Master Cyber Attack Risk Assessment in 7 Simple Steps
Master cyber attack risk assessment through a structured, seven-step process to enhance security.

Introduction
Understanding the landscape of cyber threats is more crucial than ever. Organizations are facing an increasing barrage of attacks, making it imperative to stay ahead. A well-executed cyber attack risk assessment acts as a vital shield, enabling businesses to identify vulnerabilities, prioritize critical assets, and develop effective mitigation strategies. Yet, many organizations grapple with the challenge of implementing a comprehensive assessment process.
What steps can be taken to master this essential skill? Ensuring robust cybersecurity in an ever-evolving threat environment is not just a necessity; it’s a strategic imperative. By addressing these challenges head-on, organizations can fortify their defenses and safeguard their assets.
Understand Cyber Attack Risk Assessment
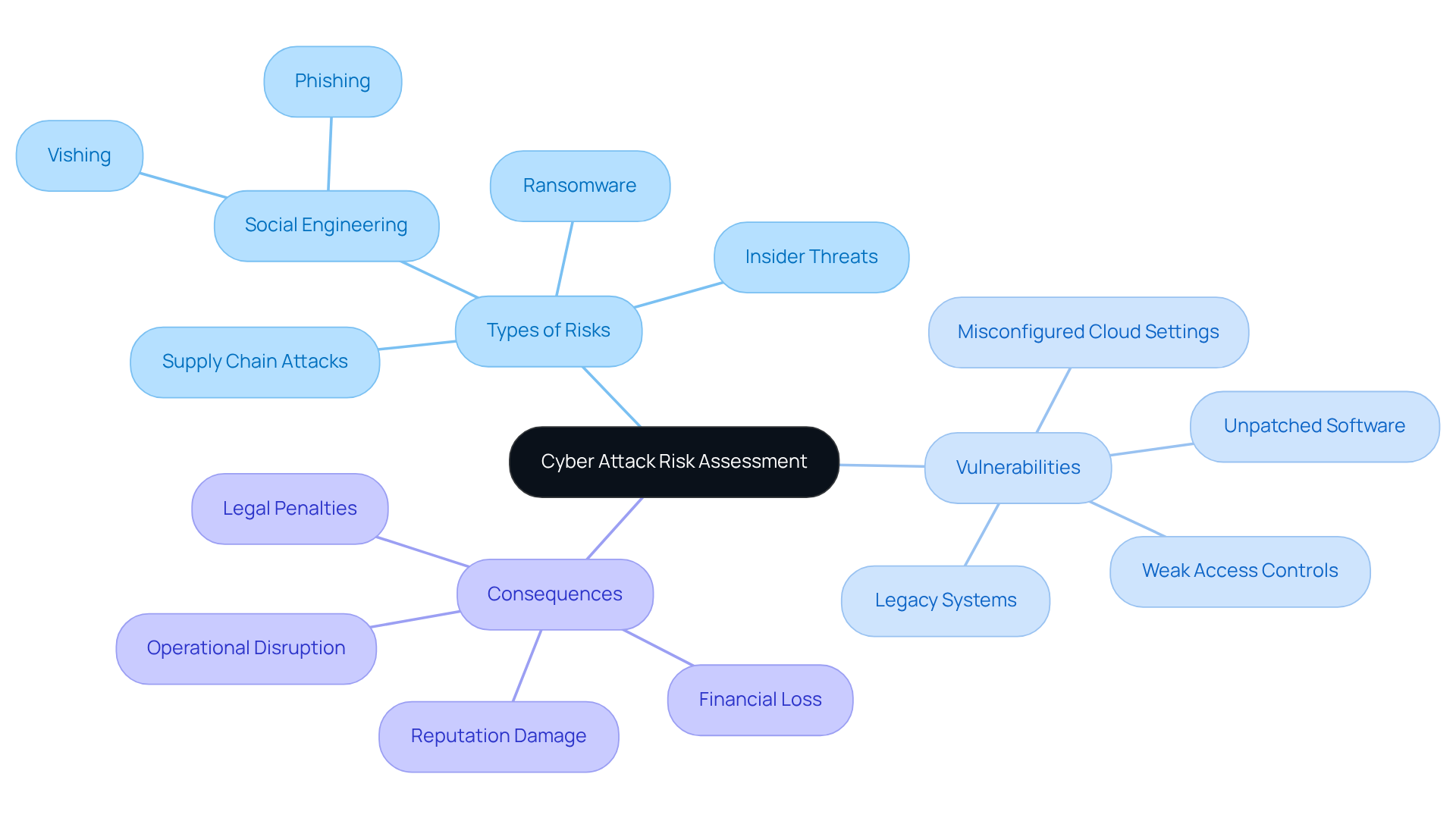
A cyber attack risk assessment is a structured procedure that assists organizations in identifying, assessing, and prioritizing risks associated with potential cyber threats. Understanding the types of risks that can impact your organization, the vulnerabilities that may be exploited, and the potential consequences of these risks is crucial. This foundational knowledge is essential for crafting a robust cybersecurity strategy.
Have you considered the key concepts of threat and vulnerability? Their interconnections are vital in the realm of cybersecurity. By grasping these ideas, you can better prepare your organization for a cyber attack risk assessment against cyber threats.
In summary, a thorough evaluation, such as a cyber attack risk assessment, not only highlights the risks but also empowers you to take informed actions. Start today by assessing your current cybersecurity posture and identifying areas for improvement.
