Master IT Security Management and Risk Assessment in 5 Steps
Master IT security management and risk assessment with a structured five-step approach.

Introduction
In an age where cyber threats loom larger than ever, organizations face an urgent need to fortify their defenses against potential breaches. Mastering IT security management and risk assessment is not merely a regulatory requirement; it’s a strategic advantage that can safeguard sensitive information and maintain operational integrity. This guide presents a structured approach to navigating the complexities of risk assessment, outlining five essential steps that empower organizations to proactively identify vulnerabilities and implement effective controls.
How can businesses transform compliance from a mere checkbox into a robust strategy that enhances their resilience against emerging threats? By understanding the critical nature of these steps, organizations can not only meet compliance standards but also strengthen their overall security posture.
Understand IT Security Management and Risk Assessment
The processes and practices involved in IT security management and risk assessment are essential for organizations to safeguard their information systems from unauthorized access, use, disclosure, disruption, modification, or destruction. A critical component of this framework is IT security management and risk assessment, which systematically identifies, assesses, and prioritizes threats to organizational operations and assets. For instance, organizations that have implemented comprehensive vulnerability assessment protocols have effectively pinpointed weaknesses that could lead to data breaches. This proactive approach enables them to adopt targeted measures that significantly reduce their exposure to threats.
Understanding these concepts is vital for developing effective IT security management and risk assessment strategies that comply with regulatory requirements, such as the Cybersecurity Maturity Model Certification (CMMC). This knowledge empowers organizations not only to identify potential threats but also to implement appropriate measures to mitigate risks efficiently. Cybersecurity experts emphasize that a solid understanding of IT security management and risk assessment is essential for organizations aiming to achieve CMMC compliance. It transforms compliance from a mere checklist into a proactive strategy for safeguarding sensitive information. By fostering a culture of security awareness and integrating threat evaluation into daily operations, organizations can bolster their resilience against emerging cyber threats.
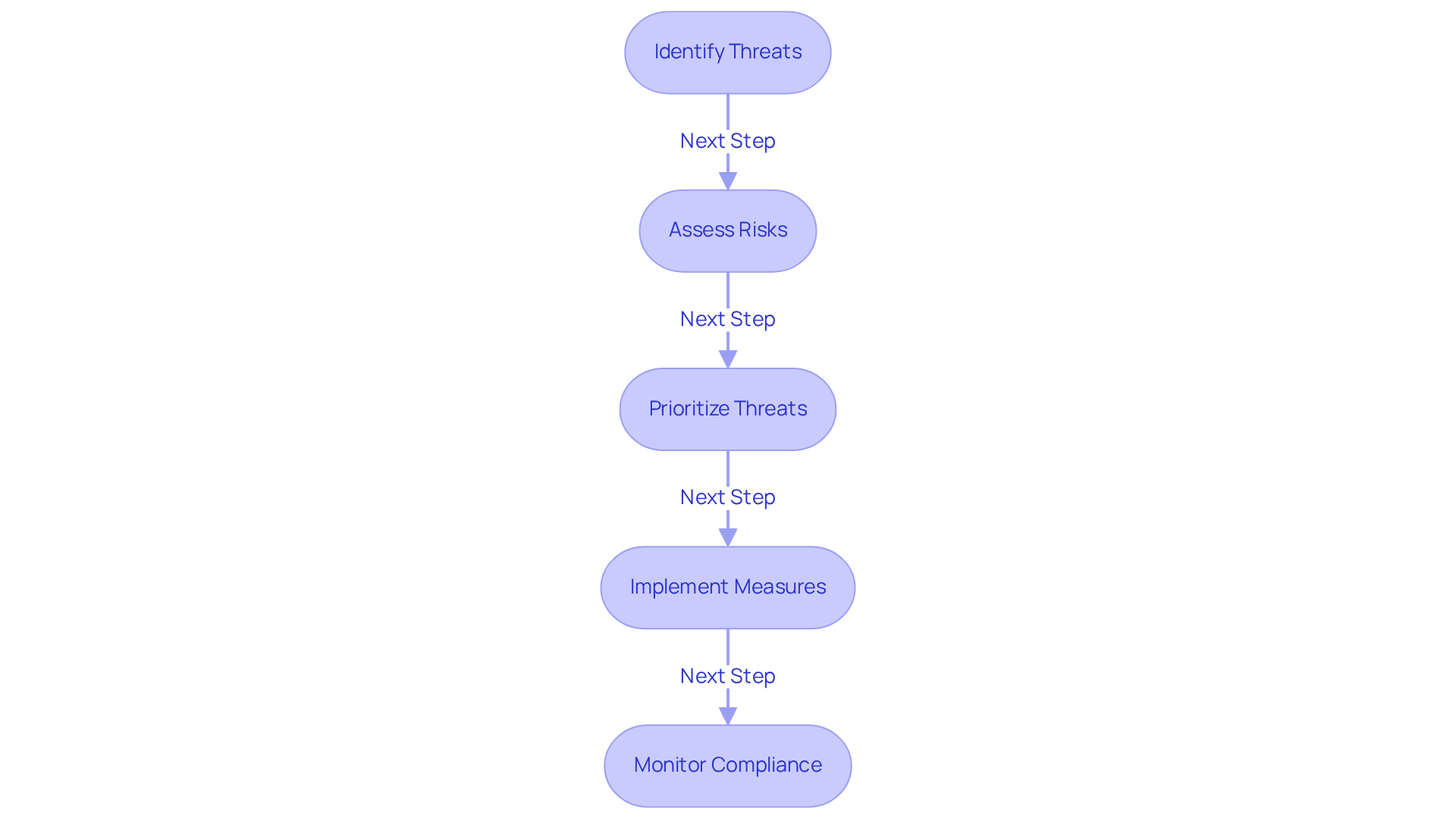
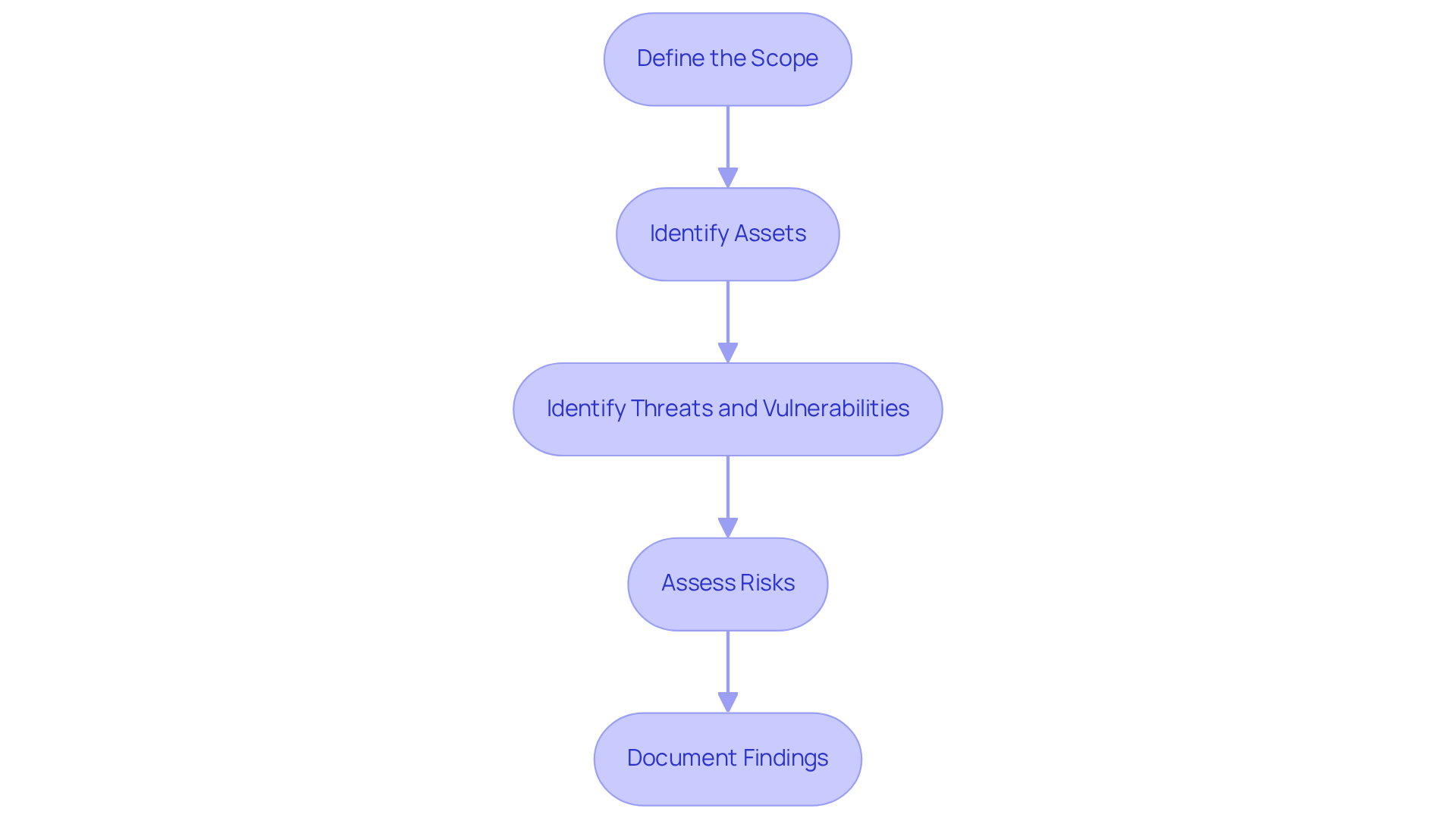
Follow Step-by-Step Procedures for Risk Assessment
-
Define the Scope: Establishing clear boundaries for threat evaluation is crucial. This involves identifying the systems, assets, and processes that will be assessed. A well-defined scope in it security management and risk assessment ensures that the evaluation focuses on critical areas, allowing organizations to allocate resources effectively and prioritize their cybersecurity initiatives. Did you know that approximately 70% of organizations that clearly outline their scope in assessments report improved clarity and focus in their protection strategies?
-
