Master Cybersecurity IR: Essential Practices for Defense Contractors
Master essential practices for cybersecurity IR to protect sensitive data and enhance compliance.

Introduction
Effective incident response stands as a cornerstone of cybersecurity, particularly for defense contractors entrusted with sensitive information and bound by rigorous regulatory standards. Mastering incident response practices not only safeguards these organizations' assets but also bolsters their compliance with the Cybersecurity Maturity Model Certification (CMMC). Yet, many organizations struggle with the effective implementation of these strategies.
What essential steps and best practices can transform their approach to incident management? How can they fortify their defenses against ever-evolving cyber threats? By addressing these questions, we can uncover actionable insights that empower organizations to enhance their cybersecurity posture and ensure compliance.
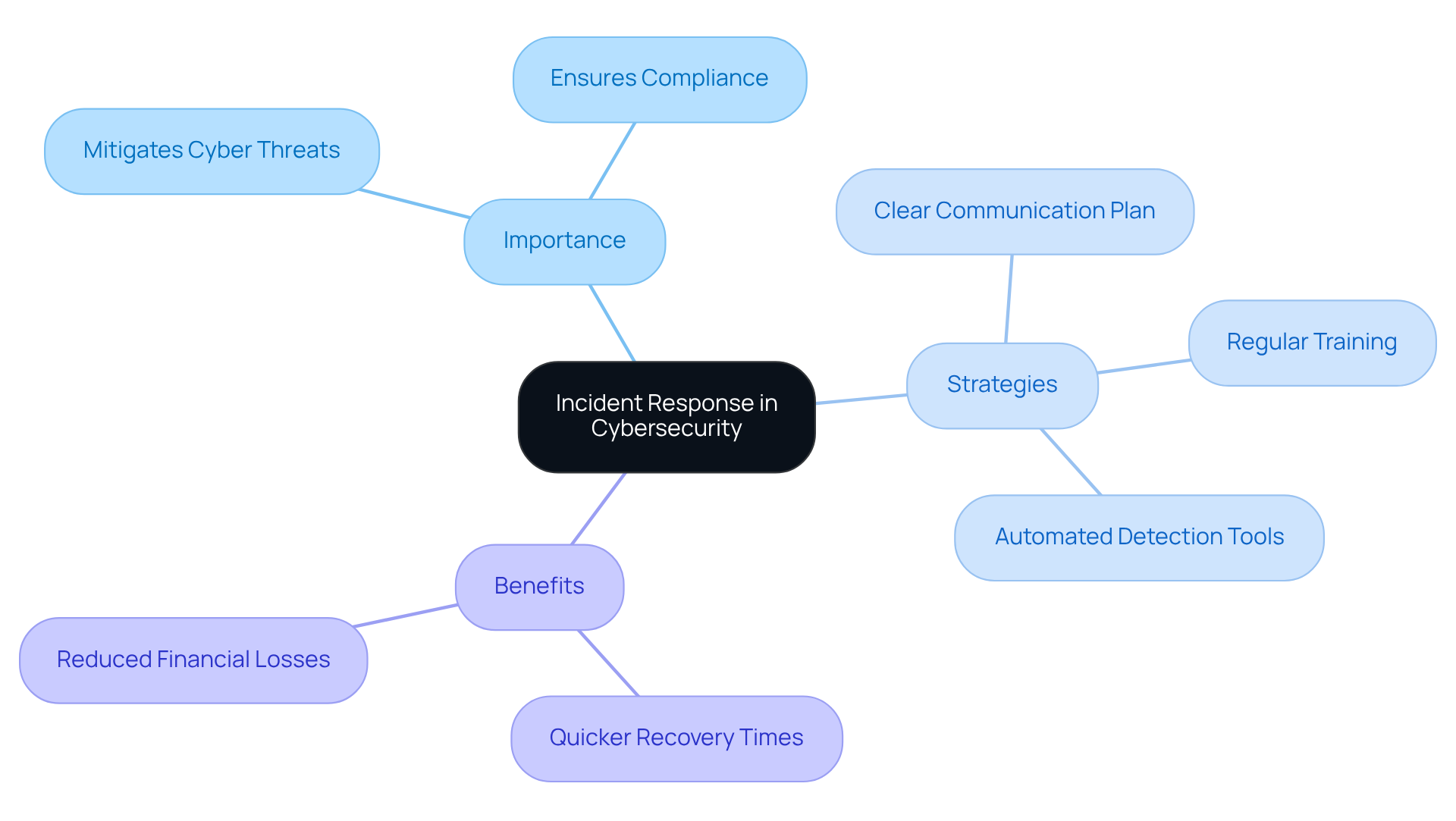
Understand the Importance of Incident Response in Cybersecurity
Incident management stands as a crucial pillar in the realm of cybersecurity IR, particularly for defense contractors entrusted with sensitive information and bound by rigorous regulatory standards. Why is this so important? Efficient event handling mitigates the repercussions of cyber threats, ensuring that organizations can swiftly recover from incidents while remaining compliant with the Cybersecurity Maturity Model Certification (CMMC).
