9 Steps to Build Your Data Privacy Compliance Program
Build an effective data privacy compliance program with these 9 essential steps.

Introduction
Building a data privacy compliance program is no longer just a checkbox exercise; it’s a strategic necessity for organizations navigating the complex landscape of regulatory requirements. With data breaches becoming increasingly costly and consumer trust dwindling, the imperative to safeguard sensitive information has never been clearer.
This article explores nine essential steps that guide organizations in establishing a robust compliance framework. These steps not only highlight the significant benefits of prioritizing data privacy but also underscore the importance of being proactive in today’s evolving regulatory environment.
However, with regulations constantly changing and the ever-present threat of cyber incidents looming, how can businesses ensure they are not just compliant but also ahead of the curve in their data protection efforts? Let's delve into these critical steps and discover how to fortify your organization's data privacy strategy.
CMMC Info Hub: Your Guide to Building a Data Privacy Compliance Program
CMMC Info Hub serves as a vital resource for organizations aiming to establish a robust information protection adherence program. It provides structured guidance, detailed roadmaps, and practical strategies that empower businesses to develop a robust data privacy compliance program to meet the stringent requirements of data privacy regulations. Are you navigating the complexities of compliance? The Hub clarifies the confusion surrounding regulatory requirements, offering defense contractors and entities within the defense supply chain access to actionable insights and community-driven solutions. This ensures they can effectively secure sensitive information and maintain adherence to the Cybersecurity Maturity Model Certification (CMMC). Ultimately, this enhances cybersecurity and regulatory standards across the industry.
By leveraging the resources available through the CMMC Info Hub, organizations can not only comply with regulations but also improve their data privacy compliance program and strengthen their overall cybersecurity posture. Don't miss out on the opportunity to elevate your compliance efforts and protect your sensitive data.
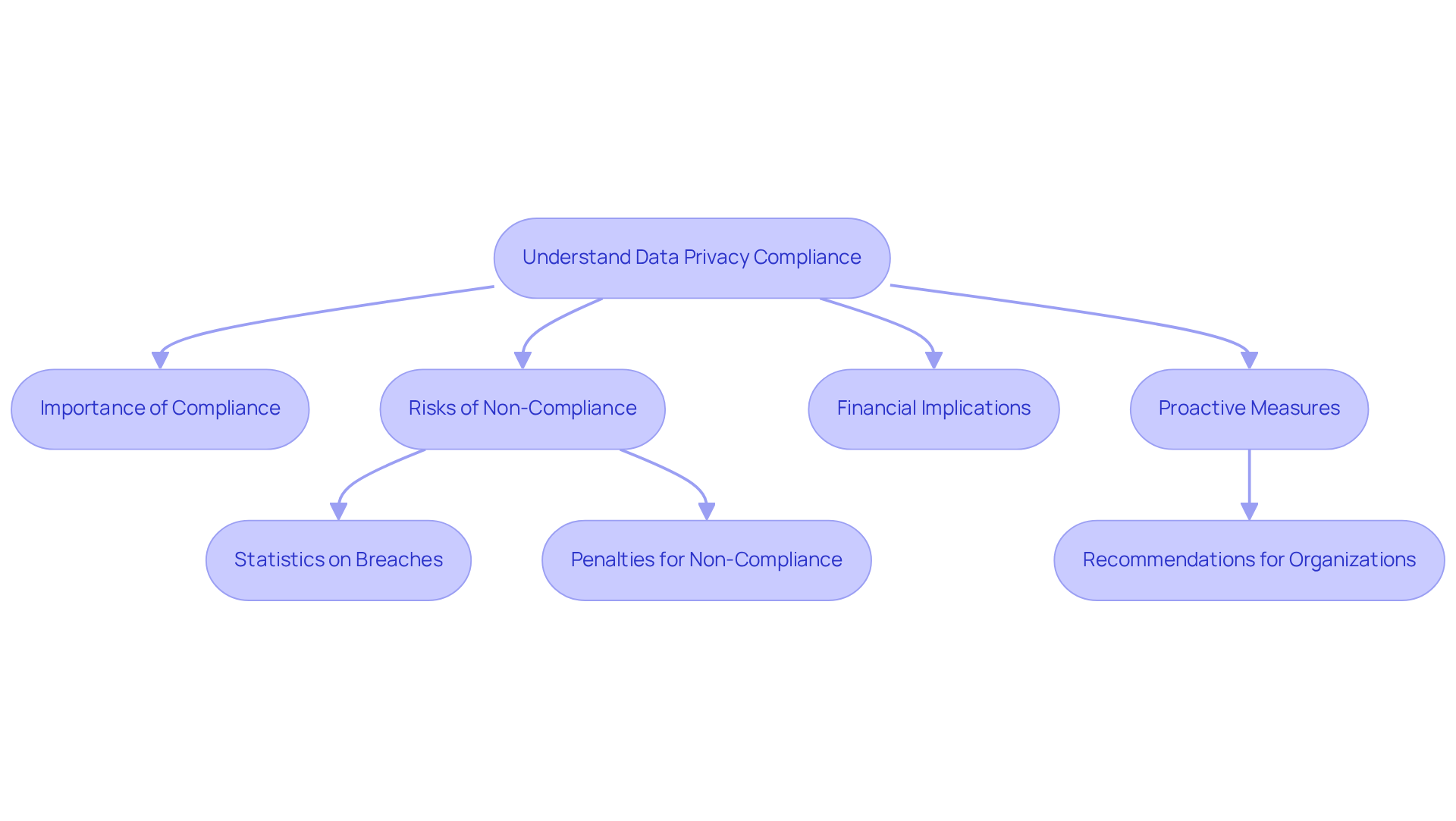
Understand the Importance of Data Privacy Compliance
Data privacy adherence is not just important; it’s essential for safeguarding sensitive information and building customer trust. Organizations that overlook compliance risk facing hefty penalties, legal troubles, and damage to their reputation. Did you know that the average cost of a data breach in the U.S. soared to $10.22 million in 2025? Globally, the average hit $4.44 million. These figures underscore the financial stakes involved. Cybersecurity experts emphasize that companies must proactively address data protection issues rather than waiting for problems to arise. Alarmingly, nearly half of Americans (48%) have stopped purchasing from businesses due to security concerns. Furthermore, 94% of firms acknowledge that clients would refrain from buying if they fail to adequately protect data. This clearly illustrates how data mismanagement can directly impact customer loyalty.
