4 Best Practices for Security Compliance in Cloud Environments
Master best practices for security compliance cloud to safeguard your data in virtual environments.

Introduction
In an era marked by escalating data breaches and cyber threats, organizations must prioritize security compliance within cloud environments to protect sensitive information. This article explores essential best practices that not only enhance compliance but also strengthen an organization's overall security posture. With the complexities of shared responsibilities and the ever-evolving nature of threats, how can companies ensure they are adequately safeguarded in the cloud?
By addressing these critical questions, we aim to equip you with actionable insights that will bolster your security measures and compliance efforts.
Understand Cloud Security Fundamentals
Fundamentals of online protection encompass the core principles that govern the safeguarding of data and applications in virtual environments. Understanding these principles is crucial for any organization aiming to enhance its security compliance cloud posture.
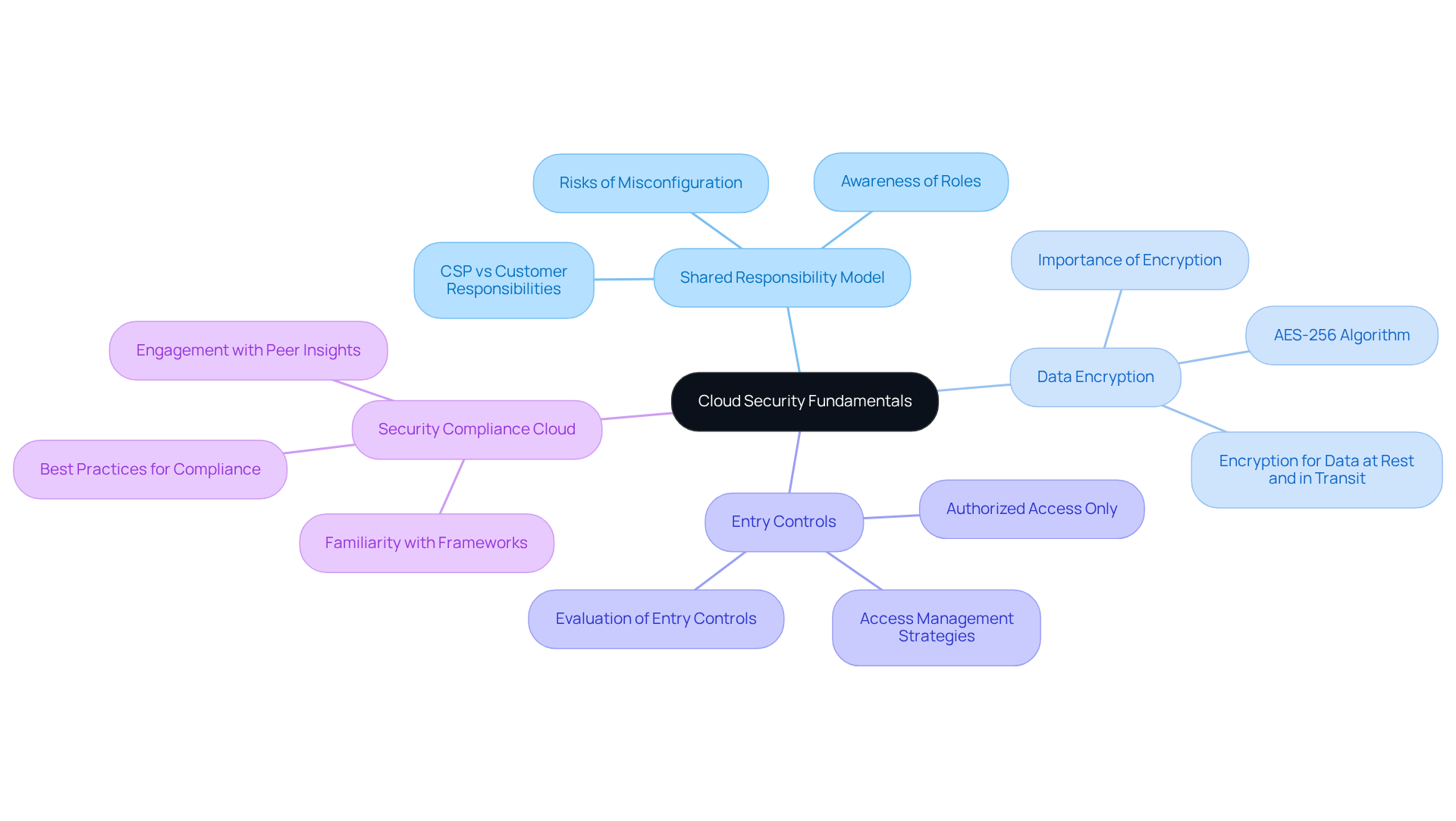
-
Shared Responsibility Model: Security is a shared responsibility between the cloud service provider (CSP) and the customer. While the CSP secures the infrastructure, customers must secure their data and applications. Organizations that overlook this model may face significant safety risks, including cloud misconfigurations that affect their security compliance cloud. Are you aware of your role in this shared responsibility?
