Craft Your Cyber Risk Management Strategy in 4 Simple Steps
Craft a robust cyber risk management strategy in 4 simple steps for defense contractors.

Overview
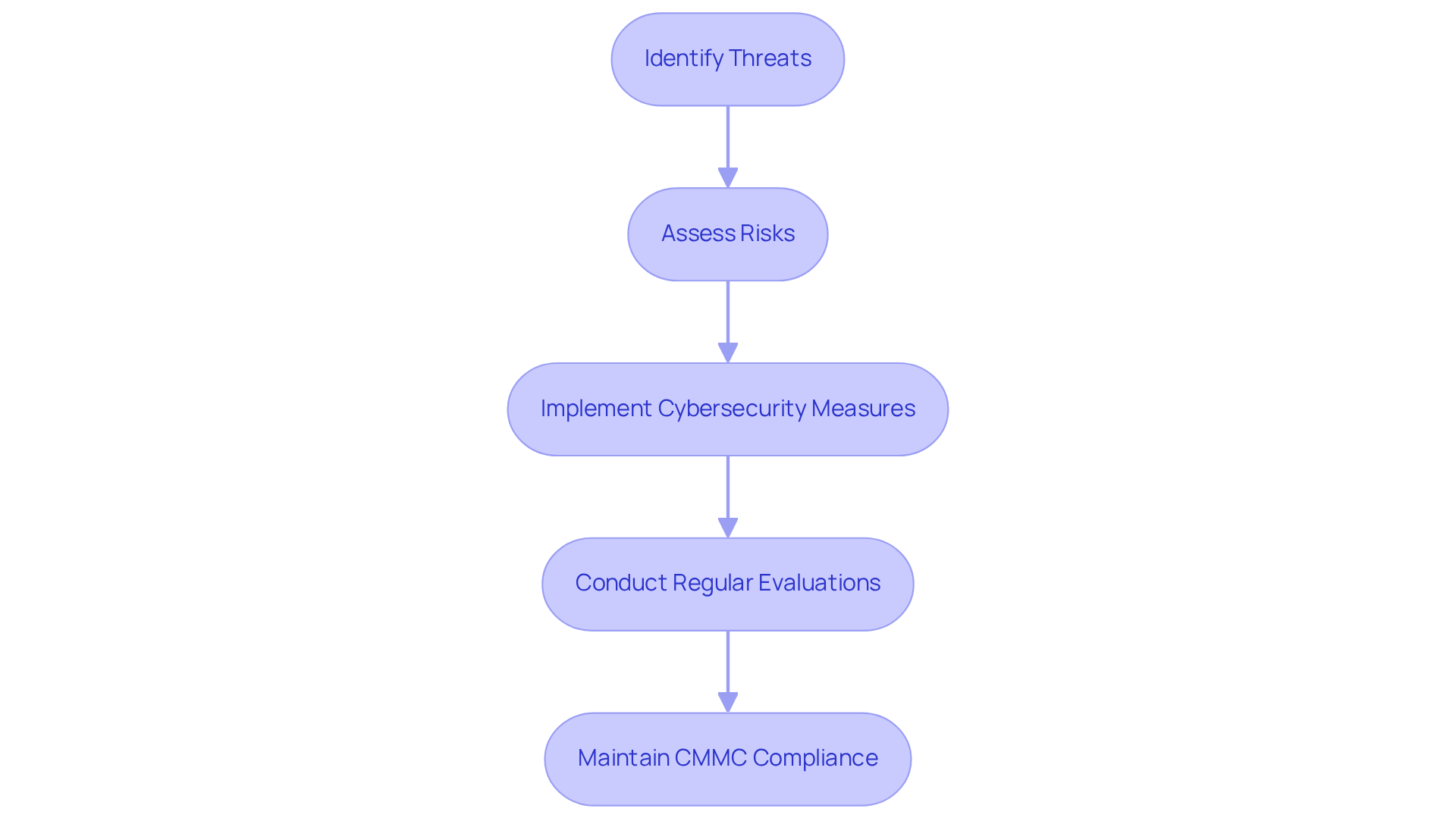
The article presents a four-step process for developing an effective cyber risk management strategy tailored for defense contractors, underscoring the critical need for compliance with the Cybersecurity Maturity Model Certification (CMMC).
- It emphasizes the importance of conducting comprehensive risk assessments. This foundational step allows organizations to identify vulnerabilities and understand the specific threats they face.
- Next, prioritizing these threats ensures that resources are allocated effectively, addressing the most pressing risks first.
