What Is the Impact of Malicious Code on Defense Contractors?
Explore what is a possible effect of malicious code on defense contractors and the need for cybersecurity.

Overview
The impact of malicious code on defense contractors is profound, leading to operational disruptions, financial losses, and potential threats to national security. Consider this: ransomware attacks can result in average losses exceeding $5 million per incident. This staggering statistic underscores the urgent need for robust cybersecurity measures and comprehensive employee training to effectively mitigate these risks.
To address these challenges, defense contractors must prioritize cybersecurity. Implementing advanced security protocols and fostering a culture of awareness among employees are essential steps. By doing so, organizations can not only protect their assets but also safeguard national security.
In conclusion, the threat posed by malicious code is real and significant. It is imperative for defense contractors to take proactive measures to enhance their cybersecurity posture. Investing in training and resources is not just a recommendation; it is a necessity in today’s digital landscape.
Introduction
The digital battlefield is increasingly fraught with peril. Malicious code—ranging from viruses to ransomware—poses significant threats to defense contractors. With stakes higher than ever, understanding the impact of these cyber threats is essential for safeguarding sensitive information and maintaining operational integrity. As incidents of cyberattacks continue to surge, one pressing question emerges: how can defense contractors effectively shield themselves from the devastating effects of malicious code while navigating an ever-evolving threat landscape?
To address this challenge, it’s crucial to recognize the types of threats that exist and their potential consequences. Defense contractors must not only be aware of the risks but also take proactive measures to protect their operations. This article will explore effective strategies for defense contractors to enhance their cybersecurity posture, ensuring they remain resilient in the face of these growing threats.
Are you prepared to defend your organization against the relentless tide of cyber threats? Let's delve into the necessary steps to fortify your defenses.
Define Malicious Code: Key Concepts and Importance
Malicious software refers to any program intentionally designed to harm computer systems, networks, or users. This category includes various threats such as viruses, worms, trojan horses, ransomware, and spyware. Understanding what is a possible effect of malicious code is crucial for contractors, as its potential to disrupt operations and compromise sensitive information can lead to dire consequences.
For example, in 2023, ransomware attacks accounted for 29% of global attacks on manufacturers, who represented over 25% of security incidents that year. This statistic underscores the vulnerability of organizations in this sector. The repercussions of such attacks can be severe, with financial losses averaging $5.46 million per breach in the security sector in 2024, alongside reputational damage and legal ramifications. Given the sensitive nature of the information managed by security contractors, one might consider what is a possible effect of malicious code, which can be especially pronounced.
