Master Risk Assessment in Cybersecurity Frameworks: A Step-by-Step Guide
Master risk assessment in cybersecurity frameworks with this step-by-step guide.

Overview
This article delves into the essential step-by-step process of mastering risk assessment within cybersecurity frameworks, highlighting its pivotal role in identifying and mitigating vulnerabilities. Why is risk assessment so crucial? By defining the scope, identifying assets, and utilizing effective tools, organizations can systematically enhance their cybersecurity posture and ensure compliance with established frameworks like NIST and ISO.
To begin with, defining the scope sets the foundation for a thorough assessment. It involves determining what assets need protection and understanding the potential threats they face. Next, identifying assets is critical; organizations must know what they are protecting to implement effective strategies. Utilizing the right tools can streamline this process, making it easier to assess risks accurately.
The systematic approach to risk assessments not only strengthens an organization’s defenses but also fosters compliance with necessary frameworks. For instance, organizations adhering to NIST guidelines can significantly reduce their vulnerability to cyber threats. This proactive stance not only safeguards sensitive information but also builds trust with clients and stakeholders.
In conclusion, mastering risk assessment is not just a best practice; it’s a necessity in today’s digital landscape. Organizations are encouraged to take action by leveraging available resources and tools to enhance their cybersecurity frameworks. Are you ready to elevate your cybersecurity posture? The time to act is now.
Introduction
In an era where cyber threats are more prevalent than ever, organizations confront a pressing challenge: identifying and mitigating risks to protect their digital assets. A comprehensive risk assessment process not only strengthens security posture but also aligns with compliance requirements and business objectives. But with a multitude of frameworks at their disposal, how can organizations pinpoint the most effective approach to risk assessment?
