7 Key Frameworks for Cyber Security Risk and Compliance in Defense
Explore essential frameworks for managing cyber security risk and compliance in defense contracts.

Introduction
Navigating the intricate landscape of cybersecurity risk and compliance presents a formidable challenge for defense contractors today. With a multitude of frameworks at their disposal, organizations can gain invaluable insights that not only enhance their security posture but also ensure adherence to regulatory standards. But how can these frameworks be effectively implemented to meet compliance requirements while simultaneously fortifying defenses against ever-evolving cyber threats? This article explores seven key frameworks that offer a structured approach to addressing these pressing issues, providing actionable strategies and expert insights for organizations striving to excel in cybersecurity compliance.
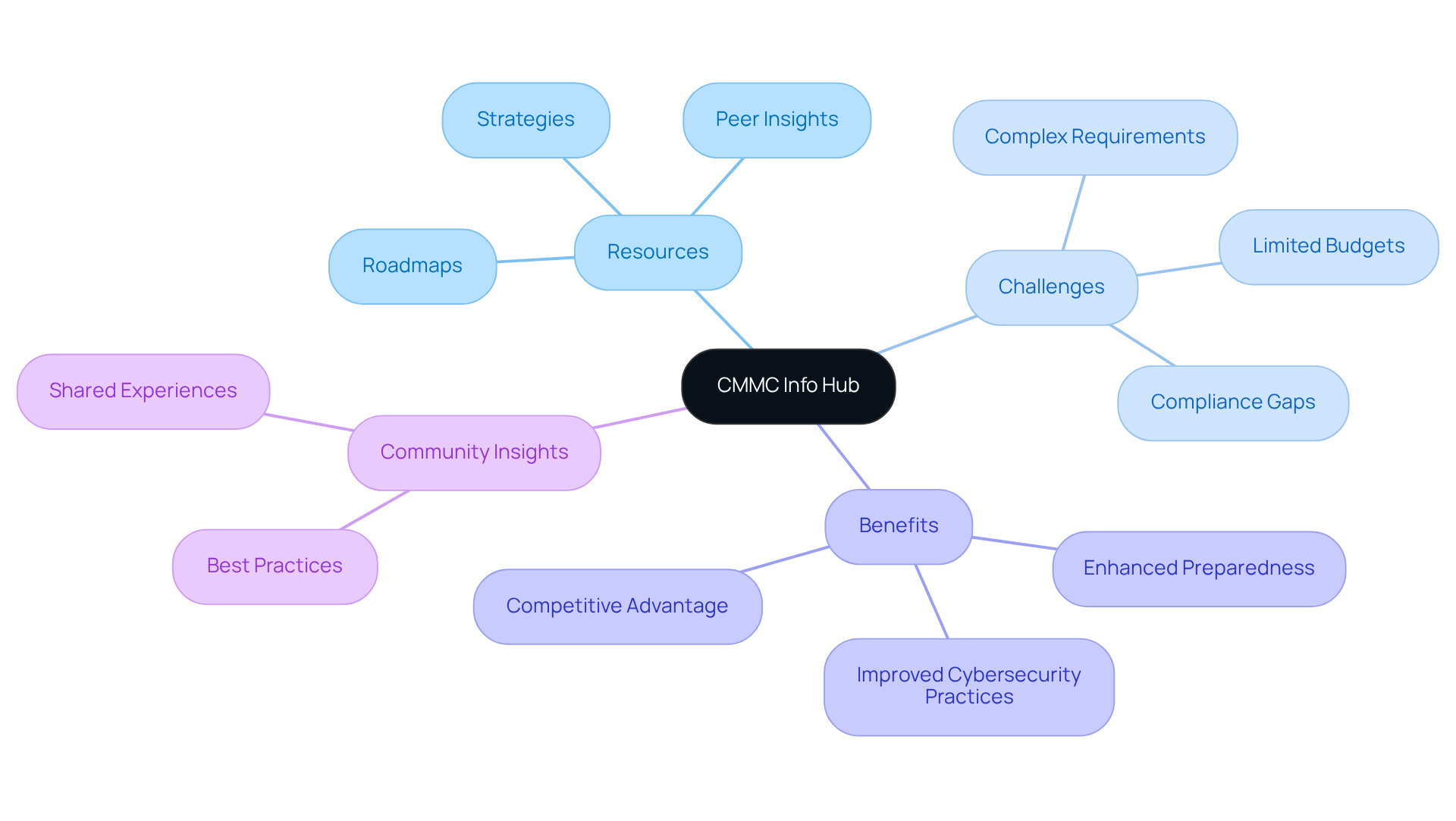
CMMC Info Hub: Your Essential Resource for Cybersecurity Maturity Model Certification Compliance
CMMC Info Hub serves as a comprehensive knowledge repository for organizations striving to achieve compliance with the cyber security risk and compliance requirements of the Cybersecurity Maturity Model Certification (CMMC). This platform is specifically designed to address the practical challenges faced by contractors, particularly the confusion surrounding complex requirements. With detailed roadmaps, actionable strategies, and insights from peers, the Hub empowers businesses to effectively navigate the intricacies of DoD cybersecurity requirements.