-
Data Encryption: Implementing encryption for data at rest and in transit is vital to protect sensitive information from unauthorized access. Organizations should prioritize strong encryption practices, such as using AES-256 algorithms and regularly updating cryptographic keys. Despite its importance, many businesses still struggle with adequate implementation. How robust is your encryption strategy?
-
Entry Controls: Establishing strict entry controls ensures that only authorized users can access sensitive data and applications. Effective access management can significantly reduce risks, especially given the increasing number of breaches linked to unauthorized access. Have you evaluated your entry control measures recently?
-
Security Compliance Cloud: Familiarizing yourself with relevant frameworks in the security compliance cloud, such as NIST, ISO, and CMMC, is essential. The CMMC framework, in particular, offers practical strategies and peer insights that can help defense contractors achieve compliance with assurance. Engaging with peer insights can provide valuable lessons learned and best practices that enhance compliance efforts. Are you leveraging these resources to strengthen your compliance initiatives?
By mastering these fundamentals, entities can establish a robust foundation for their online protection strategy. Take action now to ensure your organization is well-equipped to navigate the complexities of online security.
Explore Key Security Domains for Compliance
To achieve compliance in cloud environments, organizations must prioritize several key security domains:
-
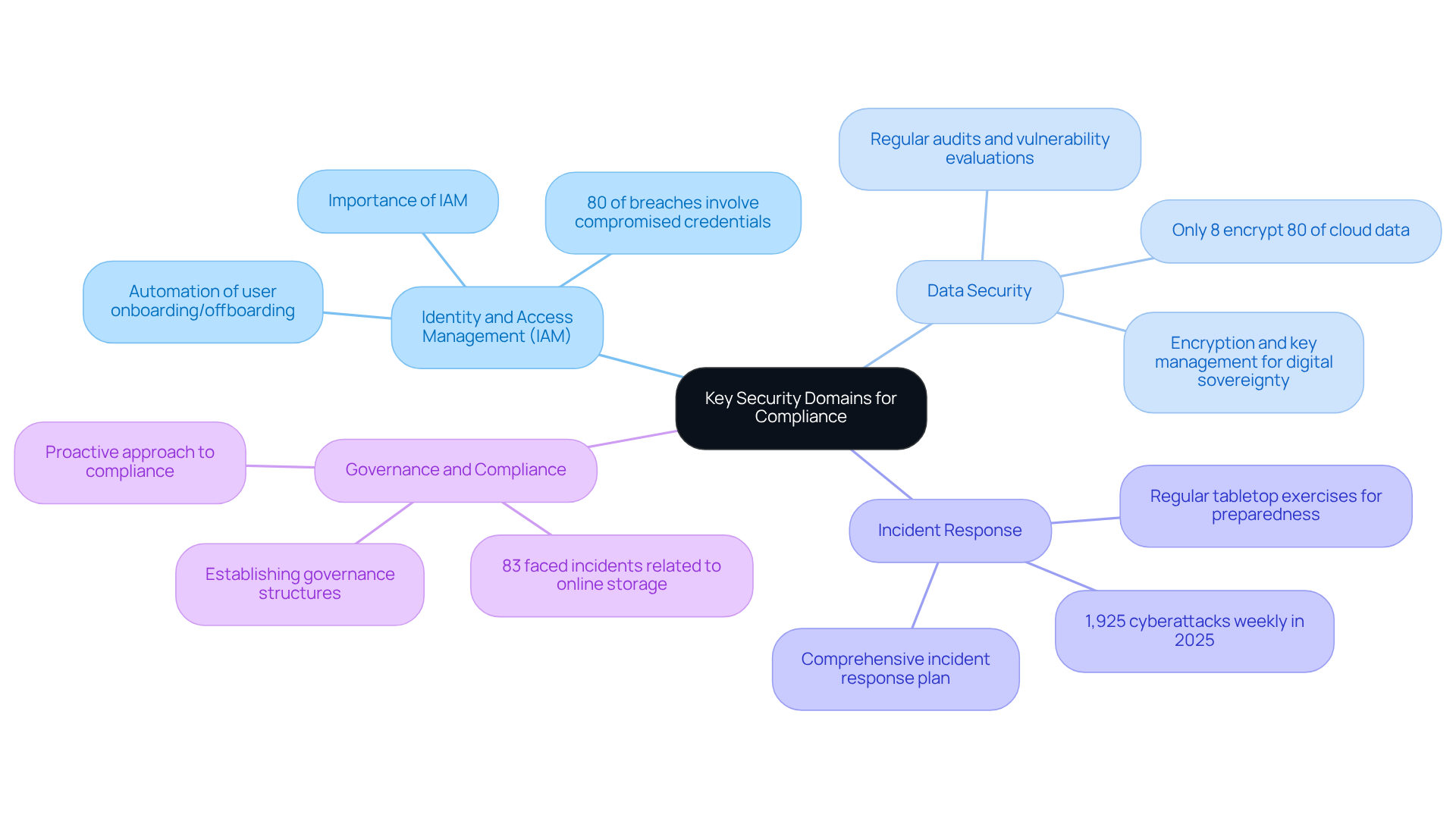
Identity and Access Management (IAM): Implementing robust IAM practices is essential for controlling user access and permissions. This ensures that only authorized personnel can access sensitive resources, significantly reducing the risk of insider threats. Did you know that by 2025, 80% of breaches will involve compromised or misused privileged credentials? This statistic underscores the importance of effective IAM strategies.
-