Identifying the characteristics and behaviors of malicious software is essential for developing robust cybersecurity strategies that protect against these evolving threats. Additionally, with 61% of military organizations reporting ransomware attacks in the past year and the security sector facing approximately 1,250 cyber incidents weekly, the need for effective protections cannot be overstated. Are you prepared to safeguard your organization against these risks? Taking proactive measures is not just advisable; it’s imperative.

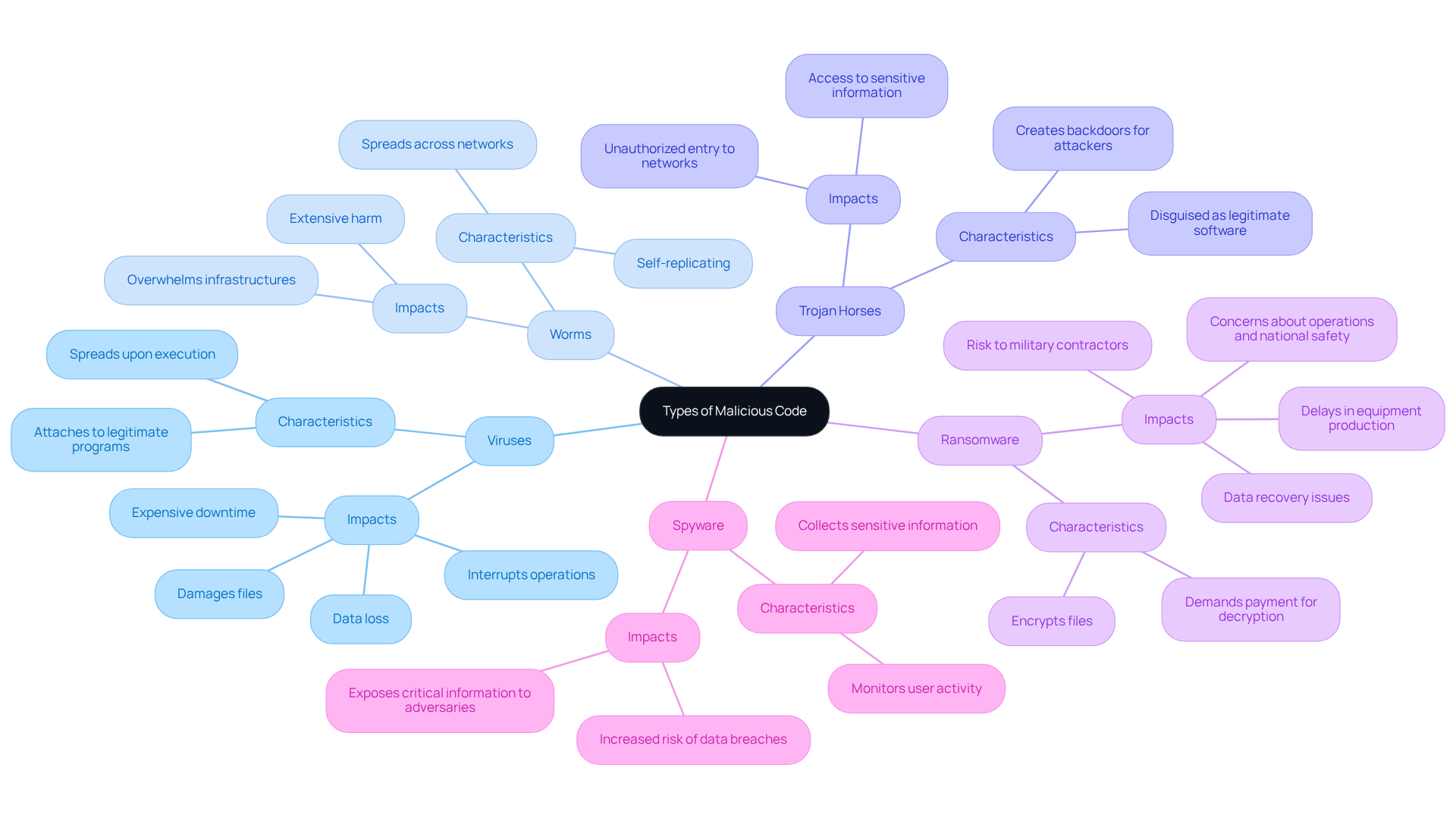
Explore Types of Malicious Code and Their Impacts
Malicious code encompasses several types, each with unique characteristics and significant impacts on defense contractors:
-
Viruses: These attach themselves to legitimate programs and spread when the infected program is executed. When considering what is a possible effect of malicious code, we see that it can damage files and interrupt operations, resulting in expensive downtime and data loss.
-
Worms: Unlike viruses, worms can replicate themselves and spread across networks without user intervention. This self-propagation can lead to extensive harm, overwhelming infrastructures and networks.
-
Trojan Horses: Disguised as legitimate software, Trojan horses contain harmful code that can create backdoors for attackers. Once inside, they enable unauthorized entry to sensitive networks and information.
-
Ransomware: This particularly insidious type of malware encrypts files on a victim's system, demanding payment for decryption. Ransomware presents a considerable risk to military contractors, leading to concerns about what is a possible effect of malicious code on operations, sensitive information, combat preparedness, and national safety. Notably, many companies that fall victim to ransomware attacks do not recover all their data, and there is no guarantee that data wasn't copied before being returned. As Jason Soroko, Senior Fellow at Sectigo, states, "Shutting down operations is a big deal for anyone, but when you work with the DoD, the delays and backups during equipment production and delivery of goods can lead to significant delays that impact military readiness."
-
Spyware: This type of malware secretly monitors user activity and collects sensitive information, which can be exploited for malicious purposes. The risk of data breaches increases as spyware can expose critical information to adversaries.
For defense contractors, understanding what is a possible effect of malicious code is crucial to implement appropriate defenses. Cybersecurity experts stress that human actions are the most vulnerable aspect in protection. This underscores the necessity for ongoing training and proactive measures to reduce these threats efficiently. As Kent Wilson, Vice President at Bugcrowd, notes, "Human behavior remains the weakest link in security, and no amount of investment in classified networks or perimeter security can fully prevent an employee from unknowingly downloading infostealer malware that exposes credentials."
What steps are you taking to safeguard your operations? It's essential to stay informed and proactive in the face of these evolving threats.