This guide explores the essential steps and tools necessary for mastering risk assessment within cybersecurity frameworks. By empowering organizations to navigate the complexities of today’s threat landscape, we aim to enhance their ability to safeguard their assets and ensure compliance. Are you ready to take the next step in fortifying your organization against cyber threats?
Understand the Importance of Risk Assessment in Cybersecurity
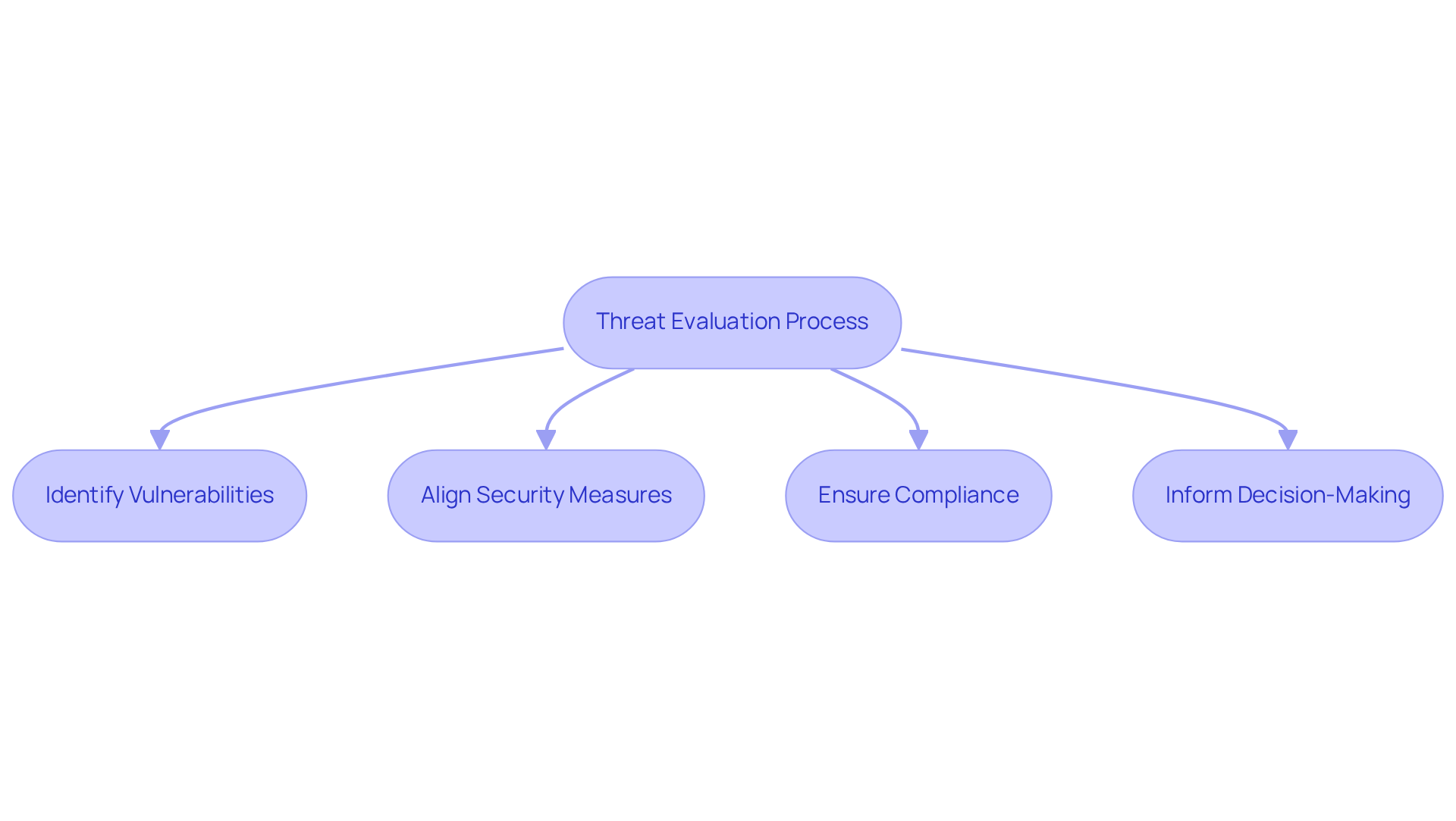
Threat evaluation is a systematic process that identifies, analyzes, and ranks cybersecurity threats. For firms, particularly defense providers, understanding this evaluation is crucial. It not only highlights vulnerabilities but also aligns security measures with broader business objectives. Did you know that over 85% of companies have developed business continuity plans for vendor-related disruptions? This statistic underscores the importance of proactively managing potential risks.
By conducting regular vulnerability assessments as part of a risk assessment cybersecurity framework, organizations can effectively address potential threats, ensuring compliance with frameworks like CMMC and enhancing their chances of securing defense contracts. These evaluations also facilitate informed decision-making regarding resource allocation and threat mitigation strategies, ultimately leading to a more robust cybersecurity posture. For instance, companies that have implemented systematic vulnerability assessments report significant improvements in their security frameworks. Many have even simulated worst-case scenarios, demonstrating the tangible benefits of this practice.