Real-world penalties for non-compliance further highlight these risks. For instance, California's Attorney General recently fined Sephora $1.2 million for failing to honor consumer opt-out requests. In California, penalties for violations can reach $2,500 per infraction or up to $7,500 for willful breaches. Additionally, organizations that disregard confidentiality regulations may face class-action lawsuits, draining resources and time-especially for small businesses, where legal defense costs can be overwhelming.
By prioritizing information security, organizations not only protect their assets but also strengthen their data privacy compliance program and enhance their credibility in the marketplace. As confidentiality regulations evolve, understanding legal responsibilities becomes vital for navigating compliance complexities within a data privacy compliance program and mitigating risks associated with data breaches. Embracing a culture of compliance through a data privacy compliance program can transform data protection from a mere obligation into a competitive advantage, fostering trust and loyalty among customers. To begin emphasizing information confidentiality, companies should regularly review their privacy policies and invest in training employees on data hygiene.
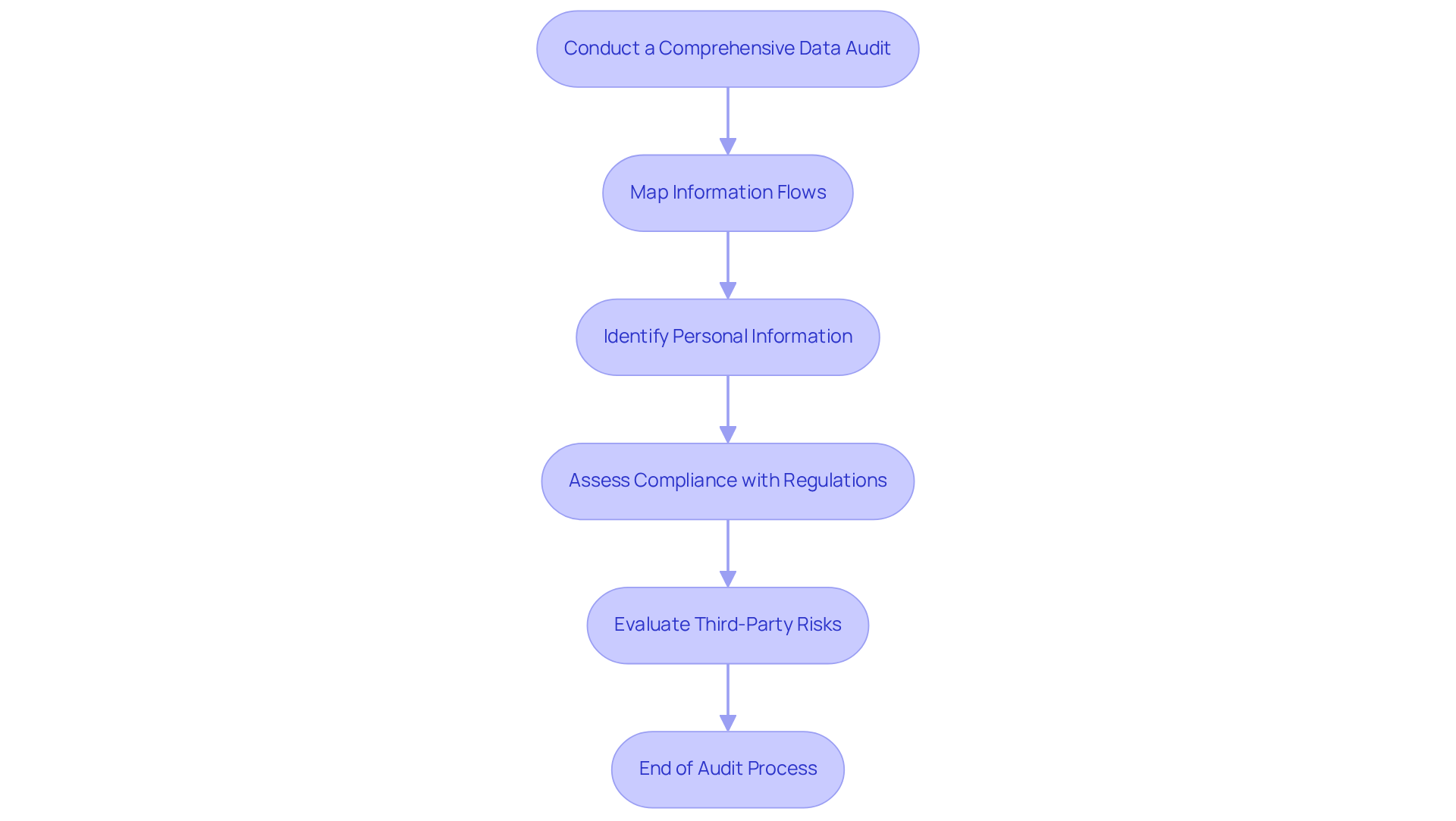
Conduct a Comprehensive Data Audit
Conducting a thorough information review is essential for organizations aiming to establish a data privacy compliance program that meets information protection standards. This process involves meticulously mapping all information flows within the organization, which includes identifying the types of personal information collected, the methods of processing, and the storage locations. By understanding these components, organizations can effectively assess their data privacy compliance program in relation to privacy regulations like GDPR and CMMC, while pinpointing any gaps that need addressing.