Identify Assets: Cataloging all information assets—such as hardware, software, and data—is vital for managing potential issues effectively. Understanding what requires protection enables organizations to tailor their it security management and risk assessment measures accordingly. This includes both physical assets like servers, workstations, and mobile devices, as well as virtual assets such as virtual machines and cloud services. For example, a small retail store might prioritize safeguarding customer databases and point-of-sale systems to protect these critical assets from potential threats.
-
Identify Threats and Vulnerabilities: Conduct a thorough analysis of potential threats, including cyberattacks and natural disasters, alongside vulnerabilities like outdated software and weak passwords. This step is essential for understanding the threat landscape that could impact your assets in the context of it security management and risk assessment. Organizations should utilize tools such as vulnerability scanners to proactively identify weaknesses in their systems.
-
Assess Risks: Evaluate the likelihood and potential impact of identified threats as part of it security management and risk assessment. Use qualitative or quantitative techniques to prioritize threats based on their severity. For instance, employing a Risk Matrix Model can help illustrate the severity of threats across various systems, guiding organizations in their mitigation strategies.
-
Document Findings: Create a comprehensive report detailing the identified threats, their potential impacts, and recommendations for mitigation. This documentation is not only crucial for compliance with frameworks like NIST CSF and CMMC but also serves as a reference for future evaluations, ensuring that organizations can monitor their progress and adapt to evolving threats effectively.