- Additionally, establishing continuous monitoring is crucial. This ongoing vigilance not only helps in detecting potential breaches but also ensures that the organization remains compliant with evolving regulatory requirements.
- By implementing these measures, defense contractors can significantly mitigate cyber threats and protect sensitive military information.
In conclusion, adopting this structured approach not only aligns with CMMC standards but also fortifies the organization against cyber risks. Are you ready to take the necessary steps to safeguard your operations?
Introduction
In a time when cyber threats are escalating rapidly, defense contractors must urgently strengthen their cybersecurity strategies. The Cybersecurity Maturity Model Certification (CMMC) has introduced a rigorous framework that not only mandates compliance but also acts as a crucial tool for safeguarding sensitive military information. This article presents a four-step guide aimed at empowering organizations to develop a robust cyber risk management strategy, ensuring they meet regulatory requirements while enhancing their operational resilience.
How can defense contractors effectively navigate the complexities of cyber risk management and protect their critical assets against an ever-evolving threat landscape? By understanding the importance of CMMC compliance and implementing a strategic approach, organizations can not only defend against potential breaches but also foster a culture of security that permeates their operations.
As we delve deeper into this guide, we will explore actionable insights that will help you fortify your defenses and stay ahead in this challenging environment.
Define Cyber Risk Management in the Context of Defense Contracting
Cybersecurity management for contractors in the military sector is essential for identifying, assessing, and mitigating threats that could jeopardize sensitive military information. This structured approach is particularly vital given the Cybersecurity Maturity Model Certification (CMMC) requirements, which mandate the protection of Controlled Unclassified Information (CUI). By understanding these regulatory demands, organizations can align their cybersecurity strategies with the Department of Defense's expectations, enhancing their readiness to secure military contracts and protect critical data.
The impact of CMMC compliance on cybersecurity management is significant. As the DoD rolls out these standards, defense contractors must implement robust cybersecurity measures to prove their ability to safeguard sensitive information. This includes conducting regular evaluations and applying necessary measures to effectively mitigate threats. Notably, the final regulation modifying the Defense Federal Acquisition Regulation Supplement, effective November 10, 2025, underscores the need for contractors to maintain their CMMC status throughout the contract lifecycle, emphasizing the importance of ongoing compliance.
Moreover, the urgency of effective cyber threat management is underscored by alarming statistics:
- The defense sector experiences approximately 1,250 cyber incidents each week.