By implementing practical strategies - such as establishing a clear communication plan, conducting regular training exercises, and utilizing automated detection tools - defense contractors can turn confusion into clarity regarding their compliance efforts. A well-defined incident response (IR) strategy not only protects essential assets but also enhances a company's overall cybersecurity IR posture, fostering trust among stakeholders and clients.
Consider this: organizations that embrace proactive cybersecurity IR strategies can significantly reduce the duration and impact of security events. Case studies reveal that these entities experience quicker recovery times and diminished financial losses. This proactive approach empowers defense contractors to pursue CMMC compliance with confidence, ensuring they are well-prepared to face the challenges of the cybersecurity landscape.
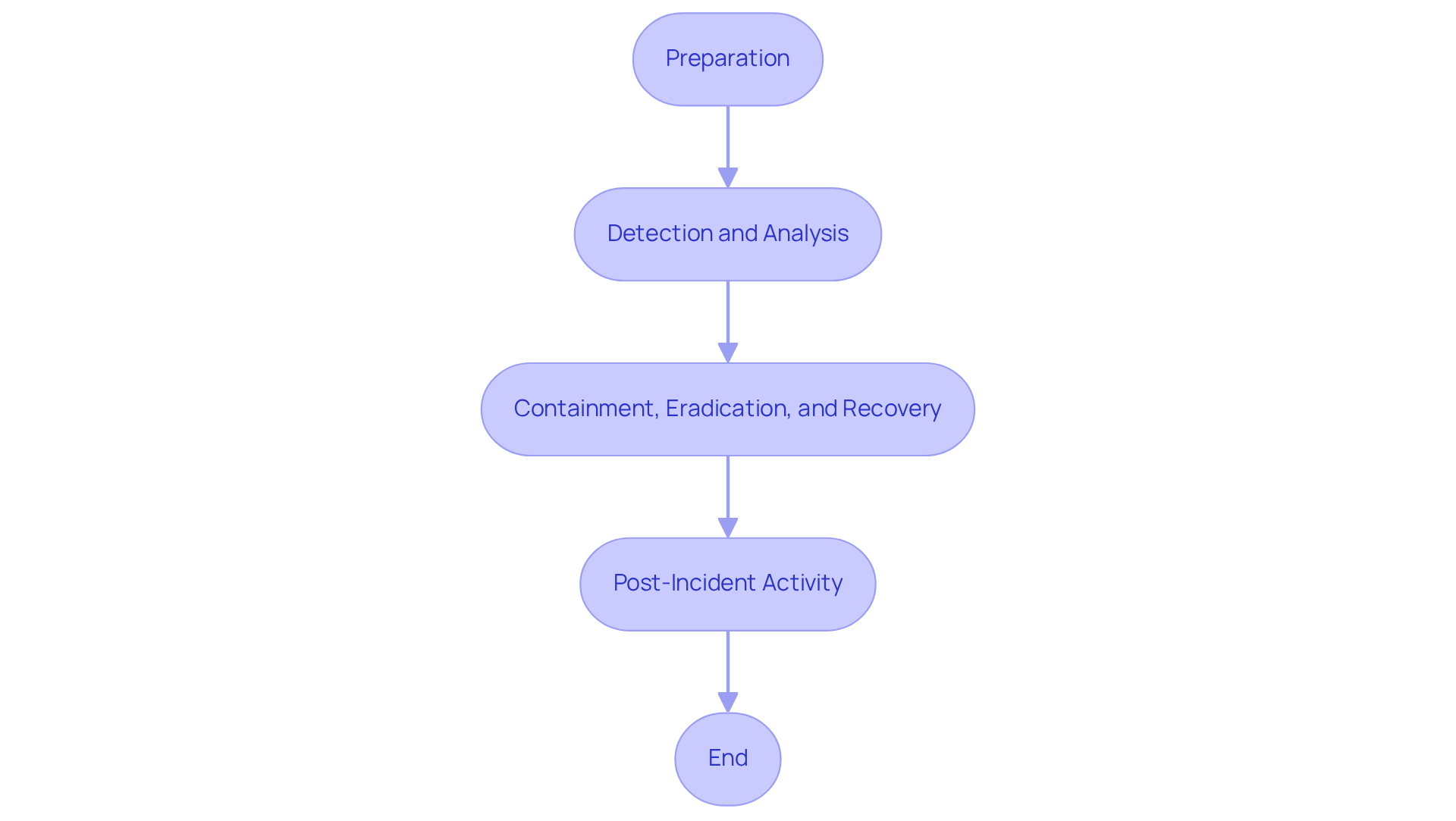
Implement the NIST Incident Response Framework: A Step-by-Step Guide
To effectively implement the NIST Incident Response Framework, organizations must follow these essential steps:
-
Preparation: Start by developing a comprehensive crisis management policy. Assemble a crisis management team and provide extensive training to ensure all personnel are ready to act effectively. Practical drills and exercises are crucial for evaluating response plans, ensuring readiness for real situations.
-
Detection and Analysis: Utilize advanced monitoring tools to promptly identify potential events. This phase involves gathering and examining data to assess the severity and impact of the occurrence, in line with the latest guidance from NIST SP 800-61 Rev. 3, published in July 2025.
-
Containment, Eradication, and Recovery: Once an occurrence is verified, initiate immediate containment measures to minimize damage. After containment, eradicate the threat and restore systems to normal operations, ensuring that all vulnerabilities are addressed.
-
Post-Incident Activity: Conduct a thorough analysis of the occurrence to derive lessons learned and enhance future approaches. This includes revising the event management strategy based on insights from the review and documenting procedures in playbooks to guarantee consistency and reproducibility.
By following these organized steps, organizations can establish a robust capability for cybersecurity incident response that aligns with NIST standards for handling events. This approach emphasizes continuous improvement throughout the event lifecycle, ultimately boosting cybersecurity incident response resilience and readiness for future occurrences.