Understand How Malicious Code Spreads and Affects Systems
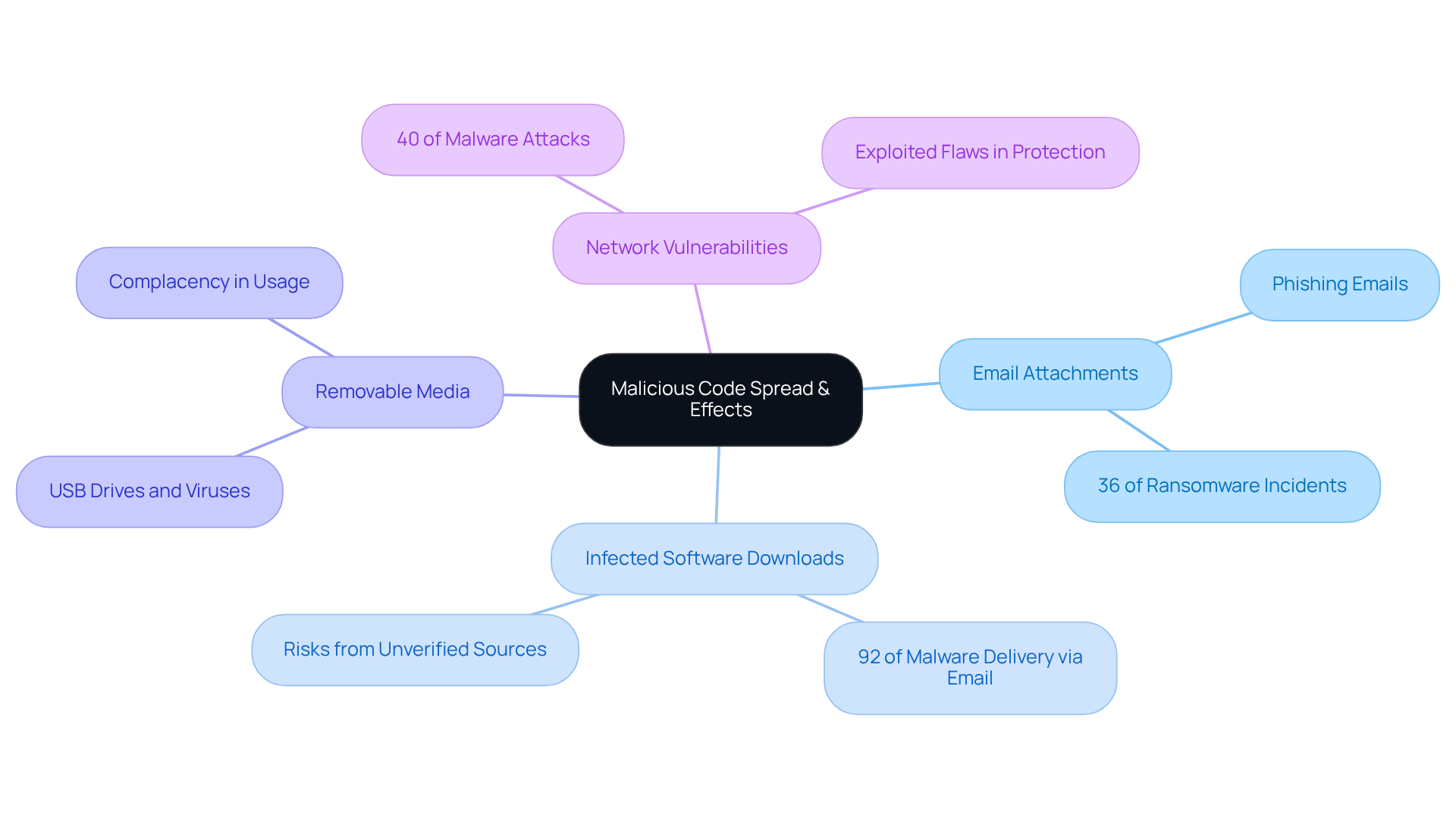
Malicious code can infiltrate systems through several key vectors, each posing significant risks to defense contractors:
- Email Attachments: Phishing emails serve as a primary method for spreading malicious code, often containing infected attachments that compromise systems when opened. In fact, phishing attacks account for 36% of ransomware incidents in Singapore, underscoring the critical need for vigilance.
- Infected Software Downloads: Acquiring software from unverified sources can introduce damaging programs into devices. This risk is heightened by the fact that 92% of malware delivery occurs via email, making it essential for organizations to scrutinize software origins.
- Removable Media: USB drives and other removable media can transmit viruses and worms that infect devices upon connection. The ease of use of these devices often leads to complacency, increasing vulnerability.
- Network Vulnerabilities: Exploiting flaws in network protection enables harmful programs to spread swiftly throughout linked systems. With 40% of malware attacks arising from exploited vulnerabilities, contractors must prioritize robust network protection measures.
When considering what is a possible effect of malicious code, the consequences can vary widely, from minor disruptions to catastrophic failures. For military contractors, the stakes are particularly high; breaches can result in what is a possible effect of malicious code, such as the loss of sensitive military information, substantial financial penalties, and potential damage to national security. In 2024, the average cost of a ransomware incident reached $5.13 million, highlighting the financial implications of such attacks. Real-world examples, such as the HMRC phishing breach that compromised 100,000 taxpayer accounts and resulted in £47 million stolen through fake rebate claims, illustrate the severe repercussions of inadequate cybersecurity measures. As the threat landscape evolves, with malware infections expected to reach around 6.5 billion by 2025, contractors must remain alert and proactive in their cybersecurity strategies to protect their operations and sensitive information.