But why are routine audits so critical? They are not just a regulatory requirement; they are vital for maintaining information integrity and security. In fact, a significant 58% of regulatory teams report conducting four or more audits each year to ensure compliance and mitigate risks associated with data breaches. This statistic highlights the necessity of regular audits in today’s dynamic compliance environment.
To keep policies effective and relevant, organizations should adopt key practices for policy maintenance. This includes:
- Reviewing policies at least once a year
- Establishing a formal process for proposing and approving changes
- Maintaining version control
- Archiving previous policy versions
- Clearly communicating any updates to all relevant personnel
Consider this: a staggering 98% of organizations have relationships with third parties that have faced a breach in the past two years. This underscores the urgent need for businesses to evaluate and manage the risks linked to their third-party vendors. Leading firms have successfully implemented information mapping strategies to clarify their information flows, which aids in their data privacy compliance program efforts. These practices not only boost transparency but also enhance risk management and accountability. By prioritizing comprehensive information reviews alongside diligent policy maintenance, organizations can strengthen their data privacy compliance program and safeguard personal information from potential breaches.
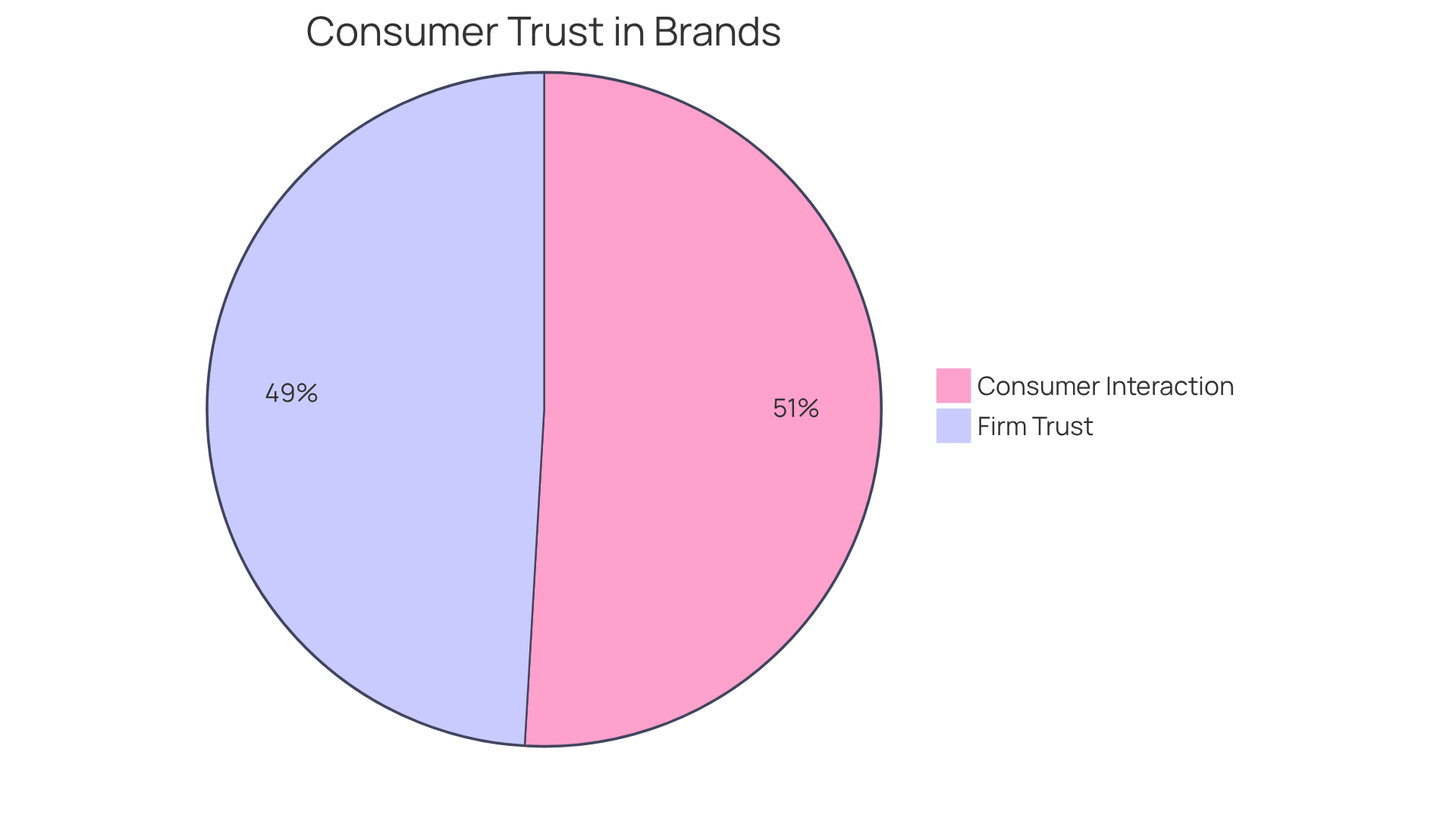
Create a Clear and Effective Privacy Policy
Creating a transparent and efficient data privacy compliance program is essential for any organization that handles personal information. This policy should comprehensively detail the types of information collected, the rationale behind the collection, and the methods employed for usage and protection.
-
Why is this important? Key elements include explicit information on user rights and the procedures for individuals to exercise those rights. A carefully crafted data privacy compliance program not only fulfills legal obligations but also fosters customer trust by demonstrating a sincere dedication to information protection.
-
In fact, 83% of consumers are more likely to interact with brands that openly communicate their data handling practices. Moreover, companies that emphasize information protection can boost customer loyalty, with 80% of firms indicating heightened trust as a result of their security investments.