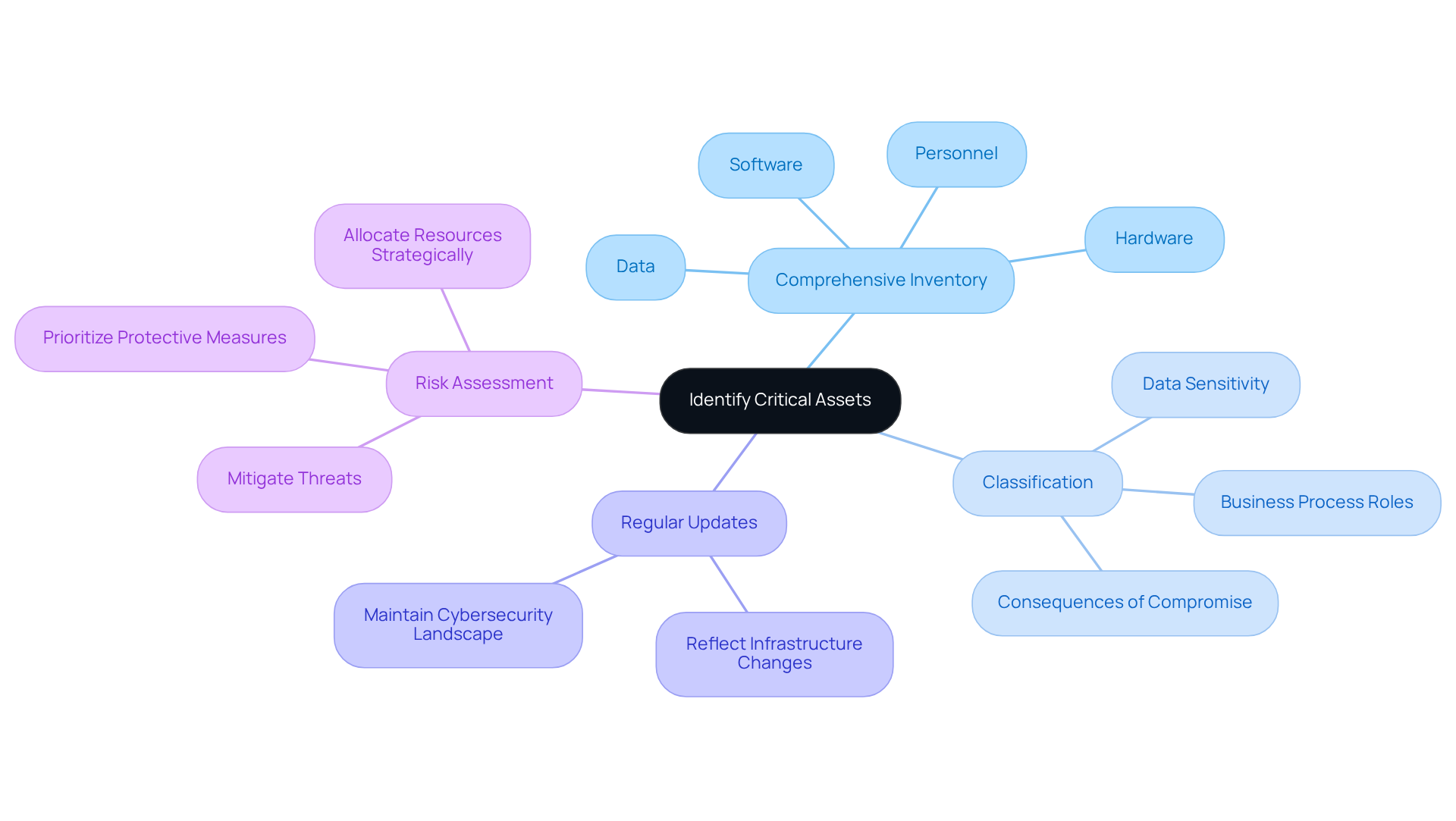
Identify Critical Assets
Start by compiling a comprehensive inventory of all organizational assets, including hardware, software, data, and personnel. Why is this important? Classifying these assets based on their criticality to operations is essential. Consider factors such as data sensitivity, their roles in business processes, and the potential consequences of their compromise. Utilizing recognized asset management software can streamline this classification process, ensuring both accuracy and efficiency. Regular updates to this inventory are crucial to reflect any changes in your entity’s infrastructure, maintaining an up-to-date understanding of your cybersecurity landscape.
The categorization of essential assets is crucial for conducting a cyber attack risk assessment. It allows organizations to prioritize protective measures effectively. By identifying which assets are most crucial, defense contractors can allocate resources more strategically, ensuring that the most sensitive and impactful components of their operations are adequately protected. Current trends indicate a growing emphasis on comprehensive asset visibility, enhancing the ability to mitigate threats and reduce security incidents. This proactive approach not only strengthens the overall security posture but also aligns with best practices in the defense sector, where the stakes are particularly high.
Furthermore, advice from the National Security Agency underscores the significance of establishing and overseeing an asset inventory to assist in the cyber attack risk assessment and weakness management. It’s also vital to consider the vulnerabilities introduced by unmanaged operational technology (OT) devices, as these can significantly impact the security of critical assets. By addressing these vulnerabilities, organizations can further bolster their defenses and ensure a robust cybersecurity framework.
