7 Key Frameworks for Governance in Cyber Security Compliance
Explore essential frameworks for governance in cyber security compliance to enhance your organization's security.

Overview
The article titled "7 Key Frameworks for Governance in Cyber Security Compliance" identifies essential frameworks that organizations can leverage to ensure compliance with cybersecurity governance standards. It highlights various frameworks, including:
- NIST
- ISO 27001
- SOC 2
- NERC-CIP
- HIPAA
- GDPR
Each of these frameworks plays a crucial role in enhancing security measures, mitigating risks, and ensuring regulatory compliance.
Why is this important? In today’s complex cybersecurity landscape, organizations face numerous challenges. Compliance with these frameworks not only strengthens security but also builds trust with stakeholders. For instance, adhering to GDPR can enhance customer confidence, while compliance with HIPAA is vital for healthcare organizations.
To effectively implement these frameworks, organizations should assess their current security posture and identify gaps. This proactive approach can lead to improved security measures and reduced risks.
In conclusion, utilizing these frameworks is not just about compliance; it’s about fostering a culture of security within the organization. By prioritizing these standards, organizations can navigate the complexities of cybersecurity with confidence.
Introduction
In an era where cyber threats are more prevalent than ever, organizations are confronted with the formidable challenge of navigating a complex landscape of compliance frameworks designed to protect their operations. This article explores seven essential frameworks that not only serve as a roadmap for governance in cybersecurity compliance but also empower organizations to strengthen their defenses against emerging threats.
With regulations constantly evolving and the stakes of non-compliance rising, one pressing question emerges: how can organizations effectively implement these frameworks to not only fulfill regulatory requirements but also gain a competitive advantage in the marketplace?
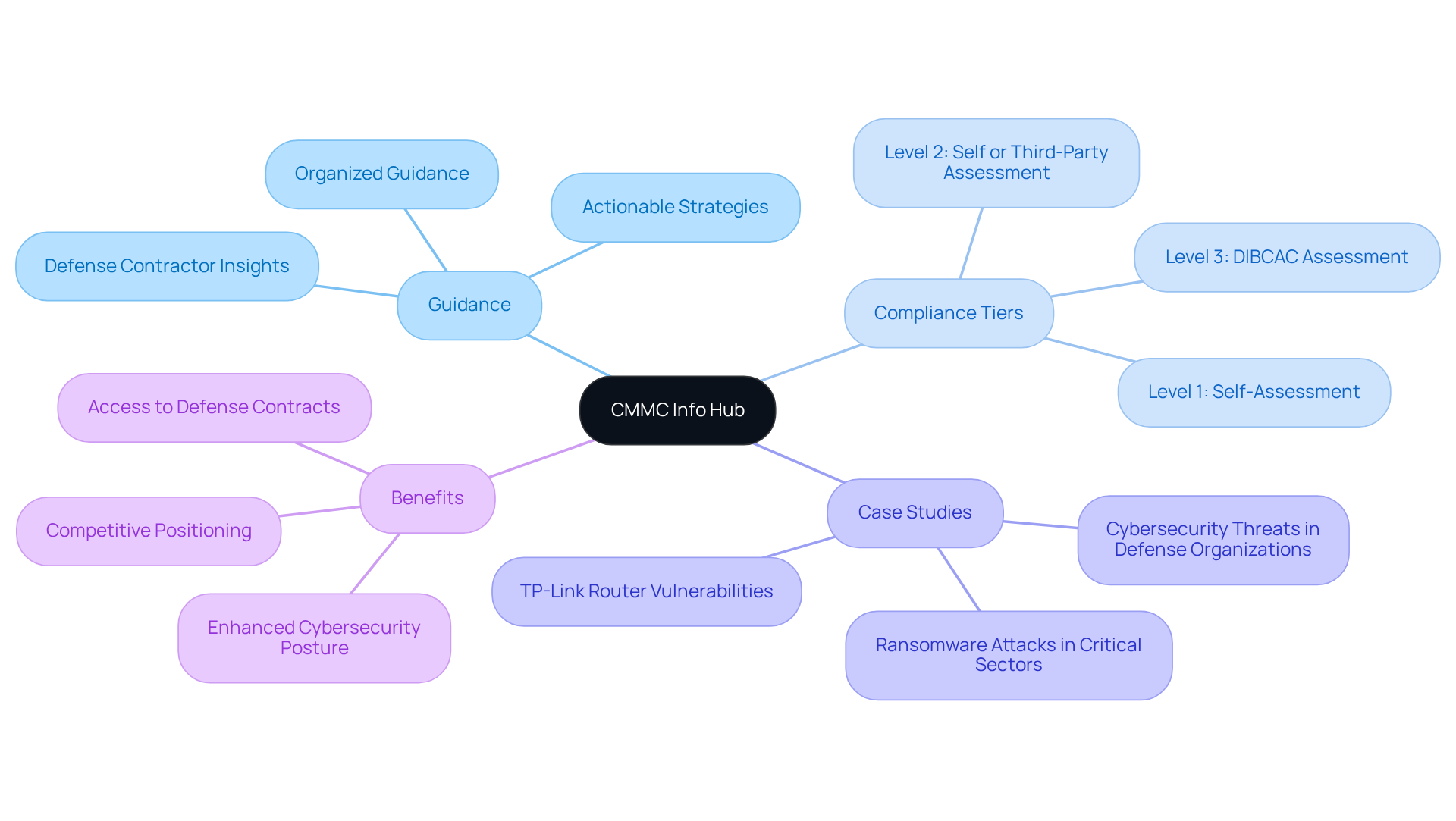
CMMC Info Hub: Your Essential Resource for Cybersecurity Maturity Model Certification
CMMC Info Hub stands as an essential resource for organizations aiming to meet the governance cyber security standards set by the Cybersecurity Maturity Model Certification. This platform provides organized guidance, comprehensive plans, and actionable strategies that encompass all facets of security standards. By leveraging insights from cybersecurity experts and learning from peer experiences, Info Hub empowers defense contractors and IT specialists to adeptly navigate the intricate landscape of DoD governance cyber security requirements. This capability is crucial for securing defense contracts and protecting sensitive information effectively.