Data Security: Protecting data through encryption, tokenization, and secure storage practices is vital for mitigating risks associated with data breaches. Despite advancements, only 8% of entities encrypt 80% or more of their cloud data, leaving many sensitive assets unprotected. Regular audits and vulnerability evaluations can assist companies in recognizing and correcting weaknesses in their data protection strategies.
-
Incident Response: Creating a comprehensive incident response plan is essential for effectively handling incidents. This plan should outline procedures for detecting, responding to, and recovering from breaches. Entities that conduct regular tabletop exercises to evaluate their incident response strategies are better equipped to manage real-world events. With an average of 1,925 cyberattacks occurring weekly in 2025, this preparation is becoming increasingly crucial.
-
Governance and Compliance: Establishing governance structures that align with security compliance cloud standards ensures that policies and practices are consistently evaluated and refreshed. With 83% of entities encountering at least one incident related to online storage in the past 18 months, maintaining a proactive approach to governance is crucial for compliance and risk management.
By addressing these areas, companies can enhance their compliance initiatives and strengthen their overall safety stance, ensuring they are well-prepared to navigate the complexities of cloud environments. Furthermore, organizations should remain vigilant about the external connections they engage with, as these can impact compliance and safety. Regularly reviewing external resources and understanding their implications is essential for maintaining a robust security framework.
Implement Best Practices for Identity and Access Management
To enhance identity and access management in cloud environments, organizations must adopt the following best practices:
-
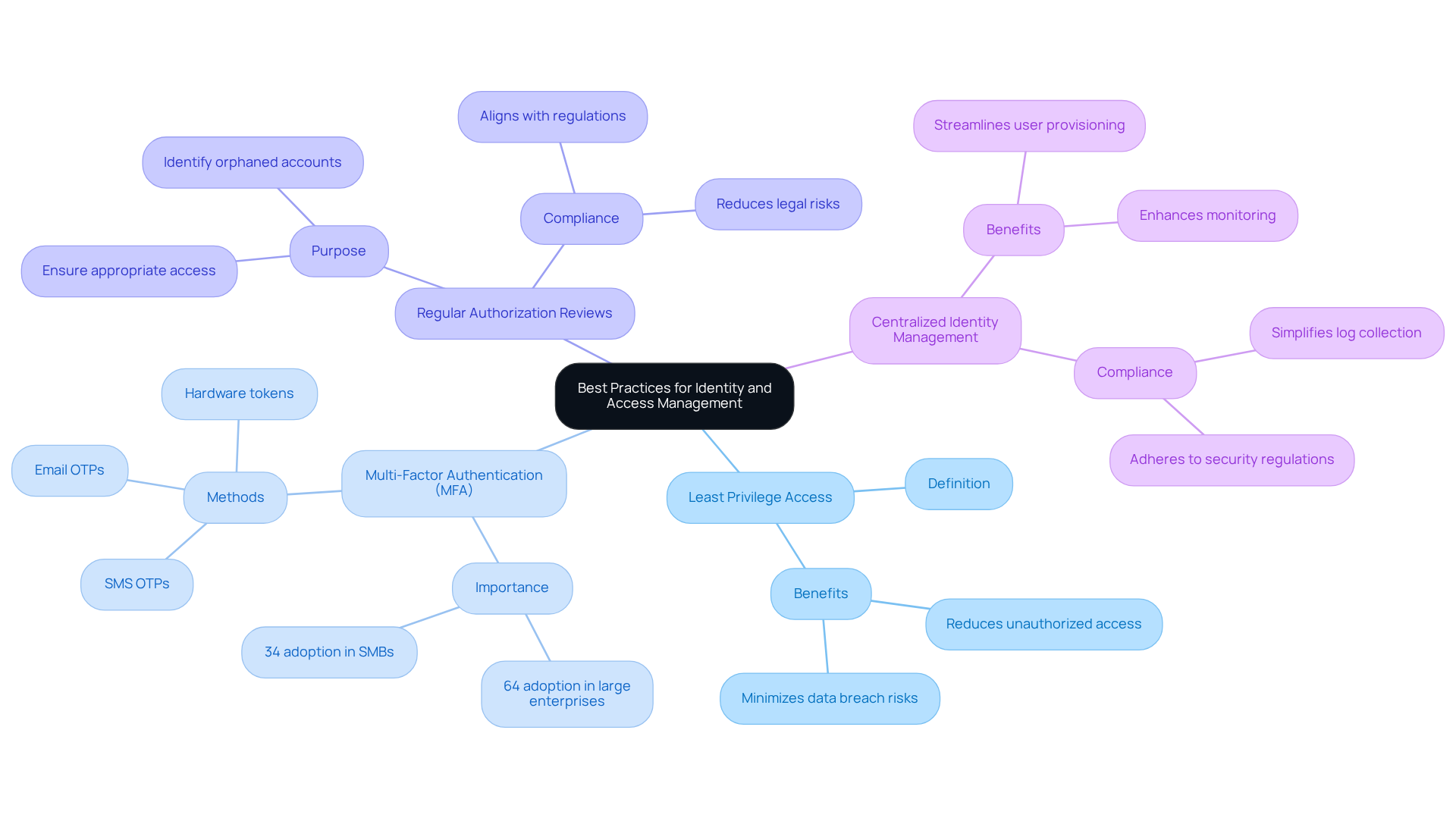