- Over half of defense contractors struggle to meet CMMC compliance requirements.
These challenges highlight the critical need for organizations to establish efficient protocols to defend against data breaches and other cyber threats.
In this context, insights from industry experts reinforce the necessity of managing cyber threats. Noël Vestal, a Certified CMMC Assessor, emphasizes the importance of developing comprehensive regulatory programs to protect sensitive information. As the landscape of cyber threats evolves, defense contractors must prioritize their cyber risk management strategy—not only to meet regulatory requirements but also to protect their operations and maintain a competitive edge in the defense sector.
Conduct a Comprehensive Cyber Risk Assessment
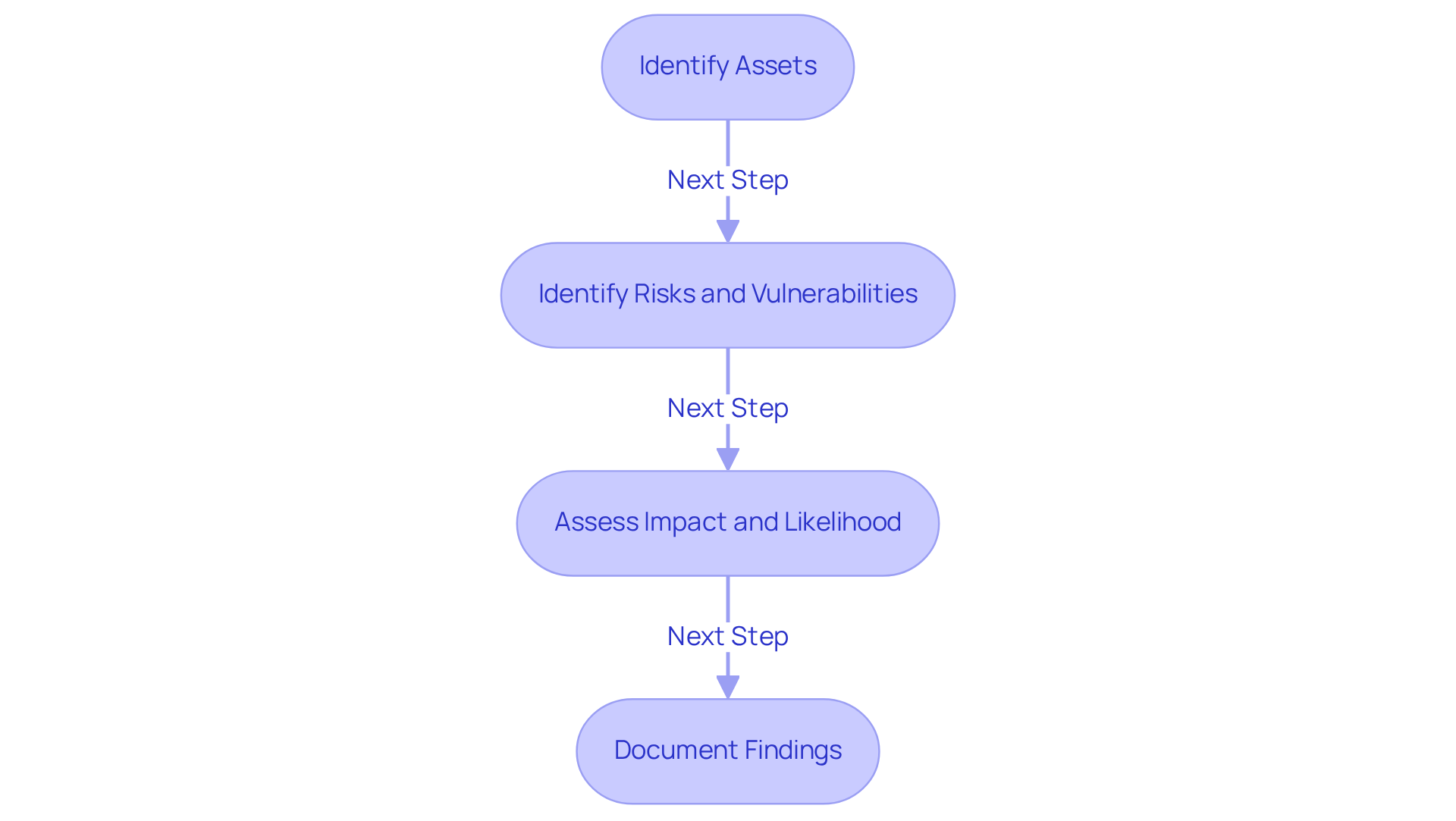
To conduct a comprehensive cyber risk assessment and align with CMMC compliance, follow these essential steps:
-
Identify Assets: Start by cataloging all critical assets, including hardware, software, and sensitive data that require protection. This crucial step ensures that every vital element of your organization is considered in the assessment process, which is essential for achieving CMMC compliance.
-
Identify Risks and Vulnerabilities: Perform a thorough analysis of potential risks, such as malware attacks and insider threats, alongside vulnerabilities like outdated software and weak password policies. Understanding these factors is key to pinpointing areas of risk that could be exploited. Notably, ransomware incidents in the healthcare sector have nearly doubled since 2022, highlighting the urgency of recognizing these risks as part of your compliance strategy.
-
Assess Impact and Likelihood: Evaluate the potential impact of each identified risk and the likelihood of its occurrence. Utilize a matrix to classify these threats into low, medium, or high levels, which aids in prioritizing mitigation efforts effectively. As Rajiv Gupta from the Canadian Centre for Cyber Security emphasizes, 'ransomware is the primary cybercrime threat confronting Canada’s critical infrastructure,' underscoring the importance of this assessment stage in the context of CMMC adherence.
-
Document Findings: Compile a detailed report summarizing the assessment findings. This report should include identified hazards, their potential impact on the organization’s operations, and implications for regulatory status. Proper documentation not only supports internal decision-making but also demonstrates due diligence in cybersecurity practices. For instance, the average ransomware payout surged from $812,380 in 2022 to $1,542,333 in 2023, illustrating the financial consequences of inadequate risk assessments.
By following these steps, defense contractors can enhance their cybersecurity posture and ensure compliance with CMMC requirements, ultimately securing their position in the defense contracting landscape. This comprehensive approach transforms confusion into clarity, providing practical strategies and peer insights to achieve CMMC compliance with confidence.