Experts agree that regular evaluations within a risk assessment cybersecurity framework are not merely a compliance checkbox; they are a strategic necessity for maintaining resilience against evolving cyber threats. As Mr. Aravind A. states, "Cybersecurity threat management enhances enterprise resilience through expert evaluation services, ensuring compliance and proactive protection." This highlights the essential role of structured evaluations in achieving CMMC compliance.
In conclusion, organizations must prioritize threat evaluations as a fundamental aspect of their cybersecurity strategy. By doing so, they not only protect their assets but also position themselves for success in an increasingly complex digital landscape.
Identify Relevant Cybersecurity Frameworks for Risk Assessment
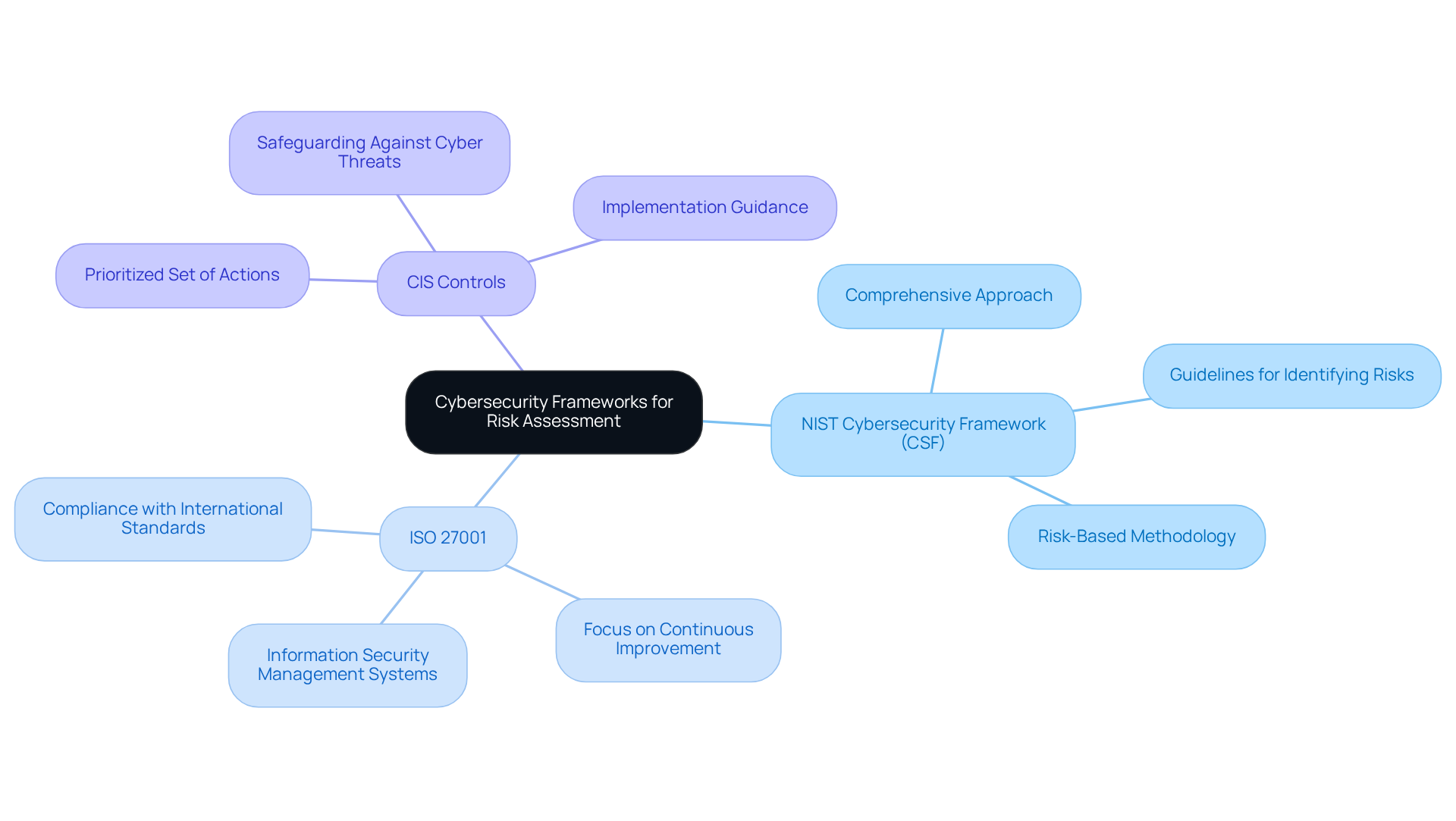
A risk assessment cybersecurity framework plays a crucial role in helping organizations effectively evaluate vulnerabilities. The NIST Cybersecurity Framework (CSF) is notable for its comprehensive approach as a risk assessment cybersecurity framework, providing essential guidelines for identifying, assessing, and addressing cybersecurity challenges. Have you considered how this framework could enhance your organization's security posture?
In addition to the NIST CSF, other significant frameworks include:
- ISO 27001, which emphasizes information security management systems
- CIS Controls, offering a prioritized set of actions to safeguard against cyber threats
Each of these frameworks has its strengths, but how do you determine which one aligns best with your organization’s specific needs and regulatory requirements?
To ensure your evaluation processes adhere to best practices and compliance mandates, it’s vital to assess your unique circumstances. By choosing the appropriate risk assessment cybersecurity framework, you not only bolster your cybersecurity defenses but also demonstrate a commitment to safeguarding sensitive information. Take action today—evaluate your options and implement a framework that meets your organizational goals.