For additional information on cybersecurity measures, consider exploring external resources that provide insights and best practices for contractors.
Implement Strategies to Prevent Malicious Code Attacks
To effectively combat malicious code attacks, defense contractors must adopt a multi-layered cybersecurity strategy that encompasses several critical components:
-
Regular Software Updates: Keeping software and systems up to date is essential for closing vulnerabilities that malicious code can exploit. Frequent updates not only fix vulnerabilities but also improve overall system resilience against emerging threats.
-
Employee Training: Comprehensive training programs focused on phishing awareness and safe browsing practices are vital. Organizations that invest in such training can observe a substantial decrease in malware infections. Studies suggest that companies participating in awareness training experience an impressive 70% reduction in incidents. This proactive approach empowers employees to recognize and respond to potential threats, minimizing the risk of infection. Notably, only about 52% of organizations conduct anti-phishing training, highlighting a critical need for improvement. Moreover, 45% of employees indicate they have not received any training from their employers, underscoring the urgency for defense contractors to prioritize training initiatives.
-
Antivirus and Anti-malware Solutions: Deploying robust security software is crucial for detecting and neutralizing threats before they can inflict damage. Regular updates to these solutions ensure they remain effective against the latest malware variants. Additionally, having a Written Information Security Plan (WISP) is essential for protecting sensitive information and outlining how an organization safeguards its data.
-
Network Security Measures: Implementing firewalls, intrusion detection systems, and secure configurations is essential for protecting against unauthorized access. These measures create a fortified perimeter that can deter potential attacks.
A well-defined incident response plan is essential for ensuring that organizations can swiftly address and mitigate what is a possible effect of malicious code during a harmful software attack. This preparedness not only reduces downtime but also helps in preserving sensitive information.
By integrating these strategies, defense contractors can significantly enhance their cybersecurity posture, safeguard sensitive information, and reduce the likelihood of successful malicious code attacks. Investing in cybersecurity awareness training is not just an expenditure; it is a strategic investment. Organizations can expect a return of more than triple their investment, potentially saving losses of up to $177,708.

Conclusion
Understanding the implications of malicious code is crucial for defense contractors. These threats can severely disrupt operations and compromise sensitive information. The various types of malicious software—viruses, worms, ransomware, and spyware—each pose unique risks that can lead to significant financial losses, reputational damage, and even threats to national security. By recognizing the potential consequences of these attacks, organizations can better prepare themselves to face these evolving challenges.
Key insights discussed include the alarming prevalence of ransomware and the various methods through which malicious code spreads. The critical need for robust cybersecurity measures cannot be overstated. Statistics, such as the average cost of a breach and the percentage of military organizations affected by ransomware, underscore the urgency for defense contractors to adopt comprehensive strategies. These strategies should include:
- Employee training
- Regular software updates
- Effective network security measures
The significance of proactive cybersecurity is paramount. As the threat landscape continues to evolve, defense contractors must prioritize their defenses against malicious code to protect sensitive information and maintain operational integrity. Investing in employee training and implementing multi-layered security strategies not only mitigates risks but also fosters a culture of awareness that is essential in today's digital environment. By taking these steps, organizations can safeguard their operations and ensure they are prepared to face the challenges posed by malicious code in the future.
Frequently Asked Questions
What is malicious code?
Malicious code refers to any program intentionally designed to harm computer systems, networks, or users. This includes threats such as viruses, worms, trojan horses, ransomware, and spyware.
Why is understanding malicious code important for contractors?
Understanding malicious code is crucial for contractors because its potential to disrupt operations and compromise sensitive information can lead to severe consequences, including financial losses and reputational damage.
What statistics highlight the impact of ransomware attacks?
In 2023, ransomware attacks accounted for 29% of global attacks on manufacturers, which represented over 25% of security incidents that year. This indicates the vulnerability of organizations in this sector.
What are the financial implications of security breaches in the security sector?
The financial losses from security breaches in the security sector averaged $5.46 million per breach in 2024, alongside potential reputational damage and legal ramifications.
How prevalent are ransomware attacks in military organizations?
In the past year, 61% of military organizations reported experiencing ransomware attacks.
What is the frequency of cyber incidents in the security sector?
The security sector faces approximately 1,250 cyber incidents weekly, highlighting the urgent need for effective cybersecurity measures.
What should organizations do to protect against malicious code?
Organizations should develop robust cybersecurity strategies that identify the characteristics and behaviors of malicious software and take proactive measures to safeguard against these evolving threats.




