What Level of System and Network is Required for CUI Compliance?
Understand what level of system and network is required for CUI compliance and data protection.

Overview
The level of system and network required for Controlled Unclassified Information (CUI) compliance varies based on the sensitivity of the information. Distinct categories such as CUI Basic, CUI Specified, and CUI High dictate specific safeguarding measures and technical requirements. Organizations must implement robust security protocols—access controls, encryption, and continuous monitoring—to effectively protect sensitive data. This adherence to federal regulations not only ensures compliance but also safeguards national interests.
To achieve CUI compliance, it is essential to understand the nuances of each category. For instance, CUI Basic may require less stringent measures compared to CUI High, which demands comprehensive security strategies. By prioritizing these protocols, organizations can mitigate risks associated with data breaches and enhance their overall security posture.
In conclusion, the implementation of these measures is not merely a regulatory requirement; it is a commitment to protecting sensitive information and maintaining the integrity of national security. Organizations are encouraged to review their current practices and take decisive action towards compliance.
Introduction
Understanding the nuances of Controlled Unclassified Information (CUI) is crucial for organizations navigating the intricate landscape of federal regulations. As this sensitive data category grows in importance—particularly for defense contractors—the stakes for compliance and security have never been higher.
With potential repercussions ranging from contract loss to national security risks, organizations must consider:
- What specific levels of system and network protection are necessary to safeguard CUI effectively?
This article delves into the essential requirements and best practices for achieving CUI compliance. It equips organizations with the knowledge to fortify their cybersecurity posture and ensure adherence to federal standards.
Define Controlled Unclassified Information (CUI) and Its Importance
Controlled Unclassified Information (CUI) is a critical category of sensitive data created or possessed by the U.S. government that requires safeguarding or dissemination controls, yet does not meet the criteria for classification. This includes technical data, privacy information, and sensitive but unclassified data. For defense contractors, understanding what level of system and network is required for CUI is essential, as mishandling this information can lead to severe repercussions, such as the loss of contracts and significant reputational damage.
The importance of adhering to CUI regulations extends beyond mere legal compliance; it is vital for national security. Improper management of CUI can expose sensitive information to unauthorized access, potentially jeopardizing defense operations. Cybersecurity experts highlight the gravity of mishandling CUI, with one expert noting, "It takes 20 years to build a reputation and a few minutes of a cyber-incident to ruin it."