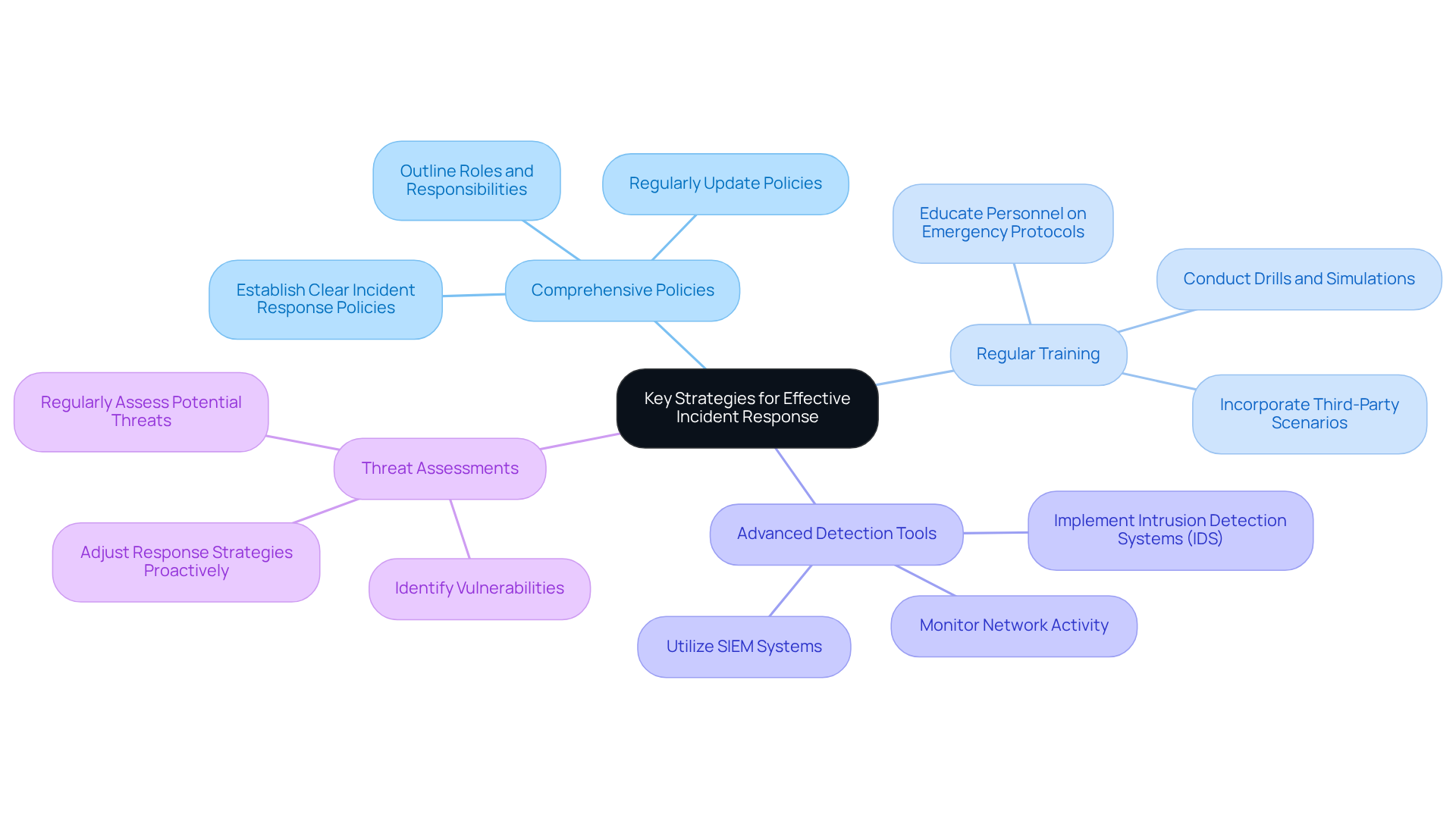
Prioritize Preparation and Detection: Key Strategies for Effective Incident Response
Efficient event management hinges on readiness and detection tactics. To enhance your organization's capabilities, consider these key practices:
- Develop Comprehensive Policies: Establish clear incident response policies that outline roles, responsibilities, and procedures for handling incidents. This clarity ensures everyone knows what to do when the unexpected occurs.
- Conduct Regular Training: Routinely educate personnel on emergency protocols. When everyone understands their role during a crisis, the organization can respond more effectively.
- Implement Advanced Detection Tools: Utilize cybersecurity measures such as security information and event management (SIEM) systems and intrusion detection systems (IDS) to monitor network activity and detect anomalies. These tools are essential for identifying potential threats before they escalate.