Least Privilege Access: Implement the principle of least privilege by granting users only the minimum level of access necessary for their job functions. This approach significantly reduces the risk of unauthorized access and potential data breaches, which can lead to compliance failures and corporate fraud.
-
Multi-Factor Authentication (MFA): The adoption of MFA is crucial for adding an extra layer of security. By requiring users to provide multiple forms of verification-such as passwords, biometrics, or one-time codes-organizations can effectively safeguard sensitive resources. As of 2025, large enterprises lead the MFA market with a 64% adoption rate, while 87% of companies with over 10,000 employees utilize MFA, compared to only about 34% of small and medium-sized businesses. This underscores the importance of MFA in securing cloud environments.
-
Regular Authorization Reviews: Conducting periodic evaluations of user permissions is essential to ensure that entitlements remain appropriate. Regular audits help identify and revoke access for users who no longer require it, thereby minimizing the risk of unauthorized access. This practice conforms to the requirements of security compliance cloud and improves the overall safety stance.
-
Centralized Identity Management: Utilizing centralized identity management solutions streamlines user provisioning and de-provisioning processes. This not only improves protection but also guarantees adherence to the security compliance cloud regulations. Centralizing log collection simplifies monitoring and assists entities in maintaining control over user permissions, adapting to changing business needs.
By applying these optimal methods, entities can greatly reduce the risk of identity-related breaches and improve their overall cybersecurity structure. As Chaithanya Yambari, co-founder of Zluri, emphasizes, "Implementing strong authentication methods and defining precise authorization protocols are critical for preventing unauthorized entry and ensuring data integrity." Furthermore, organizations should be aware of common pitfalls in MFA implementation, such as user resistance and inadequate training, to ensure successful adoption.