Recent updates indicate that the cybersecurity framework is evolving, with a phased implementation designed to alleviate the regulatory burden on small businesses. As the final regulation takes effect, organizations must prioritize understanding the specific compliance tiers pertinent to their operations. Currently, only 270 defense contractors hold final certifications, while a staggering 80,000 are expected to achieve Level 2 certification by 2025. Successful case studies reveal that organizations adopting robust governance cyber security compliance programs not only enhance their cybersecurity posture but also position themselves competitively within the defense market.
In this context, the Info Hub emerges as a vital partner in the governance cyber security compliance journey, offering tailored insights and strategies that directly address the unique challenges faced by defense contractors. Are you ready to take the next step in securing your organization’s future? Engage with the Info Hub today to ensure you’re not just compliant but also competitive.
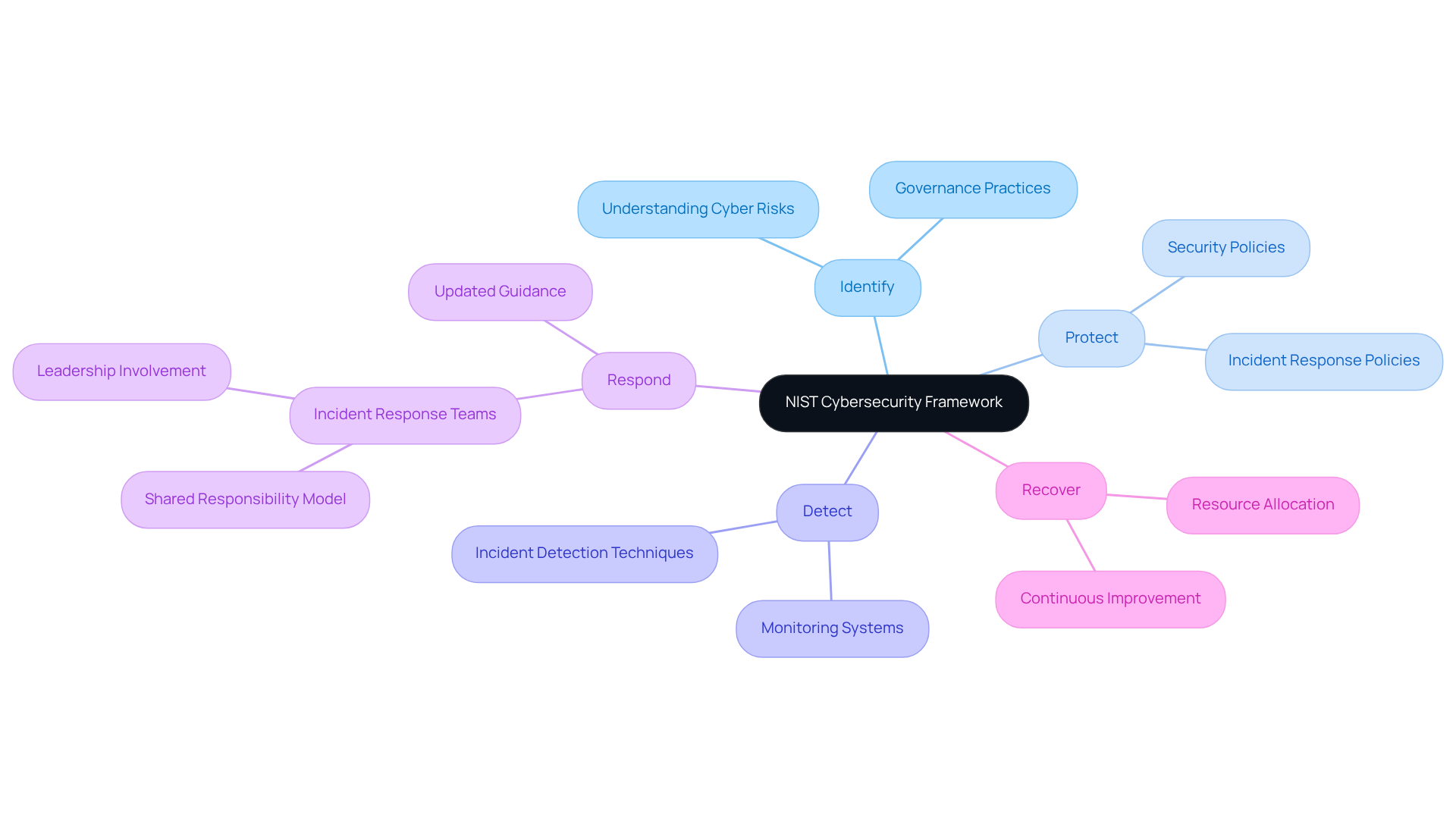
NIST Cybersecurity Framework: A Comprehensive Approach to Risk Management
The NIST Cybersecurity Framework (CSF) provides a robust methodology for managing cybersecurity risks, centered around five essential functions: Identify, Protect, Detect, Respond, and Recover. This framework empowers organizations to evaluate their current cybersecurity posture, pinpoint vulnerabilities, and implement critical controls to effectively mitigate risks. By embracing the NIST CSF, organizations not only bolster their defenses against cyber threats but also ensure compliance with various regulatory standards, including the Cybersecurity Maturity Model Certification (CMMC).