-
What happens if you don’t comply? Entities must recognize the possible legal consequences of failing to adhere to confidentiality policies, which can lead to substantial penalties under regulations like GDPR and CPRA, making a data privacy compliance program essential. By clearly articulating how personal information is managed and including contact details for user complaints and support, organizations can significantly enhance user confidence and willingness to share details.
Ultimately, this fosters a more secure and trustworthy digital environment.
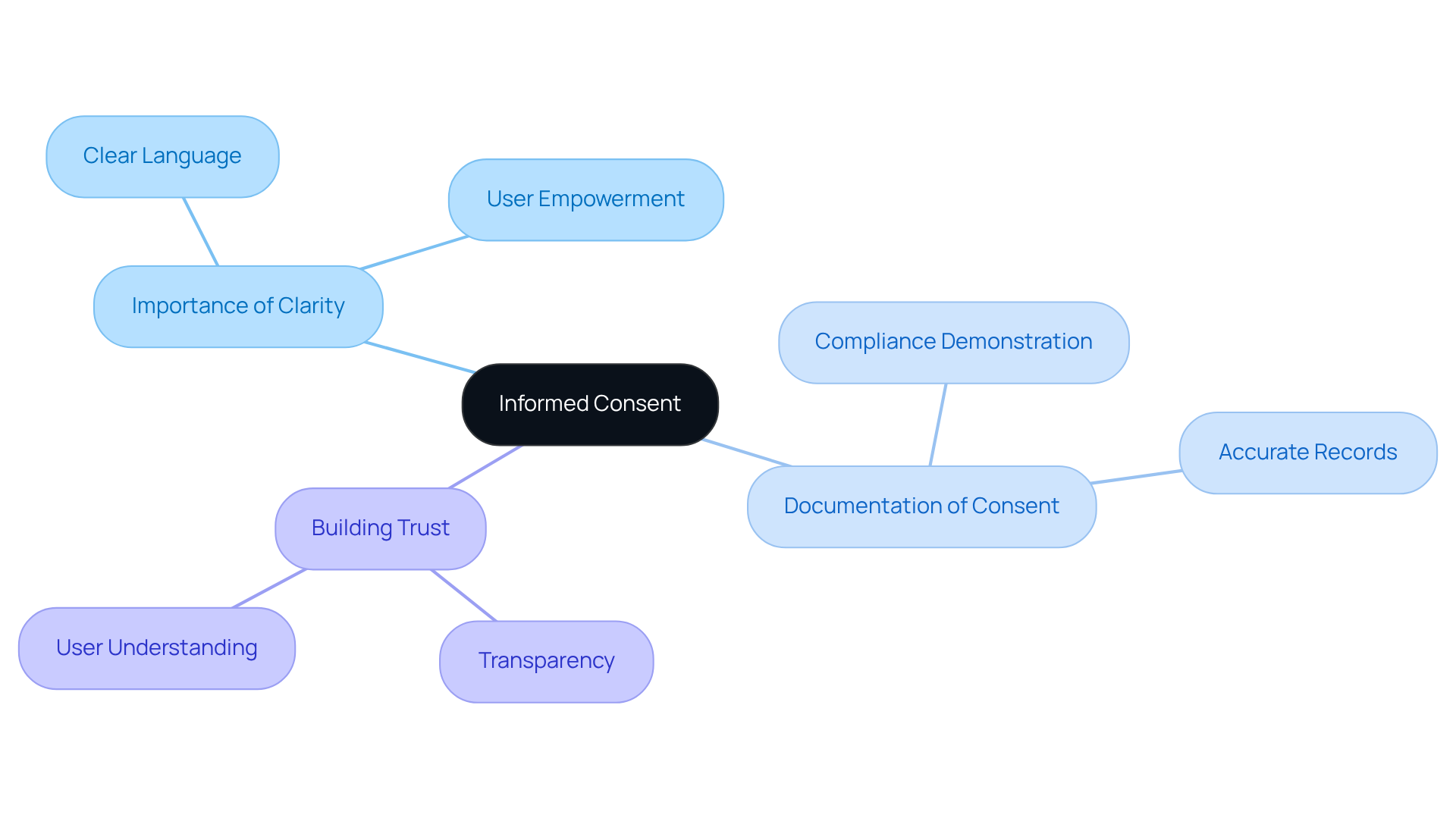
Obtain Informed Consent from Users
Obtaining informed consent from users is not just a best practice; it’s a critical aspect of adhering to information privacy standards. Are organizations truly ensuring that users understand what information is being collected, how it will be used, and their rights regarding that information? It’s essential that consent is obtained using clear and concise language, empowering users to make informed decisions.
Moreover, maintaining thorough documentation of consent is vital. This not only demonstrates compliance with the data privacy compliance program but also builds trust with users. By keeping accurate records, organizations can showcase their commitment to safeguarding personal information.
In conclusion, informed consent is a cornerstone of information privacy. Organizations must prioritize transparency and user understanding to foster a culture of compliance and trust as part of their data privacy compliance program. Are you ready to take the necessary steps to ensure your organization meets these critical standards?
Implement Robust Data Security Measures
Implementing robust information security measures is not just advisable; it’s essential for safeguarding personal details, especially in the defense contracting sector. Organizations must adopt a multi-layered security approach that includes:
- Encryption
- Access controls
- Regular security assessments
For example, utilizing technologies like firewalls and intrusion detection systems can significantly reduce the risks posed by cyber threats.
But it doesn’t stop there. Training employees on security best practices is crucial, considering that human error accounts for approximately 88% of all cyber incidents. Did you know that 69% of organizations have already implemented multi-factor authentication as a key security measure? This statistic underscores the growing recognition of the need for enhanced security protocols.
