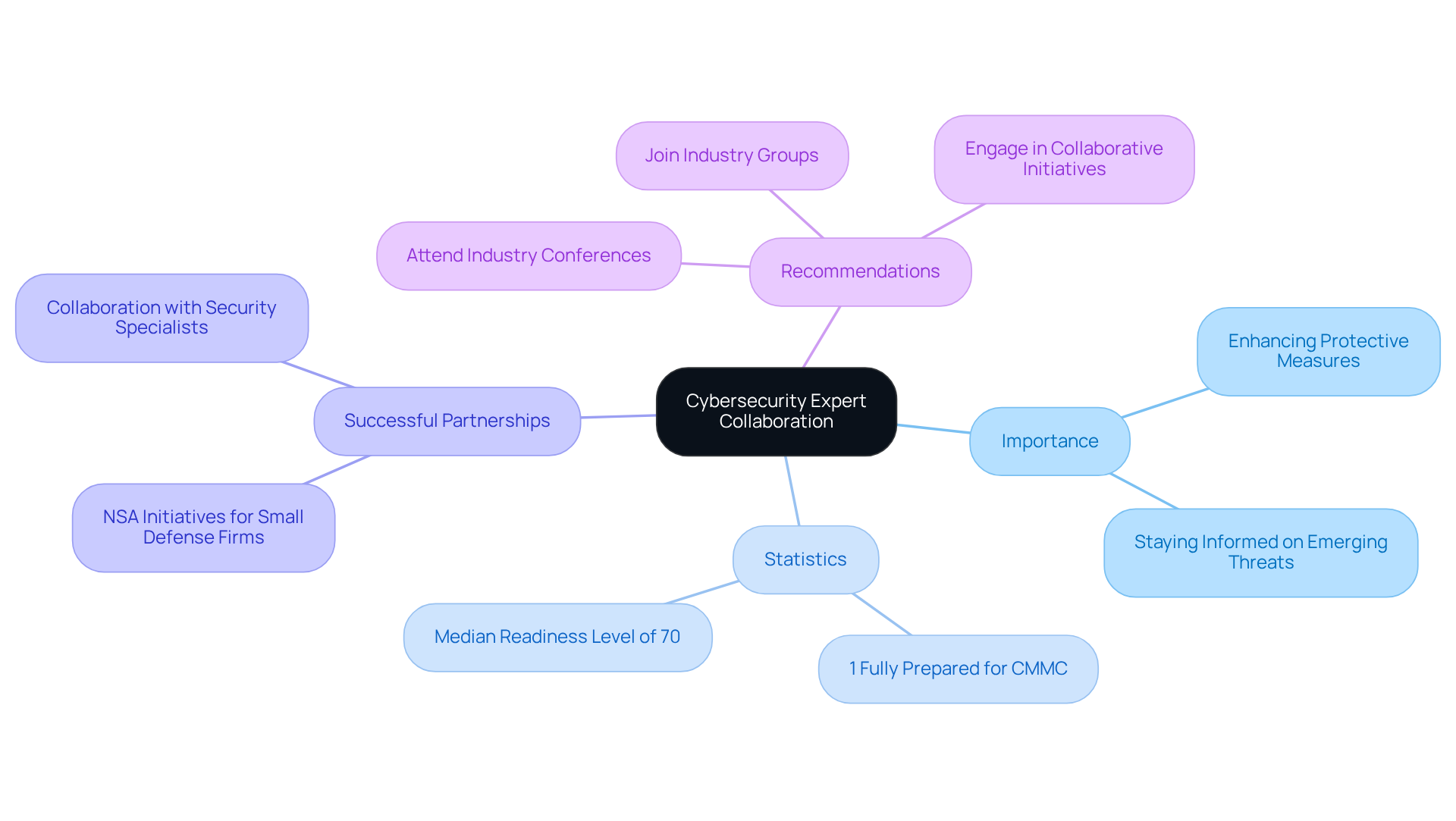
Working with security specialists is crucial for defense contractors seeking to enhance their protective measures. By collaborating with experts in various areas of online security, organizations can tap into the latest trends, tools, and best practices. This partnership not only fosters the development of comprehensive security solutions but also significantly strengthens the overall cybersecurity plans.