Moreover, recent regulatory changes emphasize what level of system and network is required for CUI to ensure that contractors establish robust data security protocols. As the cybersecurity landscape evolves, the responsibility to protect CUI becomes increasingly paramount. Effective adherence to these standards is foundational for securing defense contracts and safeguarding national interests.
The CMMC Info Hub serves as an invaluable resource for achieving and maintaining Cybersecurity Maturity Model Certification (CMMC) compliance, particularly concerning CUI. It offers actionable strategies and community insights designed to help you navigate these challenges effectively. For additional support, consider exploring our FAQs and external links, which provide further guidance on CUI adherence.

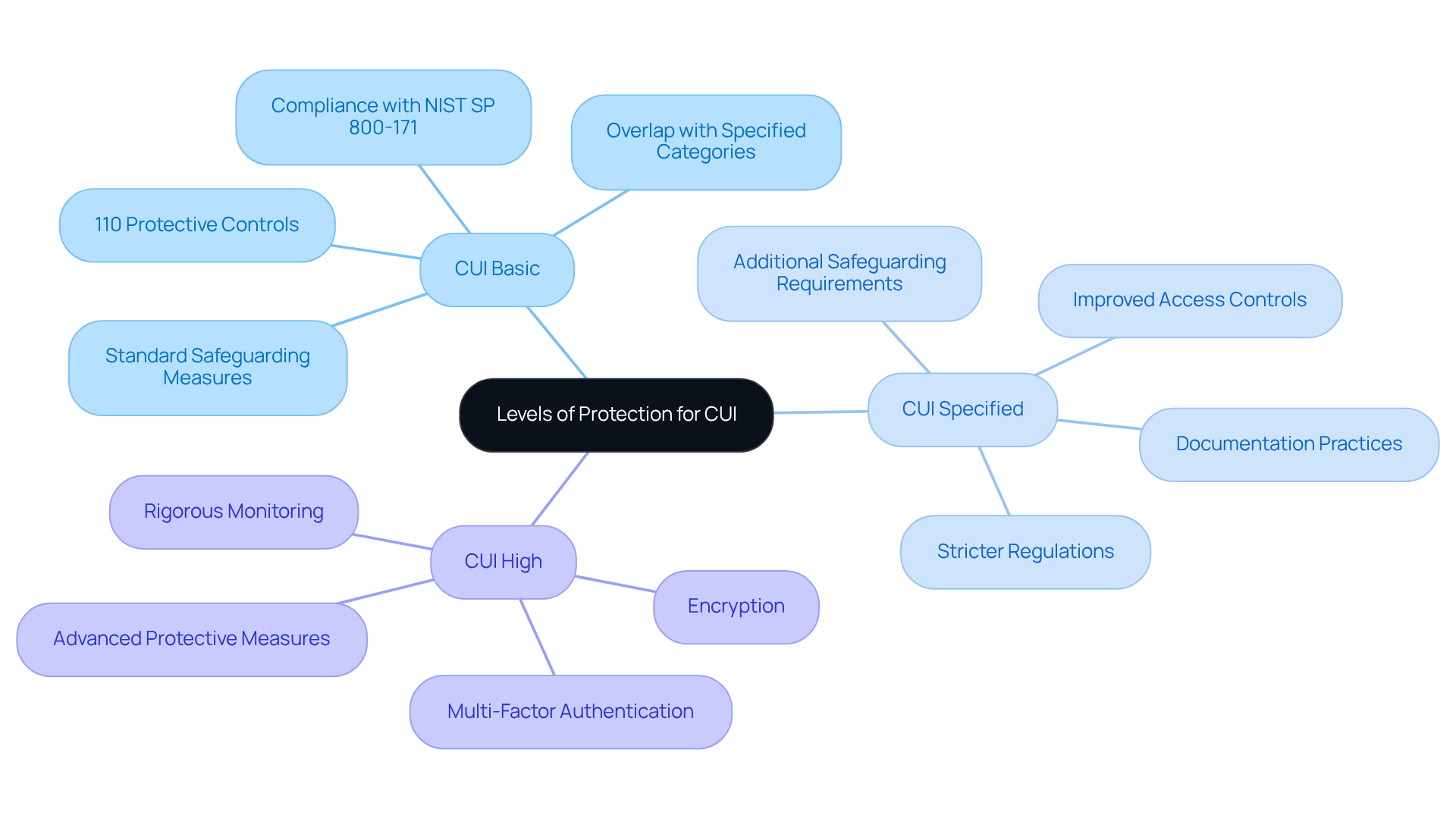
Outline Levels of Protection for CUI
CUI is categorized into distinct levels of protection based on its sensitivity, each requiring specific safeguarding measures:
-
CUI Basic: This level mandates standard safeguarding measures as outlined in NIST SP 800-171, which includes 110 protective controls across 14 families. Organizations must implement basic security controls to safeguard this information from unauthorized access, guaranteeing adherence to federal regulations. Notably, 27 of the 93 CUI Basic categories are also designated as Specified in certain contexts, highlighting the overlap between these levels. Practical strategies and peer insights can assist organizations in attaining adherence with confidence at this level.
-
CUI Specified: This level entails additional safeguarding requirements dictated by specific laws or regulations. Organizations must follow stricter regulations, which may include improved access controls and documentation practices, to ensure conformity and protect sensitive information effectively. Grasping these requirements is essential for managing the intricacies of CMMC adherence.
-
CUI High: For information designated as highly sensitive, entities are required to implement advanced protective measures. This includes encryption, multi-factor authentication, and rigorous monitoring to defend against potential threats. The execution of these actions is essential for entities managing CUI High to uphold regulations and safeguard national interests. The Ultimate Guide to Achieving CMMC Compliance acts as a roadmap for entities to master these requirements and secure defense contracts successfully.
Comprehending what level of system and network is required for CUI enables entities to customize their security strategies efficiently, ensuring strong adherence to federal regulations and protecting sensitive information. As noted by RSI Security, "Whether you need help understanding 'What is CUI Basic?' or preparing for frameworks such as CMMC NIST SP 800 171, our team offers the tools and expertise to keep your entity secure and compliant." Additionally, organizations must be aware that CMMC Level 2 certification is required for handling Controlled Unclassified Information (CUI). Furthermore, the Department of Defense is completing the rulemaking process for DFARS clause 252.204-7021, which will affect the requirements for contractors.