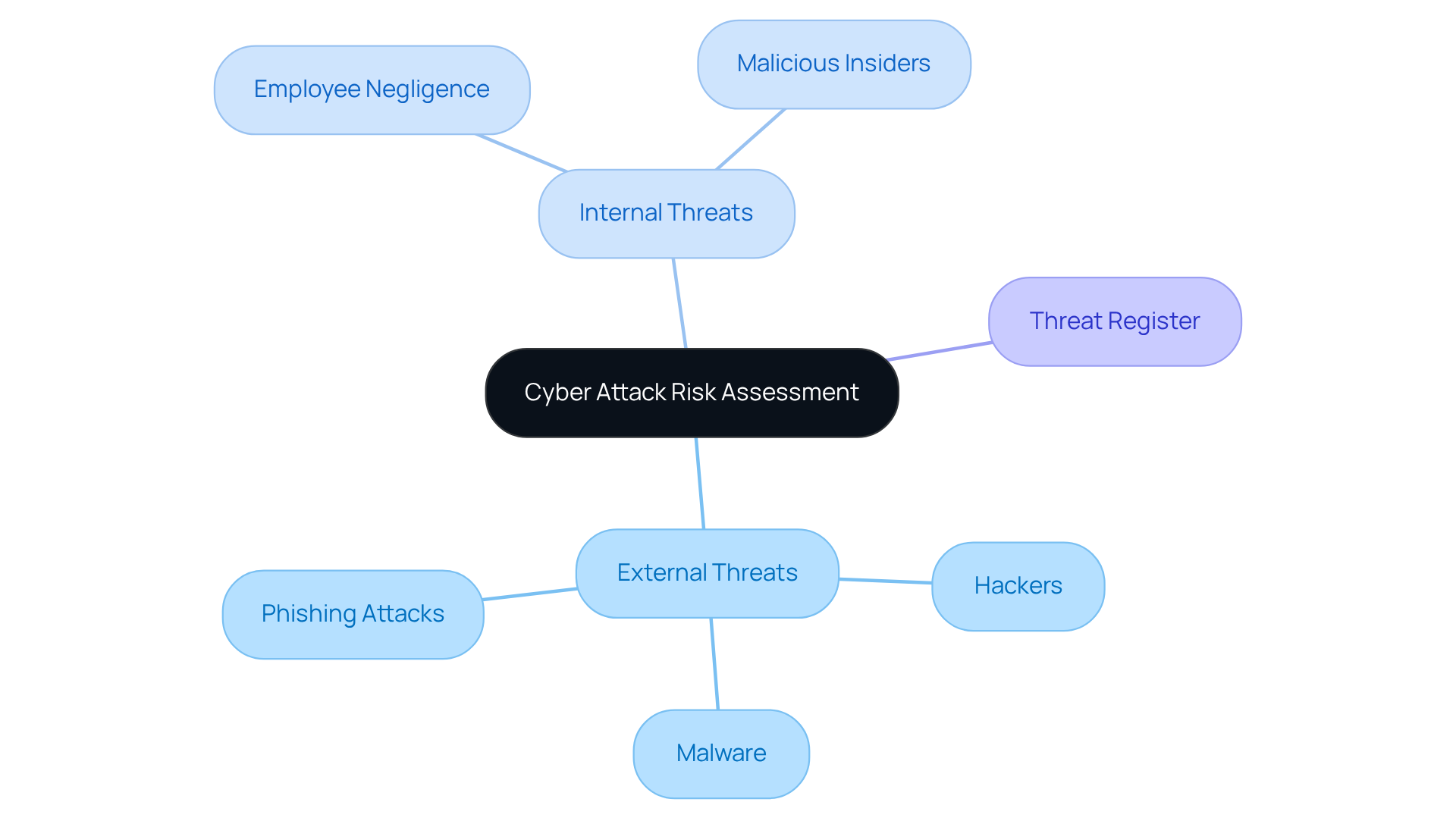
Recognize Potential Threats
Conducting a thorough cyber attack risk assessment of potential risks to your essential assets is crucial. Have you considered the external threats, such as hackers, malware, and phishing attacks, in your cyber attack risk assessment? These dangers can be identified and addressed in a cyber attack risk assessment to avoid compromising your security. Additionally, internal risks like employee negligence or malicious insiders can pose significant challenges that should be considered in a cyber attack risk assessment. To stay informed about emerging threats, leverage intelligence reports and resources from organizations like CISA. This proactive approach not only helps you identify risks but also plays a crucial role in performing a cyber attack risk assessment that empowers you to take action.
Documenting these threats in a threat register is essential for ongoing monitoring and evaluation. By maintaining this register, you can continuously assess the landscape of risks and adapt your strategies accordingly. Remember, staying vigilant is key to safeguarding your assets. Are you ready to take the necessary steps to protect your organization?