By focusing on CMMC-specific content, the platform ensures that users receive relevant information tailored to their compliance journey. This not only boosts their preparedness for defense contracts but also fortifies their cybersecurity practices. Have you considered how streamlined access to such resources can enhance your organization's readiness?
It's crucial to note that while CMMC Info Hub provides valuable resources, it does not oversee the content of external links and assumes no responsibility for their availability or accuracy. This distinction underscores the Hub's role as an essential resource for simplifying cyber security risk and compliance through community insights and actionable guidance.
In summary, leveraging the CMMC Info Hub can significantly enhance your organization's approach to cyber security risk and compliance. Don't miss out on the opportunity to strengthen your defenses and ensure readiness for future contracts.
NIST Cybersecurity Framework: A Comprehensive Approach to Risk Management
The NIST Cybersecurity Framework (CSF) offers a structured approach to managing cybersecurity risks, making it an essential tool for organizations today. It comprises five core functions:
- Identify
- Protect
- Detect
- Respond
- Recover
By adopting this framework, entities can create a comprehensive strategy for cyber security risk and compliance that not only meets regulatory standards but also enhances their overall cybersecurity posture.
Why is this important? The CSF's versatility allows companies to tailor its application to their specific needs and risk profiles. This adaptability makes it a vital resource for security providers. Recent updates to the CSF, including guidance released in April 2025, highlight its significance in tackling the ever-evolving landscape of cyber threats.
Consider this: statistics reveal that 95% of security breaches stem from human error. This alarming figure underscores the necessity of a robust framework like the CSF to effectively mitigate risks related to cyber security risk and compliance. Furthermore, the CMMC Info Hub provides practical strategies and peer insights that empower defense contractors to navigate the complexities of CMMC compliance with confidence.
In conclusion, leveraging the CSF not only improves risk management capabilities but also reinforces an organization's commitment to cybersecurity excellence. Are you ready to take action and enhance your cybersecurity framework?

ISO 27001 & ISO 27002 Frameworks: Standards for Information Security Management
ISO 27001 and ISO 27002 are internationally recognized standards that provide a robust framework for organizations to establish, implement, and maintain an Information Security Management System (ISMS). ISO 27001 outlines the specific requirements for an ISMS, while ISO 27002 delivers best practice recommendations for information security controls. Together, these standards empower organizations to protect sensitive information while ensuring cyber security risk and compliance with legal and regulatory mandates, significantly enhancing their overall security posture.
For contractors in the security sector, adherence to these standards is essential for safeguarding Controlled Unclassified Information (CUI) and ensuring cyber security risk and compliance with Department of Defense (DoD) regulations. Recent updates to ISO 27001, including the introduction of modernized controls, reflect the evolving cybersecurity landscape. These updates address contemporary challenges such as hybrid work environments and cloud security, making compliance more relevant than ever.