By prioritizing these strategies, defense contractors can not only bolster their information security initiatives but also strengthen their data privacy compliance program to meet stringent regulations. It’s time to take action and invest in these critical measures to protect sensitive information effectively.
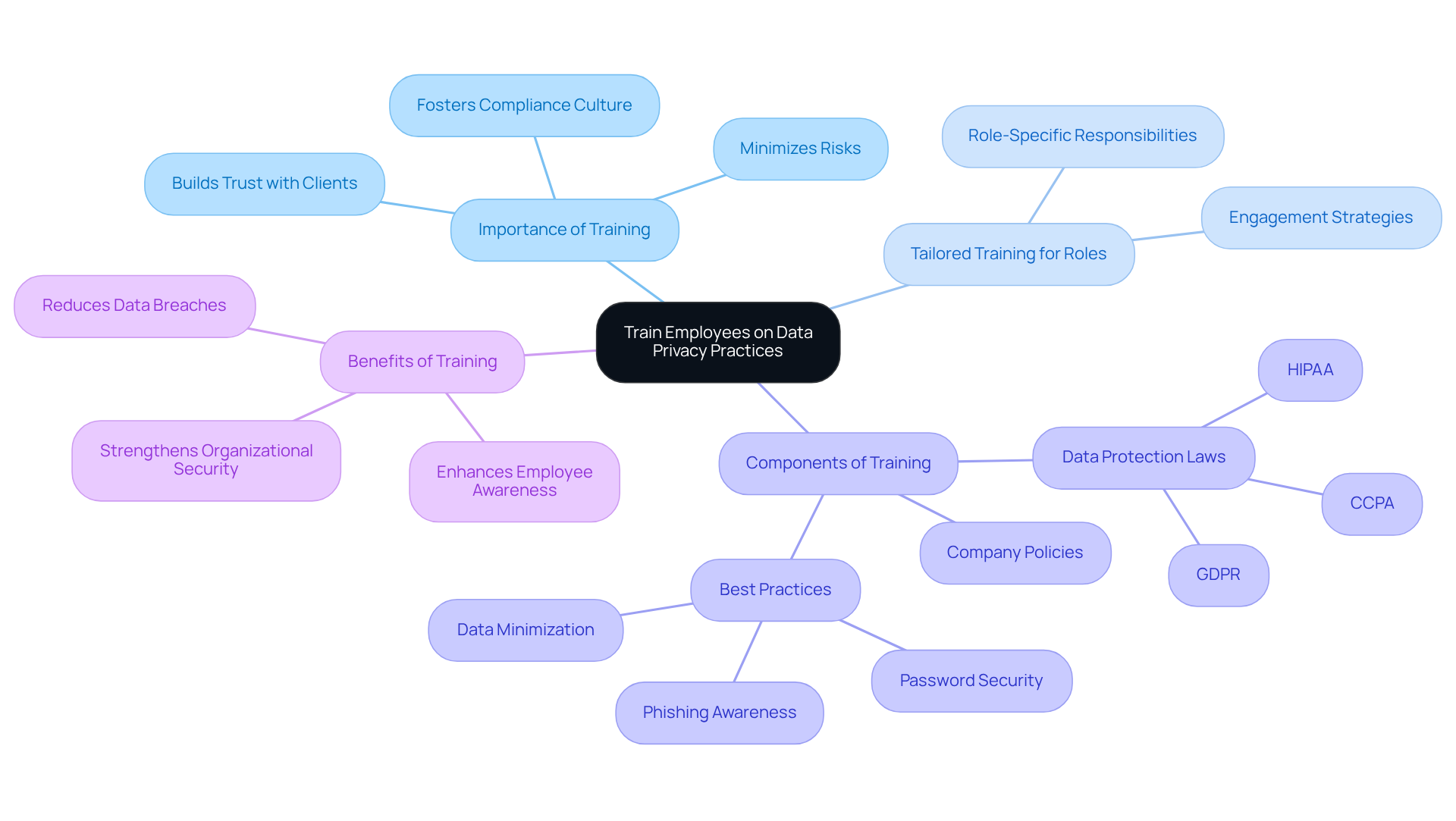
Train Employees on Data Privacy Practices
Educating staff on privacy practices is not just important; it’s essential for an effective compliance program. Organizations must implement regular training sessions that delve into data protection laws, company policies, and best practices for handling personal data. But here’s the catch: this training needs to be tailored to different roles within the organization. Why? Because ensuring that every employee understands their specific responsibilities is crucial. A knowledgeable workforce minimizes risks and fosters a culture of adherence.
Consider this: when employees are well-informed, they are more likely to comply with regulations and protect sensitive information. This proactive approach not only safeguards the organization but also builds trust with clients and stakeholders.
In conclusion, investing in comprehensive training is a strategic move that pays off. Organizations should prioritize these sessions, ensuring they are engaging and relevant to all staff members. By doing so, they not only comply with regulations but also create a robust framework for data protection.