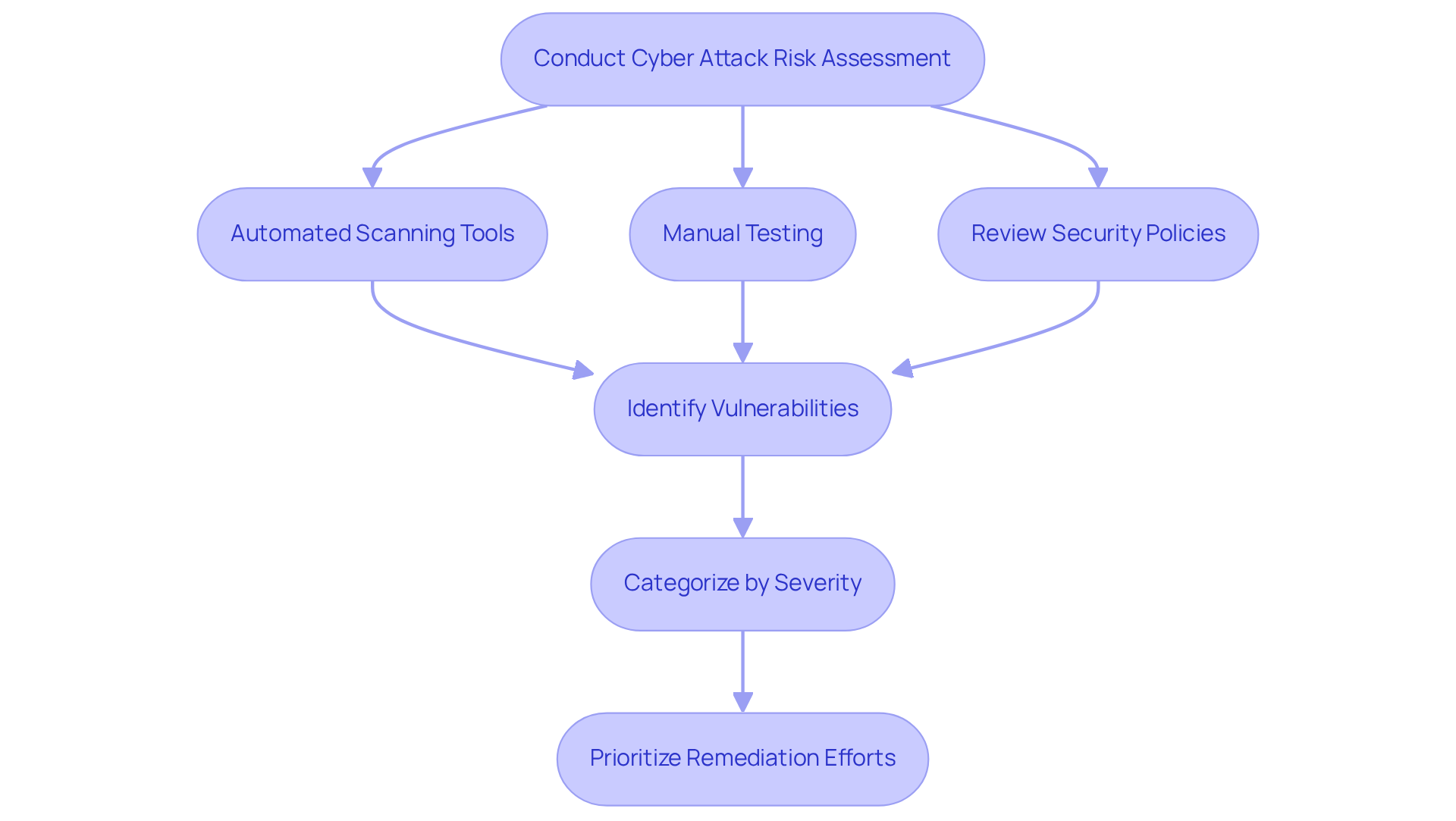
Identify Vulnerabilities
Conducting a thorough cyber attack risk assessment is essential for identifying vulnerabilities in your systems, applications, and processes, particularly when striving for CMMC compliance. This can be achieved through a blend of automated scanning tools, manual testing, and a detailed review of security policies. In 2025, common weaknesses include:
- Outdated software
- Misconfigured systems
- Insufficient employee training
All of which pose significant security risks. Alarmingly, about 38% of documented weaknesses this year are categorized as High or Critical severity, underscoring the pressing need for a cyber attack risk assessment to address these issues, especially since 71% of organizations reported an increase in cyberattack frequency over the past year.
Utilizing automated scanning tools, such as Nessus or Qualys, can streamline the identification process, allowing organizations to uncover vulnerabilities more efficiently. Continuous monitoring for weaknesses is crucial to maintain an up-to-date security posture, which is a vital component of the cyber attack risk assessment in the CMMC compliance strategy. These tools offer real-time insights into system vulnerabilities, facilitating prompt remediation.
Additionally, documenting all identified weaknesses is critical; categorize them by severity and potential impact on essential assets to prioritize remediation efforts effectively. It's important to recognize that security management is now a legal obligation, with organizations facing risks of breaches, penalties, and legal repercussions for failing to implement necessary updates. Moreover, CMMC compliance may now be required by the Department of Defense as a prerequisite for new defense industrial base contracts. By adopting these best practices and aligning with the CMMC framework, as outlined in the Ultimate Guide to Achieving CMMC Compliance, organizations can enhance their cybersecurity posture and better protect sensitive information against emerging threats.