Consider the real-world implications: organizations that have successfully implemented ISMS in the security sector report enhanced risk management and a stronger security culture. These elements are vital for preserving trust with stakeholders and securing contracts. Moreover, integrating ISO 27001 with CMMC adherence can streamline processes, reduce duplication of efforts, and bolster overall readiness for audits in relation to cyber security risk and compliance.
In conclusion, the significance of ISO 27001 for security providers is profound. It not only aids in meeting regulatory requirements but also greatly enhances an organization’s ability to manage information security effectively in a rapidly evolving digital environment. Are you ready to take the necessary steps towards compliance and security excellence?

SOC 2 Framework: Ensuring Data Security and Privacy Compliance
The SOC 2 framework, established by the American Institute of CPAs (AICPA), emphasizes five Trust Service Criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Why should organizations pursue SOC 2 adherence? Implementing robust security controls and undergoing regular audits not only demonstrates a commitment to protecting customer data but also significantly enhances an organization's cyber security risk and compliance.
For security providers, achieving SOC 2 compliance is more than just a checkbox; it builds trust with clients. When clients know that their sensitive information is managed with the utmost care and integrity, it fosters a strong relationship. This trust is invaluable in today’s data-driven landscape.
In conclusion, organizations that prioritize SOC 2 compliance not only protect their customers but also strengthen their cyber security risk and compliance, positioning themselves as leaders in security. Are you ready to take the next step in safeguarding your data and enhancing client trust? Embrace the SOC 2 framework and leverage the resources available to ensure your organization meets these critical standards.

NERC-CIP Framework: Cybersecurity for Critical Infrastructure Protection
The North American Electric Reliability Corporation's Critical Infrastructure Protection (NERC-CIP) standards play a crucial role in securing the bulk electric system against cyber threats. These standards mandate that organizations implement specific security measures to safeguard critical infrastructure. This includes:
- Conducting risk assessments
- Developing incident response plans
- Providing employee training
For security firms operating in the energy sector, cyber security risk and compliance with NERC-CIP is not merely a legal requirement; it is a fundamental aspect of national safety, ensuring the resilience of essential services against cyber threats.
In addition to NERC-CIP, defense contractors must also consider the cyber security risk and compliance aspects of the Cybersecurity Maturity Model Certification (CMMC) as part of their compliance strategy. How can organizations effectively navigate these requirements? The CMMC Info Hub serves as a comprehensive resource for achieving CMMC standards, offering practical strategies and insights that can significantly enhance cybersecurity programs. By utilizing these resources, organizations can ensure adherence to necessary regulations and bolster their defenses against potential cyber threats.

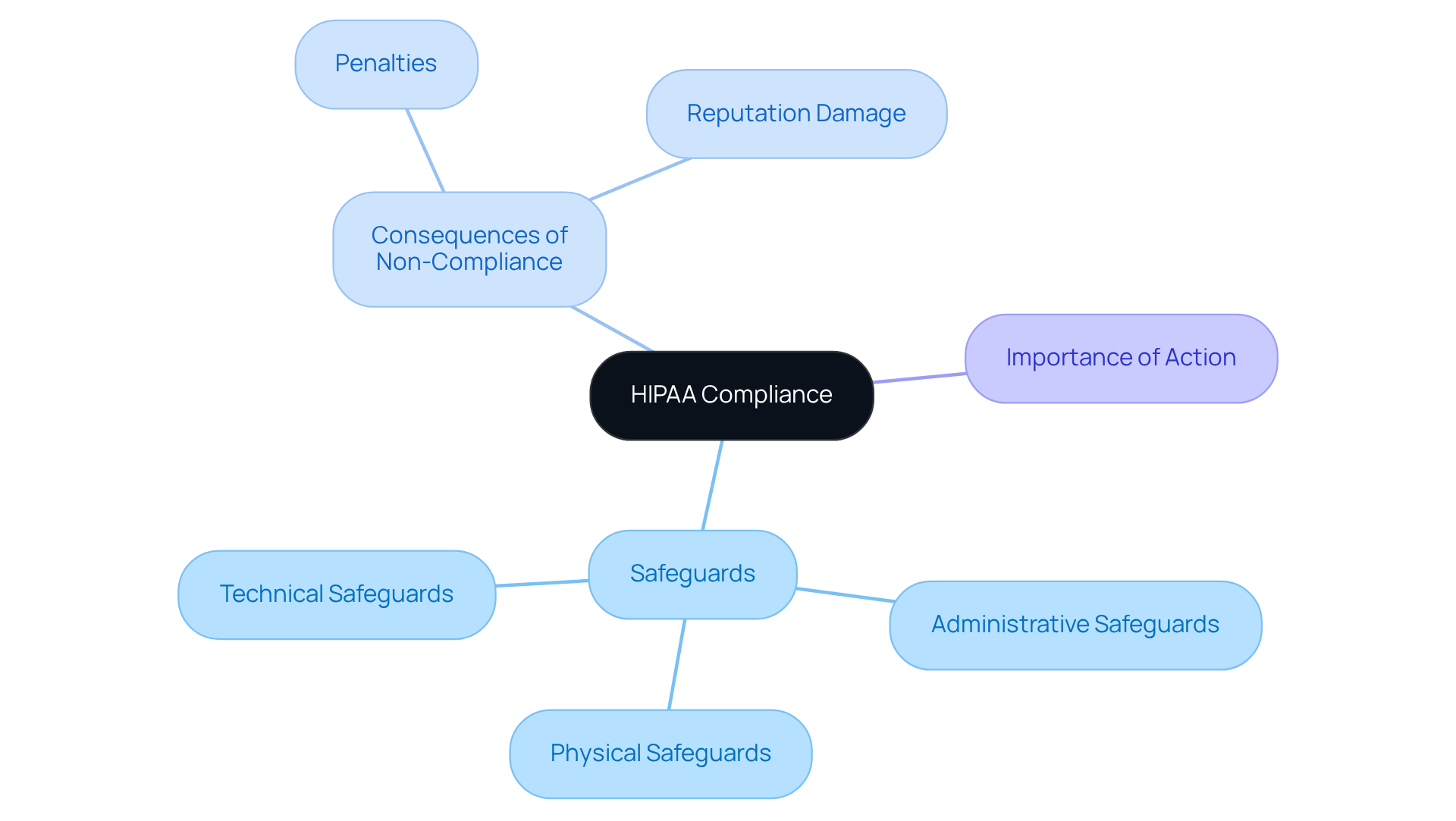
HIPAA Framework: Protecting Health Information in Defense Contracts
The Health Insurance Portability and Accountability Act (HIPAA) sets national standards for safeguarding sensitive patient information. Why is this important? Organizations managing protected health information (PHI) must implement administrative, physical, and technical safeguards to mitigate cyber security risk and compliance. For defense contractors involved in healthcare-related projects, adhering to HIPAA is essential for cyber security risk and compliance, as it protects patient data and maintains federal standards.
Failure to comply with HIPAA can lead to severe penalties and damage a company’s reputation. The stakes are high, and understanding these regulations related to cyber security risk and compliance is crucial for any organization in the healthcare sector. By prioritizing HIPAA compliance, companies can address cyber security risk and compliance, avoiding costly repercussions while also building trust with their clients and stakeholders.
In summary, the commitment to HIPAA is a vital step in safeguarding patient information and ensuring the integrity of healthcare operations. Organizations must take action now to implement the necessary safeguards in order to address cyber security risk and compliance.