Establish Continuous Monitoring and Incident Response Strategies
To maintain a robust security posture in cloud environments, organizations must prioritize continuous monitoring and effective incident response strategies:
-
Real-Time Monitoring: Implement security information and event management (SIEM) tools to facilitate real-time monitoring of cloud environments. These tools are essential for detecting anomalies and potential threats. Did you know that 82% of data breaches in 2023 involved cloud-stored data? This statistic underscores the need for vigilance. Moreover, 69% of firms acknowledge they cannot uphold consistent protective measures across various cloud providers, emphasizing the difficulties encountered in multi-cloud settings.
-
Automated Alerts: Establish automated alerts for suspicious activities to ensure that security teams can respond swiftly to potential incidents. Statistics suggest that entities encounter an average of 1,925 cyberattacks weekly. Timely alerting is essential for reducing risks. However, organizations should be cautious of alert overload, which can desensitize teams and hinder effective incident response.
-
Incident Response Plan: Create and consistently revise a thorough incident response plan that clearly defines roles, responsibilities, and procedures for handling incidents. This proactive method is essential, as 83% of companies reported encountering a breach in the security compliance cloud in the past 18 months. Furthermore, 45% of entities lack skilled personnel to handle multi-cloud protection, highlighting the significance of having a strong incident response plan established.
-
Post-Incident Analysis: Conduct thorough post-incident analyses to identify root causes and refine response strategies for future incidents. This practice not only enhances preparedness but also contributes to ongoing enhancement in protective measures. As noted by NETSCOUT, continuous monitoring is more than a best practice; it’s a risk mitigator and compliance enabler.
By implementing these strategies, organizations can significantly enhance their capability to detect and respond to security threats effectively. Are you ready to safeguard your cloud environments?

Conclusion
In the realm of cloud environments, ensuring security compliance is not just a checkbox exercise; it’s a vital necessity for safeguarding sensitive data and maintaining organizational integrity. The shared responsibility model, robust data encryption, strict entry controls, and adherence to established frameworks form the bedrock of an effective security strategy. By grasping these foundational concepts, organizations can significantly enhance their security posture and mitigate risks associated with cloud computing.
The article highlights key practices that organizations must adopt to bolster their compliance initiatives. It emphasizes the importance of:
- Identity and access management
- Data security
- Incident response strategies
- Continuous monitoring
This underscores the need for a proactive approach. Implementing least privilege access, multi-factor authentication, and regular authorization reviews are essential steps that can substantially reduce vulnerabilities. Furthermore, real-time monitoring and comprehensive incident response plans are crucial for effectively addressing potential threats.
Ultimately, the significance of security compliance in cloud environments cannot be overstated. Organizations must remain vigilant and proactive, continuously refining their strategies to adapt to the evolving landscape of cyber threats. By embracing these best practices, they not only protect their assets but also foster trust with clients and stakeholders. The time to act is now-prioritize security compliance and equip your organization to thrive in the cloud.
Frequently Asked Questions
What are the core principles of cloud security?
The core principles of cloud security include understanding the shared responsibility model, implementing data encryption, establishing entry controls, and familiarizing oneself with relevant security compliance frameworks.
What is the Shared Responsibility Model in cloud security?
The Shared Responsibility Model indicates that security is a joint effort between the cloud service provider (CSP) and the customer. The CSP secures the infrastructure, while the customer is responsible for securing their data and applications.
Why is data encryption important in cloud security?
Data encryption is crucial for protecting sensitive information from unauthorized access, both when data is at rest and in transit. Strong encryption practices, such as using AES-256 algorithms, should be prioritized.
What are entry controls in the context of cloud security?
Entry controls are measures that ensure only authorized users can access sensitive data and applications. Effective access management is essential to reduce risks associated with unauthorized access.
What frameworks should organizations be familiar with for security compliance in the cloud?
Organizations should familiarize themselves with frameworks like NIST, ISO, and CMMC. The CMMC framework, in particular, provides strategies and insights for achieving compliance, especially for defense contractors.
How can organizations enhance their security compliance efforts?
Organizations can enhance their compliance efforts by engaging with peer insights, learning from best practices, and leveraging resources related to security compliance frameworks.
What should organizations do to prepare for online security challenges?
Organizations should master the fundamentals of cloud security to establish a robust foundation for their online protection strategy and ensure they are equipped to navigate security complexities.