Analyze Risks
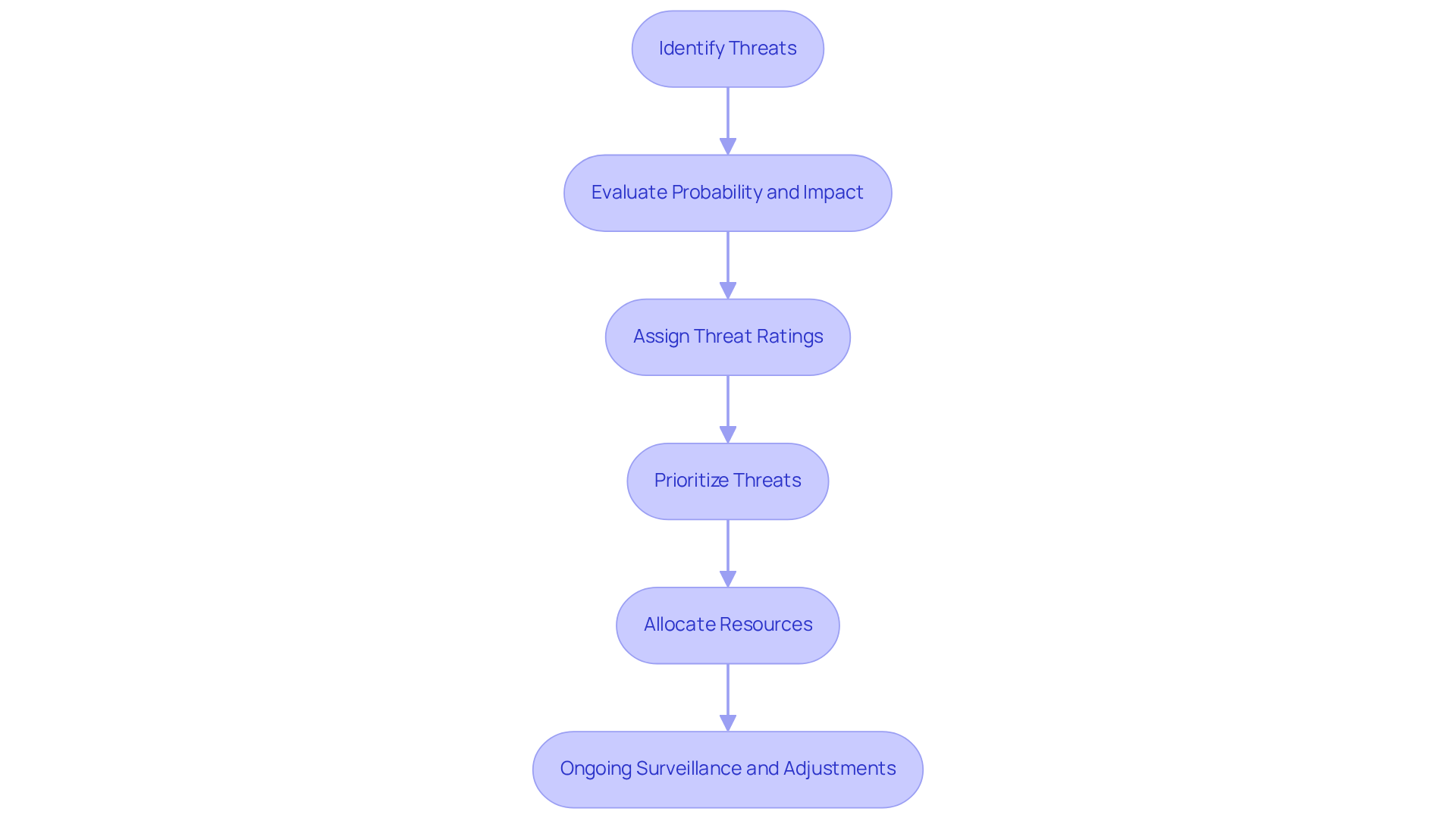
A threat matrix serves as a vital tool for systematically evaluating the probability of each recognized danger exploiting a vulnerability, which is crucial for a comprehensive cyber attack risk assessment and understanding the potential impact on your organization. This matrix not only facilitates a clear visualization of hazards but also allows you to assign a threat rating to each threat-vulnerability combination. By classifying uncertainties in this manner, you can prioritize those that demand urgent attention, ensuring effective allocation of resources.
Are you aware that organizations are increasingly adopting a 5×5 assessment matrix? This approach offers a more detailed categorization of dangers compared to the simpler 3×3 matrix. Such a comprehensive method aids in the cyber attack risk assessment by evaluating both the seriousness and probability of risks, enabling informed decision-making. Recording the outcomes of your assessments is essential; it establishes a reference point for future evaluations and strategic planning.
Ongoing surveillance and adjustment of the threat matrix are crucial for an effective cyber attack risk assessment to reflect the evolving danger landscape and compliance needs. This ensures that your entity remains robust against cyber threats. Consider this: the worldwide average cost of a data breach in 2024 is projected to hit USD 4.88 million. Efficient evaluations of potential issues are more critical than ever.
Furthermore, case studies have shown that optimizing resource distribution based on threat prioritization can significantly enhance a company's cybersecurity posture. Are you ready to take action and implement these strategies to safeguard your organization?