Recent updates to the CSF, particularly the Manufacturing Profile released in September 2025, underscore the necessity of weaving cybersecurity practices into the fabric of overall business governance. This integration is vital as organizations confront escalating pressures from cyber threats, with reports indicating a surge in ransomware attacks and supply chain vulnerabilities. Moreover, entities utilizing the NIST CSF have noted improved communication of cyber risks to leadership, fostering continuous security enhancements and more efficient resource allocation.
Key strategies for leveraging the NIST CSF include:
- Enhancing incident response capabilities through updated guidance released in April 2025.
- Implementing a 'shared responsibility' model for incident response teams to encourage collaboration.
- Utilizing insights from the CMMC Info Hub to ensure adherence to certification requirements with confidence.
For further information, please refer to the FAQs and external links available on the CMMC Info Hub, which provide additional resources and support for defense contractors navigating CMMC requirements. As the cybersecurity landscape evolves, the NIST CSF remains an indispensable tool for organizations striving to enhance their compliance and protective measures.
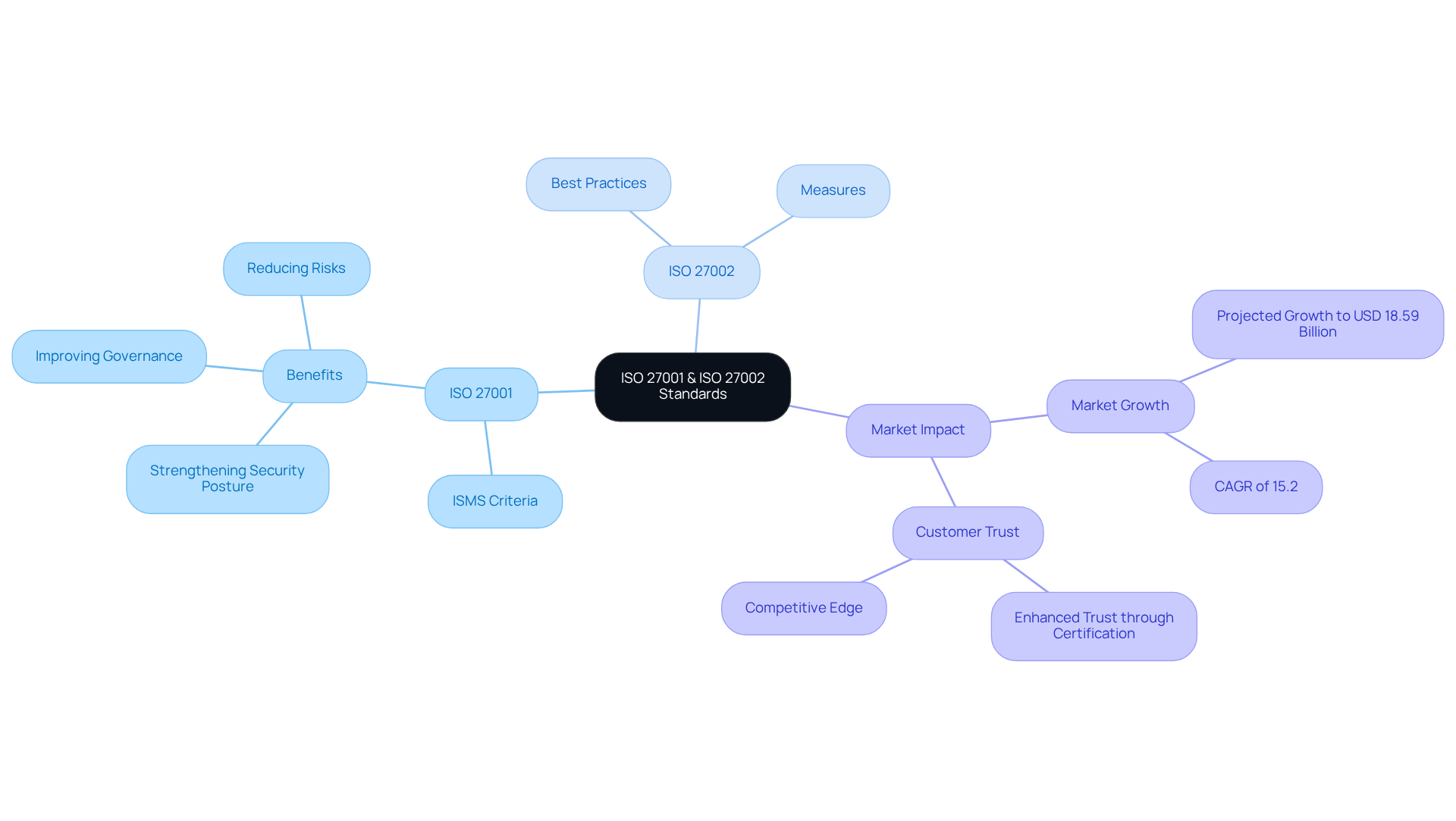
ISO 27001 & ISO 27002: Standards for Information Security Management
ISO 27001 and ISO 27002 stand as internationally recognized standards, providing a robust framework for establishing, implementing, maintaining, and continuously enhancing an information protection management system (ISMS). Why should your organization consider these standards? ISO 27001 specifies the criteria for an ISMS, while ISO 27002 offers best practice recommendations for effective information protection measures.