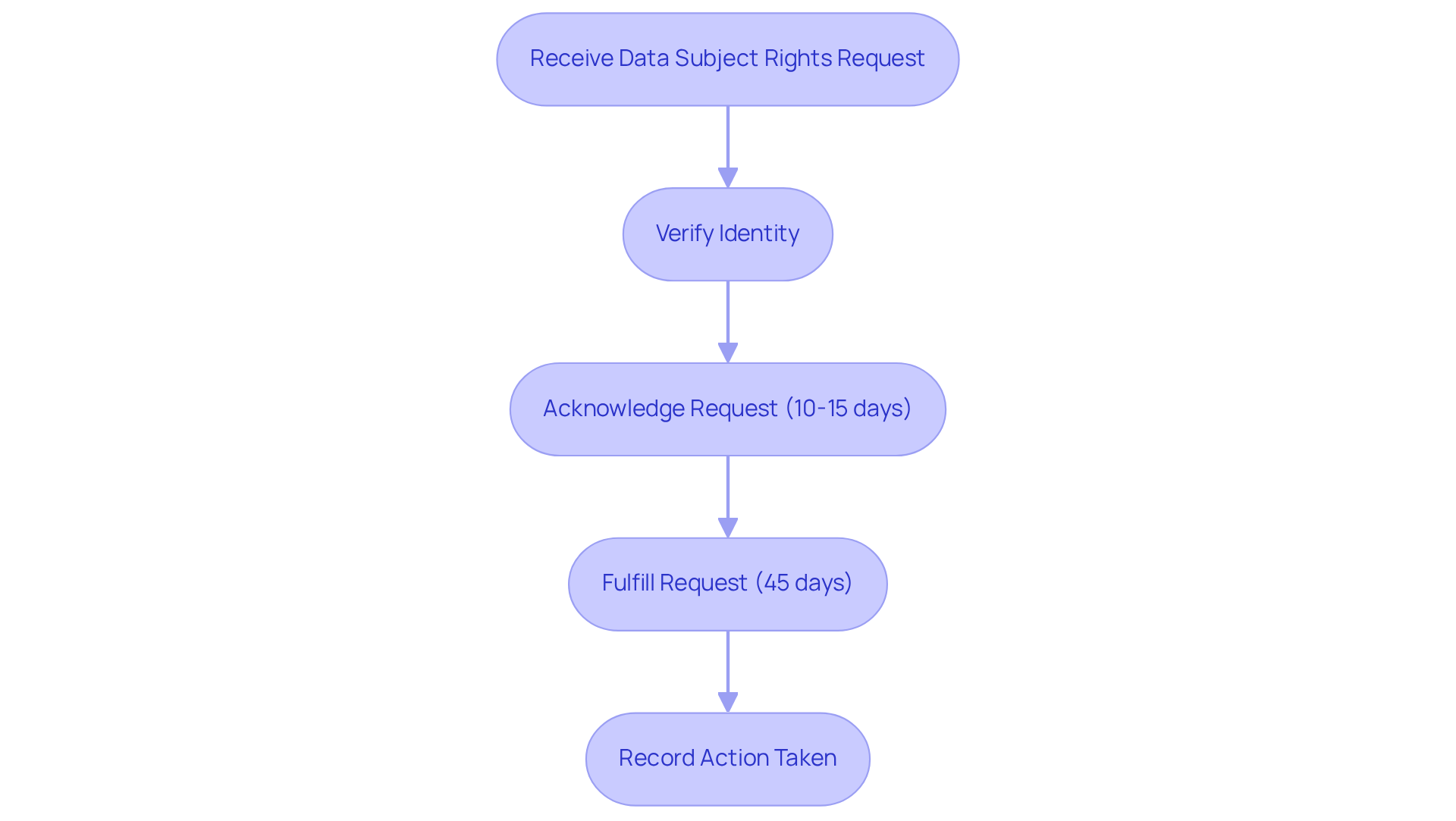
Establish Processes for Data Subject Rights Requests
Creating efficient procedures for handling subject rights requests is essential for the data privacy compliance program and adhering to protection regulations. Organizations must establish clear protocols that empower individuals to request access to their information, seek corrections, or ask for removal. These processes should incorporate identity verification to ensure that requests are legitimate and must comply with legally mandated response timelines.
For instance, under the California Consumer Privacy Act (CCPA), businesses are required to:
- Acknowledge requests within 10-15 days
- Provide a full response within 45 days
Additionally, businesses must retain records of consumer requests for at least 24 months. Efficiently handling these requests not only ensures compliance with the data privacy compliance program but also significantly enhances customer trust. As consumer awareness of data rights increases, entities that emphasize transparency and responsiveness in their data handling practices are likely to cultivate stronger relationships with their customers.
Implementing best practices, such as using automated systems to track requests and deadlines, can streamline the process and reduce the risk of errors. In fact, automation can reduce DSAR fulfillment times by as much as 75%, making it a valuable tool for organizations. Moreover, it is vital to record each action taken in response to a DSAR, as this thoroughness is critical for adherence and audit purposes.
Non-compliance can result in penalties of up to $7,500 per violation, highlighting the financial consequences of efficient information management. By prioritizing these practices, organizations not only support their data privacy compliance program but also foster trust and loyalty among their customers.