Conduct a Step-by-Step Risk Assessment Process
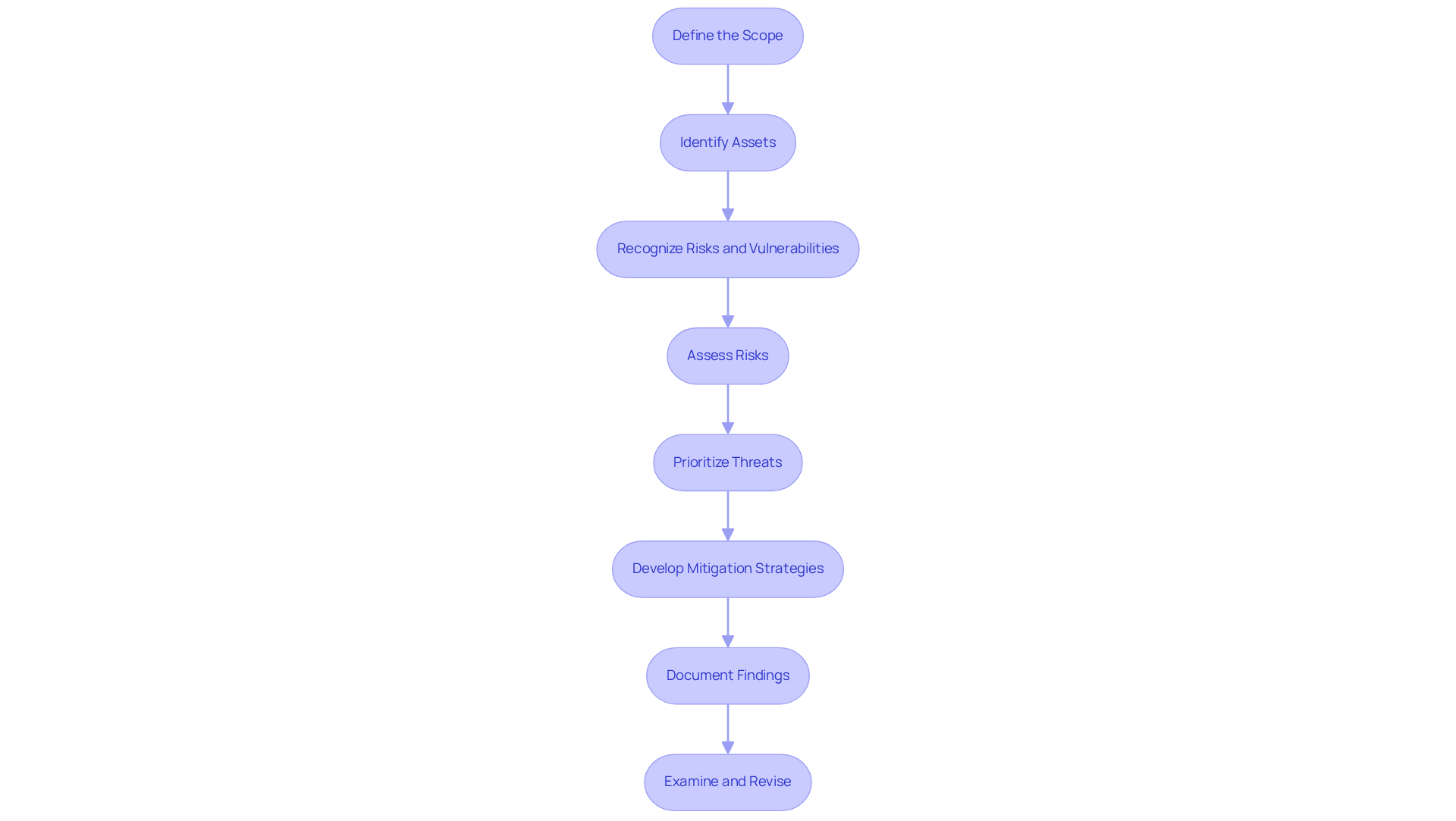
To conduct a thorough risk assessment, follow these essential steps:
-
Define the Scope: Clearly outline the boundaries of the evaluation, specifying the assets, processes, and systems to be examined. This foundational step ensures that the assessment is focused and relevant.
-
Identify Assets: Catalog all information assets, including hardware, software, and data, assessing their value to the organization. This should include both physical assets such as servers, workstations, and mobile devices, as well as virtual assets like virtual machines and cloud-based services. Utilize asset management tools to track these assets effectively, ensuring that all information is up-to-date and accessible. Understanding asset value is crucial for prioritizing protection efforts.
-
Recognize Risks and Vulnerabilities: Examine possible dangers such as cyberattacks and natural disasters, along with weaknesses like outdated software and weak passwords. This dual analysis aids in comprehending the threat landscape.
-
Assess Risks: Evaluate the likelihood and potential impact of each identified threat and vulnerability using qualitative or quantitative methods. This evaluation ought to be comprehensive, as 41% of organizations indicated encountering three or more significant threat events in the past year.
-
Prioritize Threats: Rank the threats based on their evaluated impact and likelihood, focusing on high-priority threats that require immediate attention. This prioritization is vital for effective resource allocation.
-
Develop Mitigation Strategies: Create actionable plans to address the identified threats, including implementing security controls and policies. Effective strategies can significantly reduce potential losses, as companies with incident response teams saved an average of $2.66 million compared to those without.