Prioritize and Mitigate Identified Cyber Risks
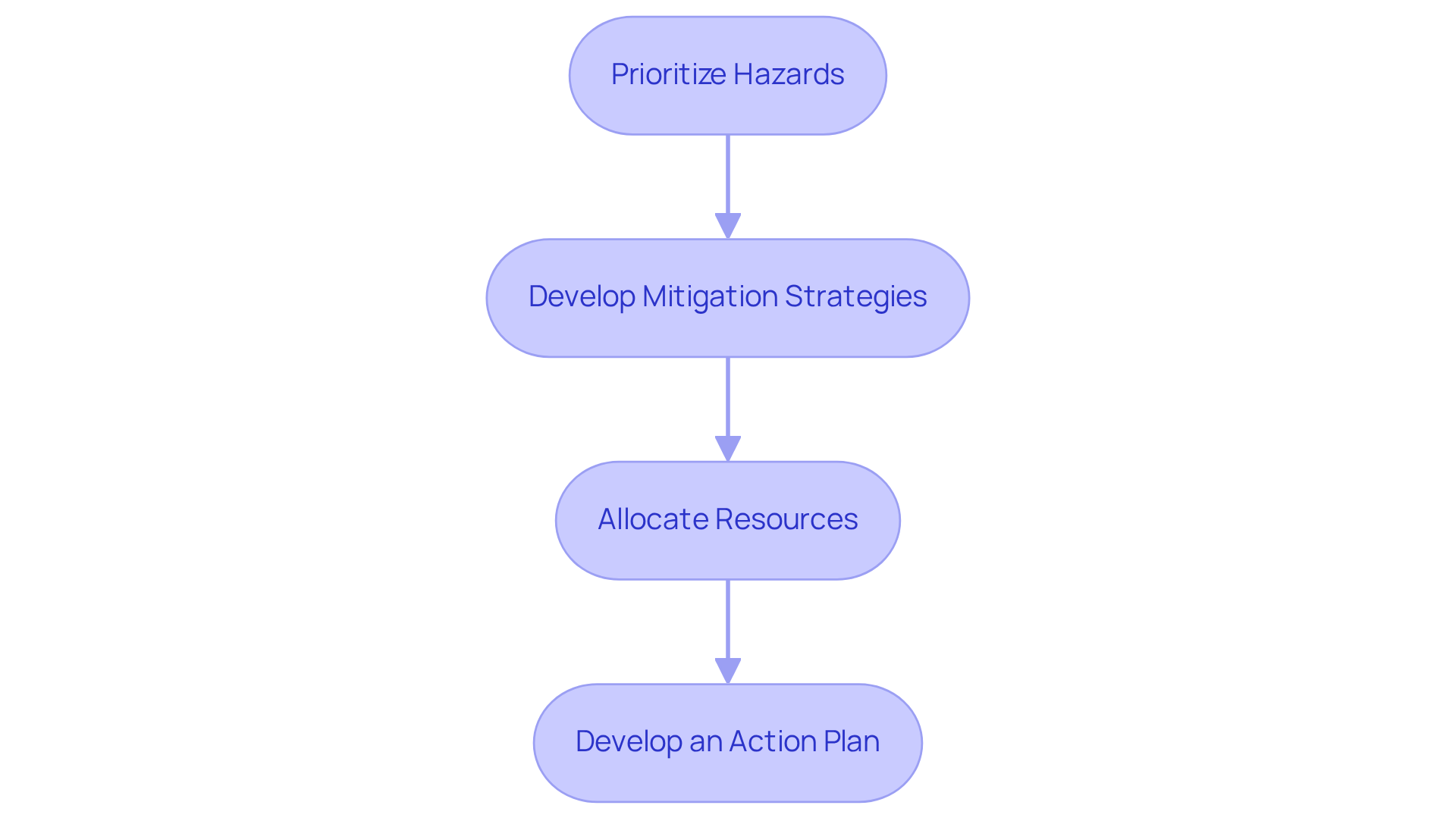
Once threats have been identified and evaluated, organizations must prioritize them based on their potential impact and likelihood. Here’s how to proceed:
- Prioritize Hazards: Start by utilizing the hazard matrix from the evaluation to rank issues from highest to lowest importance. This ensures that the most critical concerns are addressed first.
- Develop Mitigation Strategies: For each high-priority threat, create specific strategies to tackle them. This could involve implementing new security controls, updating software, or providing employee training. Common practices in the security industry include applying advanced protective measures, consistently refreshing software, and conducting extensive staff training to enhance understanding of cyber risks.
- Allocate Resources: Assess the resources—time, budget, personnel—needed to effectively implement the mitigation strategies. Notably, 58% of small and medium-sized businesses exceeded their planned cybersecurity budgets in 2024, highlighting the necessity for adequate funding to ensure effective implementation.
- Develop an Action Plan: Document the prioritized threats and corresponding mitigation strategies in an action plan, assigning responsibilities and timelines for execution. This plan should ensure accountability and facilitate progress tracking.