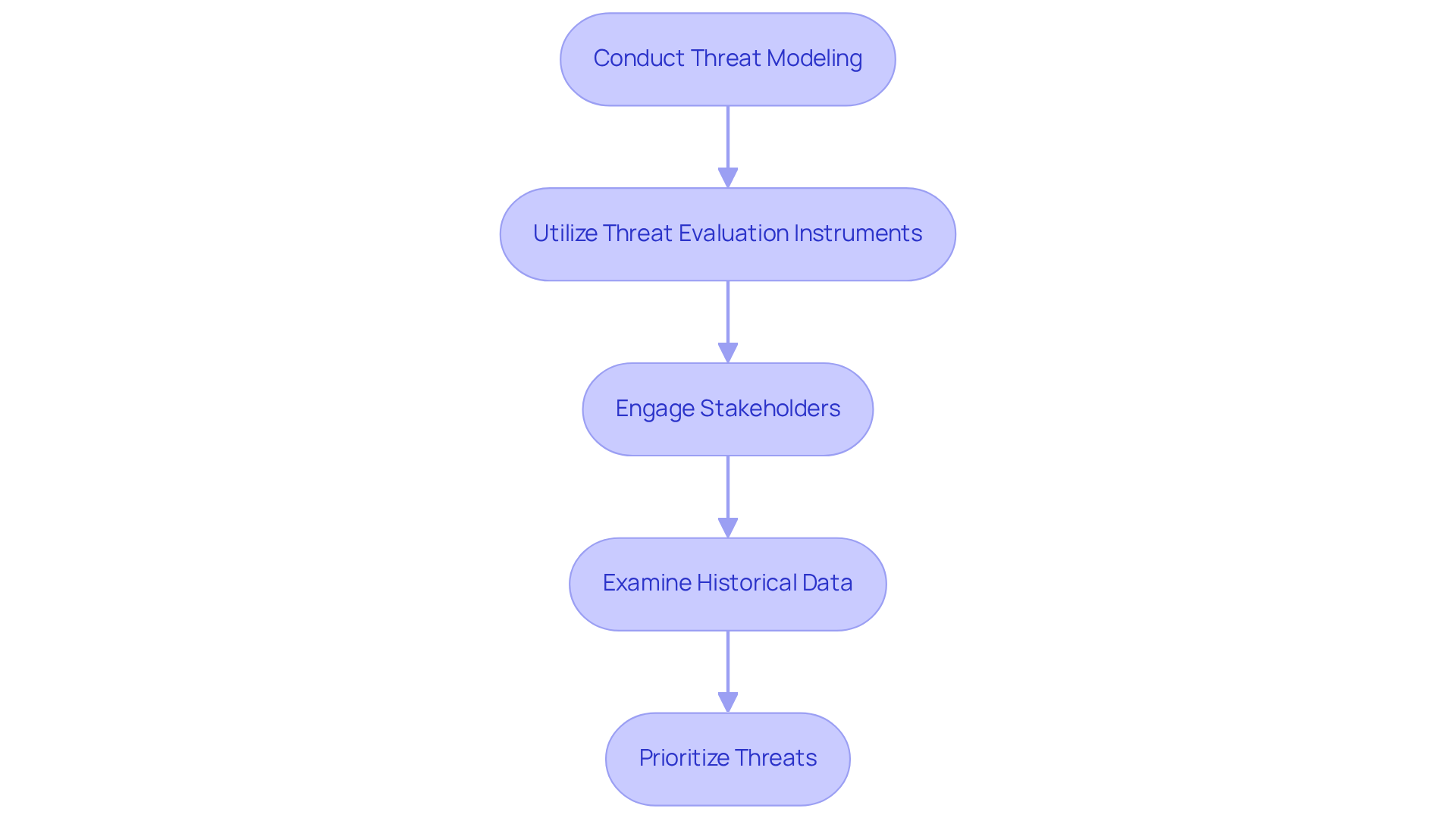
Identify and Evaluate Potential Risks
To effectively identify and evaluate potential risks, organizations must take a structured approach:
-
Conduct Threat Modeling: Begin by employing threat modeling techniques. This allows you to visualize potential attack vectors and understand how threats could exploit vulnerabilities in your systems. Have you considered how a simple oversight could lead to significant breaches?