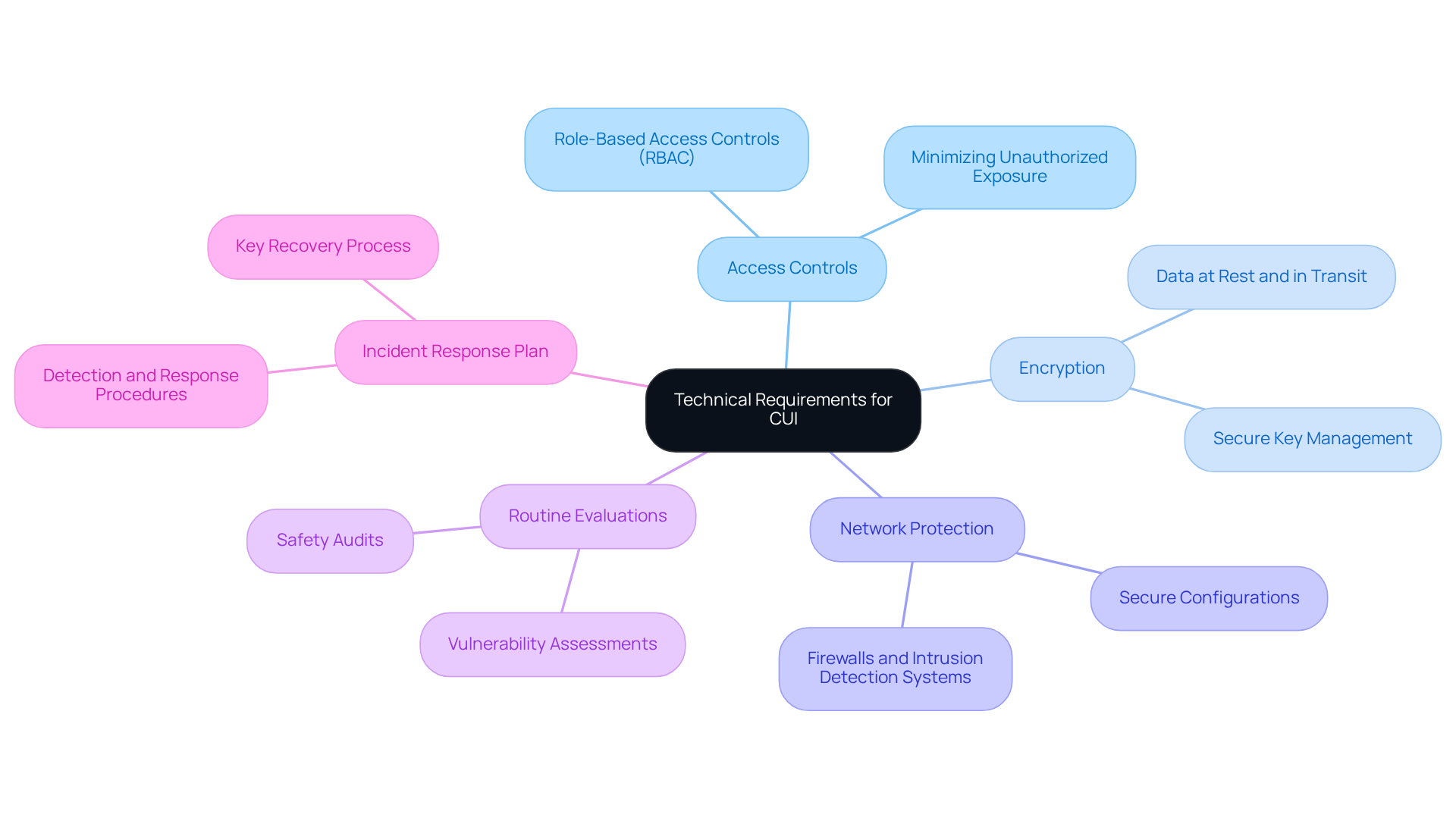
Specify Technical Requirements for Systems and Networks Handling CUI
Organizations managing Controlled Unclassified Information (CUI) must determine what level of system and network is required for CUI to adhere to specific technical requirements, ensuring robust protection and compliance with federal regulations, particularly concerning the Cybersecurity Maturity Model Certification (CMMC). Key components include:
-
Access Controls: Implementing role-based access controls (RBAC) is paramount for limiting CUI access to authorized personnel only. This strategy minimizes the risk of unauthorized exposure and bolsters data security. Effective access controls are essential for safeguarding sensitive information and ensuring compliance with regulatory standards, especially regarding what level of system and network is required for CUI, as discussed in 'The Ultimate Guide to Achieving CMMC Compliance.'
-
Encryption: Employing encryption for both data at rest and in transit is vital for protecting CUI from unauthorized access. Robust encryption protocols secure sensitive information and help define what level of system and network is required for CUI, thereby meeting the regulatory requirements outlined in FAR 52.204-21. Furthermore, secure key management practices are critical for maintaining the effectiveness of encryption strategies, as inadequate key management can undermine even the most powerful encryption algorithms.
-
Network Protection: Establishing comprehensive network protection measures—such as firewalls, intrusion detection systems, and secure configurations—is crucial for safeguarding networks, particularly in understanding what level of system and network is required for CUI. Organizations that have successfully implemented strong network protection protocols exemplify best practices in the field, contributing to the overarching goal of achieving CMMC compliance.
-
Routine Evaluations: Conducting routine safety audits and vulnerability assessments allows organizations to identify and address potential risks proactively. This practice is essential for maintaining compliance with NIST SP 800-171 and the forthcoming CMMC requirements, ensuring that organizations remain vigilant against emerging cyber threats.