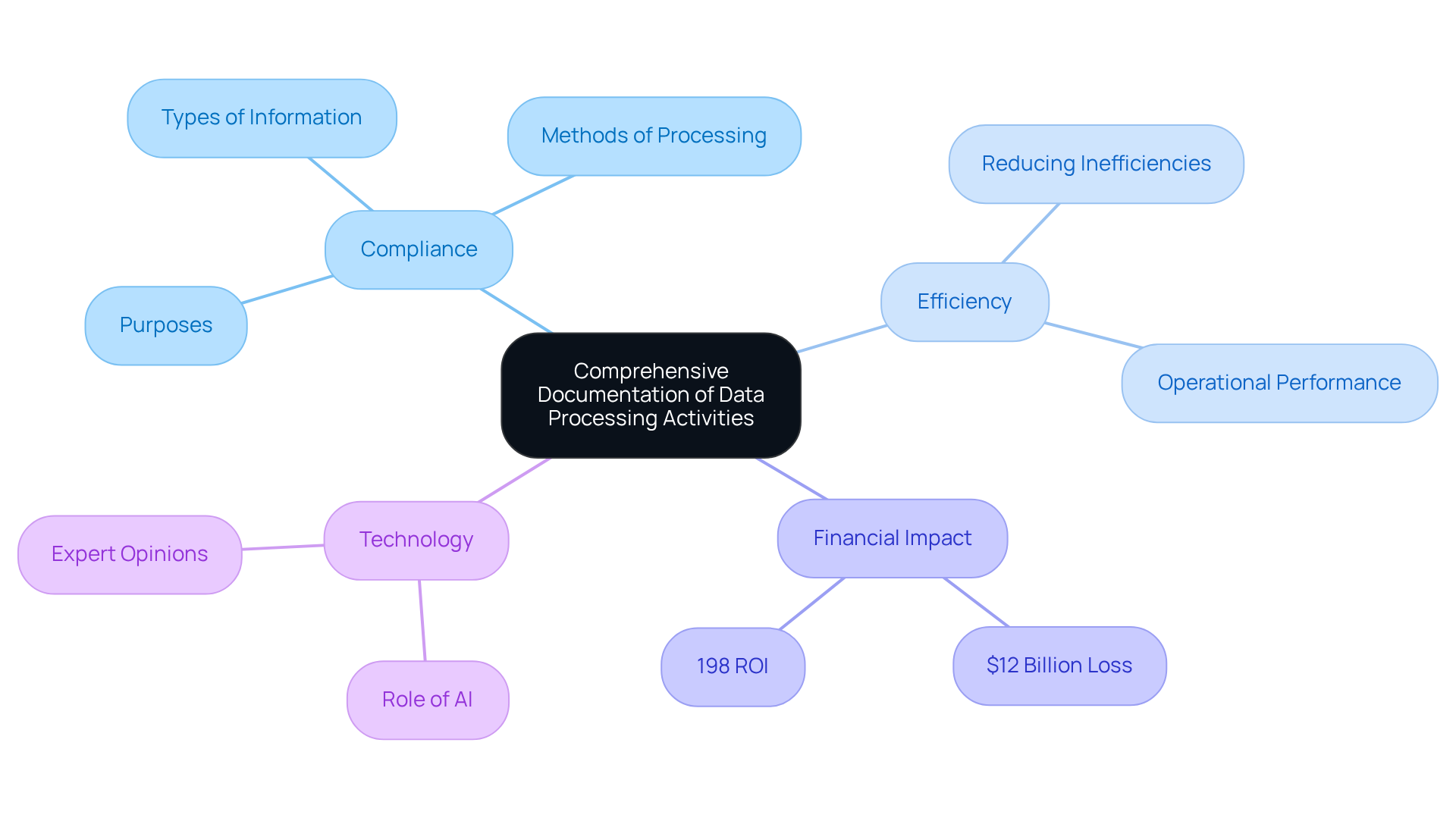
Maintain Comprehensive Documentation of Data Processing Activities
Maintaining thorough documentation of information processing activities is essential for a data privacy compliance program in order to comply with privacy regulations. Organizations must meticulously document the types of information collected, the methods of processing, and the purposes behind these actions. Have you considered how frequent assessments and revisions of this documentation can reflect changes in your information handling practices? Precise records serve as proof of adherence during audits and enhance overall information management and risk evaluation capabilities.
In fact, entities that prioritize documentation can significantly reduce inefficiencies. Did you know that Fortune 500 companies lose an estimated $12 billion annually due to poor documentation practices? Furthermore, a staggering 91% of respondents reported that data quality issues negatively impact their operations and performance. This highlights the critical role of documentation in maintaining data integrity.
Effective documentation strategies can lead to a remarkable 198% return on investment for organizations implementing document management systems. This underscores the financial benefits of maintaining thorough records. Additionally, 65% of risk and regulatory experts assert that AI is vital to their oversight programs, suggesting that leveraging technology can further enhance documentation practices.
By adopting a structured approach to documentation, businesses can effectively support their data privacy compliance program, navigate regulatory audits with confidence, and significantly enhance their operational efficiency. Are you ready to take action and improve your documentation practices?
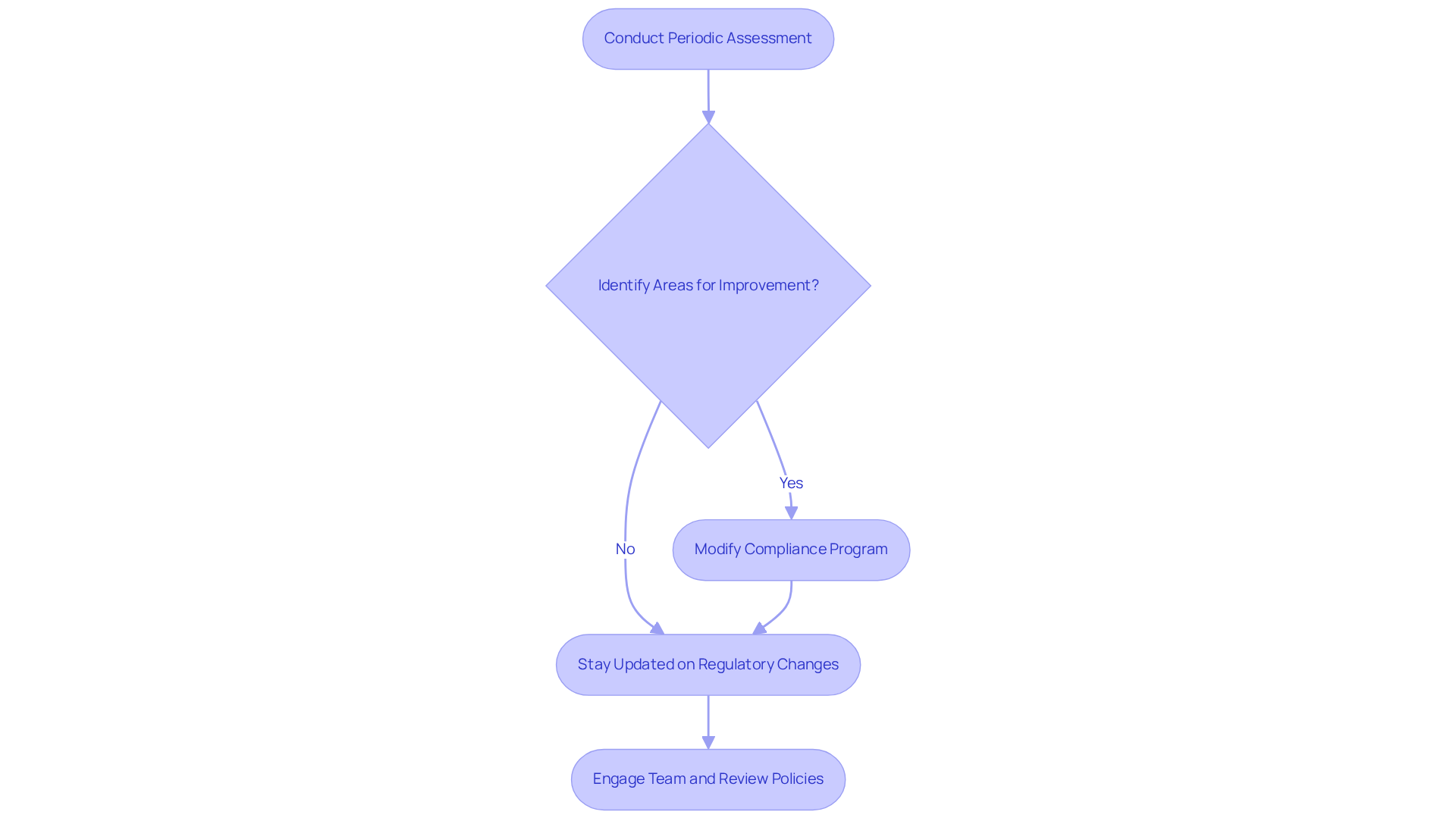
Review and Update Your Compliance Program Regularly
Consistently examining and refreshing your regulatory program is not just important; it’s essential for sustaining its effectiveness. Have you conducted a periodic assessment of your program's performance lately? This practice allows organizations to identify areas for improvement and adapt to the ever-evolving landscape of information protection regulations. By staying updated on these changes and modifying your data privacy compliance program as needed, you can ensure compliance and enhance the program's resilience.
A proactive approach to a data privacy compliance program empowers organizations to tackle new challenges head-on. It’s about more than just meeting requirements; it’s about safeguarding personal data effectively. Consider this: how prepared is your organization to respond to regulatory shifts? By prioritizing regular evaluations, your organization can thrive in a complex regulatory environment while ensuring adherence to a data privacy compliance program.
In conclusion, make it a priority to assess your regulatory program regularly. This commitment not only protects your organization but also builds trust with stakeholders. Take action today-review your policies, engage your team, and ensure your compliance efforts are robust and responsive.
Conclusion
Building a data privacy compliance program is not just a regulatory obligation; it’s a strategic imperative that safeguards sensitive information and fosters customer trust. Organizations must recognize that a robust compliance framework protects against legal ramifications and enhances their reputation in the marketplace. By prioritizing data privacy, businesses can transform compliance from a burden into a competitive advantage.