Obtaining ISO certification not only strengthens a company's security posture but also significantly improves governance cyber security by reducing risks associated with data breaches and cyber threats. Furthermore, organizations that adopt these standards often experience improved compliance with regulatory requirements, which is crucial in today’s competitive landscape. In fact, by 2025, the global number of ISO 27001 certificates is expected to exceed 70,000, highlighting the growing recognition of its significance.
What does this mean for the market? The ISO certification market is projected to expand from USD 16.14 billion in 2024 to approximately USD 18.59 billion in 2025, reflecting a compound annual growth rate (CAGR) of around 15.2%. Industry leaders have noted that achieving ISO 27001 certification can enhance customer trust and bolster market position. This makes governance cyber security a critical investment for organizations that aim to protect sensitive information and maintain a competitive edge.
In conclusion, embracing ISO 27001 and ISO 27002 is not just about compliance; it’s about securing your organization’s future in a digital world. Are you ready to take the next step towards safeguarding your information?
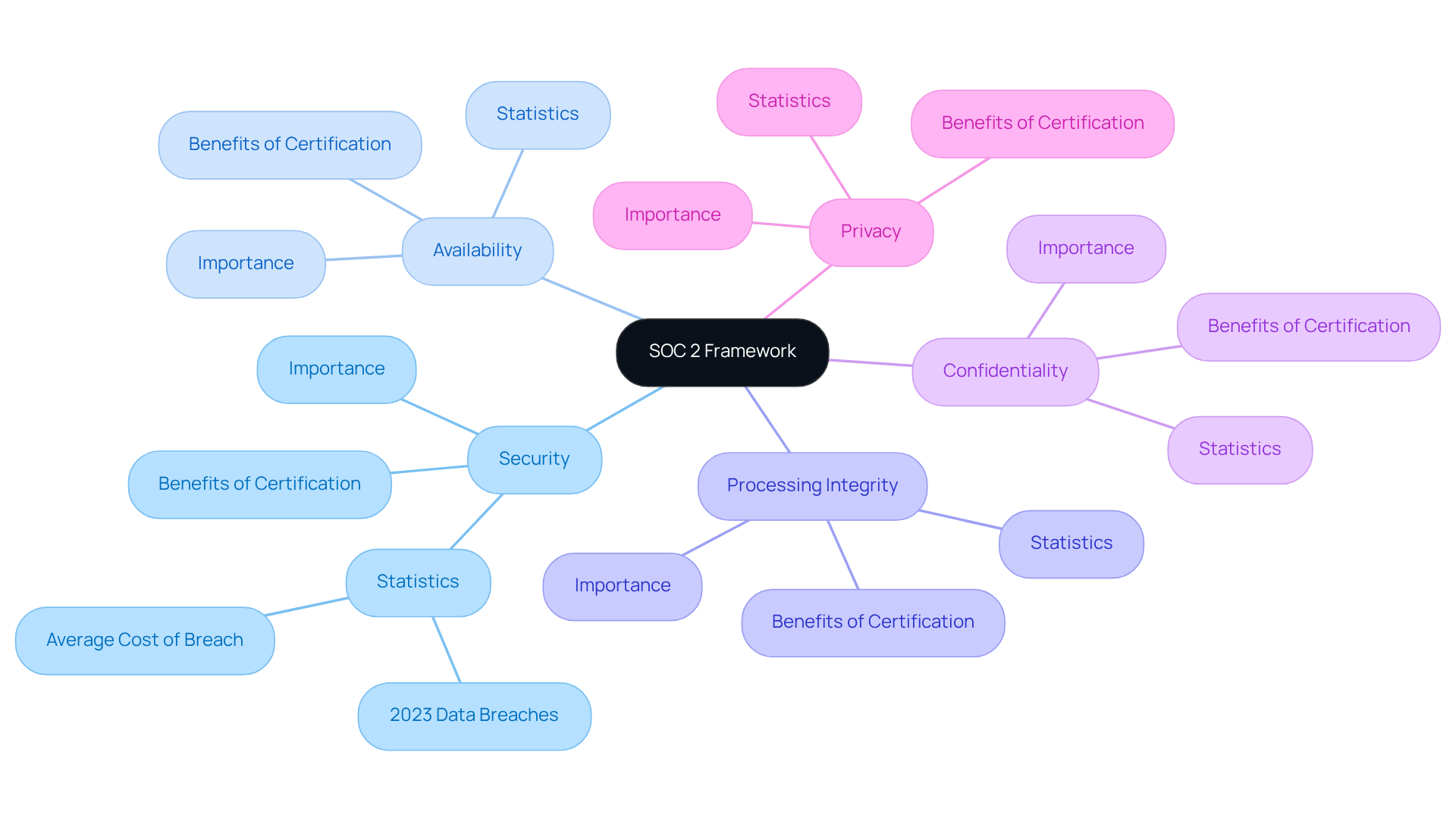
SOC 2 Framework: Ensuring Data Security and Privacy
The SOC 2 framework, developed by the American Institute of CPAs (AICPA), emphasizes five Trust Services Criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Organizations that achieve SOC 2 certification demonstrate a strong commitment to protecting customer data and implementing robust security practices. This framework is especially crucial for technology and cloud-based service providers, as it fosters trust with clients and stakeholders by ensuring that effective controls are in place to protect sensitive information.