Consider this: only 1% of U.S. military suppliers feel fully equipped for the Cybersecurity Maturity Model Certification (CMMC), with a median readiness level of just 70%. This stark reality underscores the necessity of leveraging expert knowledge. Contractors should actively pursue networking opportunities with specialists, attend industry conferences, and engage in collaborative initiatives. Such efforts keep them informed about emerging threats, including the alarming rise of AI-based malware, while facilitating the exchange of valuable experiences and strategies that can lead to improved security outcomes.
Successful partnerships, like those formed through the NSA's initiatives to support small defense firms - who represent 80% of the defense industrial base - demonstrate how expert collaboration can effectively mitigate risks and enhance resilience against cyber threats. To initiate these collaborations, contractors should consider joining relevant industry groups or forums that focus on cybersecurity plans and best practices.
In summary, engaging with security specialists is not just beneficial; it is essential for contractors aiming to bolster their defenses and ensure compliance with CMMC standards.
Conclusion
In the realm of cybersecurity, particularly for contractors, establishing effective plans is not just advisable; it’s essential for compliance and operational success. Focusing on key elements such as the Cybersecurity Maturity Model Certification (CMMC), the NIST Cybersecurity Framework, and proactive risk management strategies can significantly enhance defenses against the ever-evolving landscape of cyber threats.
Why is this important? Regular security assessments, incident response plans, and employee training programs are critical in fostering a security-conscious workforce. Moreover, the significance of data encryption and timely software updates cannot be overstated. These practices are foundational to safeguarding sensitive information and maintaining system integrity. Collaborating with cybersecurity experts amplifies these efforts, enabling contractors to stay informed and prepared.
The stakes are high for defense contractors navigating the complexities of cybersecurity regulations. Embracing these best practices and leveraging available resources can create a robust cybersecurity posture that not only meets compliance requirements but also protects valuable assets. As organizations prepare for the challenges ahead, taking proactive steps today will pave the way for a more secure and resilient future in the defense contracting sector.
Frequently Asked Questions
What is the purpose of the CMMC Info Hub?
The CMMC Info Hub serves as a centralized knowledge base offering detailed roadmaps, articles, and practical strategies to help defense contractors understand and implement measures required for Cybersecurity Maturity Model Certification (CMMC) compliance.
How can the CMMC Info Hub benefit defense contractors?
By leveraging the resources available on CMMC Info Hub, defense contractors can enhance their cybersecurity plans and significantly improve their qualifications for defense contracts.
What type of insights does the CMMC Info Hub provide?
The platform emphasizes peer insights, allowing users to learn from the experiences of others who have successfully navigated the compliance landscape.
Are there external links on the CMMC Info Hub, and what is their significance?
Yes, the CMMC Info Hub may contain links to external websites; however, the platform does not control the content of these external sites and does not endorse them.
What is the NIST Cybersecurity Framework (CSF)?
The NIST Cybersecurity Framework (CSF) is a tool that helps organizations manage and mitigate digital security risks through five essential functions: Identify, Protect, Detect, Respond, and Recover.
Why is adherence to the NIST CSF important for defense contractors?
Adherence to the NIST CSF is crucial for compliance with CMMC and helps firms enhance their resilience against cyber threats, maintaining a competitive edge in the defense sector.
What are some key requirements under DFARS and CMMC for defense suppliers?
Key requirements include maintaining a comprehensive multi-factor authentication system, continuous system monitoring, and robust endpoint detection and response solutions.
What are the consequences of non-compliance with DoD cybersecurity policies?
Non-compliance can lead to severe consequences, including contract losses, financial penalties, and reputational damage, with the average cost of a data breach in the defense sector being around $5.46 million.
What challenges do defense contractors face in meeting cybersecurity requirements?
Many defense providers express concerns about the complexities of meeting requirements, with a significant percentage reporting difficulties in developing effective protocols to prevent data breaches.
What is the significance of the final rule effective from November 10, 2025, regarding CMMC?
Vendors must post CMMC Level 1 or Level 2 self-assessment results to the Supplier Performance Risk System (SPRS) before contract awards or extensions, highlighting the necessity for proactive cybersecurity plans.