To establish an effective data privacy compliance program, consider these nine essential steps:
- Conduct comprehensive data audits.
- Create transparent privacy policies.
- Obtain informed consent.
- Implement robust security measures.
- Train employees on compliance protocols.
- Establish clear procedures for handling data subject rights requests.
- Regularly review and update practices to adapt to evolving regulations.
These steps are crucial for fostering a culture of compliance. Regularly reviewing and updating these practices ensures that organizations remain agile in the face of changing regulations.
Ultimately, the significance of a well-structured data privacy compliance program cannot be overstated. Organizations are encouraged to take proactive steps to protect their data and build lasting trust with their customers. By committing to these best practices, businesses not only comply with regulations but also position themselves as leaders in data protection, paving the way for sustainable growth and success in an increasingly data-driven world.
Frequently Asked Questions
What is the purpose of the CMMC Info Hub?
The CMMC Info Hub serves as a vital resource for organizations to establish a robust information protection adherence program, providing structured guidance, detailed roadmaps, and practical strategies to develop a data privacy compliance program that meets stringent regulatory requirements.
Why is data privacy compliance important for organizations?
Data privacy compliance is essential for safeguarding sensitive information, building customer trust, and avoiding hefty penalties and legal troubles. Non-compliance can lead to significant financial losses, damage to reputation, and loss of customer loyalty.
What are the potential consequences of failing to comply with data privacy regulations?
Organizations that overlook compliance risk facing hefty penalties, legal issues, and damage to their reputation. For example, California's Attorney General fined Sephora $1.2 million for non-compliance. Penalties can reach $2,500 per infraction or up to $7,500 for willful breaches.
How can organizations improve their data privacy compliance program?
Organizations can improve their compliance program by regularly reviewing privacy policies, investing in employee training on data hygiene, and prioritizing information security to protect assets and enhance credibility.
What is involved in conducting a comprehensive data audit?
A comprehensive data audit involves mapping all information flows within the organization, identifying types of personal information collected, methods of processing, and storage locations to assess compliance with privacy regulations like GDPR and CMMC.
Why are routine audits critical for data privacy compliance?
Routine audits are vital for maintaining information integrity and security, ensuring compliance, and mitigating risks associated with data breaches. A significant percentage of regulatory teams conduct multiple audits each year to stay compliant.
What key practices should organizations adopt for policy maintenance?
Organizations should review policies at least annually, establish a formal process for proposing and approving changes, maintain version control, archive previous policy versions, and clearly communicate updates to relevant personnel.
How can organizations manage risks associated with third-party vendors?
Organizations should evaluate and manage risks linked to third-party vendors by implementing information mapping strategies to clarify information flows, which helps strengthen their data privacy compliance program and enhance risk management.