Recent statistics underscore the importance of adhering to SOC 2 standards. In 2023, the U.S. reported a staggering 3,205 data breaches, marking a 78% increase from the previous year. The global average cost of a data breach reached USD 4.45 million, highlighting the financial risks associated with non-compliance. This alarming trend emphasizes the necessity for organizations to adopt comprehensive protective measures, such as those outlined in the SOC 2 framework, to mitigate risks and enhance their security posture.
Organizations that have successfully obtained SOC 2 certification, like a prominent SBA lender service firm featured in recent case studies, have experienced notable enhancements in their operational credibility and competitive edge. This certification not only reflects a commitment to security regulations but also paves the way for business growth, as clients increasingly seek partnerships with compliant organizations.
Experts assert that a well-structured SOC 2 compliance program not only reduces the likelihood of data breaches but also attracts new customers. Vlad Anikin, Chief Technology Officer at Trisk, emphasizes the importance of having a robust, stable, and reliable system for customer-facing operations. Furthermore, engaging a qualified third-party CPA firm to assess SOC 2 controls instills confidence in management and executives regarding their data protection strategies. This proactive approach to governance cyber security compliance is vital in today’s rapidly evolving cybersecurity landscape, where the stakes are higher than ever. Additionally, achieving SOC 2 compliance can facilitate adherence to other regulatory frameworks, enhancing a company's overall compliance strategy.
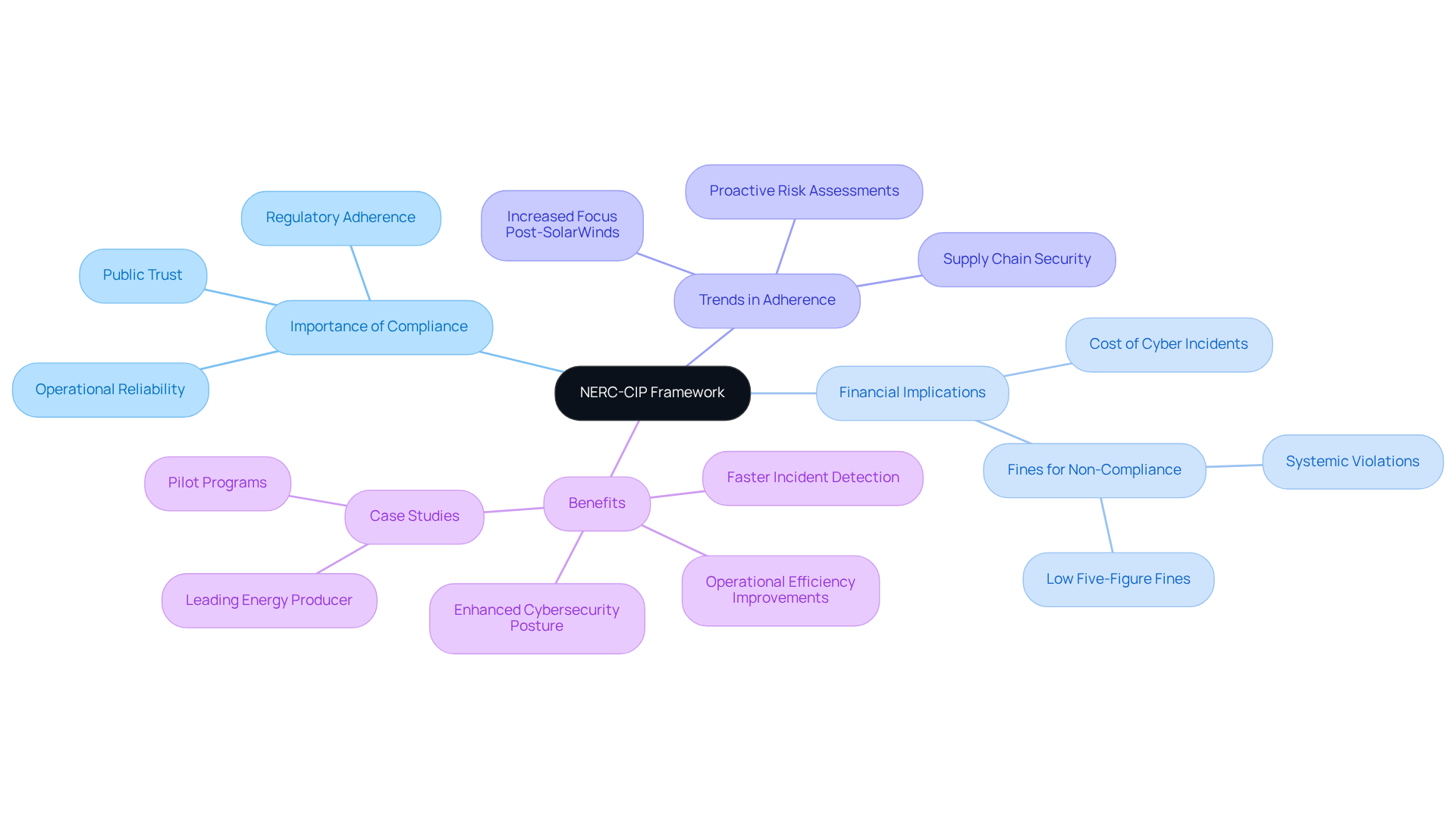
NERC-CIP Framework: Cybersecurity for Critical Infrastructure
The North American Electric Reliability Corporation's Critical Infrastructure Protection (NERC-CIP) standards are essential for strengthening the cybersecurity of the bulk electric system. These standards mandate specific protective measures that organizations must implement to shield vital infrastructure from cyber threats. For example, compliance with NERC-CIP can avert fines exceeding one million dollars for systemic violations, underscoring the financial stakes of regulatory noncompliance. Additionally, organizations that embrace these standards not only mitigate regulatory risks but also enhance their overall cybersecurity posture, ensuring the reliability and safety of critical services.