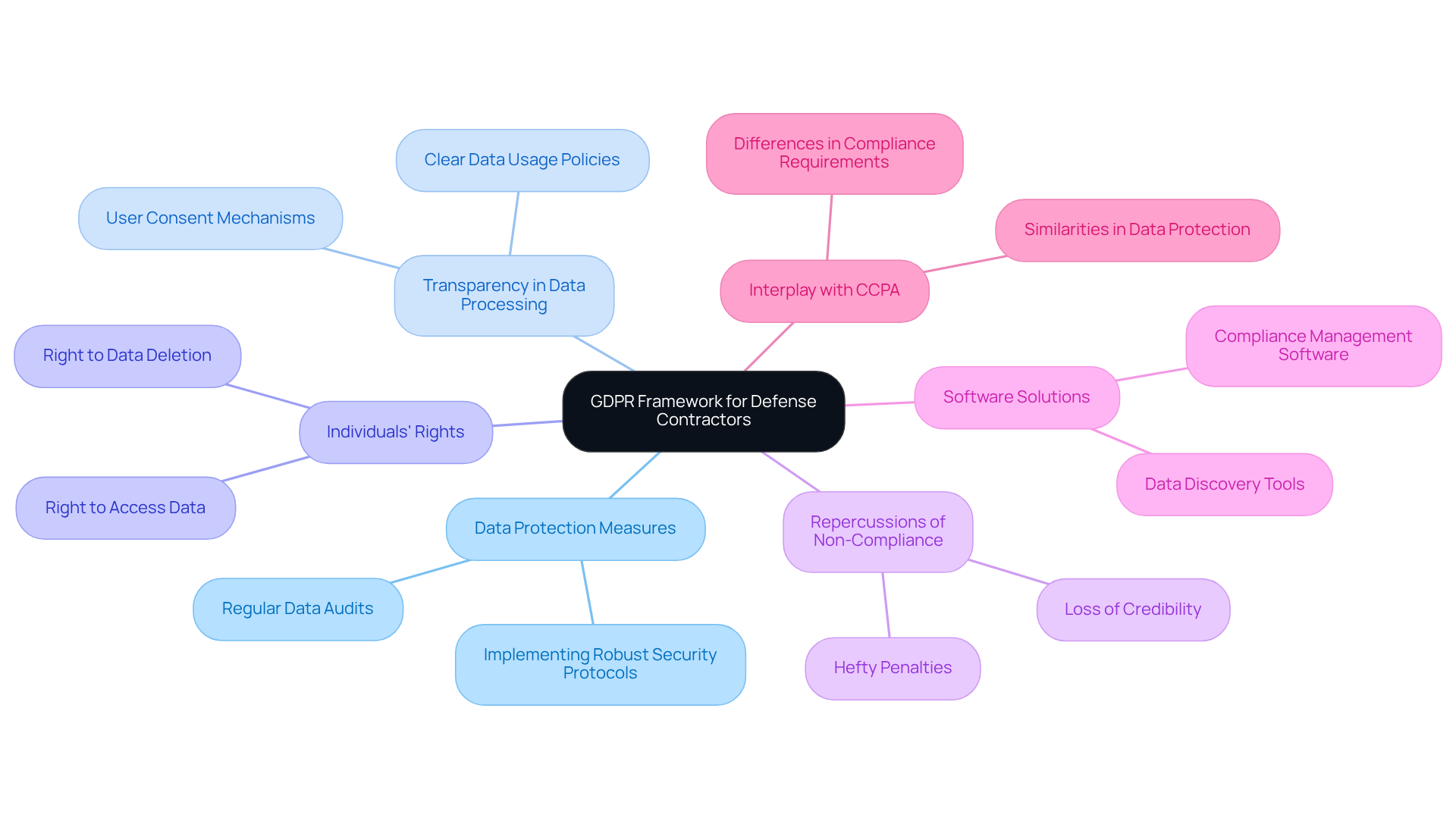
GDPR Framework: Ensuring Data Protection and Compliance for Defense Contractors
The General Data Protection Regulation (GDPR) stands as a pivotal data protection law that mandates compliance from organizations managing the personal data of EU citizens, irrespective of their geographical location. For defense contractors, adhering to GDPR is not just important; it is essential when handling data related to EU individuals. This compliance involves:
- Implementing robust data protection measures
- Ensuring transparency in data processing activities
- Upholding individuals' rights concerning their personal data
As Tim Cook, CEO of Apple, emphasizes, data protection ranks among the most pressing issues of the 21st century, highlighting the critical nature of GDPR compliance. The repercussions of non-compliance can be severe, including hefty penalties, which underscores the necessity for organizations to weave GDPR requirements into their cyber security risk and compliance frameworks.