Develop a Mitigation Plan
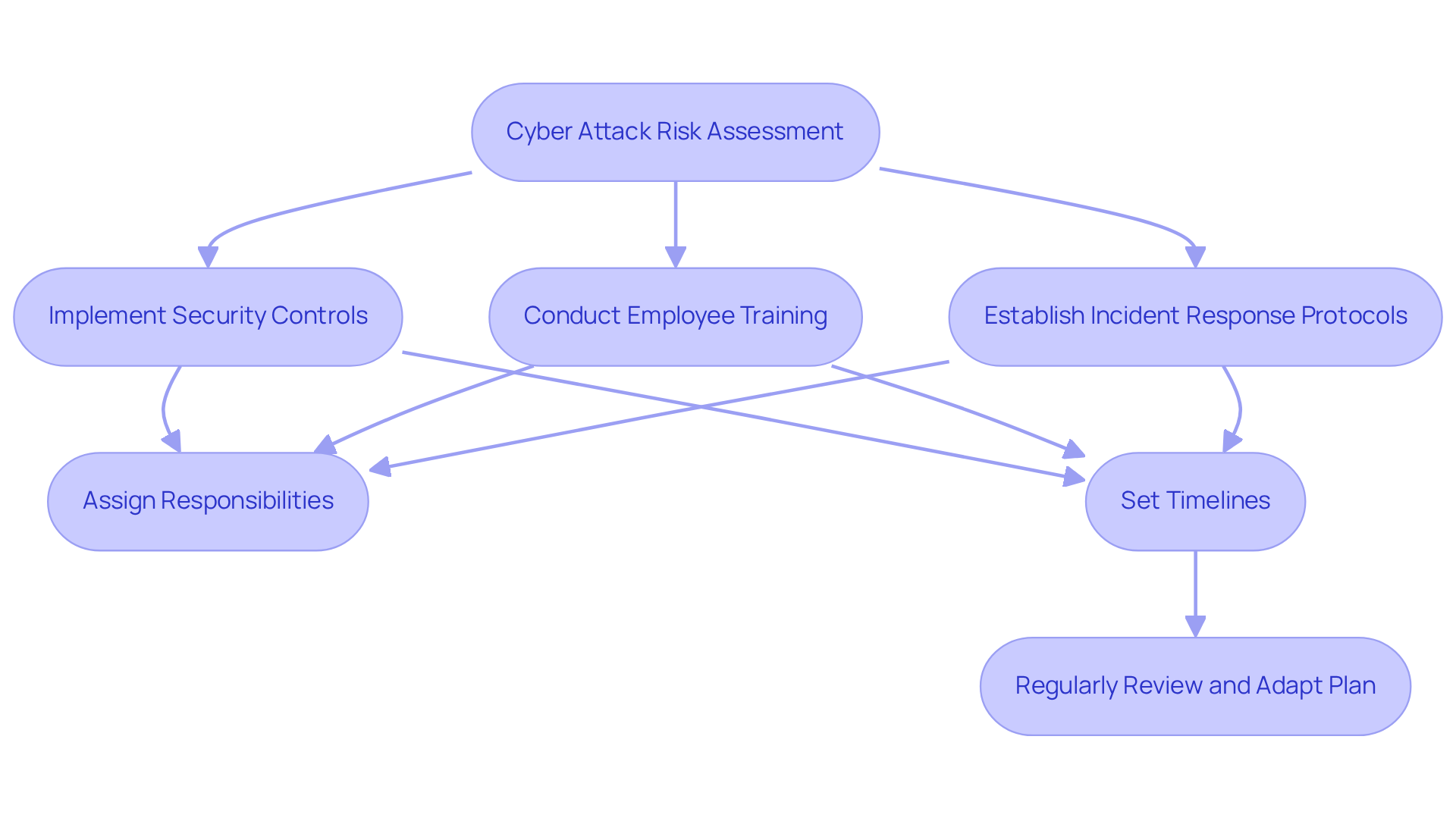
Based on your cyber attack risk assessment, it’s essential to develop a comprehensive mitigation plan that outlines specific actions to address each identified risk. This plan should include:
- The implementation of security controls
- Conducting employee training initiatives
- Establishing incident response protocols
Who will be responsible for each action item? Clearly assign responsibilities and set realistic timelines for implementation.
With CMMC compliance becoming mandatory for federal contractors starting November 10, 2025, prioritizing these actions is crucial. Regularly examine and revise your mitigation strategy to adapt to new risks and changes within your organization. This ensures that you maintain your CMMC level for all information systems utilized in contract execution.
Successful companies demonstrate that proactive training and clear communication of responsibilities significantly enhance their cybersecurity posture, particularly in the defense contracting sector. As Sean Cairncross noted, "This requires regulators to come to the table and for the private sector to step up," underscoring the importance of collaboration in achieving compliance.
Furthermore, subcontractors must submit affirmations of compliance and self-assessment results into the Supplier Performance Risk System (SPRS). This requirement further emphasizes the need for a robust and adaptable plan for cyber attack risk assessment. Are you ready to take the necessary steps to ensure compliance and protect your organization?
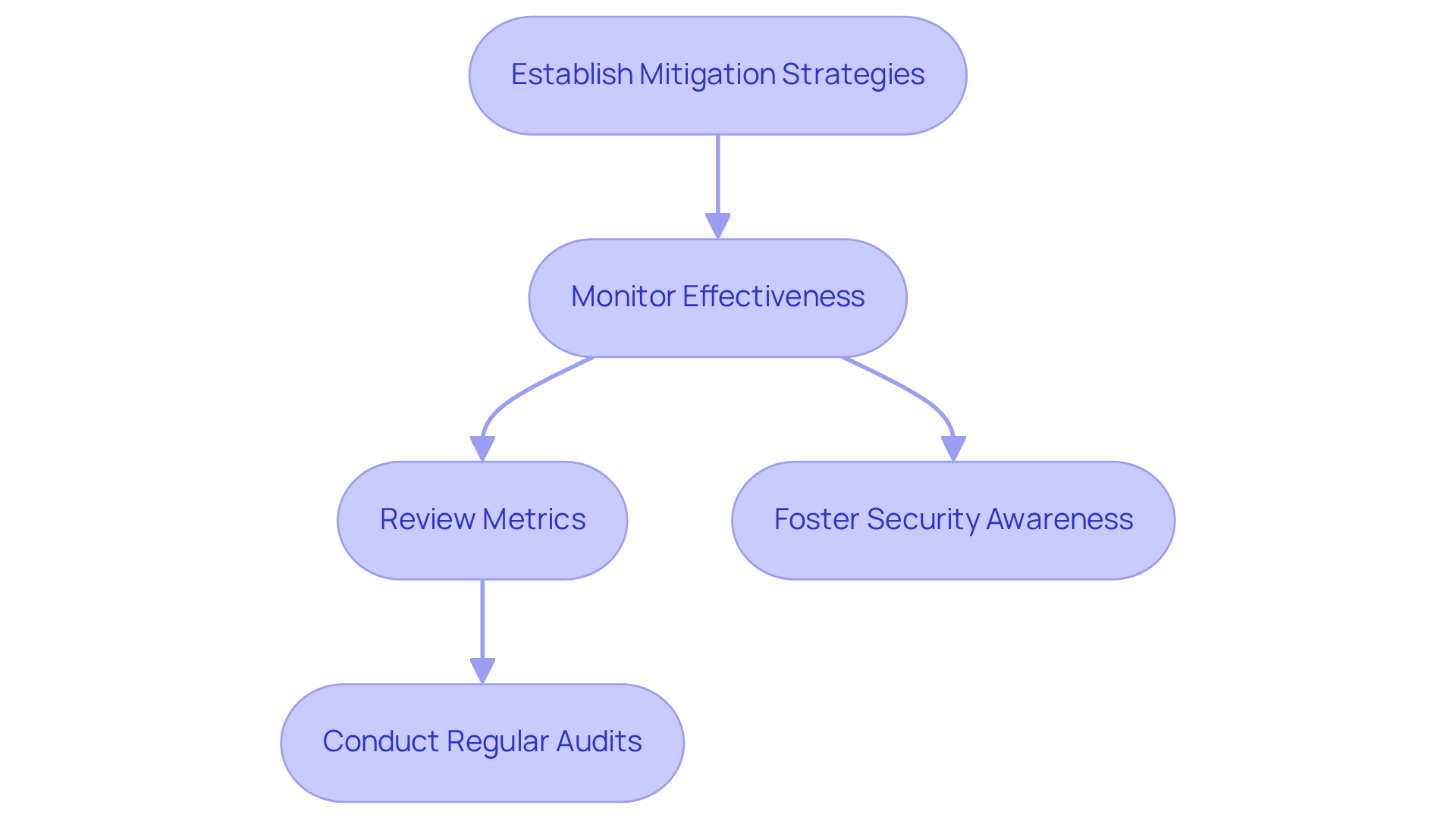
Implement and Monitor Mitigation Strategies
After establishing your mitigation strategies, it’s essential to continuously monitor their effectiveness through regular audits and cyber attack risk assessments. Are you utilizing advanced security monitoring tools like intrusion detection systems (IDS), security information and event management (SIEM) solutions, and endpoint detection and response (EDR) platforms? These tools can help you identify anomalies or breaches in real-time. Current trends show a growing reliance on AI-driven analytics and machine learning capabilities within these tools, significantly enhancing their ability to detect sophisticated threats.
To gauge the success of your mitigation efforts, establish key performance indicators (KPIs) that align with your entity's risk management objectives. Effective KPIs might include:
- The average time to detect and respond to incidents
- The percentage of systems under active monitoring
- The rate of unresolved critical vulnerabilities
Regularly reviewing these metrics will provide insights into your cybersecurity posture and highlight areas for improvement.
Best practices for conducting regular audits include:
- Developing a structured audit schedule