Recent trends indicate that the electric utility sector is placing greater emphasis on adhering to NERC-CIP, particularly in light of supply chain vulnerabilities exposed by high-profile incidents like the SolarWinds attack. This shift highlights the necessity for ongoing risk assessments and the development of robust incident response plans, which are crucial for maintaining operational integrity.
Successful case studies demonstrate the tangible benefits of NERC-CIP standards in practice. For instance, a leading energy producer reported significant improvements in operational efficiency and cybersecurity compliance after implementing these standards. Moreover, organizations engaged in proactive monitoring and regular vulnerability assessments can detect security incidents up to 60% faster than those relying solely on sporadic reviews.
The importance of NERC-CIP compliance extends beyond mere regulatory adherence; it is vital for protecting critical infrastructure and ensuring the uninterrupted delivery of services. As the cyber threat landscape continues to evolve, organizations must remain vigilant and dedicated to implementing these standards to protect their operations and uphold public trust.
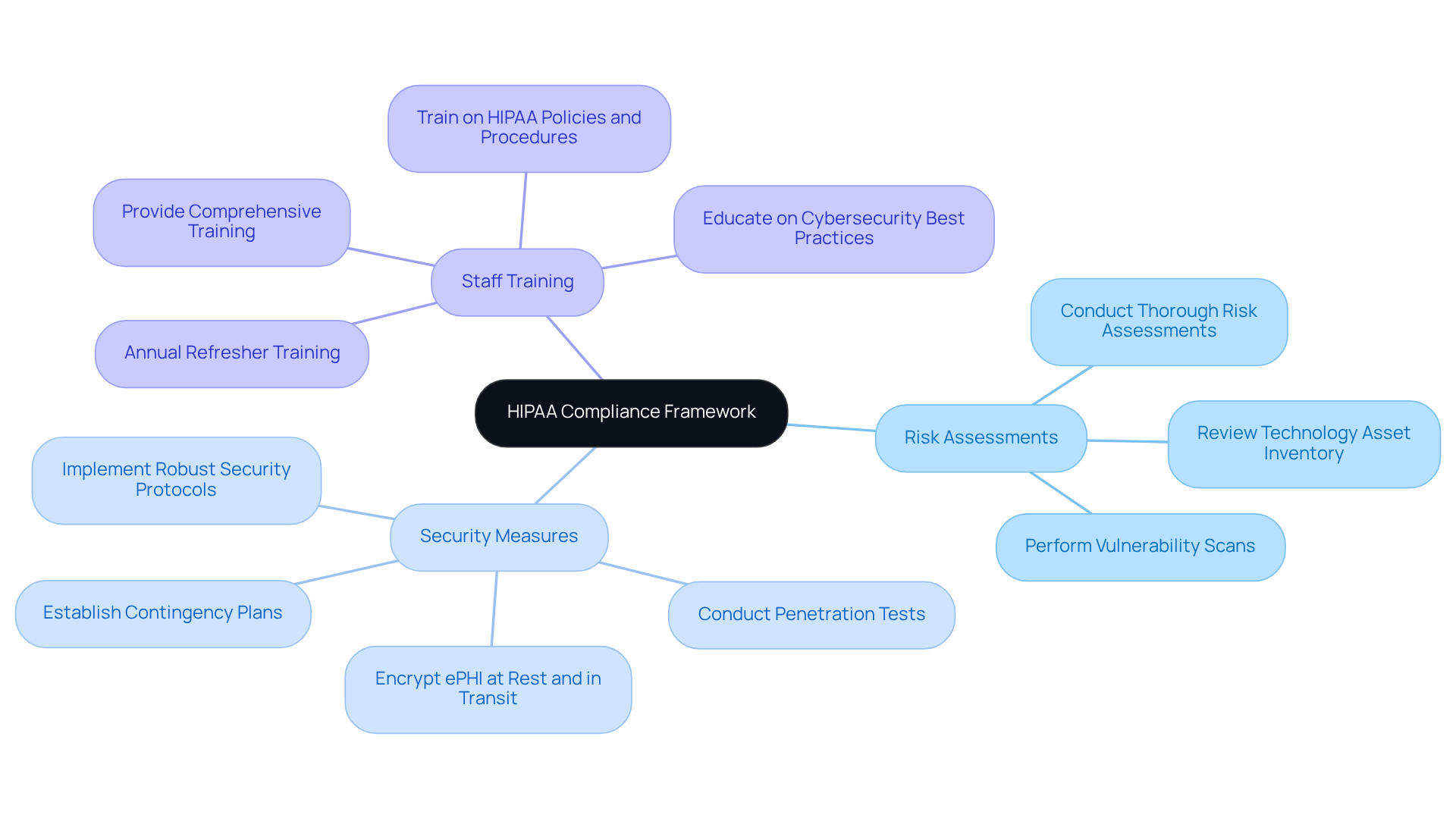
HIPAA Framework: Protecting Health Information Security
The Health Insurance Portability and Accountability Act (HIPAA) sets national standards for safeguarding sensitive patient health information. Organizations that manage protected health information (PHI) must comply with HIPAA regulations to uphold the confidentiality, integrity, and availability of patient data.