By following these steps, contractors can establish a robust cyber risk management strategy that effectively addresses high-priority challenges and enhances their overall cybersecurity posture, preparing them for the evolving threat landscape. As illustrated in the "Cybersecurity in the Defense Sector" case study, the aerospace and defense sector has experienced a staggering 300% increase in cyberattacks since 2018, underscoring the urgency of implementing these strategies. Furthermore, as IBM reported, phishing attacks can cost organizations an average of $4.9 million each, further emphasizing the financial implications of cyber risks.
Establish Continuous Monitoring and Improvement Processes
To establish effective continuous monitoring and improvement processes, organizations must focus on key strategies that not only enhance security but also ensure compliance with CMMC requirements.
-
Implement Monitoring Tools: Leverage advanced cybersecurity tools that provide real-time monitoring of networks and systems. These tools are essential for identifying anomalies and potential threats, allowing organizations to respond swiftly to incidents. Have you considered how quickly your current systems can detect a breach?
-
Regularly Review Policies and Procedures: Schedule periodic reviews of cybersecurity policies and procedures to maintain their effectiveness. Frequent evaluations help identify deficiencies and adapt to evolving threats. Are your policies keeping pace with the latest cybersecurity challenges?
-
Conduct Regular Training: Offer continuous education for employees to keep them informed about the latest cybersecurity risks and best practices. Statistics show that organizations with robust training programs experience a significant reduction in security incidents. Informed employees are less likely to fall victim to phishing and other attacks. How often do you update your training materials?
-
Feedback Loop: Establish a feedback mechanism to learn from incidents and near misses. Analyzing these occurrences enables organizations to refine their management strategies and strengthen their overall cybersecurity posture, fostering a culture of ongoing improvement. What lessons have you learned from past incidents?
By implementing these strategies, organizations can significantly bolster their defenses against cyber threats and adopt a proactive approach to risk management. Don't wait for a breach to take action—start enhancing your cybersecurity measures today.

Conclusion
Crafting a robust cyber risk management strategy is essential for defense contractors navigating the complexities of cybersecurity regulations and threats. By systematically identifying, assessing, and mitigating risks, organizations can comply with the stringent requirements of the Cybersecurity Maturity Model Certification (CMMC) while safeguarding sensitive military information crucial for national security.
This article outlines four critical steps in developing an effective cyber risk management approach:
- Conducting a comprehensive risk assessment
- Prioritizing and mitigating identified risks
- Establishing continuous monitoring and improvement processes
Each step is designed to enhance cybersecurity posture and ensure ongoing compliance with evolving regulations. By leveraging insights from industry experts and implementing best practices, defense contractors can effectively tackle the challenges posed by cyber threats.
The significance of a proactive cyber risk management strategy cannot be overstated. As the defense sector faces an increasing number of cyber incidents, organizations must prioritize their cybersecurity efforts to protect not only their operations but also their competitive edge in the industry. Embracing these practices will lead to compliance with CMMC requirements and foster a culture of resilience against the ever-evolving landscape of cyber threats.
Taking action today is crucial to securing a safer tomorrow in defense contracting. Are you ready to enhance your cybersecurity posture and ensure compliance? The time to act is now.
Frequently Asked Questions
What is cyber risk management in the context of defense contracting?
Cyber risk management in defense contracting involves identifying, assessing, and mitigating threats that could endanger sensitive military information, particularly in relation to the Cybersecurity Maturity Model Certification (CMMC) requirements.
Why is CMMC compliance important for defense contractors?
CMMC compliance is crucial for defense contractors as it mandates the protection of Controlled Unclassified Information (CUI) and requires contractors to implement robust cybersecurity measures to demonstrate their capability to safeguard sensitive information.
What are the implications of the final regulation modifying the Defense Federal Acquisition Regulation Supplement?
The final regulation, effective November 10, 2025, emphasizes that contractors must maintain their CMMC status throughout the contract lifecycle, highlighting the importance of ongoing compliance with cybersecurity standards.
How often do cyber incidents occur in the defense sector?
The defense sector experiences approximately 1,250 cyber incidents each week.
What challenges do defense contractors face regarding CMMC compliance?
Over half of defense contractors struggle to meet CMMC compliance requirements, indicating a critical need for efficient protocols to defend against data breaches and other cyber threats.
What do industry experts suggest regarding cyber threat management?
Industry experts, such as Noël Vestal, emphasize the necessity of developing comprehensive regulatory programs to protect sensitive information and prioritize cyber risk management strategies to meet regulatory demands and maintain a competitive edge in the defense sector.