-
Document Findings: Record the evaluation process, discoveries, and mitigation strategies to ensure accountability and facilitate future evaluations. Documentation is essential for ongoing enhancement in management practices.
-
Examine and Revise: Consistently examine and revise the hazard evaluation to incorporate alterations in the entity’s surroundings and arising dangers. This continuing procedure is crucial, particularly as cyber dangers are now viewed as the primary emerging challenge by 92% of business leaders.
By following these optimal methods for outlining the scope and performing evaluations, organizations can improve their cybersecurity frameworks and better prepare for possible threats.
Utilize Tools and Resources for Effective Risk Assessment
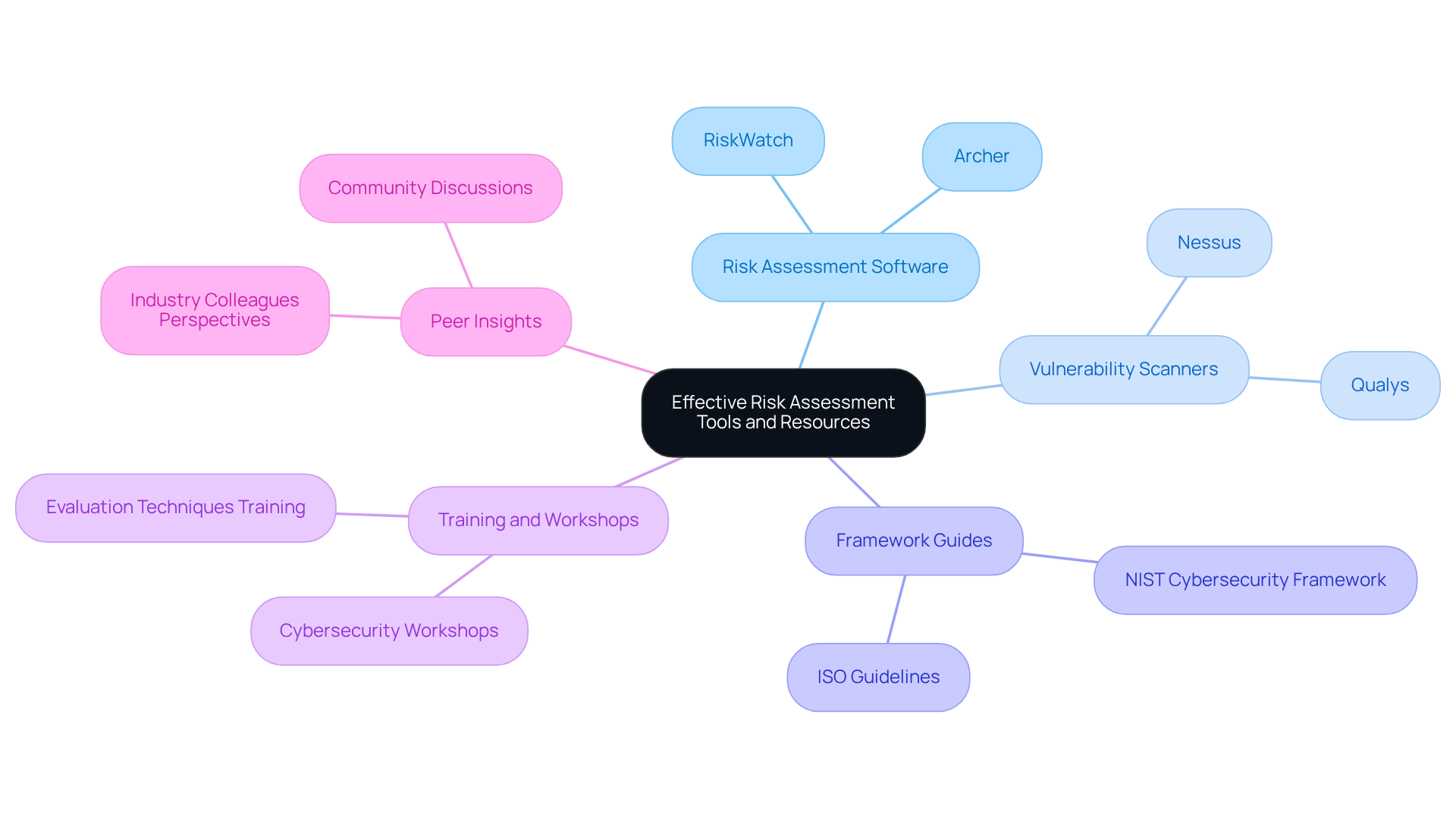
To enhance the effectiveness of your risk assessment, consider leveraging the following tools and resources:
-
Risk Assessment Software: Solutions like RiskWatch and Archer automate the risk assessment process, providing templates and frameworks that streamline evaluations. These tools not only save time but also improve accuracy by offering organized methods for identifying and managing uncertainties. Investing in such tools can be cost-effective, helping companies avoid penalties for non-compliance.