- Perform Threat Assessments: Regularly assess potential threats and vulnerabilities. Staying ahead of emerging risks allows companies to adjust their response strategies proactively.
By concentrating on these aspects, organizations can significantly enhance their cybersecurity measures to identify and react to incidents promptly, thereby reducing potential harm. Are you ready to implement these practices and bolster your event management strategy?
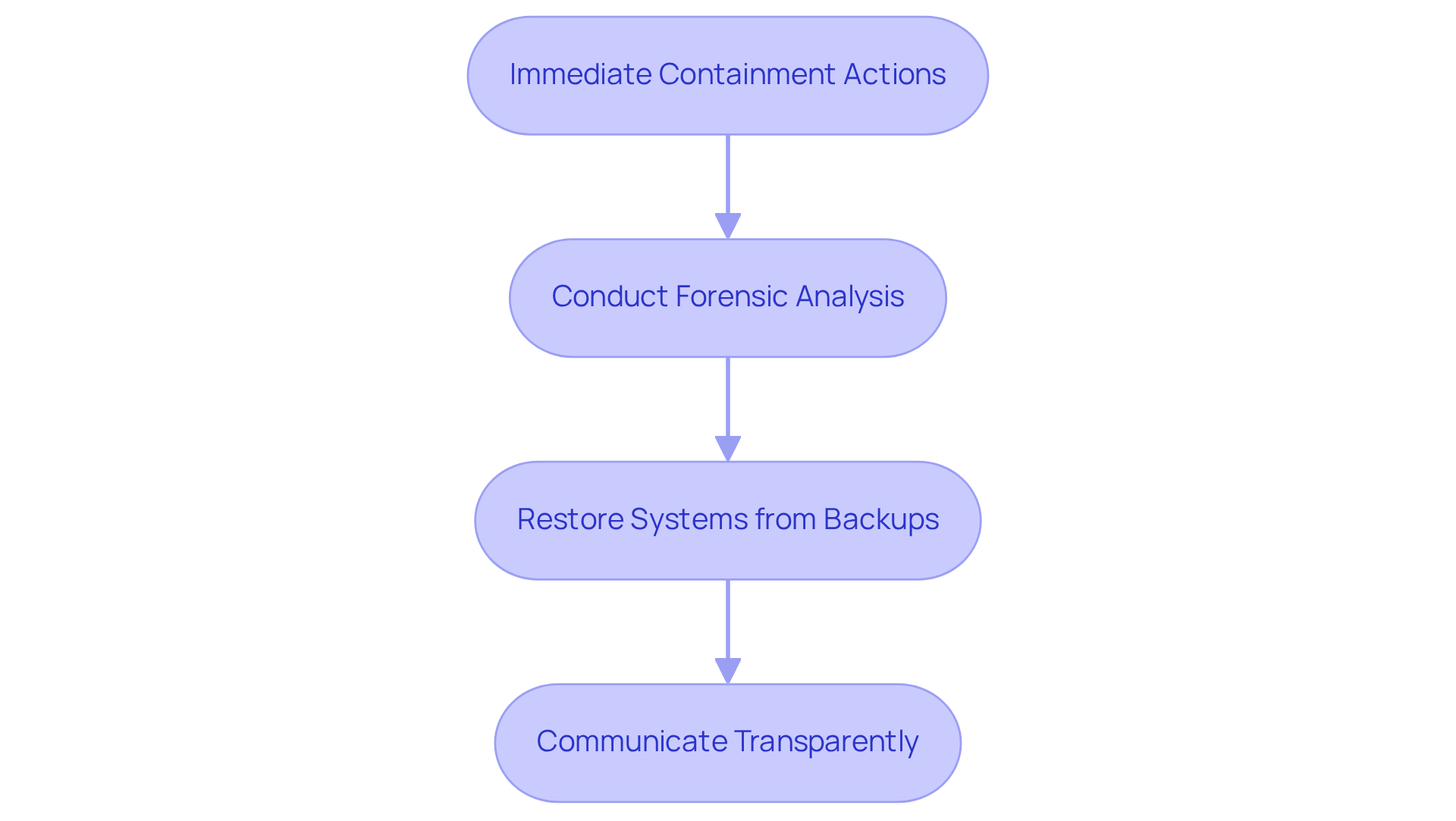
Execute Containment and Recovery: Best Practices for Mitigating Cyber Threats
To effectively execute containment and recovery during a cyber incident, organizations must adopt essential practices that enhance cybersecurity while mitigating risks and ensuring compliance with CMMC requirements.