-
Utilize Threat Evaluation Instruments: Leverage established tools and frameworks, such as NIST and ISO 27001, to systematically identify dangers. These resources provide templates and methodologies that facilitate thorough evaluations, ensuring no stone is left unturned.
-
Engage Stakeholders: Involve key stakeholders from various departments—IT, legal, compliance—to gather diverse viewpoints on potential threats and their impacts. This collaborative approach not only enriches the evaluation process but also fosters a culture of security awareness across the organization.
-
Examine Historical Data: Review previous incidents and breaches within your company and the industry. Identifying patterns and common vulnerabilities can reveal threats that may arise in the future. What lessons can be learned from past mistakes?
-
Prioritize Threats: Finally, arrange recognized threats according to their probability and potential impact on the organization. Focus on critical threats that could significantly influence operations or compliance. By prioritizing effectively, you can allocate resources where they are needed most.
By following these steps, organizations can not only enhance their risk management strategies but also ensure a proactive stance against potential threats.
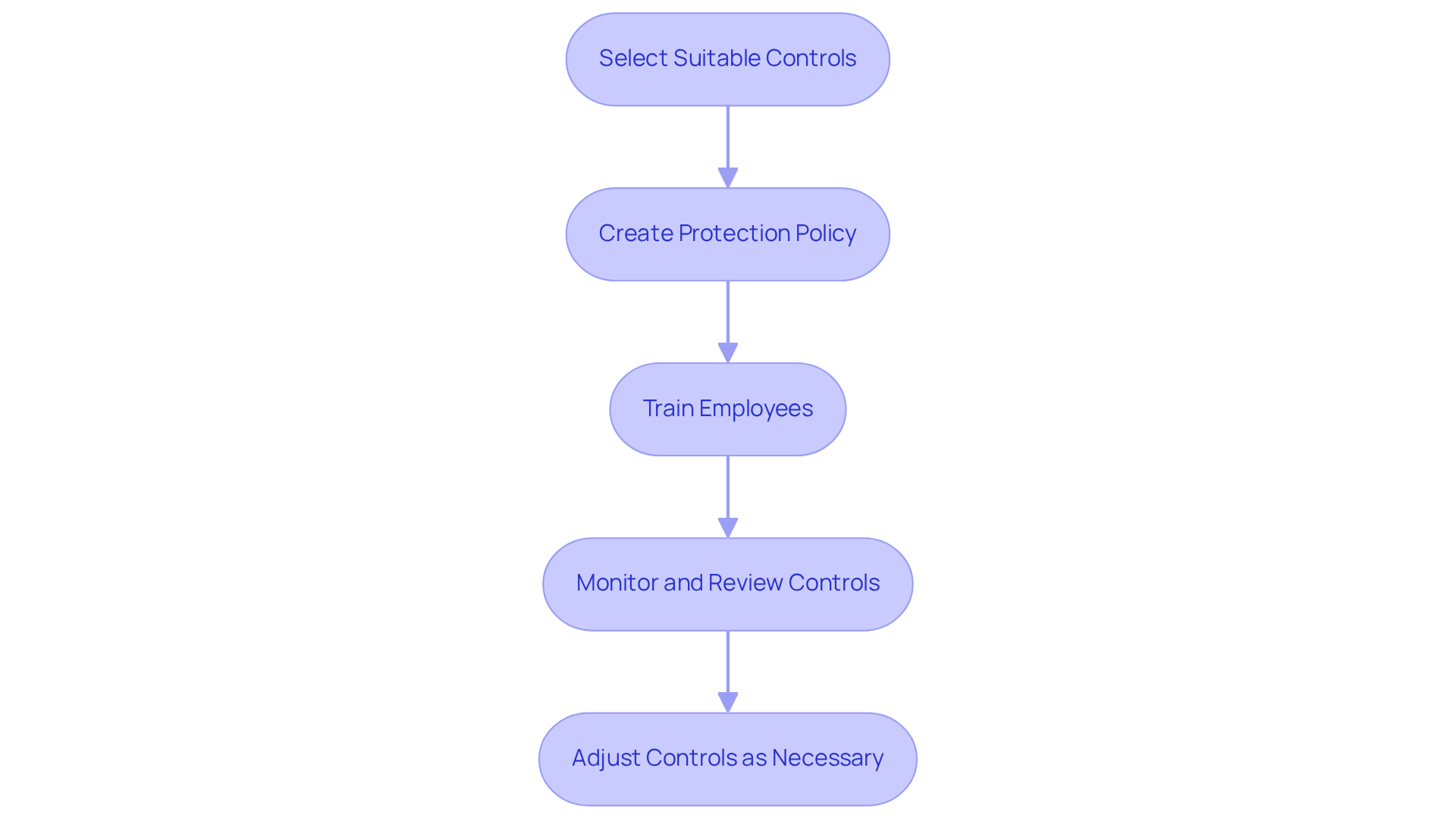
Implement Controls to Mitigate Risks
To implement controls effectively and achieve CMMC compliance with confidence, organizations should follow these essential steps:
-
Select Suitable Controls: Start by choosing protective measures based on a comprehensive risk evaluation. These controls fall into three categories: technical (like firewalls and encryption), administrative (including policies and training), and physical (such as access controls). For CMMC Level 2 adherence, it’s crucial to align your controls with the 110 protective measures outlined in NIST SP 800-171 Rev. 2. This alignment ensures a clear path from confusion to clarity in your compliance efforts.
-
Create a protection policy that incorporates IT security management and risk assessment, outlining your organization’s strategy for managing risks. This policy should clearly define roles and responsibilities, ensuring that every team member understands their part in maintaining security. Proper documentation is essential; without clear policies, adherence efforts can falter. This policy serves as a roadmap for achieving CMMC adherence and is vital for effective IT security management and risk assessment to ensure DoD cybersecurity success.