- Ensuring comprehensive coverage of all systems
- Involving cross-functional teams to gain diverse perspectives
Additionally, fostering a culture of security awareness among employees can significantly enhance the effectiveness of your monitoring efforts. Are you prepared to adjust your strategies based on the outcomes of your monitoring activities and any shifts identified in your cyber attack risk assessment? This adaptability ensures that your organization remains resilient against evolving cyber threats.
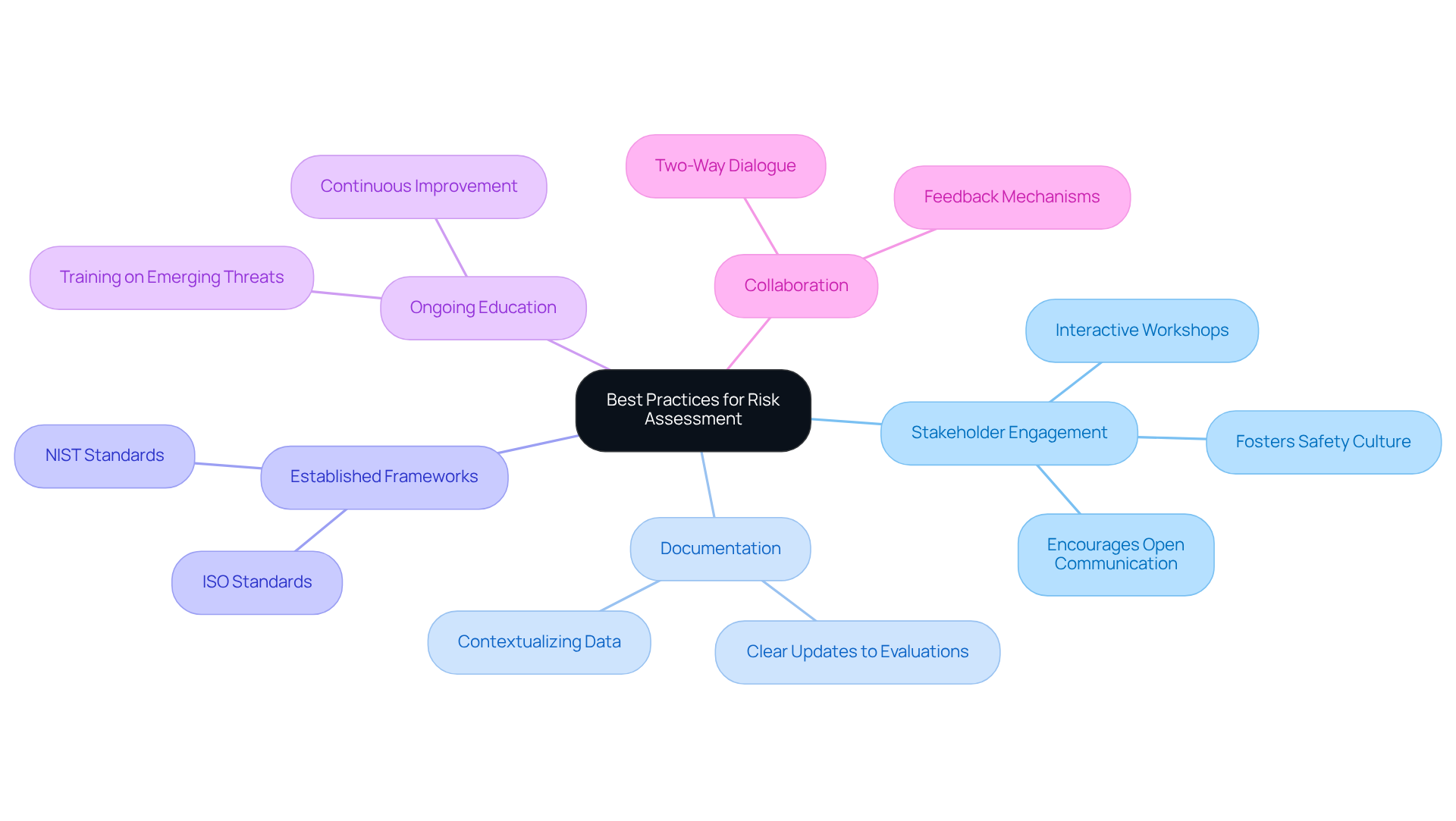
Follow Best Practices for Risk Assessment
To achieve an effective assessment process, it’s crucial to implement best practices that prioritize stakeholder engagement across various departments. Why is this important? Involving stakeholders not only fosters a culture of safety but also enhances the quality of assessments by integrating diverse perspectives. Clear documentation and regular updates to evaluations are vital, especially in light of new information or organizational changes. Utilizing established frameworks like NIST or ISO standards provides a structured approach to effectively guide the cyber attack risk assessment.
Moreover, ongoing education and training for your team on emerging threats and hazard management techniques are essential. This commitment to learning ensures that all parties are equipped to identify and address potential challenges proactively. For example, interactive workshops can spark discussions around risk findings, enabling stakeholders to express concerns and share insights. This collaborative approach ultimately leads to more comprehensive assessments. By cultivating an environment of open communication and teamwork, organizations can significantly bolster their cybersecurity posture and resilience against evolving threats through a cyber attack risk assessment.
Conclusion
A comprehensive cyber attack risk assessment is crucial for organizations that want to protect their digital assets from ever-evolving threats. By systematically identifying, prioritizing, and addressing risks, organizations can establish a resilient cybersecurity framework that not only safeguards critical assets but also enhances overall operational integrity.
Key steps in this process include:
- Understanding the types of risks and vulnerabilities
- Recognizing potential threats
- Developing a robust mitigation plan
Each phase, from identifying critical assets to implementing and monitoring mitigation strategies, plays a vital role in strengthening an organization's defenses. By adhering to best practices and engaging stakeholders throughout the assessment, companies can ensure a proactive approach to cybersecurity that adapts to emerging challenges.