-
Incident Response Plan: Developing and sustaining a robust incident response plan is vital for effectively managing any breaches or security incidents involving CUI. This plan should delineate clear procedures for detection, response, and recovery to mitigate impact. Additionally, incorporating a key recovery process is essential to avert data loss in the event of a key being misplaced or forgotten.
These technical requirements are essential for protecting sensitive information and highlight what level of system and network is required for CUI, thereby fostering trust with government agencies and stakeholders. Organizations that prioritize these measures can substantially reduce the risk of data breaches and enhance their cybersecurity resilience, aligning with the comprehensive resources provided by CMMC Info Hub for achieving cybersecurity maturity model certification.
Implement Best Practices for CUI Compliance and Security Maintenance
To ensure compliance with Controlled Unclassified Information (CUI) regulations and bolster security, organizations must adopt the following best practices:
-
Establish a CUI Program: Develop a dedicated program to manage CUI, encompassing clear policies, procedures, and comprehensive training for employees. A substantial portion of entities have acknowledged the necessity for dedicated CUI initiatives to improve their regulatory stance.
-
Conduct Regular Training: Implement ongoing training initiatives for employees focused on CUI handling, protective protocols, and adherence requirements. Professional perspectives emphasize that efficient training is essential; organizations that invest in employee education observe a significant enhancement in compliance and awareness.
-
Data Classification: Introduce a data classification scheme to accurately identify and categorize CUI, ensuring that sensitive information is handled and protected appropriately. This step is vital for maintaining the integrity of CUI and preventing unauthorized access.
-
Continuous Monitoring: Employ monitoring tools to detect unauthorized access or anomalies within systems that handle CUI. Continuous oversight is essential, especially as the aerospace and defense sector has experienced a staggering 300% increase in cyberattacks since 2018. Continuous monitoring practices should encompass:
- Vulnerability scanning to identify weaknesses
- Timely patch management for systems and applications
- Regular log reviews for signs of incidents
- Configuration monitoring to ensure systems remain aligned with established baselines
- Access reviews and incident monitoring to maintain security integrity
-
Documentation and Reporting: Maintain meticulous records of adherence efforts and promptly report any incidents involving CUI to the relevant authorities. This practice not only assists in adherence but also improves organizational accountability.
By adhering to these best practices, organizations can effectively manage CUI, ensuring compliance while safeguarding sensitive information against potential threats.

Conclusion
Understanding the requirements for Controlled Unclassified Information (CUI) compliance is essential for organizations handling sensitive data. The significance of CUI extends beyond regulatory compliance; it plays a crucial role in national security and the safeguarding of sensitive information. Organizations must recognize that effective management of CUI not only protects their reputation but also ensures the integrity of defense operations.
This article outlines various levels of protection for CUI, ranging from basic to high sensitivity, each with specific safeguarding measures. It emphasizes the need for robust technical requirements, including access controls, encryption, and continuous monitoring, to mitigate risks associated with unauthorized access. Best practices, such as establishing dedicated CUI programs, conducting regular training, and maintaining meticulous documentation, are vital for achieving compliance and enhancing security.
In a landscape where cyber threats are ever-evolving, prioritizing CUI compliance is not just a legal obligation; it is a strategic necessity. Organizations are encouraged to adopt these best practices and technical measures to fortify their defenses, protect sensitive information, and maintain trust with government agencies and stakeholders. By taking proactive steps toward CUI compliance, organizations can significantly reduce their vulnerability to data breaches and contribute to the overall security of national interests.
Frequently Asked Questions
What is Controlled Unclassified Information (CUI)?
Controlled Unclassified Information (CUI) is a category of sensitive data created or possessed by the U.S. government that requires safeguarding or dissemination controls but does not meet the criteria for classification. This includes technical data, privacy information, and sensitive but unclassified data.
Why is understanding CUI important for defense contractors?
Understanding CUI is essential for defense contractors because mishandling this information can lead to severe repercussions, such as the loss of contracts and significant reputational damage.
How does improper management of CUI affect national security?
Improper management of CUI can expose sensitive information to unauthorized access, potentially jeopardizing defense operations and national security.
What do recent regulatory changes emphasize regarding CUI?
Recent regulatory changes emphasize the level of system and network required for CUI to ensure that contractors establish robust data security protocols.
What role does the CMMC Info Hub play in relation to CUI?
The CMMC Info Hub serves as a resource for achieving and maintaining Cybersecurity Maturity Model Certification (CMMC) compliance, particularly concerning CUI. It offers actionable strategies and community insights to help navigate CUI challenges effectively.
Where can I find additional support for CUI adherence?
Additional support for CUI adherence can be found in FAQs and external links provided by resources like the CMMC Info Hub, which offer further guidance on the topic.