-
Train Employees: Conduct regular training sessions to ensure all employees are familiar with safety policies and understand their roles in protecting the organization. Awareness and education are crucial in preventing human error, a significant vulnerability. This practice is essential for maintaining the effectiveness of your policies and ensuring adherence.
-
Monitor and Review Controls: Implement a robust monitoring system to regularly evaluate the effectiveness of your security controls. This can involve audits, penetration testing, and continuous monitoring tools to identify weaknesses. Additionally, keep adherence documents for a minimum of six years following the submission of CMMC assessment results to demonstrate conformity to requirements. Ongoing monitoring is vital for IT security management and risk assessment, ensuring compliance and adapting to new challenges.
-
Adjust Controls as Necessary: Stay agile by being prepared to modify controls in response to emerging threats, vulnerabilities, or changes in your organization’s operations. Ongoing enhancement is crucial for sustaining a robust defensive stance. Consider partnering with external service providers to effectively manage your cybersecurity requirements, ensuring you remain compliant and secure.
Review and Adjust Security Measures Regularly
Organizations must establish a routine for reviewing and adjusting their IT security management and risk assessment to safeguard their assets effectively. Here’s how:
-
Conduct Regular Audits: Schedule periodic audits to evaluate the effectiveness of security controls and compliance with policies. Did you know that only 52% of companies perform regular audits? Those that do experience a 40% lower risk of data breaches. With the average cost of a data breach for US organizations in 2024 hitting $4.88 million, the financial implications of neglecting audits are staggering. These evaluations not only help identify deficiencies but also highlight opportunities for enhancement in IT security management and risk assessment, ensuring that protective measures evolve alongside emerging threats.
-
Stay Informed on Threats: Keeping up with the latest cybersecurity threats and trends is crucial. For example, a recent phishing campaign targeting the hospitality industry underscores the need for vigilance. Organizations should subscribe to threat intelligence feeds and engage in industry forums to stay updated on the evolving tactics employed by cybercriminals.