Key components of HIPAA adherence include:
- Conducting thorough risk assessments
- Implementing robust security measures
- Ensuring comprehensive training for staff
For instance, in 2023, over 168 million records were compromised, underscoring the critical need for rigorous adherence practices. By following HIPAA standards, entities can effectively mitigate risks and foster trust with patients—an essential aspect of the healthcare sector.
Recent updates to HIPAA regulations, particularly the changes to the Privacy Rule in 2024, further highlight the importance of protecting patient information, especially in sensitive areas like reproductive health. As industry leaders advocate for enhanced governance cyber security protocols, organizations are encouraged to adopt these frameworks to ensure compliance and protect patient health information efficiently.
Moreover, when utilizing external resources for HIPAA adherence, it’s vital to verify the reliability of these sources. The inclusion of links to outside websites can impact the credibility of the information provided. Are you ready to take the necessary steps to ensure compliance and safeguard your patients' information?
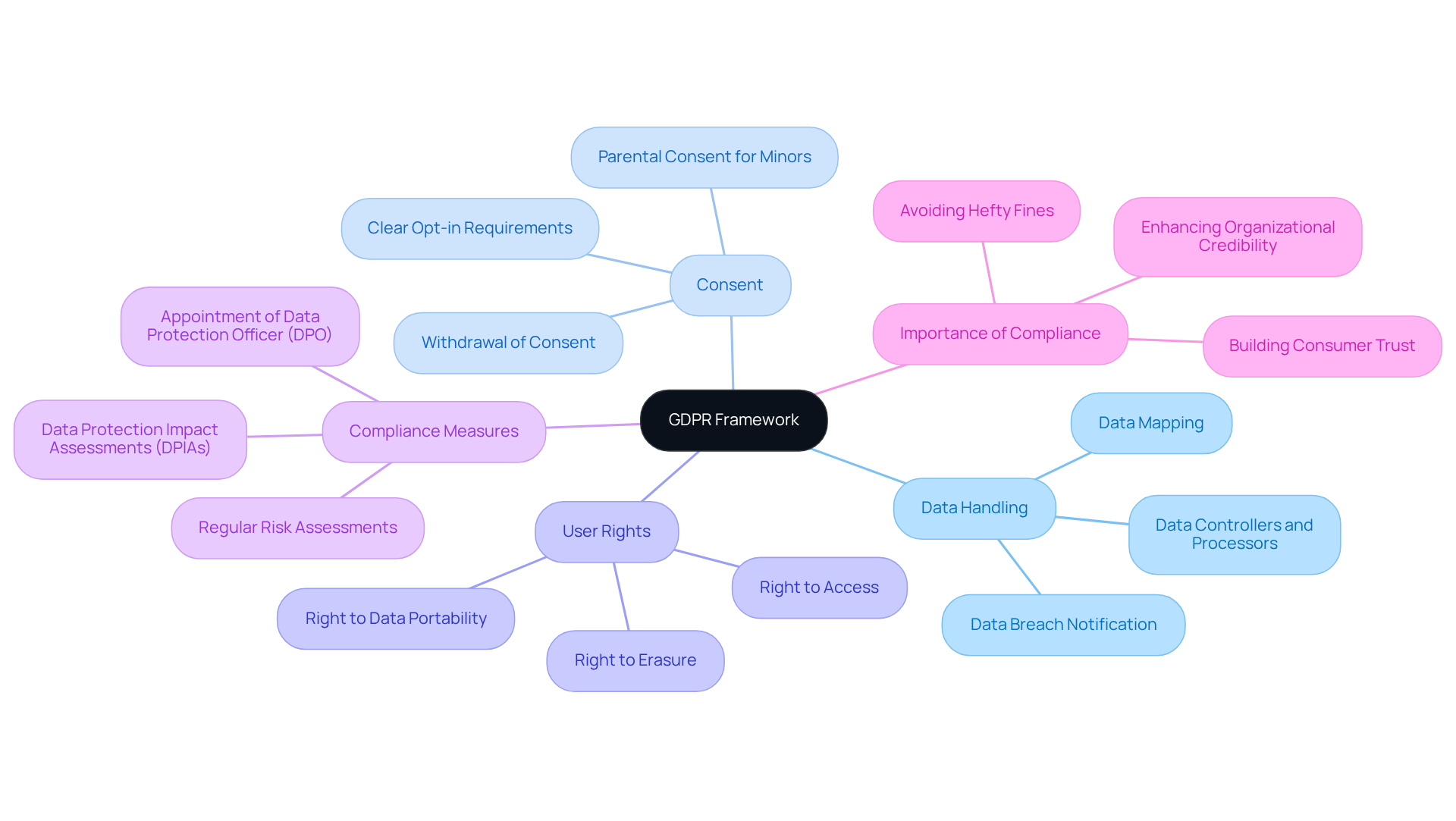
GDPR Framework: Ensuring Data Protection and Privacy Compliance
The General Data Protection Regulation (GDPR) serves as a vital framework for data protection, detailing how organizations must manage the personal data of EU citizens. It imposes stringent criteria on data handling, consent, and user rights, compelling entities to adopt robust technical and administrative measures for compliance. This includes conducting Data Protection Impact Assessments (DPIAs) and appointing a Data Protection Officer (DPO) when necessary.