Moreover, organizations must deploy software solutions to identify personal information across all datasets, including backups, to mitigate regulatory risks. By doing so, security providers not only safeguard sensitive information but also enhance their credibility and trustworthiness within the competitive military sector.
Understanding the interplay between GDPR and the California Consumer Privacy Act (CCPA) is also vital for defense contractors navigating compliance. Both regulations stress the significance of data protection and consumer rights.
In conclusion, the integration of GDPR into organizational practices is not merely a legal obligation; it is a strategic advantage that can bolster an organization's reputation and operational integrity.
Conclusion
Understanding and implementing key frameworks for cybersecurity risk and compliance is essential for organizations in the defense sector. These frameworks not only provide structured approaches to managing cyber threats but also ensure that companies meet the regulatory requirements necessary for operating in this highly sensitive environment. By focusing on frameworks such as CMMC, NIST, ISO standards, SOC 2, NERC-CIP, HIPAA, and GDPR, organizations can significantly enhance their cybersecurity posture and ensure compliance with critical regulations.
Each framework plays a vital role in addressing specific cybersecurity needs. For instance:
- The CMMC Info Hub offers invaluable resources for navigating compliance challenges.
- The NIST Cybersecurity Framework provides a comprehensive strategy for risk management.
- ISO standards establish robust information security management systems.
- SOC 2 compliance fosters trust with clients.
- NERC-CIP safeguards critical infrastructure.
- HIPAA protects sensitive health information.
- GDPR ensures data protection for EU citizens.
Each of these frameworks contributes uniquely to a holistic cybersecurity strategy.
Embracing these frameworks is not just a matter of compliance; it is a strategic imperative that can safeguard sensitive information, build client trust, and enhance operational integrity. Organizations in the defense sector are urged to take proactive steps towards implementing these frameworks. By leveraging available resources and fostering a culture of cybersecurity excellence, they can navigate the complexities of the cybersecurity landscape and position themselves as leaders in the defense industry.
Frequently Asked Questions
What is the purpose of the CMMC Info Hub?
The CMMC Info Hub serves as a comprehensive knowledge repository for organizations aiming to achieve compliance with the cybersecurity requirements of the Cybersecurity Maturity Model Certification (CMMC). It addresses the practical challenges faced by contractors and provides detailed roadmaps, actionable strategies, and insights from peers.
How does the CMMC Info Hub help organizations?
The Hub empowers businesses to navigate the complexities of DoD cybersecurity requirements by offering CMMC-specific content, which enhances their preparedness for defense contracts and strengthens their cybersecurity practices.
Does the CMMC Info Hub oversee the content of external links?
No, the CMMC Info Hub does not oversee the content of external links and assumes no responsibility for their availability or accuracy.
What is the NIST Cybersecurity Framework (CSF)?
The NIST Cybersecurity Framework (CSF) is a structured approach to managing cybersecurity risks, consisting of five core functions: Identify, Protect, Detect, Respond, and Recover.
Why is the NIST Cybersecurity Framework important?
The CSF is important because it helps organizations create a comprehensive strategy for cybersecurity risk and compliance that meets regulatory standards and enhances overall cybersecurity posture. Its adaptability allows companies to tailor its application to their specific needs and risk profiles.
What recent updates have been made to the NIST Cybersecurity Framework?
Recent updates to the CSF, including guidance released in April 2025, highlight its significance in addressing the evolving landscape of cyber threats.
What statistic emphasizes the need for a robust cybersecurity framework?
Statistics reveal that 95% of security breaches stem from human error, underscoring the necessity of a robust framework like the CSF to effectively mitigate cybersecurity risks.
How does the CMMC Info Hub complement the NIST Cybersecurity Framework?
The CMMC Info Hub provides practical strategies and peer insights that help defense contractors navigate the complexities of CMMC compliance, reinforcing their commitment to cybersecurity excellence.