-
Participate in Ongoing Training: Continuous training for staff is essential to keep them informed about new threats and best practices for maintaining safety. This proactive approach is vital, as human error remains a significant factor in many breaches. By equipping employees with the knowledge to recognize and respond to potential threats, organizations can significantly mitigate this risk.
-
Utilize Metrics and KPIs: Establish key performance indicators (KPIs) to assess the effectiveness of protective measures. Metrics such as incident response times and the number of vulnerabilities detected can guide necessary modifications and enhancements, ensuring that protection strategies remain effective against current threats.
-
Document Changes: Thorough documentation of all modifications made to protective measures, including the rationale behind adjustments, is essential. This practice not only supports compliance and future assessments but also demonstrates a commitment to robust security practices, helping to build customer trust.
By implementing these strategies, organizations can significantly enhance their IT security management and risk assessment to better protect themselves against the ever-evolving landscape of cyber threats.

Conclusion
Mastering IT security management and risk assessment is crucial for organizations aiming to protect their information systems against a constantly changing array of threats. By adopting a structured approach that includes understanding, identifying, and mitigating risks, organizations can shift their cybersecurity strategies from reactive to proactive. This not only ensures compliance but also effectively safeguards sensitive data.
The article presents a comprehensive five-step process:
- Defining the scope
- Identifying assets
- Analyzing threats and vulnerabilities
- Assessing risks
- Documenting findings
Each step builds on the previous one, creating a robust framework for enhancing IT security management. Moreover, the emphasis on regular reviews and adjustments to security measures underscores the dynamic nature of cybersecurity, reinforcing the necessity for continuous vigilance and adaptation to emerging challenges.
In conclusion, organizations must understand that effective IT security management and risk assessment are not just compliance requirements; they are vital components of a resilient operational strategy. By cultivating a culture of security awareness and integrating proactive measures, businesses can significantly lower their vulnerability to cyber threats. Taking these steps not only protects essential assets but also fosters trust with clients and stakeholders, ultimately contributing to the long-term success and integrity of the organization.
Frequently Asked Questions
What is the purpose of IT security management and risk assessment?
IT security management and risk assessment aim to safeguard organizational information systems from unauthorized access, use, disclosure, disruption, modification, or destruction by systematically identifying, assessing, and prioritizing threats.
Why is understanding IT security management and risk assessment important?
Understanding these concepts is vital for developing effective strategies that comply with regulatory requirements, such as the Cybersecurity Maturity Model Certification (CMMC), and for implementing measures to mitigate risks efficiently.
How can organizations benefit from vulnerability assessments?
Organizations that implement comprehensive vulnerability assessment protocols can effectively identify weaknesses that could lead to data breaches, allowing them to adopt targeted measures that significantly reduce their exposure to threats.
What are the first steps in conducting a risk assessment?
The first steps include defining the scope of the assessment, identifying assets that require protection, and analyzing potential threats and vulnerabilities.
What does defining the scope involve in risk assessment?
Defining the scope involves establishing clear boundaries for the evaluation by identifying the systems, assets, and processes that will be assessed, ensuring focus on critical areas.
Why is cataloging information assets important?
Cataloging information assets, including hardware, software, and data, is vital for effectively managing potential issues and tailoring security measures to protect what is most critical.
How should organizations identify threats and vulnerabilities?
Organizations should conduct a thorough analysis of potential threats, such as cyberattacks and natural disasters, and vulnerabilities like outdated software and weak passwords, using tools like vulnerability scanners.
What is the process for assessing risks?
Assessing risks involves evaluating the likelihood and potential impact of identified threats, using qualitative or quantitative techniques to prioritize them based on severity.
What should be included in the documentation of findings from a risk assessment?
Documentation should include a comprehensive report detailing identified threats, their potential impacts, and recommendations for mitigation, which is crucial for compliance and future evaluations.