Why is this important? By aligning with GDPR standards, organizations not only bolster their data protection practices but also mitigate the risk of hefty fines, which can reach £17.5 million or 4% of global revenue for violations. Recent trends reveal an intensified focus on GDPR enforcement, with the Federal Trade Commission (FTC) poised to ramp up scrutiny in 2024, signaling an expected surge in enforcement activities.
Leaders in the field emphasize that effective GDPR implementation safeguards personal data and fosters consumer trust. This makes it imperative for organizations to prioritize compliance as a core aspect of their operations. Furthermore, keeping privacy policies up-to-date is essential for ensuring transparency and adherence to GDPR requirements.
In conclusion, organizations must recognize that GDPR compliance is not just a regulatory obligation; it is a strategic advantage that enhances credibility and trust with consumers. Are you ready to take the necessary steps to ensure compliance?
Conclusion
The frameworks for governance in cybersecurity compliance are essential for organizations aiming to bolster their security posture and meet regulatory demands. By embracing structured approaches like CMMC, NIST, ISO 27001, SOC 2, NERC-CIP, HIPAA, and GDPR, businesses can achieve compliance and foster trust with stakeholders and customers. These frameworks act as blueprints, guiding organizations in identifying vulnerabilities, implementing robust security measures, and continuously enhancing their cybersecurity strategies.
Key insights into each framework have been highlighted, showcasing their unique contributions to governance and compliance. For instance:
- The CMMC Info Hub provides targeted support for defense contractors.
- The NIST Cybersecurity Framework emphasizes a comprehensive risk management approach.
- ISO standards enhance information security management.
- SOC 2 certification builds trust in data protection practices.
- NERC-CIP ensures the safety of critical infrastructure.
- HIPAA safeguards patient health information.
- GDPR mandates stringent data handling practices.
Each framework plays a vital role in protecting sensitive information and mitigating risks.
As the cybersecurity landscape evolves, organizations must recognize the urgency of implementing these frameworks to stay ahead of emerging threats. The time to act is now—prioritize compliance not just as a regulatory necessity but as a strategic advantage that can enhance your organization’s reputation and operational resilience. Engage with these frameworks to secure a future that fosters a culture of trust and accountability in your cybersecurity practices.
Frequently Asked Questions
What is the CMMC Info Hub?
The CMMC Info Hub is a resource designed for organizations seeking to meet the cybersecurity standards set by the Cybersecurity Maturity Model Certification (CMMC). It offers organized guidance, comprehensive plans, and actionable strategies for navigating DoD governance cyber security requirements.
Who can benefit from the CMMC Info Hub?
Defense contractors and IT specialists can benefit from the CMMC Info Hub as it provides insights from cybersecurity experts and peer experiences to help them comply with cybersecurity standards and secure defense contracts.
What recent changes have been made to the CMMC framework?
The CMMC framework is evolving with a phased implementation aimed at reducing the regulatory burden on small businesses. Organizations must now focus on understanding the specific compliance tiers relevant to their operations.
How many defense contractors currently hold CMMC certifications?
As of now, only 270 defense contractors hold final certifications, while around 80,000 are expected to achieve Level 2 certification by 2025.
What advantages do organizations gain by adopting robust governance cyber security compliance programs?
Organizations that implement strong governance cyber security compliance programs enhance their cybersecurity posture and improve their competitive positioning within the defense market.
What does the NIST Cybersecurity Framework (CSF) focus on?
The NIST Cybersecurity Framework focuses on five essential functions: Identify, Protect, Detect, Respond, and Recover, which help organizations manage cybersecurity risks effectively.
How does the NIST CSF assist organizations in compliance?
By adopting the NIST CSF, organizations can bolster their defenses against cyber threats and ensure compliance with various regulatory standards, including CMMC.
What recent updates were made to the NIST CSF?
Recent updates include the Manufacturing Profile released in September 2025, emphasizing the integration of cybersecurity practices into overall business governance.
What key strategies can organizations use to leverage the NIST CSF?
Key strategies include enhancing incident response capabilities, implementing a shared responsibility model for incident response teams, and utilizing insights from the CMMC Info Hub for certification adherence.
Where can additional resources and support for CMMC requirements be found?
Additional resources and support can be found on the CMMC Info Hub, which provides FAQs and external links to assist defense contractors in navigating CMMC requirements.