- Immediate Containment Actions: Upon detecting an incident, it’s crucial to act swiftly. This involves isolating affected systems, disabling compromised accounts, and blocking malicious traffic to prevent further damage.
- Conduct Forensic Analysis: Once containment is achieved, a thorough forensic analysis is necessary. This step helps organizations understand the nature of the attack and pinpoint the vulnerabilities that were exploited.
- Restore Systems from Backups: Regularly updating and securely storing data backups is vital. In the event of a cyber incident, restoring affected systems from these backups minimizes downtime and ensures business continuity.
- Communicate Transparently: Clear communication with stakeholders throughout the incident response process is essential. Transparency fosters trust and keeps all parties informed about the situation and recovery efforts.
By implementing these cybersecurity practices, organizations can effectively mitigate the impact of cyber threats and ensure a swift recovery. This proactive approach not only safeguards their operations but also reinforces their commitment to compliance with CMMC standards.
Conclusion
In the intricate realm of cybersecurity, especially for defense contractors, the importance of a robust incident response strategy is paramount. A comprehensive approach to incident management is not just beneficial; it’s essential for protecting sensitive information and ensuring compliance with rigorous regulatory standards like the Cybersecurity Maturity Model Certification (CMMC). By prioritizing effective incident response, organizations safeguard their vital assets and enhance their overall security posture, fostering trust among clients and stakeholders.
Key practices for enhancing incident response capabilities have been outlined throughout this article. These practices include:
- Implementing the NIST Incident Response Framework
- Emphasizing preparation and detection
- Executing effective containment and recovery strategies
Each of these components is crucial in minimizing the impact of cyber threats, enabling organizations to respond swiftly and efficiently to incidents while maintaining operational integrity. Proactive measures, such as regular training and advanced detection tools, empower defense contractors to stay ahead of potential risks, ensuring a more resilient cybersecurity environment.
The call to action is clear: defense contractors must take decisive steps to implement these best practices and fortify their incident response frameworks. By doing so, they not only mitigate the risks associated with cyber threats but also position themselves as leaders in cybersecurity preparedness. Embracing these strategies will pave the way for a more secure future, equipping organizations to navigate the evolving challenges of the cybersecurity landscape.
Frequently Asked Questions
What is the importance of incident response in cybersecurity for defense contractors?
Incident response is crucial for defense contractors as it helps mitigate the repercussions of cyber threats, ensuring swift recovery from incidents while maintaining compliance with regulatory standards like the Cybersecurity Maturity Model Certification (CMMC).
How can organizations improve their incident response strategies?
Organizations can enhance their incident response strategies by establishing a clear communication plan, conducting regular training exercises, and utilizing automated detection tools.
What are the benefits of having a well-defined incident response strategy?
A well-defined incident response strategy protects essential assets, enhances a company's overall cybersecurity posture, and fosters trust among stakeholders and clients.
How does a proactive cybersecurity incident response strategy affect recovery times and financial losses?
Organizations that adopt proactive incident response strategies experience quicker recovery times and reduced financial losses during security events.
What role does incident management play in achieving CMMC compliance?
Effective incident management is essential for achieving CMMC compliance, as it prepares defense contractors to handle cybersecurity challenges confidently and efficiently.