-
Vulnerability Scanners: Tools such as Nessus and Qualys are crucial for pinpointing vulnerabilities within your systems. These scanners deliver essential insights into potential threats, enabling organizations to prioritize remediation efforts effectively. Recent advancements in vulnerability scanning technology have significantly enhanced their accuracy and efficiency, making them indispensable in modern cybersecurity strategies. As cybersecurity expert Subbaiah Ku notes, 'The risk assessment cybersecurity framework helps businesses enhance their security and identify potential threats to their compliance systems.'
-
Framework Guides: Resources from NIST and ISO offer comprehensive instructions and best practices for conducting evaluations. The NIST Cybersecurity Framework, in particular, serves as a solid foundation for organizations to apply the risk assessment cybersecurity framework to understand and mitigate cybersecurity threats systematically. Regular cybersecurity evaluations should be performed at least annually to ensure ongoing compliance and security.
-
Training and Workshops: Engaging in training sessions or workshops focused on evaluation techniques ensures your team is well-equipped to manage reviews efficiently. Continuous education in this area is vital, as the landscape of cybersecurity threats evolves rapidly.
-
Peer Insights: Tapping into perspectives from industry colleagues or discussions can yield valuable lessons learned and best practices in conducting assessments. Sharing experiences within the community fosters a culture of collaboration and continuous improvement in risk management practices.
Conclusion
Mastering risk assessment within cybersecurity frameworks is not just beneficial; it’s essential for organizations that want to protect their digital assets and stay compliant in a complex threat landscape. Proactive threat evaluations form the backbone of a strong cybersecurity strategy, allowing organizations to pinpoint vulnerabilities and align their security measures with broader business goals.
Selecting the right cybersecurity framework, like the NIST Cybersecurity Framework, is crucial for effective risk assessments. The outlined step-by-step process—from defining the scope to developing mitigation strategies—serves as a clear roadmap for organizations looking to bolster their cybersecurity posture. Additionally, utilizing tools such as vulnerability scanners and risk assessment software can streamline evaluations and significantly enhance accuracy in identifying potential threats.
Organizations must understand that effective risk assessment is a continuous journey that evolves with the cyber threat landscape. By prioritizing regular evaluations and employing the right frameworks and tools, businesses not only safeguard their assets but also position themselves for success and resilience against emerging challenges. Taking decisive action today to implement these practices will pave the way for a stronger, more secure future in cybersecurity.
Frequently Asked Questions
What is the purpose of threat evaluation in cybersecurity?
Threat evaluation is a systematic process that identifies, analyzes, and ranks cybersecurity threats, highlighting vulnerabilities and aligning security measures with broader business objectives.
Why is risk assessment important for firms, particularly defense providers?
Understanding risk assessment is crucial for defense providers as it helps them manage potential risks proactively, ensuring compliance with frameworks like CMMC and enhancing their chances of securing defense contracts.
How do regular vulnerability assessments contribute to cybersecurity?
Regular vulnerability assessments allow organizations to address potential threats effectively, facilitate informed decision-making regarding resource allocation, and improve their overall cybersecurity posture.
What benefits have companies reported from implementing systematic vulnerability assessments?
Companies that have implemented systematic vulnerability assessments report significant improvements in their security frameworks and have successfully simulated worst-case scenarios, demonstrating the tangible benefits of these practices.
Are regular evaluations within a risk assessment framework considered necessary?
Yes, experts agree that regular evaluations are a strategic necessity for maintaining resilience against evolving cyber threats and are not merely a compliance checkbox.
How does cybersecurity threat management enhance enterprise resilience?
Cybersecurity threat management enhances enterprise resilience through expert evaluation services, ensuring compliance and proactive protection against cyber threats.
What should organizations prioritize in their cybersecurity strategy?
Organizations must prioritize threat evaluations as a fundamental aspect of their cybersecurity strategy to protect their assets and succeed in a complex digital landscape.