Ultimately, the importance of a thorough cyber attack risk assessment cannot be overstated. It serves as a foundational element in building a resilient cybersecurity posture, enabling organizations to navigate the complex landscape of cyber threats effectively. Taking action now to implement these strategies will not only protect sensitive information but also foster a culture of security awareness that is essential in today’s digital environment.
Frequently Asked Questions
What is a cyber attack risk assessment?
A cyber attack risk assessment is a structured procedure that helps organizations identify, assess, and prioritize risks associated with potential cyber threats, which is essential for developing a robust cybersecurity strategy.
Why is understanding threats and vulnerabilities important in cybersecurity?
Understanding the concepts of threat and vulnerability is vital because their interconnections help prepare organizations for a cyber attack risk assessment against cyber threats.
What should organizations do to assess their cybersecurity posture?
Organizations should start by evaluating their current cybersecurity posture and identifying areas for improvement through a thorough cyber attack risk assessment.
How can organizations identify critical assets?
Organizations can identify critical assets by compiling a comprehensive inventory of all hardware, software, data, and personnel, and classifying these assets based on their criticality to operations.
What factors should be considered when classifying assets?
Factors to consider include data sensitivity, the roles of assets in business processes, and the potential consequences of their compromise.
How can asset management software assist in the classification process?
Recognized asset management software can streamline the classification process, ensuring accuracy and efficiency in managing the inventory of organizational assets.
Why is it important to regularly update the asset inventory?
Regular updates to the asset inventory are crucial to reflect any changes in the organization’s infrastructure, maintaining an up-to-date understanding of the cybersecurity landscape.
What is the significance of categorizing essential assets in a cyber attack risk assessment?
Categorizing essential assets allows organizations to prioritize protective measures effectively and allocate resources strategically to protect the most sensitive and impactful components of their operations.
What does current trend indicate regarding asset visibility?
Current trends indicate a growing emphasis on comprehensive asset visibility, which enhances the ability to mitigate threats and reduce security incidents.
What advice does the National Security Agency provide regarding asset inventory?
The National Security Agency emphasizes the importance of establishing and overseeing an asset inventory to assist in cyber attack risk assessment and weakness management, particularly considering vulnerabilities from unmanaged operational technology (OT) devices.




